-
Cisco MDS 9000 Family Configuration Guide, Release 1.0(2a)
-
Index
-
Preface
-
Product Overview
-
Before You Begin
-
Initial Configuration
-
Configuring High Availability
-
Software Images
-
Managing Modules
-
Managing System Hardware
-
Configuring and Managing VSANs
-
Configuring Interfaces
-
Configuring Trunking
-
Configuring PortChannels
-
Configuring and Managing Zones
-
Managing FLOGI, Name Server, and RSCN Databases
-
Configuring System Security and AAA Services
-
Configuring Fibre Channel Routing Services and Protocols
-
Configuring IP Services
-
Configuring Call Home
-
Configuring Domain Parameters
-
Configuring Traffic Management
-
Configuring System Message Logging
-
Discovering SCSI Targets
-
Monitoring Network Traffic Using SPAN
-
Advanced Features and Concepts
-
Configuring Fabric Configuration Servers
-
Monitoring System Processes and Logs
-
Table Of Contents
Configuring System Security and AAA Services
Authentication and Authorization Process
Configuring CLI Authentication Methods
Enabling or Disabling Telnet Access
Displaying CLI Authentication Commands
Configuring Role-Based CLI Authorization
Configuring Rules and Features for Each Role
Displaying Role-Based CLI Information
Displaying User Profile Information
Configuring CLI Accounting Parameters
Setting the Accounting Log Size
Displaying Accounting Configuration
Recovering Administrator Password
Configuring RADIUS Authentication
Setting the RADIUS Server Address
Setting the RADIUS Preshared Key
Setting the RADIUS Server Time-Out Interval
Setting Iterations of the RADIUS Server
Defining Vendor-Specific Attributes
Displaying RADIUS Server Details
Generating an SSH Host Key Pair
Displaying SSH Protocol Status
Forcing Identical SNMP and CLI Passwords
Adding or Deleting Communities
Displaying SNMP Security Information
Displaying SNMP Counter Information
Configuring System Security and AAA Services
Security can be independently configured for each of the following management paths:
•
Command-line interface (CLI)—You can access the CLI using one of three connection options:
–
Console (serial connection)
–
Telnet
–
Secure Shell Protocol (SSH)
•
Simple Network Management Protocol (SNMP)—The SNMP agent supports security features FOR versions 1, 2c, and 3. Normal SNMP security mechanisms apply to all applications that use SNMP (for example, Cisco MDS 9000 Fabric Manager).
Note
Refer to the Cisco MDS 9000 Family Fabric Manager User Guide for information on this management tool.
This chapter includes the following sections:
•
Authentication and Authorization Process
•
Configuring CLI Authentication Methods
•
Configuring Role-Based CLI Authorization
•
Configuring CLI User Profiles
•
Configuring CLI Accounting Parameters
•
Configuring RADIUS Authentication
Management Security Features
Table 14-1 shows the security features of the Cisco MDS 9000 Family switches.
Note
Users and roles configured through the CLI are different from users and roles configured through SNMP. These configurations do not directly correspond with each other. However, you can configure both CLI and SNMP identically, if required.
User Authentication
Authentication is the process of verifying the identity of the person managing the switch. This identity verification is based on the user ID and password combination provided by the person trying to manage the switch. Cisco MDS 9000 Family switches allow you to perform local authentication (using the lookup database) or remote authentication (using one or more RADIUS servers).
For each management path (console or Telnet and SSH), you can enable only one of three options—local, RADIUS, or none. The option can be different for each path.
Local Authentication
The system maintains the user name and password locally and stores the password information in encrypted form. You are authenticated based on the locally stored information (see Figure 14-1).
Figure 14-1 Local Authentication
RADIUS Authentication
Cisco MDS 9000 Family switches provide remote authentication through RADIUS servers. You can also configure multiple RADIUS servers, and each server is tried in the order specified.
RADIUS protocols support one-time password (OTP) schemes that all switches can make use of for authentication purposes (see Figure 14-2).
Figure 14-2 RADIUS Authentication
Role-Based Authorization
By default, two roles exist in all switches:
•
Network operator (network-operator)—Has permission to view the configuration only. The operator cannot make any configuration changes.
•
Network administrator (network-admin)— Has permission to execute all commands and make configuration changes. The administrator can also create and customize up to 64 additional roles.
The two default roles cannot be changed or deleted. Vendor-specific attributes (VSAs) contain the user profile information used by the switch. To use this option, configure the VSAs on the RADIUS servers.
Accounting
Accounting refers to the log that is kept for each management session in a switch. This information may be used to generate reports for troubleshooting purposes and user accountability. Accounting can be implemented locally and remotely (using RADIUS).
Authentication and Authorization Process
The following steps explain the authorization and authentication process. Figure 14-3 shows a flow chart of the process.
Step 1
The switch software receives your user ID and password through a console or Telnet (or SSH) application.
Step 2
The remote server is contacted if remote authentication is enabled, or else local authentication is performed.
Note
If remote authentication is enabled but none of the servers are available (network failure), local authentication is performed.
Step 3
If authentication is successful, you are given access to the switch with appropriate permissions based on the roles to which you belong. These roles can be configured locally or can be sent by the remote server during the authentication process.
Step 4
If remote authentication is rejected, you are denied access and an appropriate message is issued.
Figure 14-3 Switch Authorization and Authentication Flow
Configuring CLI Authentication Methods
You can configure remote and local authentication for Telnet, SSH, or console access. These commands are restricted to privileged users as determined by your administrator.
Setting AAA Authentication
You can individually set authentication options for console or Telnet (and SSH) access using the aaa authentication login command. Local authentication is always disabled by default (see the "Authentication and Authorization Process" section).
To configure the authentication option, follow these steps:
Enabling or Disabling Telnet Access
You can use the telnet server enable command to enable Telnet access to the switch. By default, this service is enabled.
To enable or disable Telnet access to the switch, follow these steps:
Displaying CLI Authentication Commands
The show authentication command displays the configured authentication methods. See Example 14-1.
Example 14-1 Displays Authentication Information
switch# show authenticationauthentication method:noneconsole:not enabledtelnet/ssh:not enabledauthentication method:radiusconsole:not enabledtelnet/ssh:not enabledauthentication method:localconsole:enabledtelnet/ssh:enabledThe show telnet server command displays the state of the Telnet access configuration. See Example 14-2.
Example 14-2 Displays Telnet Server Details
switch# show telnet servertelnet service enabledConfiguring Role-Based CLI Authorization
Switches in the Cisco MDS 9000 Family perform authentication based on roles. Role-based authorization limits access to switch operations by assigning users to roles. This kind of authentication restricts you to management operations based on the roles to which you have been added.
When you execute a command, perform command completion, or obtain context sensitive help, the switch software allows the operation to progress if you have permission to access that command.
To configure a new role or to modify the profile for an existing role, follow these steps:
Each role can contain multiple users and each user can be part of multiple roles. For example, if role1 users are only allowed to perform configuration commands, and role2 users are only allowed to perform debug commands, then if Joe belongs to both role1 and role2, he can perform configuration as well as debug commands.
Note
If you belong to multiple roles, you can execute a superset of all the commands permitted by these roles. Access to a command takes priority over being denied access to a command. For example, suppose you belong to a TechDocs group and you were denied access to configuration commands. However, you also belong to the engineering group and have access to configuration commands. In this case, you will have access to configuration commands.
Configuring Rules and Features for Each Role
The rule command specifies rules for a specific group using the order in which they were issued. The order is important because the order in which they were issued is the order in which they are applied.
The feature option specifies the features accessible for this rule (for example, FSPF, zone, VSAN, fcping, interface). If no features are specified, the rule applies to all show, debug, clear, configuration commands, and all exec commands.
Note
In this case, exec commands refer to all commands in the EXEC mode that do not fall in the show, debug, and clear, categories. Up to 16 rules can be configured for each role.
To configure a new role or to modify the profile for an existing role, follow these steps:
In Step 3, rule 1 is applied first, thus permitting all config commands to sangroup users. Rule 2 is applied next, denying FSPF configuration to sangroup users. As a result, sangroup users can perform all other config commands, except fspf configuration commands.
Note
The order of rule placement is important. If you had swapped these two rules and issued the deny config feature fspf rule first and issued the permit config rule next, you would be allowing all sangroup users to perform all configuration commands since the second rule globally overrode the first rule.
Displaying Role-Based CLI Information
Use the show role command to display rules configured on the switch including those rules that have not yet been committed to persistent storage. The rules are displayed by rule number and are based on each role. All roles are displayed even if role name is not specified. See Example 14-3.
Example 14-3 Displays Information for All Roles
switch# show roleRole: network-adminDescription: Predefined Network Admin group. This role cannot be modifiedAccess to all the switch commandsRole: network-operatorDescription: Predefined Network Operator group. This role cannot be modifiedAccess to Show commands and selected Exec commandsRole: sangroupDescription: SAN management group-----------------------------------------Rule Type Command-type Feature-----------------------------------------1. permit config *2. deny config fspf3. permit debug zone4. permit exec fcpingConfiguring CLI User Profiles
Every Cisco MDS 9000 Family switch user has related NMS information stored by the system. Your authentication information, user name, user password, password expiration date, and role membership are stored in your user profile. The CLI commands explained in this section enable you to create users and modify the profile of an existing user.These commands are restricted to privileged users as determined by your administrator.
Creating or Updating Users
The switches use the same command (username) to create a user and to update an existing user. The expire option determines the date on which the user account is disabled. The date is specified in the YYYY-MM-DD format. By default, the user account does not expire unless you explicitly configure it to expire.
Tip
The following words are reserved and cannot be used to configure users: bin, daemon, adm, lp, sync, shutdown, halt, mail, news, uucp, operator, games, gopher, ftp, nobody, nscd, mailnull, rpc, rpcuser, xfs, gdm, mtsuser, ftpuser, man, and sys
Note
User passwords are not displayed in the switch configuration file.
To configure a new user or to modify the profile of an existing user, follow these steps:
Note
If the update-snmpv3 option is used, specify the clear text and old SNMP password (see the "Forcing Identical SNMP and CLI Passwords" section).
Displaying User Profile Information
Use the show user-account command to display configured information about user accounts. See Examples 14-4 to 14-6.
Example 14-4 Displays All Users
switch# show usersswitch# show usersadmin pts/7 Jan 12 20:56 (10.77.202.149)admin pts/9 Jan 12 23:29 (modena.cisco.com)admin pts/10 Jan 13 03:05 (dhcp-171-71-58-120.cisco.com)admin pts/11 Jan 13 01:53 (dhcp-171-71-49-49.cisco.com)Example 14-5 Displays Information for a Specified User
switch# show user-account user1user:user1this user account has no expiry dateroles:network-operatorno password set. Local login not allowedRemote login through RADIUS is possibleExample 14-6 Displays Information for All Users
switch# show user-accountshow user-accountuser:adminthis user account has no expiry dateroles:network-adminuser:usamexpires on Sat May 31 00:00:00 2003roles:network-admin network-operatoruser:msamthis user account has no expiry dateroles:network-operatoruser:user1this user account has no expiry dateroles:network-operatorno password set. local login not allowedRemote login through RADIUS is possibleConfiguring CLI Accounting Parameters
Accounting refers to the log information that is kept for each management session in a switch. This information may be used to generate reports for troubleshooting purposes and user accountability. Accounting can be implemented locally or remotely (using RADIUS).
Setting the Accounting Log Size
The aaa accounting logsize command sets the size limit of the accounting log file in persistent storage. The default is 15,000 bytes.
To set the log file size, follow these steps:
Step 1
Enters configuration mode.
Step 2
Sets the size of the log file on the local disk. The default is 15,000 bytes.
Enabling RADIUS Accounting
To enable RADIUS accounting in a switch, follow these steps:
You can clear the RADIUS accounting configuration by issuing the no accounting method radius command.
Displaying Accounting Configuration
The show accounting command displays configured accounting information. See Examples 14-7 to 14-9.
Example 14-7 Displays Configured Accounting Parameters.
switch# show accounting configRADIUS accounting not enabledlocal accounting enabledExample 14-8 Displays Configured Log Size.
switch# show accounting logsizemaximum local accounting log size:29000Example 14-9 Displays the Entire Log File.
switch# show accounting log2002:stop:snmp_1033151784_171.71.49.83:admin:Fri Sep 27 18:36:24 2002:start:_1033151784:rootFri Sep 27 18:36:28 2002:update:::fcc configuration requestedFri Sep 27 18:36:33 2002:start:snmp_1033151793_171.71.49.83:adminFri Sep 27 18:36:33 2002:stop:snmp_1033151793_171.71.49.83:admin:Fri Sep 27 18:39:28 2002:start:snmp_1033151968_171.71.49.96:adminFri Sep 27 18:39:28 2002:stop:snmp_1033151968_171.71.49.96:admin:Fri Sep 27 18:39:28 2002:start:_1033151968:rootFri Sep 27 18:39:31 2002:update:::fcc configuration requestedFri Sep 27 18:42:12 2002:stop:snmp_1033152132_171.71.49.96:admin:Fri Sep 27 18:42:12 2002:start:snmp_1033152132_171.71.49.96:adminFri Sep 27 18:42:40 2002:start:snmp_1033152160_171.71.49.96:admin. . .Recovering Administrator Password
An administrator can recover a password from a local console connection.
Note
Password recovery is not possible from a Telnet or SSH session.
To recover a administrator's password, follow these steps:
Step 1
Reboot the switch.
switch# reloadThe supervisor is going down for reboot NOW!Step 2
Press the Ctrl-] key sequence (when the switch begins its SAN-OS software boot sequence) to enter the switch(boot)# prompt.
Ctrl-]switch(boot)#Step 3
Change to configuration mode.
switchboot# configuration terminalStep 4
Enter the admin-password command to reset the administrator password.
switch(boot-config)# admin-password passwordStep 5
Exit to the EXEC mode.
switch(boot-config)# exit switchboot#Step 6
Enter the load command to load the SAN-OS software.
switch(boot)# load bootflash:san-ios.imgStep 7
Save the software configuration.
switch# copy running-config startup-config
Configuring RADIUS Authentication
You can configure RADIUS query parameters. These commands are restricted to privileged users as determined by your administrator.
Setting the RADIUS Server Address
You can add up to five (5) RADIUS servers using the radius-server host command. You can configure a RADIUS server to be a primary server so it is always contacted first. If you have not configured a primary server, the RADIUS servers are tried in the order they were configured.
To specify the RADIUS server address and the options, follow these steps:
Setting the RADIUS Preshared Key
You need to configure the RADIUS preshared key to authenticate the switch to the RADIUS server. The length of the key is restricted to 65 characters and can include any printable ASCII characters (white spaces are not allowed). You can configure a global key to be used for all RADIUS server configurations on the switch. You can override this global key assignment by explicitly using the key option in the radius-server host command.
To set the RADIUS preshared key, follow these steps:
Setting the RADIUS Server Time-Out Interval
To specify the time between retransmissions to the RADIUS servers, follow these steps:
You can revert the retransmission time to its default by issuing the no radius-server timeout command.
Setting Iterations of the RADIUS Server
By default, a switch retries a RADIUS server connection only once. This number can be configured. The maximum is five retries per server. You can revert the retry number to its default by issuing the no radius-server retransmit command.
To specify the number of times that RADIUS servers should try to authenticate a user, follow these steps:
The worst case cumulative response or timeout latency from RADIUS servers for authentication should not be more than 50 sec. For example in the following configuration:
radius-server timeout 5radius-server retransmit 3radius-server host A authenticationradius-server host B authenticationThe worst case cumulative response or timeout latency will be:
(5+1)*3 + (5+1)*3 = 36^^^^^^^^ ^^^^^^^^^ ^^^^^server A server B total
Note
You need to add one (1) to the retransmit count to calculate the total. The total number of tries equals the number of retransmits + 1.
Defining Vendor-Specific Attributes
The Internet Engineering Task Force (IETF) draft standard specifies a method for communicating vendor-specific attributes (VSAs) between the network access server and the RADIUS server. The IETF uses attribute 26. VSAs allow vendors to support their own extended attributes that are not suitable for general use. The Cisco RADIUS implementation supports one vendor-specific option using the format recommended in the specification. The Cisco vendor ID is 9, and the supported option is vendor type 1, which is named cisco-avpair. The value is a string with the following format:
protocol : attribute sep value *Where protocol is a Cisco attribute for a particular type of authorization, and sep is = for mandatory attributes, and * is for optional attributes.
When you use RADIUS servers to authenticate yourself to a Cisco MDS 9000 Family switch, the RADIUS protocol directs the RADIUS server to return user attributes, like authorization information, along with authentication results. This authorization information is specified through VSAs.
VSA Format
The following VSA protocol options are supported:
•
Shell protocol—used in Access-Accept packets to provide user profile information.
•
Accounting protocol—used in Accounting-Request packets. If a value contains any white spaces, it should be put within double quotation marks.
The following attributes are supported:
•
roles—This attribute lists all the roles to which the user belongs. The value field is a string storing the list of group names delimited by white space. For example, if you belong to roles vsan-admin and storage-admin, the value field would be "vsan-admin storage-admin." This subattribute is sent in the VSA portion of the Access-Accept frames from the RADIUS server, and it can only be used with the shell protocol value. This is an example using the roles attribute:
Cisco-AVPair = "shell: roles = "network-admin vsan-admin" "
•
accountinginfo—This attribute stores additional accounting information besides the attributes covered by a standard RADIUS accounting protocol. This attribute is only sent in the VSA portion of the Account-Request frames from the RADIUS client on the switch, and it can only be used with the accounting protocol value.
Authorization Process
The RADIUS based authorization process is as follows:
Step 1
The switch sends an Access-Request packet to the RADIUS server.
Step 2
The RADIUS server responds with an Accept or Reject message.
•
If Access-Reject is received, that means authentication has failed and no authorization information is sent.
•
If Access-Accept is received, that means authentication is successful and VSA is also sent along with the Access-Accept packet.
•
If no VSA data is sent, local authorization is used.
•
If your user name has no corresponding local account, a new account is created. This new account is locked and cannot be used for local login. It is deleted after 24 hours.
Step 3
You are made a member of all groups indicated in the role list attribute in the VSA. You are removed from those roles if your role is not listed in the VSA group list.
Displaying RADIUS Server Details
Use the show radius-server command to display all configured RADIUS server parameters (see Example 14-10).
Note
Only administrators can view the RADIUS preshared key.
Example 14-10 Displays Configured RADIUS Information
switch# show radius-serverGlobal RADIUS shared secret:Myxgqcretransmission count:5timeout value:10following RADIUS servers are configured:myradius.cisco.users.com:available for authentication on port:1812available for accounting on port:1813172.22.91.37:available for authentication on port:1812available for accounting on port:1813RADIUS shared secret:23MHcUnD10.10.0.0:available for authentication on port:1812available for accounting on port:1813RADIUS shared secret:hostkey----> for administrators onlyConfiguring SSH Services
The Telnet service is enabled by default on all Cisco MDS 9000 Family switches. Before enabling the SSH service, generate a host key pair. To generate a host key, use the ssh key command (see the "Generating an SSH Host Key Pair" section).
Enabling SSH Service
By default, the SSH service is disabled. To enable SSH service, issue the ssh server enable command.
To enable or disable the SSH service, follow these steps:
Generating an SSH Host Key Pair
Be sure to have an SSH host key pair with the appropriate version before enabling the SSH service. The SSH service accepts three types of key pairs for use by SSH versions 1 and 2. Generate the SSH host key pair according to the SSH client version used. The number of bits specified for each key pair ranges from 768 to 2048.
•
The rsa1 option generates the RSA1 key pair for the SSH version 1 protocol.
•
The dsa option generates the DSA key pair for the SSH version 2 protocol.
•
The rsa option generates the RSA key pair for the SSH version 2 protocol.
To generate the SSH host key pair, follow these steps:
Using the force Option
If the SSH key pair option is already generated for the required version, use the force option to overwrite the previously generated key pair.
To overwrite the previously generated key pair, follow these steps:
Displaying SSH Protocol Status
Use the show ssh server command to display the status of the SSH protocol (enabled or disabled) and the versions that are enabled for that switch. See Example 14-11.
Example 14-11 Displays SSH Protocol Status
switch# show ssh server ssh is enabled version 1 enabled version 2 enabledUse the show ssh key command to display the host key pair details for the specified key or for all keys, if no key is specified. See Example 14-12.
Example 14-12 Displays Host Key Pair Details
switch# show ssh key rsa1 Keys generated:Sun Jan 13 07:16:26 19801024 35fingerprint:1024 67:76:02:bd:3e:8d:f5:ad:59:5a:1e:c4:5e:44:03:07could not retrieve rsa key informationdsa Keys generated:Sun Jan 13 07:40:08 1980ssh-dss AAAAB3NzaC1kc3MAAABBAJTCRQOydNRel2v7uiO6Fix+OTn8eGdnnDVxw5eJs5OcOEXOyjaWcMMYsEgxc9ada1NElp8Wy7GPMWGOQYj9CU0AAAAVAMCcWhNN18zFNOIPo7cU3t7d0iEbAAAAQBdQ8UAOi/Cti84qFb3kTqXlS9mEhdQUo0lHcH5bw5PKfj2Y/dLR437zCBKXetPj4p7mhQ6Fq5os8RZtJEyOsNsAAABAA0oxZbPyWeR5NHATXiyXdPI7j9i8fgyn9FNipMkOF2Mn75Mi/lqQ4NIq0gQNvQOx27uCeQlRts/QwI4q68/eaw==fingerprint:512 f7:cc:90:3d:f5:8a:a9:ca:48:76:9f:f8:6e:71:d4:aeSNMP Security
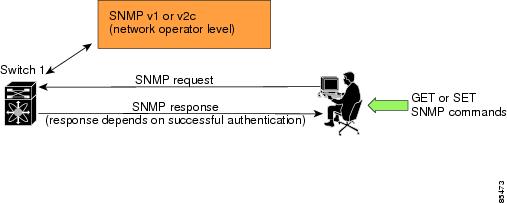
SNMP is an application layer protocol that facilitates the exchange of management information between network devices. In all Cisco MDS 9000 Family switches, three SNMP versions are available: SNMPv1, SNMPv2c, and SNMPv3 (see Figure 14-4).
Figure 14-4 SNMP Security
Note
Users and roles configured through the CLI are different from users and roles configured through SNMP. These configurations do not directly correspond with each other. However, you can configure both CLI and SNMP identically, if required.
SNMP users are different from CLI users. SNMP users also have role-based authentication for roles and authorization purposes.
SNMP Version 1 and Version 2c
SNMPv1 and SNMPv2c use a community string match for user authentication. Community strings provided a weak form of access control in earlier versions of SNMP. SNMPv3 provides much improved access control using strong authentication and should be preferred over SNMPv1 and SNMPv2c wherever it is supported.
SNMP Version 3
SNMPv3 is an interoperable standards-based protocol for network management. SNMPv3 provides secure access to devices by a combination of authenticating and encrypting frames over the network. The security features provided in SNMPv3 are:
•
Message integrity—Ensures that a packet has not been tampered with in-transit.
•
Authentication—Determines the message is from a valid source.
•
Encryption—Scrambles the packet contents to prevent it from being seen by unauthorized sources.
SNMPv3 provides for both security models and security levels. A security model is an authentication strategy that is set up for a user and the role in which the user resides. A security level is the permitted level of security within a security model. A combination of a security model and a security level determines which security mechanism is employed when handling an SNMP packet.
Group-Based SNMP Access
Note
Because group is a standard SNMP term used industry-wide, we refer to role(s) as group(s) in this SNMP section.
SNMP access rights are organized by groups. Each group in SNMP is similar to a role through the CLI. Each group is defined with three accesses: read access, write access, and notification access. Each access can be enabled or disabled within each group.
Switches in the Cisco MDS 9000 Family are preconfigured with two default groups: network-admin and network-operator. The network-admin role has the access rights to define custom roles with custom privileges. You can begin communicating with the agent once the your user name is created, your roles are set up by your administrator, and you are added to the roles.
Note
Users and roles configured through the CLI are different from users and groups configured through SNMP. These configurations do not directly correspond with each other. However, you can configure both CLI and SNMP identically, if required.
Creating SNMP Groups
You can create SNMP groups through SNMP by configuring a group entry in the vcacmAccessTable on the switch.
Refer to RFC2575.
Creating and Modifying Users
You can create users or modify existing users using SNMP or the CLI.
•
SNMP—Create a user as a clone of an existing user in the vsmUserTable on the switch. Once you have created the user, change the cloned secret key before activating the user. Refer to RFC2574.
Note
You must explicitly configure password(s) for SNMP users. The SNMP user passwords are not generated as the part of the configuration file as they are not portable across devices.
The password is limited to a minimum of 8 characters and a maximum of 64 characters.
Tip
An SNMP user must be created on each switch to which the user requires access. If the user is managing 10 switches, each of the 10 switches must have the SNMP user defined.
•
CLI—You can create a user or modify an existing user using the snmp-server user command.
By default only two groups are available in a Cisco MDS 9000 Family switch—network-operator and network-admin. To assign a user to a new SNMP group, you must first create the SNMP group.
Note
SNMP groups can only be created in SNMP (see the "Creating SNMP Groups" section).
To create or modify SNMP users using the CLI, follow these steps:
Note
Avoid using the localizedkey option when configuring an SNMP user from CLI. The localized keys are not portable across devices as they contain device engine ID information. If a configuration file is copied to the device, the passwords may not be set correctly if the configuration file was generated at a different device. Explicitly configure the desired passwords after copying the configuration into the device.
Forcing Identical SNMP and CLI Passwords
You can force the SNMPv3 password and the CLI password to be the same. You must know the SNMPv3 password to change the password using the CLI. Use CLI password to synchronize the SNMP password The password is limited to a minimum of 8 characters and a maximum of 64 characters.
CautionTo change the SNMP password, a clear text CLI password is required.
To modify the secret key for an SNMPv3 user, refer to RFC2574.
To update the SNMPv3 password from the CLI, follow these steps:
Assigning Users to Groups
Once the user and the group are created, the administrator should configure an entry in the vacmSecurityToGroupTable to add the configured user to a configured group.
To assign users to groups through SNMP, refer to RFC2575.
To assign users to groups through the CLI, refer to the procedure specified in the "Creating and Modifying Users" section.
Adding or Deleting Communities
You can configure read-only or read-write access for SNMP users by using the snmp-server community CLI command. Use the no form of the command to delete the configured community. Refer to RFC2576.
To create an SNMPv1 or SNMPv2c community, follow these steps:
Displaying SNMP Security Information
Use the show snmp commands to display configured SNMP information (see Example 14-13 and 14-14).
Example 14-13 Displays SNMP User Details
switch# show snmp userUser Group Auth Priv____ _____ ____ ____steve network-admin md5 dessadmin network-admin md5 desstever network-operator md5 desExample 14-14 Displays SNMP Community Information
switch# show snmp communityCommunity Access--------- ------private rwpublic rov93RACqPNH roDisplaying SNMP Counter Information
The show snmp command displays counter information for SNMP contact, location, and packet settings. This command provides information that is used entirely by the Cisco MDS 9000 Family Fabric Manager (see the Cisco MDS 9000 Family Fabric Manager User Guide). See Example 14-15.
Example 14-15 Displays SNMP
switch# show snmpsys contact:sys location:4 SNMP packets input0 Bad SNMP versions4 Unknown community name0 Illegal operation for community name supplied0 Encoding errors0 Number of requested variables0 Number of altered variables0 Get-request PDUs0 Get-next PDUs0 Set-request PDUs0 SNMP packets output0 Too big errors0 No such name errors0 Bad values errors0 General errorsDefault Security Settings
Table 14-2 lists the default settings for all security features in any switch.

 Feedback
Feedback