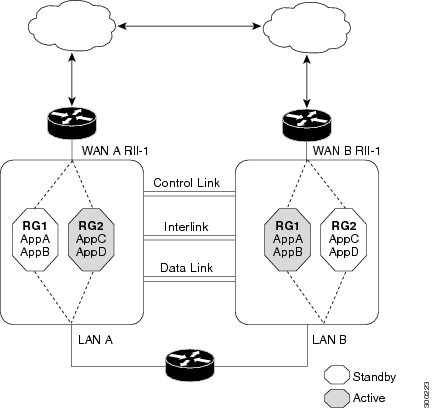
By default, when
asymmetric routing is configured, Network Address Translation (NAT) processes
non-ALG packets on the standby RG, instead of forwarding them to the active.
The NAT-only configuration (that is when the firewall is not configured) can
use both the active and standby RGs for processing packets. If you have a
NAT-only configuration and you have configured asymmetric routing, the default
asymmetric routing rule is that NAT will selectively process packets on the
standby RG. You can configure the
asymmetric-routing
always-divert enable
command to divert packets received on the standby RG to
the active RG. Alternatively, if you have configured the firewall along with
NAT, the default asymmetric routing rule is to always divert the packets to the
active RG.
When NAT receives a
packet on the standby RG and if you have not configured the diverting of
packets, NAT does a lookup to see if a session exists for that packet. If a
session exists and there is no ALG associated for that session, NAT processes
the packet on the standby RG. The processing of packets on the standby RG when
a session exists significantly increases the bandwidth of the NAT traffic.
ALGs are used by NAT
to identify and translate payload and to create child flows. ALGs require a
two-way traffic to function correctly. NAT must divert all traffic to the
active RG for any packet flow that is associated with an ALG. This is
accomplished by checking if ALG data that is associated with the session is
found on the standby RG. If ALG data exits, the packet is diverted for
asymmetric routing.
VRF-Aware Software
Infrastructure (VASI) support was added in Cisco IOS XE Release 3.16S.
Multiprotocol Label Switching (MPLS) asymmetric routing is also supported.
In Cisco IOS XE
Release 3.16S, NAT supports asymmetric routing with ALGs, Carrier Grade NAT
(CGN), and virtual routing and forwarding (VRF) instances. No configuration
changes are required to enable asymmetric routing with ALGs, CGN, or VRF. For
more information, see the section, “Example: Configuring Asymmetric Routing
with VRF”.

 Feedback
Feedback