- New and Changed Information
- Index
- Preface
- Overview
- Configuring AAA
- Configuring RADIUS
- Configuring TACACS+
- Configuring User Accounts and RBAC
- Configuring 802.1X
- Configuring IP ACLs
- Configuring MAC ACLs
- Configuring VLAN ACLs
- Configuring Port Security
- Configuring DHCP Snooping
- Configuring Dynamic ARP Inspection
- Configuring Source Guard
- Configuring Keychain Management
- Configuring Traffic Storm Control
Cisco DCNM Security Configuration Guide, Release 4.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- December 19, 2008
Chapter: Configuring User Accounts and RBAC
Configuring RBAC
This chapter describes how to configure user accounts and role-based access control (RBAC) on NX-OS devices.
This chapter includes the following sections:
•![]() Information About User Accounts and RBAC
Information About User Accounts and RBAC
•![]() Licensing Requirements for User Accounts and RBAC
Licensing Requirements for User Accounts and RBAC
•![]() Feature History for User Accounts and RBAC
Feature History for User Accounts and RBAC
Information About User Accounts and RBAC
You can create and manage users accounts and assign roles that limit access to operations on the NX-OS device. RBAC allows you to define the rules for an assign role that restrict the authorization that the user has to access management operations.
This section includes the following topics:
•![]() Characteristics of Strong Passwords
Characteristics of Strong Passwords
About User Accounts
You can configure up to a maximum of 256 user accounts. By default, the user account does not expire unless you explicitly configure it to expire. The expire option determines the date when the user account is disabled.
Users can have user accounts on multiple VDCs. These users can move between VDCs after an initial connection to a VDC.
The Cisco NX-OS software provides two default user accounts, admin and adminbackup.

Tip ![]() The following words are reserved and cannot be used to configure users: bin, daemon, adm, lp, sync, shutdown, halt, mail, news, uucp, operator, games, gopher, ftp, nobody, nscd, mailnull, rpc, rpcuser, xfs, gdm, mtsuser, ftpuser, man, and sys.
The following words are reserved and cannot be used to configure users: bin, daemon, adm, lp, sync, shutdown, halt, mail, news, uucp, operator, games, gopher, ftp, nobody, nscd, mailnull, rpc, rpcuser, xfs, gdm, mtsuser, ftpuser, man, and sys.

Note ![]() User passwords are not displayed in the configuration files.
User passwords are not displayed in the configuration files.

Characteristics of Strong Passwords
A strong password has the following characteristics:
•![]() At least eight characters long
At least eight characters long
•![]() Does not contain many consecutive characters (such as "abcd")
Does not contain many consecutive characters (such as "abcd")
•![]() Does not contain many repeating characters (such as "aaabbb")
Does not contain many repeating characters (such as "aaabbb")
•![]() Does not contain dictionary words
Does not contain dictionary words
•![]() Does not contain proper names
Does not contain proper names
•![]() Contains both uppercase and lowercase characters
Contains both uppercase and lowercase characters
•![]() Contains numbers
Contains numbers
The following are examples of strong passwords:
•![]() If2CoM18
If2CoM18
•![]() 2004AsdfLkj30
2004AsdfLkj30
•![]() Cb1955S21
Cb1955S21

Note ![]() Clear text passwords cannot include the dollar sign ($) special character.
Clear text passwords cannot include the dollar sign ($) special character.

Tip ![]() If a password is trivial (such as a short, easy-to-decipher password), the NX-OS software will reject your password configuration if password-strength checking is enabled. Be sure to configure a strong password as shown in the sample configuration. Passwords are case sensitive.
If a password is trivial (such as a short, easy-to-decipher password), the NX-OS software will reject your password configuration if password-strength checking is enabled. Be sure to configure a strong password as shown in the sample configuration. Passwords are case sensitive.
About User Roles
User roles contain rules that define the operations allowed for the user who is assigned the role. Each user role can contain multiple rules and each user can have multiple roles. For example, if role1 allows access only to configuration operations, and role2 allows access only to debug operations, then users who belong to both role1 and role2 can access configuration and debug operations. You can also limit access to specific VLANs, virtual routing and forwarding instances (VRFs), and interfaces.
The Cisco NX-OS software provides four default user roles:
•![]() network-admin—Complete read-and-write access to the entire NX-OS device (only available in the default VDC)
network-admin—Complete read-and-write access to the entire NX-OS device (only available in the default VDC)
•![]() network-operator—Complete read access to the entire NX-OS device (only available in the default VDC)
network-operator—Complete read access to the entire NX-OS device (only available in the default VDC)
•![]() vdc-admin—Read-and-write access limited to a VDC
vdc-admin—Read-and-write access limited to a VDC
•![]() vdc-operator—Read access limited to a VDC
vdc-operator—Read access limited to a VDC

Note ![]() You cannot change the default user roles.
You cannot change the default user roles.
You can create custom roles within a VDC. By default, the user roles that you create do not allow access to any device operations. You must add rules to allow users to display or configure features.
The VDCs do not share user roles. Each VDC maintains an independent user role database. Within a VDC, roles are configured by rule and attribute assignment.

Note ![]() If you belong to multiple roles, you can execute a combination of all the commands permitted by these roles. Access to a command takes priority over being denied access to a command. For example, suppose a user has RoleA, which denied access to the configuration commands. However, the user also has RoleB, which has access to the configuration commands. In this case, the user has access to the configuration commands.
If you belong to multiple roles, you can execute a combination of all the commands permitted by these roles. Access to a command takes priority over being denied access to a command. For example, suppose a user has RoleA, which denied access to the configuration commands. However, the user also has RoleB, which has access to the configuration commands. In this case, the user has access to the configuration commands.
About User Role Rules
The rule is the basic element of a role. A rule defines what operations the role allows the user to perform. You can apply rules for the following parameters:
•![]() Command—A command or group of commands defined in a regular expression.
Command—A command or group of commands defined in a regular expression.
•![]() Feature—Commands that apply to a function provided by the NX-OS software.
Feature—Commands that apply to a function provided by the NX-OS software.
•![]() Feature group—Default or user-defined group of features.
Feature group—Default or user-defined group of features.
These parameters create a hierarchical relationship. The most basic control parameter is the command. The next control parameter is the feature, which represents all commands associated with the feature. The last control parameter is the feature group. The feature group combines related features and allows you to easily manage the rules. The NX-OS software also supports the predefined feature group L3 that you can use.
You can configure up to 256 rules for each role. The user-specified rule number determines the order in which the rules are applied. Rules are applied in descending order. For example, if a role has three rules, rule 3 is applied before rule 2, which is applied before rule 1.
Virtualization Support
The users with the network-admin and network-operator roles can operate in all virtual device contexts (VDCs) when logged in from the default VDC. All other user roles are local to the VDC. Roles are not shared between VDCs. Each VDC maintains an independent user role database. For more information on VDCs, see the Cisco DCNM Virtual Device Context Configuration Guide, Release 4.1.
Licensing Requirements for User Accounts and RBAC
The following table shows the licensing requirements for this feature:
Guidelines and Limitations
User accounts and RBAC have the following configuration guidelines and limitations:
•![]() You can create up to 64 user-defined roles in a VDC in addition to the four default user roles in the default VDC and the two default user roles in the nondefault VDCs.
You can create up to 64 user-defined roles in a VDC in addition to the four default user roles in the default VDC and the two default user roles in the nondefault VDCs.
•![]() You can add up to 256 rules to a user role.
You can add up to 256 rules to a user role.
•![]() You can add up to 64 user-defined feature groups to a VDC in addition to the default feature group, L3.
You can add up to 64 user-defined feature groups to a VDC in addition to the default feature group, L3.
•![]() You can configure up to 256 users in a VDC.
You can configure up to 256 users in a VDC.
•![]() You can assign a maximum of 64 user roles to a user account.
You can assign a maximum of 64 user roles to a user account.
•![]() If you have a user account configured on the local Cisco NX-OS device that has the same name as a remote user account on an AAA server, the Cisco NX-OS software applies the user roles for the local user account to the remote user, not the user roles configured on the AAA server.
If you have a user account configured on the local Cisco NX-OS device that has the same name as a remote user account on an AAA server, the Cisco NX-OS software applies the user roles for the local user account to the remote user, not the user roles configured on the AAA server.
•![]() You cannot delete the default admin or adminbackup user account.
You cannot delete the default admin or adminbackup user account.
•![]() You cannot remove the default user roles from the default admin or adminbackup user account.
You cannot remove the default user roles from the default admin or adminbackup user account.
•![]() You cannot change the default user roles network-admin, vdc-admin, network-operator, and vdc-operator.
You cannot change the default user roles network-admin, vdc-admin, network-operator, and vdc-operator.
Configuring User Accounts
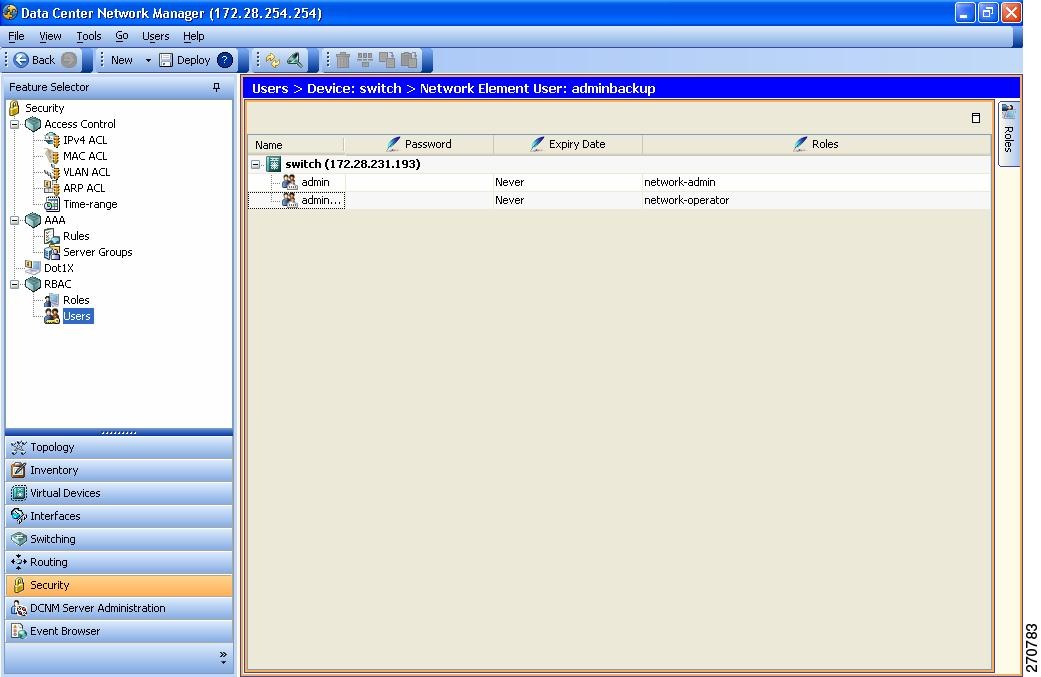
You can configure user accounts for the NX-OS device. Figure 5-1 shows the Users pane.
Figure 5-1 Users Pane
This section includes the following topics:
•![]() Changing a User Account Password
Changing a User Account Password
•![]() Changing a User Account Expiry Date
Changing a User Account Expiry Date
Creating a User Account
You can create a maximum of 256 user accounts on an NX-OS device. User accounts have the following attributes:
•![]() Username
Username
•![]() Password
Password
•![]() Expiry date
Expiry date
•![]() User roles
User roles
The username is a case-sensitive, alphanumeric character string with a maximum length of 28 characters.
User accounts can have a maximum of 64 user roles.
User accounts are local to a VDC. However, users with the network-admin or network-operator role can log in to the default VDC and access other VDCs.
For more information on user roles, see the "Configuring Roles" section.

Note ![]() If you do not specify a password, the user might not be able to log in to the NX-OS device.
If you do not specify a password, the user might not be able to log in to the NX-OS device.
DETAILED STEPS
To create a user account, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Users.
From the Feature Selector pane, choose Security > RBAC > Users.
Step 2 ![]() From the Summary pane, double-click the device to display the users.
From the Summary pane, double-click the device to display the users.
Step 3 ![]() From the menu bar, choose File > New > Add User.
From the menu bar, choose File > New > Add User.
A new row appears in the list of users.
Step 4 ![]() Enter the username.
Enter the username.
The maximum length of the username is 28 characters.
Step 5 ![]() Double-click the Password cell and click the down arrow to display the password dialog box (see Figure 5-2).
Double-click the Password cell and click the down arrow to display the password dialog box (see Figure 5-2).
Figure 5-2 Password Dialog Box
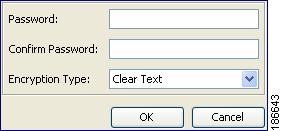
Step 6 ![]() From the password dialog box, enter the password in the Password and Confirm Password fields.
From the password dialog box, enter the password in the Password and Confirm Password fields.
Step 7 ![]() From the Encryption Type menu list, choose Clear Text or Strongly Encrypted.
From the Encryption Type menu list, choose Clear Text or Strongly Encrypted.
Step 8 ![]() Click OK.
Click OK.
Step 9 ![]() Double-click the Expiry Date cell and click the down arrow to display the expiry date dialog box (see Figure 5-3).
Double-click the Expiry Date cell and click the down arrow to display the expiry date dialog box (see Figure 5-3).
Figure 5-3 Expiry Date Dialog Box
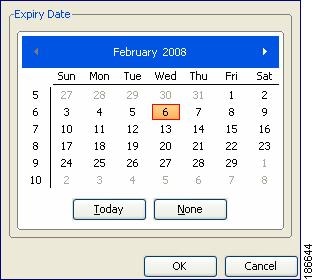
Step 10 ![]() Navigate to the desired expiry date and click OK.
Navigate to the desired expiry date and click OK.
The default expiry date is Never.
Step 11 ![]() Double-click the Roles cell and click the down arrow to display the user role dialog box (see Figure 5-4).
Double-click the Roles cell and click the down arrow to display the user role dialog box (see Figure 5-4).
Figure 5-4 User Role Dialog Box
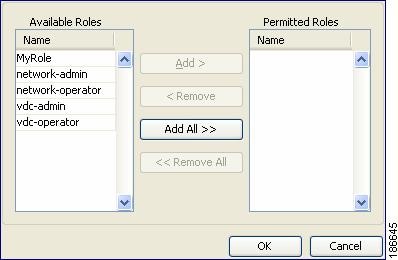
Step 12 ![]() Choose one or more user roles by moving them to the Permitted column and click OK.
Choose one or more user roles by moving them to the Permitted column and click OK.
Step 13 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Copying a User Account
You can copy the configuration of a user account from one NX-OS device to another NX-OS device.
BEFORE YOU BEGIN
Create one or more user accounts (see the "Creating a User Account" section).
Ensure that the roles assigned to the user account exist on the target device (see the "Creating a User Role" section).
DETAILED STEPS
To copy the configuration of a user account, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Users.
From the Feature Selector pane, choose Security > RBAC > Users.
Step 2 ![]() From the Summary pane, double-click the device to display the users.
From the Summary pane, double-click the device to display the users.
Step 3 ![]() Click on the user account that you want to copy.
Click on the user account that you want to copy.
Step 4 ![]() From the menu bar, choose Actions > Copy.
From the menu bar, choose Actions > Copy.
Step 5 ![]() Click the destination device.
Click the destination device.
Step 6 ![]() From the menu bar, choose Actions > Paste.
From the menu bar, choose Actions > Paste.
The user account appears in the list of users for the device.
Step 7 ![]() Double-click the Password cell and click the down arrow to display the password dialog box (see Figure 5-5).
Double-click the Password cell and click the down arrow to display the password dialog box (see Figure 5-5).
Figure 5-5 Password Dialog Box
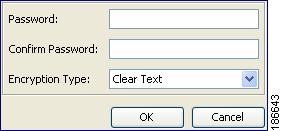
Step 8 ![]() From the password dialog box, enter the password in the Password and Confirm Password fields.
From the password dialog box, enter the password in the Password and Confirm Password fields.
Step 9 ![]() From the Encryption Type menu list, choose Clear Text or Strongly Encrypted.
From the Encryption Type menu list, choose Clear Text or Strongly Encrypted.
Step 10 ![]() Click OK.
Click OK.
Step 11 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Changing a User Account Password
You can change the password for any user account if you have network-admin privileges in the default VDC or for VDC user accounts if you have vdc-admin privileges.

Note ![]() Changes to user account password do not take effect until the user logs in and creates a new session.
Changes to user account password do not take effect until the user logs in and creates a new session.
BEFORE YOU BEGIN
Create one or more user accounts (see the "Creating a User Account" section).
DETAILED STEPS
To change user account passwords, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Users.
From the Feature Selector pane, choose Security > RBAC > Users.
Step 2 ![]() From the Summary pane, double-click the device to display the users.
From the Summary pane, double-click the device to display the users.
Step 3 ![]() Click the user account to change.
Click the user account to change.
Step 4 ![]() Double-click the Password cell and click the down arrow to display the password dialog box (see Figure 5-2).
Double-click the Password cell and click the down arrow to display the password dialog box (see Figure 5-2).
Step 5 ![]() From the password dialog box, enter the password in the Password and Confirm Password fields.
From the password dialog box, enter the password in the Password and Confirm Password fields.
Step 6 ![]() From the Encryption Type menu list, choose Clear Text or Strongly Encrypted and click OK.
From the Encryption Type menu list, choose Clear Text or Strongly Encrypted and click OK.
Step 7 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Changing a User Account Expiry Date
You can change the expiry date for any user account if you have network-admin privileges in the default VDC or you can change the expiry date for a VDC user account if you have vdc-admin privileges.

Note ![]() Changes to the user account expiry date do not take effect until the user logs in and creates a new session.
Changes to the user account expiry date do not take effect until the user logs in and creates a new session.

Note ![]() You cannot change expiry date for the default admin user account.
You cannot change expiry date for the default admin user account.
BEFORE YOU BEGIN
Create one or more user accounts (see the "Creating a User Account" section).
DETAILED STEPS
To change a user account expiry date, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Users.
From the Feature Selector pane, choose Security > RBAC > Users.
Step 2 ![]() From the Summary pane, double-click the device to display the users.
From the Summary pane, double-click the device to display the users.
Step 3 ![]() Click the user account to change.
Click the user account to change.
Step 4 ![]() Double-click the Expiry Date cell and click the down arrow to display the expiry date dialog box (see Figure 5-3).
Double-click the Expiry Date cell and click the down arrow to display the expiry date dialog box (see Figure 5-3).
Step 5 ![]() Navigate to the desired expiry date and click OK.
Navigate to the desired expiry date and click OK.
The default expiry date is Never.
Step 6 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Adding a User Account Role
You can add roles to a user account if you have network-admin privileges in the default VDC or you can add roles for VDC user accounts if you have vdc-admin privileges.

Note ![]() Changes to user account roles do not take effect until the user logs in and creates a new session.
Changes to user account roles do not take effect until the user logs in and creates a new session.

Note ![]() You cannot add a role to the default admin user account.
You cannot add a role to the default admin user account.
BEFORE YOU BEGIN
Create one or more user accounts (see the "Creating a User Account" section).
DETAILED STEPS
To add a user account role, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Users.
From the Feature Selector pane, choose Security > RBAC > Users.
Step 2 ![]() From the Summary pane, double-click the device to display the users.
From the Summary pane, double-click the device to display the users.
Step 3 ![]() Click the user account to change.
Click the user account to change.
Step 4 ![]() Double-click the Roles cell and click the down arrow to display the user roles dialog box (see Figure 5-4).
Double-click the Roles cell and click the down arrow to display the user roles dialog box (see Figure 5-4).
Step 5 ![]() Choose one or more user roles by moving them to the Permitted Roles column and click OK.
Choose one or more user roles by moving them to the Permitted Roles column and click OK.
Step 6 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Deleting a User Account Role
You can delete the roles from a user account if you have network-admin privileges in the default VDC or for VDC user accounts if you have vdc-admin privileges.

Note ![]() Changes to a user account role do not take effect until the user logs in and creates a new session.
Changes to a user account role do not take effect until the user logs in and creates a new session.

Note ![]() You cannot delete the network-admin role from the default admin user account in the default VDC or the vdc-admin role from the default admin user account in nondefault VDCs.
You cannot delete the network-admin role from the default admin user account in the default VDC or the vdc-admin role from the default admin user account in nondefault VDCs.
BEFORE YOU BEGIN
Create one or more user accounts (see the "Creating a User Account" section).
Add a role to the user account (see the "Adding a User Account Role" section.
DETAILED STEPS
To delete a user account role, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Users.
From the Feature Selector pane, choose Security > RBAC > Users.
Step 2 ![]() From the Summary pane, double-click the device to display the users.
From the Summary pane, double-click the device to display the users.
Step 3 ![]() Click the user account to change.
Click the user account to change.
Step 4 ![]() Double-click the Roles cell and click the down arrow to display the user roles dialog box (see Figure 5-4).
Double-click the Roles cell and click the down arrow to display the user roles dialog box (see Figure 5-4).
Step 5 ![]() Delete one or more user roles by moving them to the Available Roles column and click OK.
Delete one or more user roles by moving them to the Available Roles column and click OK.
Step 6 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Deleting a User Account
You can delete a user account.

Note ![]() You cannot delete the default admin user account.
You cannot delete the default admin user account.
BEFORE YOU BEGIN
Create one or more user accounts (see the "Creating a User Account" section).
DETAILED STEPS
To delete a user account, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Users.
From the Feature Selector pane, choose Security > RBAC > Users.
Step 2 ![]() From the Summary pane, double-click the device to display the users.
From the Summary pane, double-click the device to display the users.
Step 3 ![]() Click the user account to delete.
Click the user account to delete.
Step 4 ![]() From the top menu bar, choose Users > Delete User and click Yes in the confirmation dialog.
From the top menu bar, choose Users > Delete User and click Yes in the confirmation dialog.
The user account name disappears from the user account list.
Step 5 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Configuring Roles
You can configure user roles on your NX-OS device.
Figure 5-6 shows the RBAC Roles content pane.
Figure 5-6 Roles Content Pane

This section includes the following topics:
•![]() Changing a Rule in a User Role
Changing a Rule in a User Role
•![]() Rearranging a Rule in a User Role
Rearranging a Rule in a User Role
•![]() Deleting a Rule from a User Role
Deleting a Rule from a User Role
•![]() Changing a User Role Interface Policy
Changing a User Role Interface Policy
•![]() Changing a User Role VLAN Policy
Changing a User Role VLAN Policy
•![]() Changing a User Role VRF Policy
Changing a User Role VRF Policy
Creating a User Role
You can configure up to 64 user roles in a VDC. You can assign a user role to more that one user account.
DETAILED STEPS
To create user roles, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the roles.
From the Summary pane, double-click the device to display the roles.
Step 3 ![]() From the menu bar, choose File > New > Add Role.
From the menu bar, choose File > New > Add Role.
A new row appears in the list of roles.
Step 4 ![]() In the Name cell, enter the role name.
In the Name cell, enter the role name.
The maximum length of the role name is 16 characters.
Step 5 ![]() (Optional) In the Description cell, enter the role description.
(Optional) In the Description cell, enter the role description.
Step 6 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Adding a Rule to a User Role
You can use rules to define the actions that users can perform on the NX-OS device. Each user role can have up to 256 rules.
The rule number that you specify determines the order in which the rules are applied. Rules are applied in descending order. For example, if a role has three rules, rule 3 is applied before rule 2, which is applied before rule 1.
BEFORE YOU BEGIN
Create one or more user roles (see the "Creating a User Role" section).
DETAILED STEPS
To add a rule to a user role, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the user roles.
From the Summary pane, double-click the device to display the user roles.
The Details tab appears in the Details pane.
Step 3 ![]() Click the user role to which to add a rule.
Click the user role to which to add a rule.

Note ![]() You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
Step 4 ![]() From the Details tab, click Command Authorization Rules.
From the Details tab, click Command Authorization Rules.
Step 5 ![]() From the menu bar, choose Roles > Add Rule or Roles > Insert Rule Above or Roles > Insert Rule Below.
From the menu bar, choose Roles > Add Rule or Roles > Insert Rule Above or Roles > Insert Rule Below.
A new rule appears in the Details pane.
Step 6 ![]() Double-click the Permission cell for the new rule and choose Permit or Deny.
Double-click the Permission cell for the new rule and choose Permit or Deny.
Step 7 ![]() Double-click the Match Command Type cell for the new rule and choose from the drop-down list.
Double-click the Match Command Type cell for the new rule and choose from the drop-down list.
Step 8 ![]() Double-click the Match Value (Component/Command) cell for the new rule.
Double-click the Match Value (Component/Command) cell for the new rule.
Step 9 ![]() Click the down arrow to display the match value dialog box (see Figure 5-7).
Click the down arrow to display the match value dialog box (see Figure 5-7).
Figure 5-7 Match Value Dialog Box
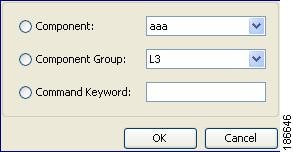
Step 10 ![]() From the dialog box, specify the match value for the rule and click OK.
From the dialog box, specify the match value for the rule and click OK.
Step 11 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Changing a Rule in a User Role
You can change the command authorization criteria for a rule in a user role.
BEFORE YOU BEGIN
Add one or more rules to a user role (see the "Adding a Rule to a User Role" section).
DETAILED STEPS
To change a rule to a user role, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the user roles.
From the Summary pane, double-click the device to display the user roles.
The Details tab appears in the Details pane.
Step 3 ![]() Click the user role to change.
Click the user role to change.

Note ![]() You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
Step 4 ![]() From the Details tab, click Command Authorization Rules.
From the Details tab, click Command Authorization Rules.
Step 5 ![]() Click the rule to rearrange.
Click the rule to rearrange.
Step 6 ![]() Double-click the Match Command Type cell for the rule and choose from the drop-down list.
Double-click the Match Command Type cell for the rule and choose from the drop-down list.
Step 7 ![]() Double-click the Match Value (Component/Command) cell for the rule.
Double-click the Match Value (Component/Command) cell for the rule.
Step 8 ![]() Click the down arrow to display the match value dialog box (see Figure 5-7).
Click the down arrow to display the match value dialog box (see Figure 5-7).
Step 9 ![]() From the dialog box, specify the match value for the rule and click OK.
From the dialog box, specify the match value for the rule and click OK.
Step 10 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Rearranging a Rule in a User Role
You can rearrange a rule in a user role.
BEFORE YOU BEGIN
Add one or more rules to a user role (see the "Adding a Rule to a User Role" section).
DETAILED STEPS
To rearrange a rule to a user role, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the user roles.
From the Summary pane, double-click the device to display the user roles.
The Details tab appears in the Details pane.
Step 3 ![]() Click the user role to change.
Click the user role to change.

Note ![]() You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
Step 4 ![]() From the Details tab, click Command Authorization Rules.
From the Details tab, click Command Authorization Rules.
Step 5 ![]() Click the rule to rearrange.
Click the rule to rearrange.
Step 6 ![]() From the menu bar, choose Roles > Move Up or Roles > Move Down.
From the menu bar, choose Roles > Move Up or Roles > Move Down.
Step 7 ![]() Double-click the Match Value (Component/Command) cell for the rule.
Double-click the Match Value (Component/Command) cell for the rule.
Step 8 ![]() Click the down arrow to display the match value dialog box (see Figure 5-7).
Click the down arrow to display the match value dialog box (see Figure 5-7).
Step 9 ![]() From the dialog box, specify the match value for the rule and click OK.
From the dialog box, specify the match value for the rule and click OK.
Step 10 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Deleting a Rule from a User Role
You can delete rules from a user role. Each role must have at least one rule.
BEFORE YOU BEGIN
Add one or more rules to a user role (see the "Adding a Rule to a User Role" section).
DETAILED STEPS
To delete a rule from a user role, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the user roles.
From the Summary pane, double-click the device to display the user roles.
The Details tab appears in the Details pane.
Step 3 ![]() Click the user role from which to delete the rule.
Click the user role from which to delete the rule.

Note ![]() You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
Step 4 ![]() From the Details tab, click Command Authorization Rules.
From the Details tab, click Command Authorization Rules.
Step 5 ![]() Click the rule that you want to delete.
Click the rule that you want to delete.
Step 6 ![]() From the menu bar, choose Roles > Delete Rule and click Yes in the confirmation dialog box.
From the menu bar, choose Roles > Delete Rule and click Yes in the confirmation dialog box.
The rule disappears from the Details pane.
Step 7 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Changing a User Role Interface Policy
You can change a user role interface policy to limit the interfaces that the user can access. By default, a user role allows access to all interfaces in the VDC.
BEFORE YOU BEGIN
Create one or more user roles (see the "Creating a User Role" section).
DETAILED STEPS
To change user role interface policies, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the roles.
From the Summary pane, double-click the device to display the roles.
Step 3 ![]() Click the role to change.
Click the role to change.
The Details tab appears in the Details pane.

Note ![]() You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
Step 4 ![]() From the Details pane, click General.
From the Details pane, click General.
Step 5 ![]() From the Permitted Interfaces field, click the down arrow to display the permitted interfaces dialog box (see Figure 5-8).
From the Permitted Interfaces field, click the down arrow to display the permitted interfaces dialog box (see Figure 5-8).
Figure 5-8 Permitted Interfaces Dialog Box
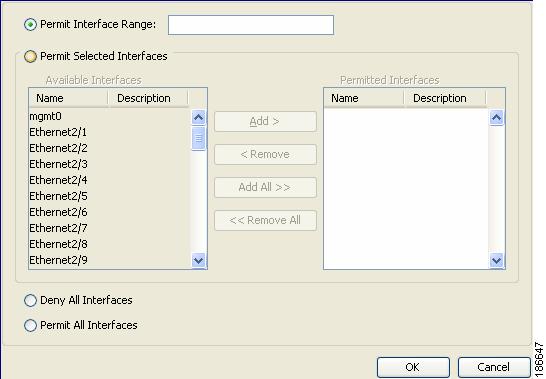
Step 6 ![]() From the dialog box, you can enter the range of interfaces to permit, specify selected interfaces to permit, deny all interfaces, or permit all interfaces.
From the dialog box, you can enter the range of interfaces to permit, specify selected interfaces to permit, deny all interfaces, or permit all interfaces.
Step 7 ![]() Click OK.
Click OK.
Step 8 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Changing a User Role VLAN Policy
You can change a user role VLAN policy to limit the VLANs that the user can access. By default, a user role allows access to all VLANs in the VDC.
BEFORE YOU BEGIN
Create one or more user roles (see the "Creating a User Role" section).
DETAILED STEPS
To change user role VLAN policies, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the roles.
From the Summary pane, double-click the device to display the roles.
Step 3 ![]() Click the role to change.
Click the role to change.
The Details tab appears in the Details pane.

Note ![]() You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
Step 4 ![]() From the Details pane, click General.
From the Details pane, click General.
Step 5 ![]() From the Permitted VLANs field, click the down arrow to display the permitted VLANs dialog box (see Figure 5-9).
From the Permitted VLANs field, click the down arrow to display the permitted VLANs dialog box (see Figure 5-9).
Figure 5-9 Permitted VLANs Dialog Box
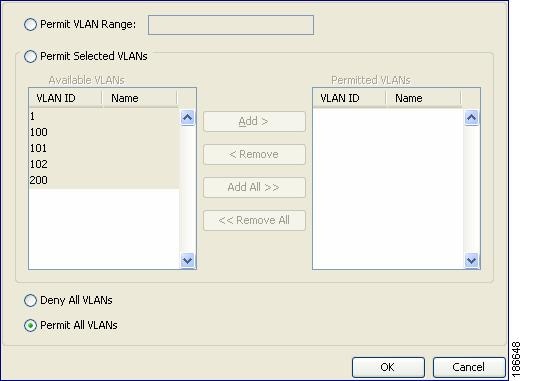
Step 6 ![]() From the dialog box, you can enter the range of VLANs to permit, specify selected VLANs to permit, deny all VLANs, or permit all VLANs.
From the dialog box, you can enter the range of VLANs to permit, specify selected VLANs to permit, deny all VLANs, or permit all VLANs.
Step 7 ![]() Click OK.
Click OK.
Step 8 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Changing a User Role VRF Policy
You can change a user role VRF policy to limit the VRFs that the user can access. By default, a user role allows access to all VRFs in the VDC.
BEFORE YOU BEGIN
Create one or more user roles (see the "Creating a User Role" section).
DETAILED STEPS
To change user role VRF policies, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the roles.
From the Summary pane, double-click the device to display the roles.
Step 3 ![]() Click the role to change.
Click the role to change.
The Details tab appears in the Details pane.

Note ![]() You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
You cannot modify the default roles network-admin, network-operator, vdc-admin, and vdc-operator.
Step 4 ![]() From the Details pane, click General.
From the Details pane, click General.
Step 5 ![]() From the Permitted VRFs field, click the down arrow to display the permitted VRFs dialog box (see Figure 5-10).
From the Permitted VRFs field, click the down arrow to display the permitted VRFs dialog box (see Figure 5-10).
Figure 5-10 Permitted VRFs Dialog Box
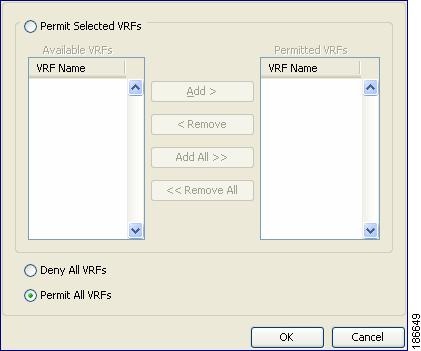
Step 6 ![]() From the dialog box, you can enter the range of VRFs to permit, specify selected VRFs to permit, deny all VRFs, or permit all VRFs.
From the dialog box, you can enter the range of VRFs to permit, specify selected VRFs to permit, deny all VRFs, or permit all VRFs.
Step 7 ![]() Click OK.
Click OK.
Step 8 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Copying a User Role
You can copy the configuration of a user role within an NX-OS device or from one NX-OS device to another NX-OS device.
BEFORE YOU BEGIN
Create one or more user account roles (see the "Creating a User Role" section).
DETAILED STEPS
To copy the configuration of a user account, follow these steps:
Step 1 ![]() From the Feature Selector pane, choose Security > RBAC > Roles.
From the Feature Selector pane, choose Security > RBAC > Roles.
Step 2 ![]() From the Summary pane, double-click the device to display the roles.
From the Summary pane, double-click the device to display the roles.
Step 3 ![]() Click the role you that want to copy.
Click the role you that want to copy.
Step 4 ![]() From the menu bar, choose Actions > Copy.
From the menu bar, choose Actions > Copy.
Step 5 ![]() Click the destination device.
Click the destination device.
Step 6 ![]() From the menu bar, choose Actions > Paste.
From the menu bar, choose Actions > Paste.
The role appears in the list of roles for the device.
Step 7 ![]() From the menu bar, choose File > Deploy to apply your changes to the device.
From the menu bar, choose File > Deploy to apply your changes to the device.
Field Descriptions for RBAC
This section includes the following topics:
•![]() Security: RBAC: Roles: Summary Pane
Security: RBAC: Roles: Summary Pane
•![]() Security: RBAC: Roles: device: role: Details Tab: General Area
Security: RBAC: Roles: device: role: Details Tab: General Area
•![]() Security: RBAC: Roles: device: role: Details Tab: Command Authorization Rules Area
Security: RBAC: Roles: device: role: Details Tab: Command Authorization Rules Area
•![]() Security: RBAC: Users: Summary Pane
Security: RBAC: Users: Summary Pane
Security: RBAC: Roles: Summary Pane
Security: RBAC: Roles: device: role: Details Tab: General Area
Security: RBAC: Roles: device: role: Details Tab: Command Authorization Rules Area
Security: RBAC: Users: Summary Pane
Additional References
For additional information related to implementing RBAC, see the following sections:
•![]() MIBs
MIBs
Related Documents
|
|
|
|---|---|
NX-OS Licensing |
|
DCNM Licensing |
Cisco DCNM Fundamentals Configuration Guide, Release 4.1 |
VRF configuration |
Cisco DCNM Unicast Routing Configuration Guide, Release 4.1 |
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
— |
MIBs
|
|
|
|---|---|
• |
To locate and download MIBs, go to the following URL: http://www.cisco.com/public/sw-center/netmgmt/cmtk/mibs.shtml |
Feature History for User Accounts and RBAC
Table 5-5 lists the release history for this feature.
 Feedback
Feedback