Integrate with Cisco SecureX
View and work with data from all of your Cisco security products and more through a single pane of glass, the SecureX cloud portal. Use the tools available via SecureX to enrich your threat hunts and investigations. SecureX can also provide useful appliance and device information such as whether each is running an optimal software version.
For more information about SecureX, see Cisco SecureX page.
Enable SecureX Integration
The Cisco SecureX platform connects the breadth of Cisco's integrated security portfolio and your infrastructure for a consistent experience that unifies visibility, enables automation, and strengthens your security across network, endpoints, cloud, and applications. For more information about SecureX, see the Cisco SecureX product page.
Integrating SecureX with the management center provides you a complete overview of all the data from the management center. For more information about integrating the management center with SecureX, see the Cisco Secure Firewall Management Center (Version 7.2 and later) and SecureX Integration Guide.
Before you begin
You need a SecureX account that belongs to an organization. If you don't have a SecureX account, create a SecureX account using your CDO tenant. See Create a SecureX Account Using CDO for more information.
Procedure
|
Step 1 |
In the management center, choose . |
|
Step 2 |
(Optional) For the Cloud Region, choose your Current Region. The region selected by default matches your Smart Licensing region, so you probably do not need to change the region. |
|
Step 3 |
In SecureX Enablement, perform the following steps. |
Configure the Management Center to Send Events to the Cisco Security Cloud
Configure your management center to have the managed threat defense devices send events directly to Cisco Security Cloud. The cloud region and event types that you configure in this page can be used for multiple integrations when applicable and enabled.
Before you begin
-
Ensure that you register the management center with the Smart License (System (
 )) or enable Cisco Security Cloud integration to allow your devices to send firewall events to the Cisco cloud.
)) or enable Cisco Security Cloud integration to allow your devices to send firewall events to the Cisco cloud.
-
In the management center:
-
Go to the System > Configuration page and give your management center a unique name to clearly identify it in the Devices list in the cloud.
-
Add your threat defense devices to the management center, assign licenses to them, and ensure that the system is working correctly. Ensure that you have created the necessary policies and the generated events are displayed as expected in the management center UI under the Analysis menu.
-
-
Ensure that you have your Cisco security cloud sign on credentials and can sign in to the SecureX regional cloud in which your account was created.
For more information on SecureX regional cloud URLs and supported device versions, see Cisco Secure Firewall Management Center and SecureX Integration Guide.
-
If you are currently sending events to the cloud using syslog, disable it to avoid duplication.
Procedure
|
Step 1 |
Determine the Cisco regional cloud you want to use for sending firewall events. For more information for choosing a regional cloud, see Cisco Secure Firewall Management Center and SecureX Integration Guide.
|
|||||||||||||
|
Step 2 |
In your management center, click . |
|||||||||||||
|
Step 3 |
Choose a regional cloud from the Current Region drop-down list. |
|||||||||||||
|
Step 4 |
Check the Send events to the cloud check box to enable the cloud event configuration. |
|||||||||||||
|
Step 5 |
Select the event types that you want to send to the cloud.
|
|||||||||||||
|
Step 6 |
Click Save. |
Configure Cisco Success Network Enrollment
Cisco Success Network is a cloud service that enables the management center to establish a secure connection to Cisco cloud and stream usage information and statistics. Streaming this telemetry provides a mechanism to select data of interest from the threat defense device and send it in a structured format to remote management stations for the following reasons:
-
To inform you of available, but unused features that can improve the effectiveness of the product in your network.
-
To inform you of additional technical support services and monitoring that are available for your product.
-
(If you integrate with SecureX) To summarize appliance and device status in SecureX tiles and know whether all your devices are running optimal software versions.
-
To help Cisco improve its products.
To know more about the telemetry data that Cisco collects, see Cisco Success Network Telemetry Data Collected from Cisco Secure Firewall Management Center Devices.
The management center establishes and maintains a secure connection with Cisco cloud at all times when either Cisco Support Diagnostics or Cisco Success Network is enabled. However, the management center and the threat defense devices establish and maintain secure connections with the Cisco cloud when Cisco Support Diagnostics is enabled. You can turn off this connection at any time by disabling both Cisco Success Network and Cisco Support Diagnostics, which disconnects the management center from the Cisco cloud.
You can enable Cisco Success Network when you register the management center with the Smart Software Manager.
 Note |
|
Before you begin
Enable SecureX integration or register your management center with the Smart License to perform this task.
Procedure
|
Step 1 |
Click . |
||
|
Step 2 |
Under Cisco Cloud Support, check the Enable Cisco Success Network check box to enable this service.
|
||
|
Step 3 |
Click Save. |
Configure Cisco Support Diagnostics Enrollment
Cisco Support Diagnostics is a user-enabled cloud-based TAC support service. When enabled, the management center and the managed devices establish a secure connection with the Cisco cloud to stream system health-related information.
Cisco Support Diagnostics provides an enhanced user experience during troubleshooting by allowing Cisco TAC to securely collect essential data from your device during the resolution of a TAC case. Moreover, Cisco periodically collects health data, and processes this data using an automated problem-detection system to notify you of issues if any. While data collection service during the resolution of a TAC case is available for all users with support contracts, the notification service is available only to users with specific service contracts.
Cisco Support Diagnostics allows both threat defense devices and the management center to establish and maintain secure connections with the Cisco cloud. The management center sends the collected data to the regional cloud selected on the SecureX Integration page.
You can turn off this connection at any time by disabling both Cisco Success Network and Cisco Support Diagnostics, which disconnect these features from the Cisco cloud.
Administrators can view a sample data set collected from the management center by following the steps in Producing Troubleshooting Files for Specific System Functions.
Before you begin
Enable SecureX integration or register your management center with the Smart License to perform this task.
Procedure
|
Step 1 |
Click . |
||
|
Step 2 |
Under Cisco Cloud Support, check the Enable Cisco Support Diagnostics check box to enable this service.
|
||
|
Step 3 |
Click Save. |
Access SecureX Using the Ribbon
The ribbon appears at the bottom of every page in the management center web interface. You can use the ribbon to quickly pivot to other Cisco security products and work with threat data from multiple sources.
Before you begin
-
If you do not see the SecureX ribbon at the bottom of management center web interface pages, do not use this procedure.
Instead, see the Cisco Secure Firewall Threat Defense and SecureX Integration Guide.
-
If you don't already have a SecureX account, obtain one from your IT department.
Procedure
|
Step 1 |
In management center, click the ribbon at the bottom of any management center page. |
|
Step 2 |
Click Get SecureX. |
|
Step 3 |
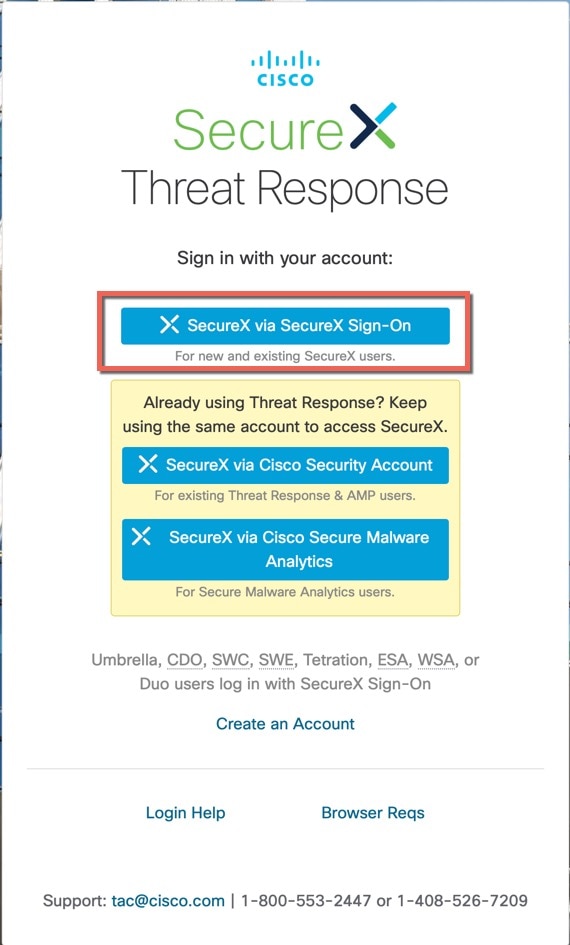
Sign in to SecureX. |
|
Step 4 |
Click the link to authorize access. |
|
Step 5 |
Click the ribbon to expand and use it. |
What to do next
For information about ribbon features and how to use them, see the online help in SecureX.



 )
) )
) )
) )
)
 )
) )
) Feedback
Feedback