- Index
- Preface
- Product Overview
- Command-Line Interfaces
- Configuring the Switch for the First Time
- Administering the Switch
- Configuring the Cisco IOS In-Service Software Upgrade Process
- Configuring Interfaces
- Checking Port Status and Connectivity
- Configuring Supervisor Engine Redundancy Using RPR and SSO
- Configuring Cisco NSF with SSO Supervisor Engine Redundancy
- Environmental Monitoring and Power Management
- Configuring Power over Ethernet
- Configuring NetWork Assista nt
- Configuring VLANs
- Configuring IP Unnumbered Interface
- Configuring Layer 2 Ethernet Interfaces
- Configuring SmartPort Macros
- Configuring Auto SmartPort Macros
- Configuring Spanning Tree
- Configuring Flex Links and MAC Address-Table Move Update
- Configuring Resilient Ethernet Protocol
- Configuring Enhanced Spanning Tree Features
- Configuring EtherChannel and Link State Tracking
- Configuring IGMP Snooping and Filtering
- Configuring MLD Snooping
- Configuring 802.1Q Tunneling, VLAN Mapping, and Layer 2 Protocol Tunneling
- Configuring CDP
- Configuring LLDP, LLDP-MED, and Location Service
- Configuring UDLD
- Configuring Unidirectional Ethernet
- Configuring Layer 3 Interfaces
- Configuring Cisco Express Forwarding
- Configuring Unicast Reverse Path Forwarding
- Configuring IP Multicast
- Configuring ANCP Client
- Configuring Policy-Based Routing
- Configuring VRF
- Configuring Quality of Service
- Configuring Voice Interfaces
- Configuring Private VLANs
- Configuring 802.1X Port-Based Authentication
- Configuring the PPPoE Intermediate Agent
- Configuring Web-based Authentication
- Configuring Port Security
- Configuring Control Plane Policing and Layer 2 Control Packet QoS
- Configuring DHCP Snooping, IP Source Guard, and IPSG for Static Hosts
- Configuring Dynamic ARP Inspection
- Configuring Network Security with ACL
- Support for IPv6
- Port Unicast and Multicast Flood Blocking
- Configuring Storm Control
- Configuring SPAN
- Configuring System Message Logging
- Configuring OBFL
- Configuring SNMP
- Configuring NetFlow-lite
- Configuring NetFlow Switching
- Configuring CFM and OAM
- Configuring Y1731
- Configuring Call Home
- Configuring Cisco IOS IP SLA Operations
- Configuring RMON
- Performing Diagnostics
- Configuring WCCP
- ROM Monitor
- Configuring MIB Support
- Acronyms
Configuring SPAN and RSPAN
This chapter describes how to configure the Switched Port Analyzer (SPAN) and Remote SPAN (RSPAN) on the Catalyst 4500 series switches. SPAN selects network traffic for analysis by a network analyzer, such as a SwitchProbe device or other Remote Monitoring (RMON) probe.
This chapter consists of the following sections:
- About SPAN and RSPAN
- Configuring SPAN
- CPU Port Sniffing
- Encapsulation Configuration
- Ingress Packets
- Access List Filtering
- Packet Type Filtering
- Configuration Example
- Configuring RSPAN
- Displaying SPAN and RSPAN Status

Note![]() For complete syntax and usage information for the switch commands used in this chapter, first look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
For complete syntax and usage information for the switch commands used in this chapter, first look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
http://www.cisco.com/en/US/products//hw/switches/ps4324/index.html
If the command is not found in the Catalyst 4500 Command Reference, it will be found in the larger Cisco IOS library. Refer to the Catalyst 4500 Series Switch Cisco IOS Command Reference and related publications at this location:
http://www.cisco.com/en/US/products/ps6350/index.html
About SPAN and RSPAN
This sections includes the following subsections:
- SPAN and RSPAN Concepts and Terminology
- SPAN and RSPAN Session Limits
- Default SPAN and RSPAN Configuration
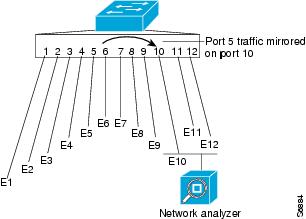
SPAN mirrors traffic from one or more source interfaces on any VLAN or from one or more VLANs to a destination interface for analysis. In Figure 1-1, all traffic on Ethernet interface 5 (the source interface) is mirrored to Ethernet interface 10. A network analyzer on Ethernet interface 10 receives all network traffic from Ethernet interface 5 without being physically attached to it.
For SPAN configuration, the source interfaces and the destination interface must be on the same switch.
SPAN does not affect the switching of network traffic on source interfaces; copies of the packets received or transmitted by the source interfaces are sent to the destination interface.
Figure 1-1 Example SPAN Configuration
RSPAN extends SPAN by enabling remote monitoring of multiple switches across your network. The traffic for each RSPAN session is carried over a user-specified RSPAN VLAN that is dedicated for that RSPAN session in all participating switches. The SPAN traffic from the sources is copied onto the RSPAN VLAN and then forwarded over trunk ports that are carrying the RSPAN VLAN to any RSPAN destination sessions monitoring the RSPAN VLAN, as shown in Figure 1-2.
Figure 1-2 Example of RSPAN Configuration

SPAN and RSPAN do not affect the switching of network traffic on source ports or source VLANs; a copy of the packets received or sent by the sources is sent to the destination. Except for traffic that is required for the SPAN or RSPAN session, by default, destination ports do not receive or forward traffic.
You can use the SPAN or RSPAN destination port to forward transmitted traffic from a network security device. For example, if you connect a Cisco Intrusion Detection System (IDS) sensor appliance to a destination port, the IDS device can send TCP reset packets to close down the TCP session of a suspected attacker.
SPAN and RSPAN Concepts and Terminology
This section describes concepts and terminology associated with SPAN and RSPAN configuration and includes the following subsections:
SPAN Session
A local SPAN session associates a destination port with source ports. You can monitor incoming or outgoing traffic on a series or range of ports and source VLANs. An RSPAN session associates source ports and source VLANs across your network with an RSPAN VLAN. The destination source is the RSPAN VLAN.
You configure SPAN sessions by using parameters that specify the source of network traffic to monitor.
You can configure multiple SPAN or RSPAN sessions with separate or overlapping sets of SPAN sources. Both switched and routed ports can be configured as SPAN sources or destination ports.
An RSPAN source session associates SPAN source ports or VLANs with a destination RSPAN VLAN. An RSPAN destination session associates an RSPAN VLAN with a destination port.
SPAN sessions do not interfere with the normal operation of the switch; however, an oversubscribed SPAN destination (for example, a 10-Mbps port monitoring a 100-Mbps port) results in dropped or lost packets.
You can configure SPAN sessions on disabled ports; however, a SPAN session does not become active unless you enable the destination port and at least one source port or VLAN for that session.
A SPAN session remains inactive after system startup until the destination port is operational.
Traffic Types
SPAN sessions include these traffic types:
- Receive (Rx) SPAN—The goal of receive (or ingress) SPAN is to monitor as much as possible all packets received by the source interface or VLAN before any modification or processing is performed by the switch. A copy of each packet received by the source is sent to the destination port for that SPAN session. You can monitor a series or range of ingress ports or VLANs in a SPAN session.
On tagged packets (Inter-Switch Link [ISL] or IEEE 802.1Q), the tagging is removed at the ingress port. At the destination port, if tagging is enabled, the packets appear with the ISL or 802.1Q headers. If no tagging is specified, packets appear in the native format.
Packets that are modified because of routing are copied without modification for Rx SPAN; that is, the original packet is copied. Packets that are modified because of quality of service (QoS)—for example, modified Differentiated Services Code Point (DSCP)—are copied without modification for Rx SPAN.
Some features that can cause a packet to be dropped during receive processing have no effect on SPAN; the destination port receives a copy of the packet even if the actual incoming packet is dropped. These features include IP standard and extended input access control lists (ACLs), IP standard and extended output ACLs for unicast and ingress QoS policing, VLAN maps, ingress QoS policing, and policy-based routing. Switch congestion that causes packets to be dropped also has no effect on SPAN.
- Transmit (Tx) SPAN—The goal of transmit (or egress) SPAN is to monitor as much as possible all packets sent by the source interface after the switch performs all modification and processing. After the packet is modified, the source sends a copy of each packet to the destination port for that SPAN session. You can monitor a range of egress ports in a SPAN session.
Packets that are modified because of routing—for example, with a time-to-live (TTL) or MAC-address modification—are duplicated at the destination port. On packets that are modified because of QoS, the modified packet might not have the same DSCP (IP packet) or CoS (non-IP packet) as the SPAN source.
Some features that can cause a packet to be dropped during transmit processing might also affect the duplicated copy for SPAN. These features include VLAN maps, IP standard and extended output ACLs on multicast packets, and egress QoS policing. In the case of output ACLs, if the SPAN source drops the packet, the SPAN destination would also drop the packet. In the case of egress QoS policing, if the SPAN source drops the packet, the SPAN destination might not drop it. If the source port is oversubscribed, the destination ports have different dropping behavior.
Source Port
A source port (also called a monitored port) is a switched or routed port that you monitor for network traffic analysis. In a single local SPAN session or RSPAN source session, you can monitor source port traffic, such as received (Rx), transmitted (Tx), or bidirectional (both). The switch supports any number of source ports (up to the maximum number of available ports on the switch) and any number of source VLANs.
A source port has these characteristics:
- It can be any port type (for example, EtherChannel, Fast Ethernet, Gigabit Ethernet, and so forth).
- It can be monitored in multiple SPAN sessions.
- It cannot be a destination port.
- Each source port can be configured with a direction (ingress, egress, or both) to monitor. For EtherChannel sources, the monitored direction would apply to all physical ports in the group.
- Source ports can be in the same or different VLANs.
- For VLAN SPAN sources, all active ports in the source VLAN are included as source ports.
You can configure a trunk port as a source port. By default, all VLANs active on the trunk are monitored. You can limit SPAN traffic monitoring on trunk source ports to specific VLANs by using VLAN filtering. Only switched traffic in the selected VLANs is sent to the destination port. This feature affects only traffic forwarded to the destination SPAN port and does not affect the switching of normal traffic. This feature is not allowed in sessions with VLAN sources.
Destination Port
Each local SPAN session or RSPAN destination session must have a destination port (also called a monitoring port) that receives a copy of traffic from the source ports and VLANs.
A destination port has these characteristics:
- A destination port must reside on the same switch as the source port (for a local SPAN session).
- A destination port can be any Ethernet physical port.
- A destination port can participate in only one SPAN session at a time. (A destination port in one SPAN session cannot be a destination port for a second SPAN session.)
- A destination port cannot be a source port.
- A destination port cannot be an EtherChannel group, nor a physical port that is an EtherChannel member port.
- The port does not transmit any traffic except that traffic required for the SPAN session unless learning is enabled. If learning is enabled, the port also transmits traffic directed to hosts that have been learned on the destination port.
- If ingress traffic forwarding is enabled for a network security device, the destination port forwards traffic at Layer 2.
- A destination port does not participate in spanning tree while the SPAN session is active.
- When it is a destination port, it does not participate in any of the Layer 2 protocols (STP, VTP, CDP, DTP, PagP).
- A destination port that belongs to a source VLAN of any SPAN session is excluded from the source list and is not monitored.
- A destination port receives copies of sent and received traffic for all monitored source ports. If a destination port is oversubscribed, it could become congested and result in packet drops at the destination port. This congestion does not affect traffic forwarding on the source ports.
VLAN-Based SPAN
VLAN-based SPAN (VSPAN) is the monitoring of the network traffic in one or more VLANs.
Use these guidelines for VSPAN sessions:
- Traffic on RSPAN VLANs is not monitored by VLAN-based SPAN sessions.
- Only traffic on the monitored VLAN is sent to the destination port.
- If a destination port belongs to a source VLAN, it is excluded from the source list and is not monitored.
- If ports are added to or removed from the source VLANs, the traffic on the source VLAN received by those ports is added to or removed from the sources being monitored.
- VLAN pruning and the VLAN allowed list have no effect on SPAN monitoring.
- VSPAN monitors only traffic that enters the switch, not traffic that is routed between VLANs. For example, if a VLAN is being Rx-monitored, and the multilayer switch routes traffic from another VLAN to the monitored VLAN, that traffic is not monitored and is not received on the SPAN destination port.
- You cannot use filter VLANs in the same session with VLAN sources.
- You can monitor only Ethernet VLANs.
SPAN Traffic
You can use local SPAN to monitor all network traffic, including multicast and bridge protocol data unit (BPDU) packets, Cisco Discovery Protocol (CDP), VLAN Trunk Protocol (VTP), Dynamic Trunking Protocol (DTP), Spanning Tree Protocol (STP), and Port Aggregation Protocol (PAgP) packets. You cannot use RSPAN to monitor Layer 2 protocols. See the “RSPAN Configuration Guidelines” section for more information.)
In some SPAN configurations, multiple copies of the same source packet are sent to the SPAN destination port. For example, a bidirectional (both Rx and Tx) SPAN session is configured for the sources a1 Rx monitor and the a2 Rx and Tx monitor to destination port d1. If a packet enters the switch through a1 and is switched to a2, both incoming and outgoing packets are sent to destination port d1. Both packets are the same (unless a Layer-3 rewrite occurs, in which case the packets are different because of the added Layer 3 information).
SPAN and RSPAN Session Limits
You can configure up to eight simultaneous SPAN sessions containing ingress sources and up to eight simultaneous SPAN sessions containing egress sources. Bidirectional sources count as both ingress and egress. RSPAN destination sessions count as a session containing an ingress source.

Note![]() Catalyst 4900M, Catalyst 4948E, Supervisor Engine 6-E, and Supervisor Engine 6L-E allow a maximum of 16 SPAN/RSPAN sessions ( 8 concurrent sessions with Rx sources and 8 concurrent sessions with Tx sources). Bidirectional sources count as both Rx and Tx. All other supervisor engines allow a maximum of 6 sessions (2 concurrent sessions with RX sources and 4 concurrent sessions with Txsources).
Catalyst 4900M, Catalyst 4948E, Supervisor Engine 6-E, and Supervisor Engine 6L-E allow a maximum of 16 SPAN/RSPAN sessions ( 8 concurrent sessions with Rx sources and 8 concurrent sessions with Tx sources). Bidirectional sources count as both Rx and Tx. All other supervisor engines allow a maximum of 6 sessions (2 concurrent sessions with RX sources and 4 concurrent sessions with Txsources).
Default SPAN and RSPAN Configuration
Table 1-1 shows the default SPAN and RSPAN configuration.
|
|
|
|---|---|
Configuring SPAN
The following sections describe how to configure SPAN:
- SPAN Configuration Guidelines and Restrictions
- Configuring SPAN Sources
- Configuring SPAN Destinations
- Monitoring Source VLANs on a Trunk Interface
- Configuration Scenario
- Verifying a SPAN Configuration

Note![]() Entering SPAN configuration commands does not clear previously configured SPAN parameters. You must enter the no monitor session command to clear configured SPAN parameters.
Entering SPAN configuration commands does not clear previously configured SPAN parameters. You must enter the no monitor session command to clear configured SPAN parameters.
SPAN Configuration Guidelines and Restrictions
Follow these guidelines and restrictions when configuring SPAN:
- You must use a network analyzer to monitor interfaces.
- You cannot mix source VLANs and filter VLANs within a SPAN session. You can have source VLANs or filter VLANs, but not both at the same time.
- EtherChannel interfaces can be SPAN source interfaces; they cannot be SPAN destination interfaces.
- When you specify source interfaces and do not specify a traffic type (Tx, Rx, or both), “both” is used by default. To change from both to either “tx” or “rx,” unconfigure the corresponding other type “rx” or “tx” with the no monitor session {session_number} {source {interface interface_list | {vlan vlan_IDs | cpu [queue queue_ids] } {rx | tx} command.
- If you specify multiple SPAN source interfaces, the interfaces can belong to different VLANs.
- You must enter the no monitor session number command with no other parameters to clear the SPAN session number.
- The no monitor command clears all SPAN sessions.
- SPAN destinations never participate in any spanning tree instance. SPAN includes BPDUs in the monitored traffic, so any BPDUs seen on the SPAN destination are from the SPAN source.
- SPAN is limited to one destination port per session.
- When you create a SPAN session, it sets the packet filter to good automatically and hence you will see another configuration line:
monitor session 1 filter packet-type good rx
Reenter the monitor session 1 filter packet-type good rx command.
Configuring SPAN Sources
To configure the source for a SPAN session, perform this task:
This example shows how to configure SPAN session 1 to monitor bidirectional traffic from source interface Fast Ethernet 5/1:
This example shows how to configure sources with differing directions within a SPAN session:
Configuring SPAN Destinations
To configure the destination for a SPAN session, perform this task:

Note![]() SPAN is limited to one destination port per session.
SPAN is limited to one destination port per session.
This example shows how to configure interface Fast Ethernet 5/48 as the destination for SPAN session 1:
Monitoring Source VLANs on a Trunk Interface
To monitor specific VLANs when the SPAN source is a trunk interface, perform this task:
This example shows how to monitor VLANs 1 through 5 and VLAN 9 when the SPAN source is a trunk interface:
Configuration Scenario
This example shows how to use the commands described in this chapter to completely configure and unconfigure a span session. Assume that you want to monitor bidirectional traffic from source interfaces Fast Ethernet 4/10, 4/11 and 4/12, Interface 4/10 is configured as a trunk interface carrying VLANs 1 through 4094. Interface Fast Ethernet 4/11 is configured as an access port in VLAN 57 and interface Fast Ethernet 4/12 is configured as an access port in VLAN 58. You want to monitor only traffic in VLAN 57 in that session. Using Fast Ethernet 4/15 as your destination interface, you would enter the following commands:
You are now monitoring traffic from interface Fast Ethernet 4/10 that is on VLAN 57 out of interface FastEthernet 4/15. To disable the span session enter the following command:
Verifying a SPAN Configuration
This example shows how to verify the configuration of SPAN session 2:
CPU Port Sniffing
When configuring a SPAN session, you can specify the CPU (or a subset of CPU queues) as a SPAN source. Queues may be specified either by number or by name. When such a source is specified, traffic going to the CPU through one of the specified queues is mirrored and sent out of the SPAN destination port in the session. This traffic includes both control packets and regular data packets that are sent to or from the CPU (due to software forwarding).
You can mix the CPU source with either regular port sources or VLAN sources.
To configure CPU source sniffing, perform this task:
This example shows how to configure a CPU source to sniff all packets received by the CPU:
This example shows how to use queue names and queue number ranges for the CPU as a SPAN source on Supervisor Engines 2+ to V 10-GE:
This example shows how to use queue names and queue number ranges for the CPU as a SPAN source on Catalyst 4900M, Catalyst 4948E, Supervisor Engine 6-E, or Supervisor Engine 6L-E:

Note![]() For Catalyst 4900M, Catalyst 4948E, Supervisor Engine 6-E, and Supervisor Engine 6L-E, control-packet is mapped to queue 10.
For Catalyst 4900M, Catalyst 4948E, Supervisor Engine 6-E, and Supervisor Engine 6L-E, control-packet is mapped to queue 10.
Encapsulation Configuration
When configuring a SPAN destination port, you can explicitly specify the encapsulation type used by the port. Packets sent out the port are tagged in accordance with the specified mode. (The encapsulation mode also controls how tagged packets are handled when the ingress packet option is enabled.) The Catalyst 4500 series switch supervisor engines support ISL encapsulation and 802.1q encapsulation, as well as untagged packets.

Note![]() Catalyst 4900M, Catalyst 4948E, Supervisor Engine 6-E, and Supervisor Engine 6L-E support only 802.1q encapsulation.
Catalyst 4900M, Catalyst 4948E, Supervisor Engine 6-E, and Supervisor Engine 6L-E support only 802.1q encapsulation.
The “replicate” encapsulation type (in which packets are transmitted from the destination port using whatever encapsulation applied to the original packet) is not supported. If no encapsulation mode is specified, the port default is untagged.
Ingress Packets
When ingress is enabled, the SPAN destination port accepts incoming packets (potentially tagged depending on the specified encapsulation mode) and switches them normally. When configuring a SPAN destination port, you can specify whether the ingress feature is enabled and what VLAN to use to switch untagged ingress packets. (Specifying an ingress VLAN is not required when ISL encapsulation is configured, as all ISL encapsulated packets have VLAN tags.) Although the port is STP forwarding, it does not participate in the STP, so use caution when configuring this feature lest a spanning-tree loop be introduced in the network. When both ingress and a trunk encapsulation are specified on a SPAN destination port, the port goes forwarding in all active VLANs. Configuring a non-existent VLAN as an ingress VLAN is not allowed.
By default, host learning is disabled on SPAN destination ports with ingress enabled. The port is also removed from VLAN floodsets, so regular traffic is not switched out of the destination port. If learning is enabled, then traffic for hosts learned on the destination port is switched out the destination port. A host connected to the SPAN destination port will not receive broadcast ARP requests and will not respond. You can also configure static host entries (including a static ARP entry and a static entry in the MAC-address table) on SPAN destination ports.

Note![]() This configuration does not work if the SPAN session does not have a source configured; the session is half configured with only the SPAN destination port.
This configuration does not work if the SPAN session does not have a source configured; the session is half configured with only the SPAN destination port.
To configure ingress packets and encapsulation, perform this task:
This example shows how to configure a destination port with 802.1q encapsulation and ingress packets using native VLAN 7:
With this configuration, traffic from SPAN sources associated with session 1 would be copied out of interface Fast Ethernet 5/48, with 802.1q encapsulation. Incoming traffic would be accepted and switched, with untagged packets being classified into VLAN 7.
Access List Filtering
When configuring a SPAN session, you can apply access list filtering. Access list filtering applies to all packets passing through a SPAN destination port that might be sniffed in the egress or ingress direction. Access list filters are allowed on local SPAN sessions only. If the SPAN destination is an RSPAN VLAN, the access list filter is rejected.

Note![]() Access list filtering is available in Cisco IOS Release 12.2(20)EW and later releases.
Access list filtering is available in Cisco IOS Release 12.2(20)EW and later releases.
ACL Configuration Guidelines
You can configure ACLs on a SPAN session. Use these guidelines for ACL/SPAN sessions:
- If an ACL is associated with a SPAN session, the rules associated with that ACL are applied against all packets exiting the SPAN destination interface. Rules pertaining to other VACLs or RACLs previously associated with the SPAN destination interface are not applied.
- Only one ACL can be associated with a SPAN session.
- When no ACLs are applied to packets exiting a SPAN destination interface, all traffic is permitted regardless of the PACLs, VACLs, or RACLs that have been previously applied to the destination interface or VLAN to which the SPAN destination interface belongs.
- If an ACL is removed from a SPAN session, all traffic is permitted once again.
- If SPAN configuration is removed from the SPAN session, all rules associated with the SPAN destination interface are applied once again.
- If a SPAN destination port is configured as a trunk port and the VLANs to which it belongs have ACLs associated with them, the traffic is not subjected to the VACLs.
- ACL configuration applies normally to the RSPAN VLAN and to trunk ports carrying the RSPAN VLAN. This configuration enables you to apply VACLs on RSPAN VLANs. If a user attempts to configure an ACL on a SPAN session with the destination port as an RSPAN VLAN, the configuration is rejected.
- If CAM resources are exhausted and packets are passed to the CPU for lookup, any output port ACLs associated with a SPAN session are not applied.
- If a named IP ACL is configured on a SPAN session before an ACL is created, the configuration is accepted, and the software creates an empty ACL with no ACEs. (An empty ACL permits all packets.) Subsequently, the rules can be added to the ACL.
- The ACLs associated with a SPAN session are applied on the destination interface on output.
- No policing is allowed on traffic exiting SPAN ports.
- Only IP ACLs are supported on SPAN sessions.
Configuring Access List Filtering
To configure access list filtering, perform this task:

Note![]() IP access lists must be created in configuration mode as described in the chapter “Configuring Network Security with ACLs.”
IP access lists must be created in configuration mode as described in the chapter “Configuring Network Security with ACLs.”
This example shows how to configure IP access group 10 on a SPAN session and verify that an access list has been configured:
Packet Type Filtering
When configuring a SPAN session, you can specify packet filter parameters similar to VLAN filters. When specified, the packet filters indicate types of packets that may be sniffed. If no packet filters are specified, packets of all types may be sniffed. Different types of packet filters may be specified for ingress and egress traffic.
The two categories of packet filtering are packet-based (good, error) or address-based (unicast/multicast/broadcast). Packet-based filters can only be applied in the ingress direction. Packets are classified as broadcast, multicast, or unicast by the hardware based on the destination address.

Note![]() When filters of both types are configured, only packets that pass both filters are spanned. For example, if you set both “error” and “multicast,” only multicast packets with errors are spanned.
When filters of both types are configured, only packets that pass both filters are spanned. For example, if you set both “error” and “multicast,” only multicast packets with errors are spanned.
To configure packet type filtering, perform this task:
This example shows how to configure a session to accept only unicast packets in the ingress direction:
Configuration Example
The following is an example of SPAN configuration using some of the SPAN enhancements.
In this example, you configure a session to sniff unicast traffic arriving on interface Gi1/1. The traffic is mirrored out of interface Gi1/2 with ISL encapsulation. Ingress traffic is permitted.
Configuring RSPAN
This section describes how to configure RSPAN on your switch and it contains this configuration information:
- RSPAN Configuration Guidelines
- Creating an RSPAN Session
- Creating an RSPAN Destination Session
- Creating an RSPAN Destination Session and Enabling Ingress Traffic
- Removing Ports from an RSPAN Session
- Specifying VLANs to Monitor
- Specifying VLANs to Filter
RSPAN Configuration Guidelines
Follow these guidelines when configuring RSPAN:

Note![]() Since RSPAN VLANs have special properties, you should reserve a few VLANs across your network for use as RSPAN VLANs; do not assign access ports to these VLANs.
Since RSPAN VLANs have special properties, you should reserve a few VLANs across your network for use as RSPAN VLANs; do not assign access ports to these VLANs.

Note![]() You can apply an output access control list (ACL) to RSPAN traffic to selectively filter or monitor specific packets. Specify these ACLs on the RSPAN VLAN in the RSPAN source switches.
You can apply an output access control list (ACL) to RSPAN traffic to selectively filter or monitor specific packets. Specify these ACLs on the RSPAN VLAN in the RSPAN source switches.
- RSPAN sessions can coexist with SPAN sessions within the limits described in the “SPAN and RSPAN Session Limits” section.
- For RSPAN configuration, you can distribute the source ports and the destination ports across multiple switches in your network.
- RSPAN does not support BPDU packet monitoring or other Layer 2 switch protocols.
- The RSPAN VLAN is configured only on trunk ports and not on access ports. To avoid unwanted traffic in RSPAN VLANs, make sure that all participating switches support the VLAN remote-span feature. Access ports on the RSPAN VLAN are silently disabled.
- You should create an RSPAN VLAN before configuring an RSPAN source or destination session.
- If you enable VTP and VTP pruning, RSPAN traffic is pruned in the trunks to prevent the unwanted flooding of RSPAN traffic across the network for VLAN-IDs that are lower than 1005.
- Because RSPAN traffic is carried across a network on an RSPAN VLAN, the original VLAN association of the mirrored packets is lost. RSPAN can only support forwarding of traffic from an IDS device onto a single user-specified VLAN.
Creating an RSPAN Session
First create an RSPAN VLAN that does not exist for the RSPAN session in any of the switches that participate in RSPAN. With VTP enabled in the network, you can create the RSPAN VLAN in one switch, and then VTP propagates it to the other switches in the VTP domain for VLAN-IDs that are lower than 1005.
Use VTP pruning to get efficient flow of RSPAN traffic, or manually delete the RSPAN VLAN from all trunks that do not need to carry the RSPAN traffic.
To start an RSPAN source session and to specify the source (monitored) ports and the destination RSPAN VLAN, perform this task:
This example shows how to clear any existing RSPAN configuration for session 1, configure RSPAN session 1 to monitor multiple source interfaces, and configure the destination RSPAN VLAN.
Creating an RSPAN Destination Session
To create an RSPAN destination session and to specify the source RSPAN VLAN and the destination port, perform this task:
This example shows how to configure VLAN 901 as the source remote VLAN and port 5 as the destination interface:
Creating an RSPAN Destination Session and Enabling Ingress Traffic
To create an RSPAN destination session, to specify the source RSPAN VLAN, and to enable ingress traffic on the destination port for a network security device (such as a Cisco IDS [Intrusion Detection System] sensor appliance), perform this task:
This example shows how to configure VLAN 901 as the source remote VLAN and how to configure the destination port for ingress traffic on VLAN 5 by using a security device that supports 802.1Q encapsulation:
Removing Ports from an RSPAN Session
To remove a port as an RSPAN source for a session, perform this task:
This example shows how to remove port 1 as an RSPAN source for RSPAN session 1:
This example shows how to disable received traffic monitoring on port 1, which was configured for bidirectional monitoring:
The monitoring of traffic received on port 1 is disabled, but traffic transmitted from this port continues to be monitored.
Specifying VLANs to Monitor
VLAN monitoring is similar to port monitoring. To specify VLANs to monitor, perform this task:
To remove one or more source VLANs from the RSPAN session, use the no monitor session session_number source vlan vlan-id rx global configuration command.
This example shows how to clear any existing configuration on RSPAN session 2, configure RSPAN session 2 to monitor received traffic on all ports belonging to VLANs 1 through 3, and send it to destination remote VLAN 902. The configuration is then modified to also monitor received traffic on all ports belonging to VLAN 10.
Specifying VLANs to Filter
To limit RSPAN source traffic to specific VLANs, perform this task:
To monitor all VLANs on the trunk port, use the no monitor session session_number filter vlan global configuration command.
This example shows how to clear any existing configuration on RSPAN session 2, configure RSPAN session 2 to monitor traffic received on trunk port 4, and send traffic for only VLANs 1 through 5 and 9 to destination remote VLAN 902.
Displaying SPAN and RSPAN Status
To display the status of the current SPAN or RSPAN configuration, use the show monitor privileged EXEC command.
This example displays the output for the show monitor command for SPAN source session 1:
 Feedback
Feedback