- About this Guide
-
- IPSec and ISAKMP
- L2TP over IPSec
- General VPN Parameters
- Connection Profiles, Group Policies, and Users
- IP Addresses for VPN
- Remote Access VPNs
- Network Admission Control
- Easy VPN on the ASA 5505
- PPPoE Client
- LAN-to-LAN VPNs
- AnyConnect VPN Client Connections
- AnyConnect Host Scan
- External Server for Authorization and Authentication
-
- Clientless SSL VPN Overview
- Basic Clientless SSL VPN Configuration
- Advanced Clientless SSL VPN Configuration
- Policy Groups
- Clientless SSL VPN Remote Users
- Clientless SSL VPN Users
- Clientless SSL VPN with Mobile Devices
- Customizing Clientless SSL VPN
- Clientless SSL VPN Troubleshooting
- Clientless SSL VPN Licensing
- Information About AnyConnect VPN Client Connections
- Licensing Requirements for AnyConnect Connections
- Guidelines and Limitations
- Configuring AnyConnect Connections
- Configuring the ASA to Web-Deploy the Client
- Enabling Permanent Client Installation
- Configuring DTLS
- Prompting Remote Users
- Enabling AnyConnect Client Profile Downloads
- Enabling AnyConnect Client Deferred Upgrade
- Enabling Additional AnyConnect Client Features
- Enabling Start Before Logon
- Translating Languages for AnyConnect User Messages
- Configuring Advanced AnyConnect SSL Features
- Updating AnyConnect Client Images
- Enabling IPv6 VPN Access
- Monitoring AnyConnect Connections
- Logging Off AnyConnect VPN Sessions
- Configuration Examples for Enabling AnyConnect Connections
- Feature History for AnyConnect Connections
AnyConnect VPN Client Connections
This section describes how to configure AnyConnect VPN Client Connections and covers the following topics:
- Information About AnyConnect VPN Client Connections
- Licensing Requirements for AnyConnect Connections
- Guidelines and Limitations
- Configuring AnyConnect Connections
- Configuring Advanced AnyConnect SSL Features
- Configuration Examples for Enabling AnyConnect Connections
- Feature History for AnyConnect Connections
Information About AnyConnect VPN Client Connections
The Cisco AnyConnect Secure Mobility Client provides secure SSL and IPsec/IKEv2 connections to the ASA for remote users. Without a previously-installed client, remote users enter the IP address in their browser of an interface configured to accept SSL or IPsec/IKEv2 VPN connections. Unless the ASA is configured to redirect http:// requests to https://, users must enter the URL in the form https://< address >.
After entering the URL, the browser connects to that interface and displays the login screen. If the user satisfies the login and authentication, and the ASA identifies the user as requiring the client, it downloads the client that matches the operating system of the remote computer. After downloading, the client installs and configures itself, establishes a secure SSL or IPsec/IKEv2 connection and either remains or uninstalls itself (depending on the configuration) when the connection terminates.
In the case of a previously installed client, when the user authenticates, the ASA examines the revision of the client, and upgrades the client as necessary.
When the client negotiates an SSL VPN connection with the ASA, it connects using Transport Layer Security (TLS), and optionally, Datagram Transport Layer Security (DTLS). DTLS avoids latency and bandwidth problems associated with some SSL connections and improves the performance of real-time applications that are sensitive to packet delays.
The AnyConnect client can be downloaded from the ASA, or it can be installed manually on the remote PC by the system administrator. For more information about installing the client manually, see the Cisco AnyConnect VPN Client Administrator Guide .
The ASA downloads the client based on the group policy or username attributes of the user establishing the connection. You can configure the ASA to automatically download the client, or you can configure it to prompt the remote user about whether to download the client. In the latter case, if the user does not respond, you can configure the ASA to either download the client after a timeout period or present the login page.
Licensing Requirements for AnyConnect Connections

Note This feature is not available on No Payload Encryption models.
|
– Base license or Security Plus license: 2 sessions. – Optional permanent or time-based licenses: 10 or 25 sessions. – Shared licenses are not supported.3
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, or 250 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, or 250 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, 250, 500, or 750 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, 250, 500, 750, 1000, or 2500 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, 250, 500, 750, 1000, 2500, or 5000 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, 250, 500, 750, 1000, 2500, or 5000 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, 250, 500, 750, 1000, 2500, 5000, or 10000 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
– Optional permanent or time-based licenses: 10, 25, 50, 100, 250, 500, 750, 1000, 2500, 5000, or 10000 sessions. – Optional Shared licenses 3 : Participant or Server. For the Server license, 500-50,000 in increments of 500 and 50,000-545,000 in increments of 1000.
|
|
|
1.If you start a clientless SSL VPN session and then start an AnyConnect client session from the portal, 1 session is used in total. However, if you start the AnyConnect client first (from a standalone client, for example) and then log into the clientless SSL VPN portal, then 2 sessions are used. 2.The maximum combined VPN sessions of all types cannot exceed the maximum sessions shown in this table. For the ASA 5505, the maximum combined sessions is 10 for the Base license, and 25 for the Security Plus license. 3.A shared license lets the ASA act as a shared license server for multiple client ASAs. The shared license pool is large, but the maximum number of sessions used by each individual ASA cannot exceed the maximum number listed for permanent licenses. 4.The AnyConnect Essentials license enables AnyConnect VPN client access to the ASA. This license does not support browser-based SSL VPN access or Cisco Secure Desktop. For these features, activate an AnyConnect Premium license instead of the AnyConnect Essentials license. |
Guidelines and Limitations
This section includes the guidelines and limitations for this feature.
Configuring AnyConnect Connections
This section describes prerequisites, restrictions, and detailed tasks to configure the ASA to accept AnyConnect VPN client connections.
Configuring the ASA to Web-Deploy the Client
The section describes the steps to configure the ASA to web-deploy the AnyConnect client.
Detailed Steps
Enabling Permanent Client Installation
Enabling permanent client installation disables the automatic uninstalling feature of the client. The client remains installed on the remote computer for subsequent connections, reducing the connection time for the remote user.
To enable permanent client installation for a specific group or user, use the anyconnect keep-installer command from group-policy or username webvpn modes:
anyconnect keep-installer installer
The default is that permanent installation of the client is enabled. The client remains on the remote computer at the end of the session. The following example configures the existing group-policy sales to remove the client on the remote computer at the end of the session:
Configuring DTLS
Datagram Transport Layer Security (DTLS) allows the AnyConnect client establishing an SSL VPN connection to use two simultaneous tunnels—an SSL tunnel and a DTLS tunnel. Using DTLS avoids latency and bandwidth problems associated with SSL connections and improves the performance of real-time applications that are sensitive to packet delays.
By default, DTLS is enabled when SSL VPN access is enabled on an interface. If you disable DTLS, SSL VPN connections connect with an SSL VPN tunnel only.

Note In order for DTLS to fall back to a TLS connection, Dead Peer Detection (DPD) must be enabled. If you do not enable DPD, and the DTLS connection experiences a problem, the connection terminates instead of falling back to TLS. For more information on enabling DPD, see Enabling and Adjusting Dead Peer Detection
You can disable DTLS for all AnyConnect client users with the enable command tls-only option in webvpn configuration mode:
hostname(config-webvpn)# enable outside tls-only
By default, DTLS is enabled for specific groups or users with the anyconnect ssl dtls command in group policy webvpn or username webvpn configuration mode:
[ no ] anyconnect ssl dtls {enable interface | none}
If you need to disable DTLS, use the no form of the command. For example:
Prompting Remote Users
You can enable the ASA to prompt remote SSL VPN client users to download the client with the anyconnect ask command from group policy webvpn or username webvpn configuration modes:
[ no ] anyconnect ask { none | enable [ default { webvpn | } timeout value ]}
anyconnect enable prompts the remote user to download the client or go to the clientless portal page and waits indefinitely for user response.
anyconnect ask enable default immediately downloads the client.
anyconnect ask enable default webvpn immediately goes to the portal page.
anyconnect ask enable default timeout value prompts the remote user to download the client or go to the clientless portal page and waits the duration of value before taking the default action—downloading the client.
anyconnect ask enable default clientless timeout value prompts the remote user to download the client or go to the clientless portal page, and waits the duration of value before taking the default action—displaying the clientless portal page.
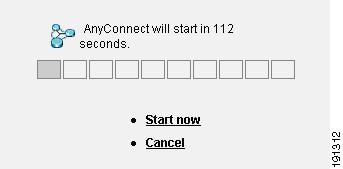
Figure 11-1 shows the prompt displayed to remote users when either default anyconnect timeout value or default webvpn timeout value is configured:
Figure 11-1 Prompt Displayed to Remote Users for SSL VPN Client Download
The following example configures the ASA to prompt the user to download the client or go to the clientless portal page and wait 10 seconds for a response before downloading the client:
Enabling AnyConnect Client Profile Downloads
You enable Cisco AnyConnect Secure Mobility client features in the AnyConnect profiles—XML files that contain configuration settings for the core client with its VPN functionality and for the optional client modules Network Access Manager (NAM), posture, telemetry, and Web Security. The ASA deploys the profiles during AnyConnect installation and updates. Users cannot manage or modify profiles.
You can configure a profile using the AnyConnect profile editor, a convenient GUI-based configuration tool launched from ASDM. The AnyConnect software package for Windows, version 2.5 and later, includes the editor, which activates when you load the AnyConnect package on the ASA and specify it as an AnyConnect client image.
We also provide a standalone version of the profile editor for Windows that you can use as an alternative to the profile editor integrated with ASDM. If you are predeploying the client, you can use the standalone profile editor to create profiles for the VPN service and other modules that you deploy to computers using your software management system. For more information about using the profile editor, see the Cisco AnyConnect Secure Mobility Client Administrator Guide .

Note The AnyConnect client protocol defaults to SSL. To enable IPsec IKEv2, you must configure the IKEv2 settings on the ASA and also configure IKEv2 as the primary protocol in the client profile. The IKEv2enabled profile must be deployed to the endpoint computer, otherwise the client attempts to connect using SSL. For more information, see the Cisco AnyConnect Secure Mobility Client Administrator Guide.
Follow these steps to edit a profile and enable the ASA to download it to remote clients:
Step 1 Use the profile editor from ASDM or the standalone profile editor to create a profile. For more information, see the Cisco AnyConnect Secure Mobility Client Administrator Guide.
Step 2 Load the profile file into flash memory on the ASA using tftp or another method.
Step 3 Use the anyconnect profiles command from webvpn configuration mode to identify the file as a client profile to load into cache memory.
The following example specifies the files sales_hosts.xml and engineering_hosts.xml as profiles:
The profiles are now available to group policies.
You can view the profiles loaded in cache memory using the dir cache:stc/profiles command:
Step 4 Enter group policy webvpn configuration mode and specify a client profile for a group policy with the anyconnect profiles command:
You can enter the anyconnect profiles value command followed by a question mark ( ? ) to view the available profiles. For example:
The next example configures the group policy to use the profile sales with the client profile type vpn :
Enabling AnyConnect Client Deferred Upgrade
Deferred Upgrade allows the AnyConnect user to delay download of a client upgrade. When a client update is available, AnyConnect opens a dialog asking the user if they would like to update, or to defer the upgrade.
Deferred Upgrade is enabled by adding custom attributes to the ASA, and then referencing and configuring those attributes in a group policy.
The following custom attributes support Deferred Upgrade:
Step 1 Create the custom attributes with the anyconnnect-custom-attr command in webvpn configuration mode:
[no] anyconnect-custom-attr attr-name [description description ]
The following example shows how to add the custom attribute DeferredUpdateAllowed :
Step 2 Add or remove the custom attributes to a group policy, and configure values for each attribute, using the anyconnect-custom command:
anyconnect-custom attr-name value value
The following example shows how to enable Deferred Update for the group policy named sales:
hostname(config-group-policy)# anyconnect-custom DeferredUpdateAllowed value true
Enabling Additional AnyConnect Client Features
To minimize download time, the client only requests downloads (from the ASA) of the core modules that it needs. As additional features become available for the AnyConnect client, you need to update the remote clients in order for them to use the features.
To enable new features, you must specify the new module names using the anyconnect modules command from group policy webvpn or username webvpn configuration mode:
[no ] anyconnect modules { none | value string }
Separate multiple strings with commas.
For a list of values to enter for each client feature, see the release notes for the Cisco AnyConnect VPN Client.
Enabling Start Before Logon
Start Before Logon (SBL) allows login scripts, password caching, drive mapping, and more, for the AnyConnect client installed on a Windows PC. For SBL, you must enable the ASA to download the module which enables graphical identification and authentication (GINA) for the AnyConnect client. The following procedure shows how to enable SBL:
Step 1 Enable the ASA to download the GINA module for VPN connection to specific groups or users using the anyconnect modules vpngina command from group policy webvpn or username webvpn configuration modes.
In the following example, the user enters group-policy attributes mode for the group policy telecommuters , enters webvpn configuration mode for the group policy, and specifies the string vpngina :
Step 2 Retrieve a copy of the client profiles file (AnyConnectProfile.tmpl).
Step 3 Edit the profiles file to specify that SBL is enabled. The example below shows the relevant portion of the profiles file (AnyConnectProfile.tmpl) for Windows:
The <UseStartBeforeLogon> tag determines whether the client uses SBL. To turn SBL on, replace false with true . The example below shows the tag with SBL turned on:
Step 4 Save the changes to AnyConnectProfile.tmpl and update the profile file for the group or user on the ASA using the profile command from webvpn configuration mode. For example:
Translating Languages for AnyConnect User Messages
The ASA provides language translation for the portal and screens displayed to users that initiate browser-based, Clientless SSL VPN connections, as well as the interface displayed to Cisco AnyConnect VPN Client users.
This section describes how to configure the ASA to translate these user messages and includes the following sections:
Understanding Language Translation
Functional areas and their messages that are visible to remote users are organized into translation domains. All messages displayed on the user interface of the Cisco AnyConnect VPN Client are located in the AnyConnect domain.
The software image package for the ASA includes a translation table template for the AnyConnect domain. You can export the template, which creates an XML file of the template at the URL you provide. The message fields in this file are empty. You can edit the messages and import the template to create a new translation table object that resides in flash memory.
You can also export an existing translation table. The XML file created displays the messages you edited previously. Reimporting this XML file with the same language name creates an new version of the translation table object, overwriting previous messages. Changes to the translation table for the AnyConnect domain are immediately visible to AnyConnect client users.
Creating Translation Tables
The following procedure describes how to create translation tables for the AnyConnect domain:
Step 1 Export a translation table template to a computer with the export webvpn translation-table command from privileged EXEC mode.
In the following example, the show webvpn translation-table command shows available translation table templates and tables.
Then the user exports the translation table for the AnyConnect translation domain. The filename of the XML file created is named client and contains empty message fields:
In the next example, the user exports a translation table named zh , which was previously imported from a template. zh is the abbreviation by Microsoft Internet Explorer for the Chinese language.
Step 2 Edit the Translation Table XML file. The following example shows a portion of the AnyConnect template. The end of this output includes a message ID field (msgid) and a message string field (msgstr) for the message Connected , which is displayed on the AnyConnect client GUI when the client establishes a VPN connection. The complete template contains many pairs of message fields:
The msgid contains the default translation. The msgstr that follows msgid provides the translation. To create a translation, enter the translated text between the quotes of the msgstr string. For example, to translate the message “Connected” with a Spanish translation, insert the Spanish text between the quotes:
Step 3 Import the translation table using the import webvpn translation-table command from privileged EXEC mode. Be sure to specify the name of the new translation table with the abbreviation for the language that is compatible with the browser.
In the following example, the XML file is imported es-us —the abbreviation used by Microsoft Internet Explorer for Spanish spoken in the United States.
Configuring Advanced AnyConnect SSL Features
The following section describes advanced features that fine-tune AnyConnect SSL VPN connections, and includes the following sections:
Enabling Rekey
When the ASA and the AnyConnect client client perform a rekey on an SSL VPN connection, they renegotiate the crypto keys and initialization vectors, increasing the security of the connection.
To enable the client to perform a rekey on an SSL VPN connection for a specific group or user, use the anyconnect ssl rekey command from group-policy or username webvpn modes.
[no]anyconnect ssl rekey { method { new-tunnel | none | ssl } | time minutes }
method new-tunnel specifies that the client establishes a new tunnel during rekey.
method ssl specifies that the client estanyablishes a new tunnel during rekey.

Note Configuring the rekey method as ssl or new-tunnel specifies that the client establishes a new tunnel during rekey instead of the SSL renegotiation taking place during the rekey. See the command reference for a history of the anyconnect ssl rekey command.
time minutes specifies the number of minutes from the start of the session, or from the last rekey, until the rekey takes place, from 1 to 10080 (1 week).
In the following example, the client is configured to renegotiate with SSL during rekey, which takes place 30 minutes after the session begins, for the existing group-policy sales :
Enabling and Adjusting Dead Peer Detection
Dead Peer Detection (DPD) ensures that the ASA (gateway) or the client can quickly detect a condition where the peer is not responding, and the connection has failed.
To enable DPD on the ASA or client for a specific group or user, and to set the frequency with which either the ASA or client performs DPD, use the anyconnect dpd-interval command from group-policy or username webvpn mode:
anyconnect dpd-interval {[ gateway { seconds | none }] | [ client { seconds | none }] }
gateway seconds enables DPD performed by the ASA (gateway) and specifies the frequency, from 5 to 3600 seconds, with which the ASA (gateway) performs DPD.
gateway none disables DPD performed by the ASA.
client seconds enable DPD performed by the client, and specifies the frequency, from 5 to 3600 seconds, with which the client performs DPD.
client none disables DPD performed by the client.
To remove the anyconnect dpd-interval command from the configuration, use the no form of the command:
no anyconnect dpd-interval {[ gateway { seconds | none }] | [ client { seconds | none }] }

Note If you enable DTLS, enable Dead Peer Detection (DPD) also. DPD enables a failed DTLS connection to fallback to TLS. Otherwise, the connection terminates.
The following example sets the frequency of DPD performed by the ASA to 30 seconds, and the frequency of DPD performed by the client set to 10 seconds for the existing group-policy sales :
Enabling Keepalive
You can adjust the frequency of keepalive messages to ensure that an SSL VPN connection through a proxy, firewall, or NAT device remains open, even if the device limits the time that the connection can be idle. Adjusting the frequency also ensures that the client does not disconnect and reconnect when the remote user is not actively running a socket-based application, such as Microsoft Outlook or Microsoft Internet Explorer.

Note Keepalives are enabled by default. If you disable keepalives, in the event of a failover event, SSL VPN client sessions are not carried over to the standby device.
To set the frequency of keepalive messages, use the keepalive command from group-policy webvpn or username webvpn configuration mode:
[no] anyconnect ssl keepalive {none | seconds }
none disables client keepalive messages.
seconds enables the client to send keepalive messages, and specifies the frequency of the messages in the range of 15 to 600 seconds.
The default is keepalive messages are enabled.
Use the no form of the command to remove the command from the configuration and cause the value to be inherited:
In the following example, the ASA is configured to enable the client to send keepalive messages with a frequency of 300 seconds (5 minutes), for the existing group-policy sales :
Using Compression
Compression increases the communications performance between the ASA and the client by reducing the size of the packets being transferred for low-bandwidth connections. By default, compression for all SSL VPN connections is enabled on the ASA, both at the global level and for specific groups or users.

Note When implementing compression on broadband connections, you must carefully consider the fact that compression relies on loss-less connectivity. This is the main reason that it is not enabled by default on broadband connections.
Compression must be turned-on globally using the anyconnect ssl compression command from global configuration mode, and then it can be set for specific groups or users with the anyconnect ssl compression command in group-policy and username webvpn modes.
To change the global compression settings, use the anyconnect ssl compression command from global configuration mode:
To remove the command from the configuration, use the no form of the command.
In the following example, compression is disabled for all SSL VPN connections globally:
Changing Compression for Groups and Users
To change compression for a specific group or user, use the anyconnect ssl compression command in the group-policy and username webvpn modes:
anyconnect ssl compression {deflate | none}
no anyconnect ssl compression {deflate | none}
By default, for groups and users, SSL compression is set to deflate (enabled).
To remove the anyconnect ssl compression command from the configuration and cause the value to be inherited from the global setting, use the no form of the command:
In the following example, compression is disabled for the group-policy sales:
Adjusting MTU Size
You can adjust the MTU size (from 256 to 1406 bytes) for SSL VPN connections established by the client with the anyconnect mtu command from group policy webvpn or username webvpn configuration mode:
This command affects only the AnyConnect client. The legacy Cisco SSL VPN Client () is not capable of adjusting to different MTU sizes.
The default for this command in the default group policy is no anyconnect mtu . The MTU size is adjusted automatically based on the MTU of the interface that the connection uses, minus the IP/UDP/DTLS overhead.
This command affects client connections established in SSL and those established in SSL with DTLS.
Examples
The following example configures the MTU size to 1200 bytes for the group policy telecommuters :
Updating AnyConnect Client Images
You can update the client images on the ASA at any time using the following procedure:
Step 1 Copy the new client images to the ASA using the copy command from privileged EXEC mode, or using another method.
Step 2 If the new clientt image files have the same filenames as the files already loaded, reenter the anyconnect image command that is in the configuration. If the new filenames are different, uninstall the old files using the no anyconnect image command. Then use the anyconnect image command to assign an order to the images and cause the ASA to load the new images.
Enabling IPv6 VPN Access
If you want to configure IPv6 access, you must use the command-line interface. Release 9.0(x) of the ASA adds support for IPv6 VPN connections to its outside interface using SSL and IKEv2/IPsec protocols.
You enable IPv6 access using the ipv6 enable command as part of enabling SSL VPN connections. The following is an example for an IPv6 connection that enables IPv6 on the outside interface:
To enable IPV6 SSL VPN, do the following general actions:
1. Enable IPv6 on the outside interface.
2. Enable IPv6 and an IPv6 address on the inside interface.
3. Configure an IPv6 address local pool for client assigned IP Addresses.
4. Configure an IPv6 tunnel default gateway.
To implement this procedure, do the following steps:
Step 2 Configure an 'ipv6 local pool' (used for IPv6 address assignment):

Note You can configure the ASA to assign an IPv4 address, an IPv6 address, or both an IPv4 and an IPv6 address to an AnyConnect client by creating internal pools of addresses on the ASA or by assigning a dedicated address to a local user on the ASA.
Step 3 Add the ipv6 address pool to your tunnel group policy (or group-policy):

Note You must also configure an IPv4 address pool here as well (using the 'address-pool' command).
Step 4 Configure an IPv6 tunnel default gateway:
Monitoring AnyConnect Connections
To view information about active sessions use the show vpn-sessiondb :
Logging Off AnyConnect VPN Sessions
To log off all VPN sessions, use the vpn-sessiondb logoff command in global configuration mode:
The following example logs off all VPN sessions:
You can log off individual sessions using either the name argument or the index argument:
vpn-session-db logoff name name
vpn-session-db logoff index index
The sessions that have been inactive the longest time are marked as idle (and are automatically logged off) so that license capacity is not reached and new users can log in. If the session resumes at a later time, it is removed from the inactive list.
You can find both the username and the index number (established by the order of the client images) in the output of the show vpn-sessiondb anyconnect command. The following examples shows the username lee and index number 1 .
The following example terminates the session using the name option of the vpn-session-db logoff command:
Configuration Examples for Enabling AnyConnect Connections
The following example shows how to configure L2TP over IPsec:
Feature History for AnyConnect Connections
Table 11-2 lists the release history for this feature.
 Feedback
Feedback