Overview
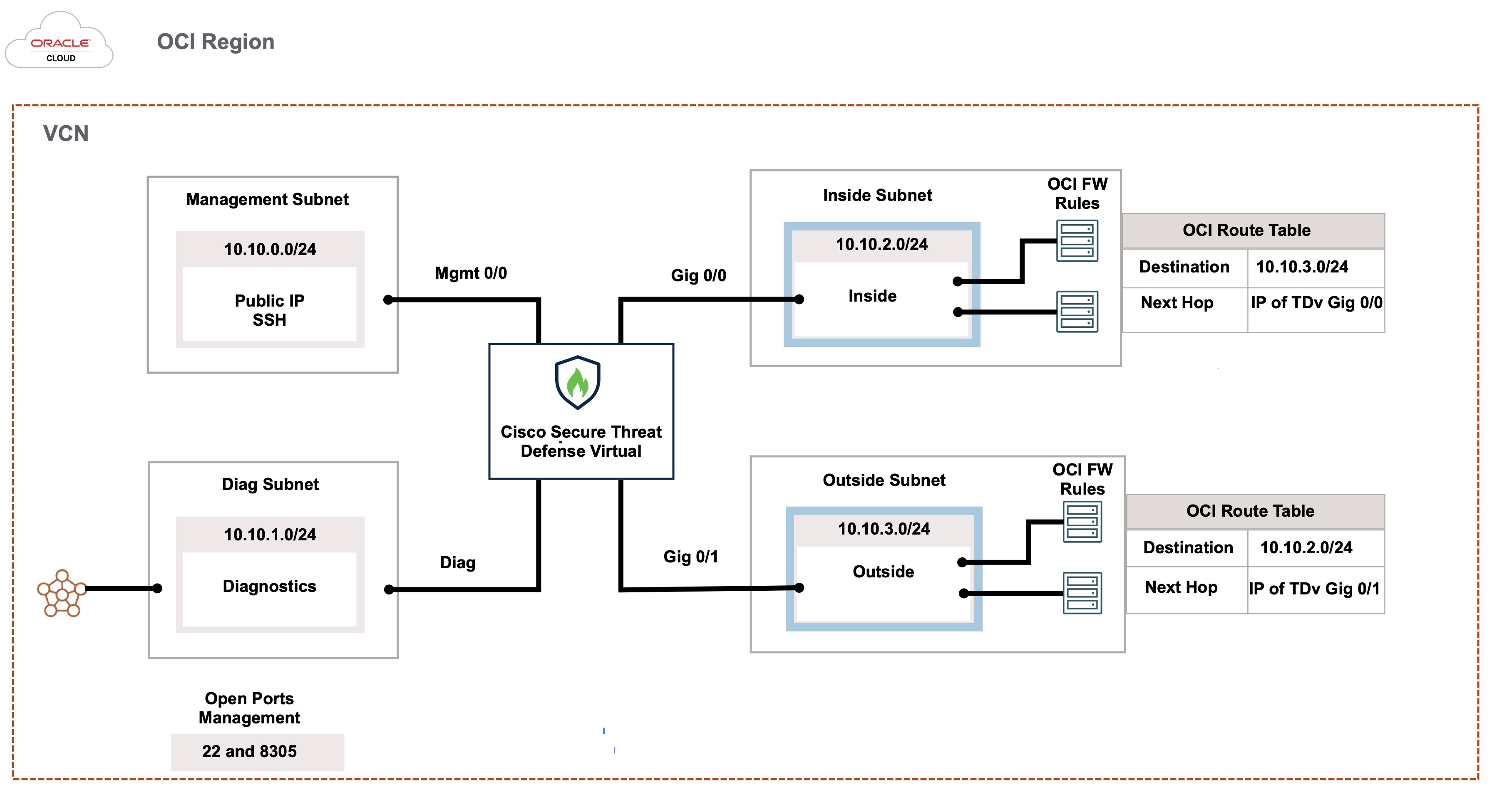
The Cisco Secure Firewall Threat Defense Virtual runs the same software as physical Cisco threat defense to deliver proven security functionality in a virtual form factor. The threat defense virtual can be deployed in the public OCI. It can then be configured to protect virtual and physical data center workloads that expand, contract, or shift their location over time.
OCI Compute Shapes
A shape is a template that determines the number of CPUs, amount of memory, and other resources that are allocated to an instance. The threat defense virtual support the following OCI shape types:
|
OCI Shape |
Supported Threat Defense Virtual version |
Attributes |
Interfaces |
|
|---|---|---|---|---|
|
oCPUs |
RAM (GB) |
|||
|
Intel VM.Standard2.4 |
7.1, 7.2.x, and 7.3.x |
4 |
60 |
Minimum 4, Maximum 4 |
|
Intel VM.Standard2.8 |
7.1, 7.2.x, and 7.3.x |
8 |
120 |
Minimum 4, Maximum 8 |
-
*SR-IOV mode is supported with Flex shapes from Version 7.4.x and later.
-
In OCI, 1 oCPU is equal to 2 vCPU.
-
The threat defense virtual requires a minimum of 4 interfaces.
You create an account on OCI, launch a compute instance using the Cisco Firepower NGFW virtual firewall (NGFWv) offering on the Oracle Cloud Marketplace, and choose an OCI shape.





















 Feedback
Feedback