Information About Identity Control Policies
The following sections provide information about how to configure identity control policies.
Identity-Based Networking Services Configuration
To convert all relevant authentication commands to their Class-Based Policy Language(CPL) control policy equivalents, use the authentication convert-to new-style command. This command permanently converts the legacy configuration on the switch to identity-based networking services.
 Note |
This configuration is irreversible. It disables the conversion command – authentication display [legacy | new-style] . |
Use the authentication display config-mode command in EXEC mode to display the current configuration mode; legacy if it is legacy mode and new-style if it is Identity-Based Networking Services configuration mode.
(Device)# authentication display config-mode
Current configuration mode is legacy
Device)# authentication display config-mode
Current configuration mode is new-styleConcurrent Authentication Methods
Identity-Based Networking Services allows the concurrent operation of IEEE 802.1x (dot1x), MAC authentication bypass (MAB), and web authentication methods, making it possible to invoke multiple authentication methods in parallel on a single subscriber session. This allows the client-supported method to complete at the earliest opportunity without the delays associated with serialization.
Typically, the access control method that is used to authorize a host is left up to the endpoint. For example, a printer without an 802.1x supplicant would be authorized through MAB only, an employee desktop through 802.1x only, and a guest through web authentication only. The default priority order is 802.1x, followed by MAB, then web authentication. When method priorities are the same, the first method that successfully authenticates the session prevails.
An example in which more than one method may succeed during the lifetime of a session is when MAB is used to provide interim access pending success of 802.1x. A host could be also be given interim access to a web server to allow credentials to be updated so that 802.1x can succeed after an authentication failure.
Configuration Display Mode
Identity-Based Networking Services introduces new Cisco IOS commands that replace many of the previously supported authentication and policy commands. These commands are available only after enabling the Cisco common classification policy language (C3PL) display mode that supports Identity-Based Networking Services. Identity-Based Networking Services features such as concurrent authentication and web authentication with IPv6 are not supported in legacy mode.
The device defaults to the legacy configuration mode until you do one of the following:
-
Enter the authentication display new-style command—This command switches to C3PL display mode, temporarily converting your legacy configuration to a Identity-Based Networking Services configuration so you can see how it looks before you make the conversion permanent. You can switch back to legacy mode by using the authentication display legacy command. See the “Enabling the Display Mode for Identity-Based Networking Services” section.
-
Enter a Identity-Based Networking Services configuration command—After you enter the first explicit Identity-Based Networking Services command, the configuration converts to C3PL display mode permanently and legacy commands are suppressed. The authentication display command is disabled and you can no longer revert to the legacy configuration mode.
Control Policies for Identity-Based Networking Services
A control policy defines the handling of different subscriber life-cycle events. For various events, such as session start or session failure, you can specify actions in the control policy. These actions can be executed conditionally for different subscribers based on various match criteria. Control policies are activated on interfaces and typically control the authentication of subscriber identity and the activation of services on sessions. For example, you can configure a control policy to authenticate specific subscribers and then provide them with access to specific services.
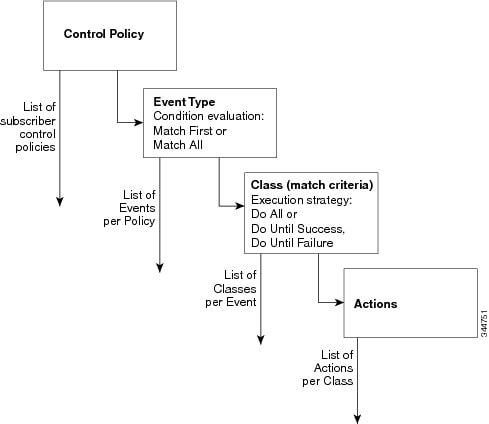
A control policy consists of one or more control policy rules and a decision strategy that governs how the policy rules are evaluated. A control policy rule consists of a control class (a flexible condition clause), an event for which the condition is evaluated, and one or more actions. Actions are general system functions, such as “authenticate” or “activate.” You define the specific actions that an event will trigger and some events have default actions.
The figure below illustrates how each control policy contains a list of events that are considered applicable to the subscriber life cycle. Within each event type is a list of control classes with different match criteria for subscriber identity, and under each class is a list of actions to be executed.
Control Policy Configuration Overview
Control policies express system functionality in terms of an event, a condition, and an action. There are three steps in defining a control policy:
-
Create one or more control classes—A control class specifies the conditions that must be met for a control policy to be activated. A control class can contain multiple conditions, each of which will evaluate as either true or false. Match directives specify whether all, any, or none of the individual conditions must evaluate true for the class to evaluate true. Or, you can specify the default control class which does not contain any conditions and always evaluates true.
-
Create a control policy—A control policy contains one or more control policy rules. A control policy rule consists of a control class, an event that causes the class to be evaluated, and one or more actions. Actions are numbered and executed sequentially.
-
Apply the control policy—A control policy is activated by applying it to an interface.
Parameter Maps for Identity-Based Networking Services
A parameter map allows you to specify parameters that control the behavior of actions specified under a control policy. For Identity-Based Networking Services, an authentication parameter map defines parameters used for the action specified with the authenticate using webauth command. You can configure the following types of parameter maps:
-
Authentication bypass (This is also called nonresponsive host [NRH] authentication.)
-
Consent
-
Web authentication
-
Web authentication with consent
Parameter maps are optional. If you do not configure a named parameter map, the software uses the default parameters that are specified in the global parameter map.
Per User Inactivity Handling Across Methods
A common inactivity aging feature extends support for RADIUS attributes 28 (Idle-Timeout) and attribute 29 (Termination-Action) to web authenticated sessions, providing consistent inactivity handling across all authentication methods, including 802.1x, MAC authentication bypass (MAB), and web authentication. The AAA server sends these attributes as part of the user authorization. After a session has been idle for the amount of time specified in attribute 28, or has reached the timeout configured with attribute 29, the session is terminated.
You can also apply the inactivity timeout and absolute timeout to sessions through a locally defined service template. When enabling the inactivity timeout, you can also enable address resolution protocol (ARP) probes that are sent before the session is terminated.
Single Control Policy for Identity-Based Networking Services
Prior 17.7.1, after the conversion of legacy configuration on the switch to identity-based networking services, the relevant authentication commands are converted to new-style and An identity control policy is generated for each interface. All interfaces have the same configuration as the identity control policy maps. The service templates for each interface are also identical.
Beginning from 17.7.1, to avoid interfaces having the same identity control policy configurations and individual identity control policy, you can configure a single control policy for all interfaces that have identical policy-maps and service-templates. You can also choose to replace all the policy-maps with the specified single control policy map. To use the single control policy map, ensure that the authentication methods on each interface is identical after the conversion.
You can also use the single policy approach if the switch is already in Identity-Based Networking Services configuration mode and you want to replace the existing interface policy-maps with a specific single policy-map.
Use the authentication convert-to new-style single-policy interface and access-session single-policy commands to apply the configuration of a specific single policy map to the relevant interfaces.
Use the authentication display config-mode command in EXEC mode to display the current configuration mode; legacy if it is legacy mode and new-style if it is Identity-Based Networking Services configuration mode.
 Feedback
Feedback