- Index
- Preface
- Product Overview
- Command-line Interfaces
- Configuring the Switch for the First Time
- Administering the Switch
- Configuring the Cisco IOS In Service Software Upgrade Process
- Configuring Interfaces
- Checking Port Status and Connectivity
- Configuring Supervisor Engine Redundancy Using RPR and SSO
- Configuring Cisco NSF with SSO Supervisor Engine Redundancy
- Environmental Monitoring and Power Management
- Configuring Power over Ethernet
- Configuring Energy Wise
- Configuring the Catalyst 4500 Series Switch with Cisco Network Assistant
- Configuring VLANs, VTP, and VMPS
- Configuring IP Unnumbered Interface
- Configuring Layer 2 Ethernet Interfaces
- Configuring SmartPort Macros
- Auto SmartPort Macro
- Configuring STP and MST
- Configuring Flex Links and the MAC Address-Table Move Update Feature
- Configuring Resilient Ethernet Protocol
- Configuring Optional STP Features
- Configuring EtherChannels
- Configuring IGMP Snooping and Filtering
- Configuring IPv6 MLD Snooping
- Configuring 802.1Q and Layer 2 Protocol Tunneling
- Configuring CDP
- Configuring LLDP and LLDP-MED
- Configuring UDLD
- Configuring Unidirectional Ethernet
- Configuring Layer 3 Interfaces
- Configuring Cisco Express Forwarding
- Configuring Unicast Reverse Path Forwarding
- Configuring IP Multicast
- Configuring ANCP Client
- Configuring Policy-Based Routing
- Configuring VRF-lite
- Configuring Quality of Service
- Configuring Voice Interfaces
- Configuring Private VLANs
- Configuring 802.1X Port-Based Authentication
- Configuring PPPoE Intermediate Agent
- Configuring Web-Based Authentication
- Configuring Port Security
- Configuring Control Plane Policing
- Configuring DHCP Snooping, IP Source Guard, and IPSG for Static Hosts
- Configuring Dynamic ARP Inspection
- Configuring Network Security with ACLs
- IPv6
- Port Unicast and Multicast Flood Blocking
- Configuring Storm Control
- Configuring SPAN and RSPAN
- Configuring System Message Logging
- Configuring SNMP
- Configuring NetFlow
- Configuring Ethernet CFM and OAM
- Configuring Y.1731 (AIS and RDI)
- Configuring Call Home
- Configuring Cisco IOS IP SLAs Operations
- Configuring RMON
- Performing Diagnostics
- Configuring WCCP Version 2 Services
- ROM Monitor
- Configuring MIB Support
- Acronyms
- Managing the System Time and Date
- Building the Address Table
- MAC Addresses and VLANs
- Default MAC Address Table Configuration
- Changing the Address Aging Time
- Removing Dynamic Address Entries
- Configuring MAC Change Notification Traps
- Configuring MAC Move Notification Traps
- Configuring MAC Threshold Notification Traps
- Adding and Removing Static Address Entries
- Configuring Unicast MAC Address Filtering
- Disabling MAC Address Learning on a VLAN
- Displaying Address Table Entries
Administering the Switch
This chapter describes how to perform one-time operations to administer the Catalyst 4500 Series switch.
This chapter also describes how to install and configure the Embedded CiscoView network management system to provide a graphical representation of a Catalyst 4500 series switch and to provide a GUI-based management and configuration interface.
This chapter includes the following major sections:
- Managing the System Time and Date
- Configuring a System Name and Prompt
- Creating a Banner
- Managing the MAC Address Table
- Managing the ARP Table
- Configuring Embedded CiscoView Support

Note![]() For complete syntax and usage information for the switch commands used in this chapter, look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
For complete syntax and usage information for the switch commands used in this chapter, look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
http://www.cisco.com/en/US/products/hw/switches/ps4324/index.html
If the command is not found in the Catalyst 4500 Command Reference, it is located in the larger Cisco IOS library. Refer to the Cisco IOS Command Reference and related publications at this location:
http://www.cisco.com/en/US/products/ps6350/index.html
Managing the System Time and Date
You can configure the system time and date on your switch manually or automatically by using Network Time Protocol (NTP).
These sections contain this configuration information:
System Clock
The core of the time service is the system clock, which monitors the date and time. This clock starts when the system starts.
The system clock can provide time to these services:
The system clock keeps track of time internally based on Universal Time Coordinated (UTC), also known as Greenwich Mean Time (GMT). You can configure information about the local time zone and summer time (daylight saving time) so that the time is correct for the local time zone.
The system clock keeps track of whether the time is authoritative or not (whether it was set by a time source considered to be authoritative). If it is not authoritative, the time is available only for display purposes and is not redistributed. For configuration information, see the “Configuring Time and Date Manually” section.
Understanding Network Time Protocol
The NTP is designed to synchronize a network of devices. NTP runs over User Datagram Protocol (UDP), which runs over IP. NTP is documented in RFC 1305.
An NTP network usually gets its time from an authoritative time source, such as a radio clock or an atomic clock attached to a time server. NTP then distributes this time across the network. NTP is extremely efficient; no more than one packet per minute is necessary to synchronize two devices to within a millisecond of one another.
NTP uses the concept of a stratum to describe how many NTP hops away a device is from an authoritative time source. A stratum 1 time server has a radio or atomic clock directly attached, a stratum 2 time server receives its time through NTP from a stratum 1 time server, and so on. A device running NTP automatically chooses as its time source the device with the lowest stratum number with which it communicates through NTP. This strategy effectively builds a self-organizing tree of NTP speakers.
NTP avoids synchronizing to a device whose time might not have been synchronized. NTP also compares the time reported by several devices and does not synchronize to a device whose time is significantly different than the others, even if its stratum is lower.
The communications between devices running NTP (known as associations) are usually statically configured; each device is given the IP address of all devices with which it should associate. Accurate timekeeping is possible by exchanging NTP messages between each pair of devices with an association. However, in a LAN environment, NTP can be configured to use IP broadcast messages instead. This alternative reduces configuration complexity because each device can be configured to send or receive broadcast messages; however, information flow is one-way only.
The time kept on a device is a critical resource; you should use the security features of NTP to avoid the accidental or malicious setting of an incorrect time. Two mechanisms are available: an access list-based restriction scheme and an encrypted authentication mechanism.
Cisco’s implementation of NTP does not support stratum 1 service; it is not possible to connect to a radio or atomic clock. We recommend that the time service for your network be derived from the public NTP servers available on the IP Internet.
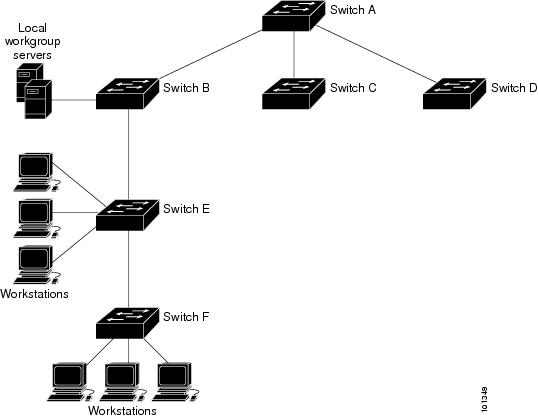
Figure 4-1 shows a typical network example using NTP. Switch A is the NTP master, with Switches B, C, and D configured in NTP server mode, in server association with Switch A. Switch E is configured as an NTP peer to the upstream and downstream switches, Switch B and Switch F, respectively.
Figure 4-1 Typical NTP Network Configuration
If the network is isolated from the Internet, Cisco’s implementation of NTP allows a device to act as if it is synchronized through NTP, when it is not. Other devices then synchronize to that device through NTP.
NTP time overrides the time set by any other method.
Several manufacturers include NTP software for their host systems, and a public version for systems running UNIX and its various derivatives is also available. This software allows host systems to be synchronized as well.
Configuring NTP
Default NTP Configuration
Table 4-1 shows the default NTP configuration.
|
|
|
|---|---|
Disabled; no interface sends or receives NTP broadcast packets. |
|
NTP is enabled on all interfaces by default. All interfaces receive NTP packets.
Configuring NTP Authentication
This procedure must be coordinated with the administrator of the NTP server; the information you configure in this procedure must be matched by the servers used by the switch to synchronize its time to the NTP server.
To authenticate the associations (communications between devices running NTP that provide for accurate timekeeping) with other devices for security purposes, perform this task:
To disable NTP authentication, use the no ntp authenticate global configuration command. To remove an authentication key, use the no ntp authentication-key number global configuration command. To disable authentication of the identity of a device, use the no ntp trusted-key key-number global configuration command.
This example shows how to configure the switch to synchronize only to devices providing authentication key 42 in the device’s NTP packets:
Configuring NTP Associations
An NTP association can be a peer association (this switch can either synchronize to the other device or allow the other device to synchronize to it), or it can be a server association (meaning that only this switch synchronizes to the other device, and not the other way around).
To form an NTP association with another device, perform this task:
You need to configure only one end of an association; the other device can automatically establish the association. If you are using the default NTP version (Version 3) and NTP synchronization does not occur, try using NTP Version 2. Many NTP servers on the Internet run Version 2.
To remove a peer or server association, use the no ntp peer ip-address or the no ntp server ip-address global configuration command.
This example shows how to configure the switch to synchronize its system clock with the clock of the peer at IP address 172.16.22.44 using NTP Version 2:
Configuring NTP Broadcast Service
The communications between devices running NTP (known as associations) are usually statically configured; each device is given the IP addresses of all devices with which it should form associations. Accurate timekeeping is possible by exchanging NTP messages between each pair of devices with an association. However, in a LAN environment, NTP can be configured to use IP broadcast messages instead. This alternative reduces configuration complexity because each device can be configured to send or receive broadcast messages. However, the information flow is one-way only.
The switch can send or receive NTP broadcast packets on an interface-by-interface basis if there is an NTP broadcast server, such as a router, broadcasting time information on the network. The switch can send NTP broadcast packets to a peer so that the peer can synchronize to it. The switch can also receive NTP broadcast packets to synchronize its own clock. This section provides procedures for both sending and receiving NTP broadcast packets.
To configure the switch to send NTP broadcast packets to peers so that they can synchronize their clock to the switch, perform this task:
To disable the interface from sending NTP broadcast packets, use the no ntp broadcast interface configuration command.
This example shows how to configure a port to send NTP Version 2 packets:
To configure the switch to receive NTP broadcast packets from connected peers, perform this task:
To disable an interface from receiving NTP broadcast packets, use the no ntp broadcast client interface configuration command. To change the estimated round-trip delay to the default, use the
no ntp broadcastdelay global configuration command.
This example shows how to configure a port to receive NTP broadcast packets:
Configuring NTP Access Restrictions
You can control NTP access on two levels as described in these sections:
Creating an Access Group and Assigning a Basic IP Access List
To control access to NTP services by using access lists, perform this task:
The access group keywords are scanned in this order, from least restrictive to most restrictive:
1.![]() peer —Allows time requests and NTP control queries and allows the switch to synchronize itself to a device whose address passes the access list criteria.
peer —Allows time requests and NTP control queries and allows the switch to synchronize itself to a device whose address passes the access list criteria.
2.![]() serve —Allows time requests and NTP control queries, but does not allow the switch to synchronize itself to a device whose address passes the access list criteria.
serve —Allows time requests and NTP control queries, but does not allow the switch to synchronize itself to a device whose address passes the access list criteria.
3.![]() serve-only —Allows only time requests from a device whose address passes the access list criteria.
serve-only —Allows only time requests from a device whose address passes the access list criteria.
4.![]() query-only —Allows only NTP control queries from a device whose address passes the access list criteria.
query-only —Allows only NTP control queries from a device whose address passes the access list criteria.
If the source IP address matches the access lists for more than one access type, the first type is granted. If no access groups are specified, all access types are granted to all devices. If any access groups are specified, only the specified access types are granted.
To remove access control to the switch NTP services, use the
no ntp access-group { query-only | serve-only | serve | peer } global configuration command.
This example shows how to configure the switch to allow itself to synchronize to a peer from access list 99. However, the switch restricts access to allow only time requests from access list 42:
Disabling NTP Services on a Specific Interface
NTP services are enabled on all interfaces by default.
To disable NTP packets from being received on an interface, perform this task:
Configuring the Source IP Address for NTP Packets
When the switch sends an NTP packet, the source IP address is normally set to the address of the interface through which the NTP packet is sent. To use a particular source IP address for all NTP packets, use the ntp source global configuration command. The address is taken from the specified interface. This command is useful if the address on an interface cannot be used as the destination for reply packets.
To configure a specific interface from which the IP source address is to be taken, perform this task:
The specified interface is used for the source address for all packets sent to all destinations. If a source address is to be used for a specific association, use the source keyword in the ntp peer or n tp server global configuration command as described in the “Configuring NTP Associations” section.
Displaying the NTP Configuration
Use the following privileged EXEC commands to display NTP information:
For detailed information about the fields in these displays, see the
Cisco IOS Configuration Fundamentals Command Reference, Release 12.3.
Configuring Time and Date Manually
If no other source of time is available, you can manually configure the time and date after the system is restarted. The time remains accurate until the next system restart. We recommend that you use manual configuration only as a last resort. If you have an outside source to which the switch can synchronize, you do not need to manually set the system clock.
Setting the System Clock
If you have an outside source on the network that provides time services, such as an NTP server, you do not need to manually set the system clock.
To set the system clock, perform this task:
|
|
|
|
|---|---|---|
|
|
This example shows how to manually set the system clock to 1:32 p.m. on July 23, 2001:
Displaying the Time and Date Configuration
To display the time and date configuration, use the show clock [ detail ] privileged EXEC command.
The system clock keeps an authoritative flag that shows whether the time is authoritative (believed to be accurate). If the system clock was set by a timing source such as NTP, the flag is set. If the time is not authoritative, it is used only for display purposes. Until the clock is authoritative and the authoritative flag is set, the flag prevents peers from synchronizing to the clock when the peers’ time is invalid.
The symbol that precedes the show clock display has this meaning:
Configuring the Time Zone
To manually configure the time zone, perform this task:
The minutes-offset variable in the clock timezone global configuration command is available for those cases where a local time zone is a percentage of an hour different from UTC. For example, the time zone for some sections of Atlantic Canada (AST) is UTC-3.5, where the 3 means 3 hours and.5 means 50 percent. The necessary command is clock timezone AST -3 30.
Configuring Summer Time (Daylight Saving Time)
To configure summer time (daylight saving time) in areas where it starts and ends on a particular day of the week each year, perform this task:
The first part of the clock summer-time global configuration command specifies when summer time begins, and the second part specifies when it ends. All times are relative to the local time zone. The start time is relative to standard time. The end time is relative to summer time. If the starting month is after the ending month, the system assumes that you are in the southern hemisphere.
This example shows how to specify that summer time starts on the first Sunday in April at 02:00 and ends on the last Sunday in October at 02:00:
If summer time in your area does not follow a recurring pattern (configure the exact date and time of the next summer time events), perform this task:
The first part of the clock summer-time global configuration command specifies when summer time begins, and the second part specifies when it ends. All times are relative to the local time zone. The start time is relative to standard time. The end time is relative to summer time. If the starting month is after the ending month, the system assumes that you are in the southern hemisphere.
To disable summer time, use the no clock summer-time global configuration command.
This example shows how to set summer time to start on October 12, 2000, at 02:00, and end on April 26, 2001, at 02:00:
Configuring a System Name and Prompt
You configure the system name on the switch to identify it. By default, the system name and prompt are Switch.
If you have not configured a system prompt, the first 20 characters of the system name are used as the system prompt. A greater-than symbol [>] is appended. The prompt is updated whenever the system name changes.
For complete syntax and usage information for the commands used in this section, see the Cisco IOS Configuration Fundamentals Command Reference, Release 12.3 and the Cisco IOS IP Command Reference, Volume 2 of 3: Routing Protocols, Release 12.3.
These sections contain this configuration information:
Configuring a System Name
To manually configure a system name, perform this task:
When you set the system name, it is also used as the system prompt.
Understanding DNS
The DNS protocol controls the Domain Name System (DNS), a distributed database with which you can map hostnames to IP addresses. When you configure DNS on your switch, you can substitute the hostname for the IP address with all IP commands, such as ping, telnet, connect, and related Telnet support operations.
IP defines a hierarchical naming scheme that allows a device to be identified by its location or domain. Domain names are pieced together with periods (.) as the delimiting characters. For example, Cisco Systems is a commercial organization that IP identifies by a com domain name, so its domain name is cisco.com. A specific device in this domain, for example, the File Transfer Protocol (FTP) system is identified as ftp.cisco.com.
To keep track of domain names, IP has defined the concept of a domain name server, which holds a cache (or database) of names mapped to IP addresses. To map domain names to IP addresses, you must first identify the hostnames, specify the name server that is present on your network, and enable the DNS.
Default DNS Configuration
Table 4-2 shows the default DNS configuration.
|
|
|
|---|---|
Setting Up DNS
To set up your switch to use the DNS, perform this task:
If you use the switch IP address as its hostname, the IP address is used and no DNS query occurs. If you configure a hostname that contains no periods (.), a period followed by the default domain name is appended to the hostname before the DNS query is made to map the name to an IP address. The default domain name is the value set by the ip domain-name global configuration command. If there is a period (.) in the hostname, the Cisco IOS software looks up the IP address without appending any default domain name to the hostname.
Displaying the DNS Configuration
To display the DNS configuration information, use the show running-config privileged EXEC command.
Creating a Banner
You can configure a message-of-the-day (MOTD) and a login banner. The MOTD banner displays on all connected terminals at login and is useful for sending messages that affect all network users (such as impending system shutdowns).
The login banner also displays on all connected terminals. It appears after the MOTD banner and before the login prompts.

Note![]() For complete syntax and usage information for the commands used in this section, see the Cisco IOS Configuration Fundamentals Command Reference, Release 12.3.
For complete syntax and usage information for the commands used in this section, see the Cisco IOS Configuration Fundamentals Command Reference, Release 12.3.
The contain this configuration information:
- Default Banner Configuration
- Configuring a Message-of-the-Day Login Banner
- Configuring a Login Banner
Default Banner Configuration
Configuring a Message-of-the-Day Login Banner
You can create a single or multiline message banner that appears on the screen when someone logs in to the switch.
To configure a MOTD login banner, perform this task:
This example shows how to configure a MOTD banner for the switch by using the pound sign (#) symbol as the beginning and ending delimiter:
This example shows the banner that appears from the previous configuration:
Configuring a Login Banner
You can configure a login banner to be displayed on all connected terminals. This banner appears after the MOTD banner and before the login prompt.
To configure a login banner, perform this task:
This example shows how to configure a login banner for the switch by using the dollar sign ($) symbol as the beginning and ending delimiter:
Managing the MAC Address Table
The MAC address table contains address information that the switch uses to forward traffic between ports. All MAC addresses in the address table are associated with one or more ports. The address table includes these types of addresses:
- Dynamic address—A source MAC address that the switch learns and then ages when it is not in use.
- Static address—A manually entered unicast address that does not age and that is not lost when the switch resets.
The address table lists the destination MAC address, the associated VLAN ID, and port number associated with the address and the type (static or dynamic).

Note![]() For complete syntax and usage information for the commands used in this section, see the command reference for this release.
For complete syntax and usage information for the commands used in this section, see the command reference for this release.
These sections contain this configuration information:
- Building the Address Table
- MAC Addresses and VLANs
- Default MAC Address Table Configuration
- Changing the Address Aging Time
- Removing Dynamic Address Entries
- Configuring MAC Change Notification Traps
- Configuring MAC Move Notification Traps
- Configuring MAC Threshold Notification Traps
- Adding and Removing Static Address Entries
- Configuring Unicast MAC Address Filtering
- Disabling MAC Address Learning on a VLAN
- Displaying Address Table Entries
Building the Address Table
With multiple MAC addresses supported on all ports, you can connect any port on the switch to individual workstations, repeaters, switches, routers, or other network devices. The switch provides dynamic addressing by learning the source address of packets it receives on each port and adding the address and its associated port number to the address table. As stations are added or removed from the network, the switch updates the address table, adding new dynamic addresses and aging out those that are not in use.
The aging interval is globally configured. However, the switch maintains an address table for each VLAN, and STP can accelerate the aging interval on a per-VLAN basis.
The switch sends packets between any combination of ports, based on the destination address of the received packet. Using the MAC address table, the switch forwards the packet only to the port associated with the destination address. If the destination address is on the port that sent the packet, the packet is filtered and not forwarded. The switch always uses the store-and-forward method: complete packets are stored and checked for errors before transmission.
MAC Addresses and VLANs
All addresses are associated with a VLAN. An address can exist in more than one VLAN and have different destinations in each. Unicast addresses, for example, could be forwarded to port 1 in VLAN 1 and ports 9, 10, and 1 in VLAN 5.
Each VLAN maintains its own logical address table. A known address in one VLAN is unknown in another until it is learned or statically associated with a port in the other VLAN.
When PVLANs are configured, address learning depends on the type of MAC address:
- Dynamic MAC addresses learned in one VLAN of a PVLAN are replicated in the associated VLANs. For example, a MAC address learned in a private-VLAN secondary VLAN is replicated in the primary VLAN.
- Static MAC addresses configured in a primary or secondary VLAN are not replicated in the associated VLANs. When you configure a static MAC address in a PVLAN primary or secondary VLAN, you should also configure the same static MAC address in all associated VLANs.
For more information about PVLANs, see Chapter39, “Configuring Private VLANs”
Default MAC Address Table Configuration
Table 4-3 shows the default MAC address table configuration.
|
|
|
|---|---|
Changing the Address Aging Time
Dynamic addresses are source MAC addresses that the switch learns and then ages when they are not in use. You can change the aging time setting for all VLANs or for a specified VLAN.
Setting too short an aging time can cause addresses to be prematurely removed from the table. When the switch receives a packet for an unknown destination, it floods the packet to all ports in the same VLAN as the receiving port. This unnecessary flooding can impact performance. Setting too long an aging time can cause the address table to be filled with unused addresses, which prevents new addresses from being learned. Flooding results, which can impact switch performance.
To configure the dynamic address table aging time, perform this task:
Removing Dynamic Address Entries
To remove all dynamic entries, use the clear mac address-table dynamic command in EXEC mode. You can also remove a specific MAC address (clear mac address-table dynamic address mac-address), remove all addresses on the specified physical port or port channel
(clear mac address-table dynamic interface interface-id), or remove all addresses on a specified VLAN (clear mac address-table dynamic vlan vlan-id).
To verify that dynamic entries have been removed, use the show mac address-table dynamic privileged EXEC command.
Configuring MAC Change Notification Traps
MAC change notification allows you to track users on a network by storing the MAC change activity on the switch. Whenever the switch learns or removes a MAC address, an SNMP notification can be generated and sent to the network management system. If you have many users entering and exiting the network, you can set a trap interval time to bundle the notification traps and reduce network traffic. The MAC notification history table stores the MAC address activity for each hardware port for which the trap is enabled. MAC address notifications are generated for dynamic and static MAC addresses; events are not generated for self addresses or multicast addresses.
To send MAC change notification traps to an NMS host, perform this task:
This example shows how to specify 172.69.59.93 as the network management system, enable the switch to send MAC change notification traps to the network management system, enable the MAC change notification feature, set the interval time to 60 seconds, set the history-size to 100 entries, and enable traps whenever a MAC address is added on the specified port:
Configuring MAC Move Notification Traps
When you configure MAC move notification, an SNMP notification is generated and sent to the network management system whenever a MAC address moves from one port to another within the same VLAN.
To configure MAC move notification, perform this task:
This example shows how to specify 172.69.59.93 as the network management system, enable the switch to send MAC move notification traps to the NMS, enable the MAC move notification feature, and enable traps whenever a MAC address moves from one port to another:
Configuring MAC Threshold Notification Traps
When you configure MAC threshold notification, an SNMP notification is generated and sent to the network management system when a MAC address table (MAT) threshold limit is reached or exceeded.
To configure MAC address threshold notification, perform this task:
This example shows how to specify 172.69.59.93 as the network management system, enable the MAC threshold notification feature, enable the switch to send MAC threshold notification traps to the NMS, set the interval to 123 seconds, and set the limit to 78 percent:
Adding and Removing Static Address Entries
A static address has these characteristics:
- It is manually entered in the address table and must be manually removed.
- It can be a unicast or multicast address.
- It does not age and is retained when the switch restarts.
You can add and remove static addresses and define the forwarding behavior for them. The forwarding behavior defines how a port that receives a packet forwards it to another port for transmission. Because all ports are associated with at least one VLAN, the switch acquires the VLAN ID for the address from the ports that you specify. You can specify a different list of destination ports for each source port.
A packet with a static address that arrives on a VLAN where it has not been statically entered is flooded to all ports and not learned.
You add a static address to the address table by specifying the destination MAC unicast address and the VLAN from which it is received. Packets received with this destination address are forwarded to the interface specified with the interface-id option.
When you configure a static MAC address in a private-VLAN primary or secondary VLAN, you should also configure the same static MAC address in all associated VLANs. Static MAC addresses configured in a private-VLAN primary or secondary VLAN are not replicated in the associated VLAN. For more information about PVLANs, see Chapter39, “Configuring Private VLANs”
To add a static address, perform this task:
This example shows how to add the static address c2f3.220a.12f4 to the MAC address table. When a packet is received in VLAN 4 with this MAC address as its destination address, the packet is forwarded to the specified port:
Configuring Unicast MAC Address Filtering
When unicast MAC address filtering is enabled, the switch drops packets with specific source or destination MAC addresses. This feature is disabled by default and only supports unicast static addresses.
When using unicast address filtering, consider these guidelines:
- Multicast MAC addresses, broadcast MAC addresses, and router MAC addresses are not supported. If you specify one of these addresses when entering the mac address-table static vlan drop global configuration command, one of these messages appears:
- Packets that are forwarded to the CPU are also not supported.
- If you add a unicast MAC address as a static address and configure unicast MAC address filtering, the switch either adds the MAC address as a static address or drops packets with that MAC address, depending on which command was entered last. The second command that you entered overrides the first command.
For example, if you enter the mac address-table static vlan interface global configuration command followed by the mac address-table static vlan drop command, the switch drops packets with the specified MAC address as a source or destination.
If you enter the mac address-table static vlan drop global configuration command followed by the mac address-table static vlan interface command, the switch adds the MAC address as a static address.
You enable unicast MAC address filtering and configure the switch to drop packets with a specific address by specifying the source or destination unicast MAC address and the VLAN from which it is received.
To configure the switch to drop a source or destination unicast static address, perform this task:
This example shows how to enable unicast MAC address filtering and to configure the switch to drop packets that have a source or destination address of c2f3.220a.12f4. When a packet is received in VLAN 4 with this MAC address as its source or destination, the packet is dropped:

Note![]() To filter MAC addresses on a secondary VLAN, specify the corresponding primary VLAN in the above configuration. If the specified VLAN is a primary VLAN, all matching packets received in this primary VLAN and associated secondary VLANs are dropped.
To filter MAC addresses on a secondary VLAN, specify the corresponding primary VLAN in the above configuration. If the specified VLAN is a primary VLAN, all matching packets received in this primary VLAN and associated secondary VLANs are dropped.
Disabling MAC Address Learning on a VLAN
By default, MAC address learning is enabled on all VLANs on the switch. By controlling which VLANs can learn MAC addresses, you can manage the available MAC address table space. By disabling learning on a VLAN, you can conserve the MAC address table space because all the MAC addresses seen on this VLAN are not learned.
Before disabling MAC address learning, you should understand the network topology and features deployed. Many Layer 2 features use MAC addresses and may not work properly if learning is disabled. Because disabling learning causes flooding of packets, you need to understand the impact of flooding on the network.
Configuring Disable MAC Address Learning
To disable MAC address learning on a VLAN, perform this task:
This example shows how to disable learning on any VLAN or range of VLANs:
Usage Guidelines

Note![]() These guidelines are advisory only. Contact the Cisco solution provider team for specific solution implementations.
These guidelines are advisory only. Contact the Cisco solution provider team for specific solution implementations.
When disabling MAC address learning on a VLAN, consider these guidelines:
- If learning is disabled on a VLAN with an SVI interface, it floods every IP packet in the Layer 2 domain. Because this flooding may be undesirable, you should disable MAC address learning on a SVI VLAN carefully.
- If you provide a VLAN range that includes reserved VLAN (such as 1000-1006), the command is accepted and disable learning is enabled for all VLANs except for 1002-005 (that is, 1000-1001,1006). However, if you specify an invalid range (such as 1-5000), the command fails and disable learning is not enabled on any of the VLANs.
- Both RSPAN and the MAC learning disable feature share a hardware restriction on Supervisor Engines II, IV, and V. If the combination of VLANs configured with RSPAN and learning disable exceeds four, hardware MAC table resources are consumed to emulate learning disable on the additional VLANs. High CPU occur when these resources are exhausted.
- With PVLANs, you need to disable learning on the primary VLAN and all secondary VLANs associated with that primary VLANs. Otherwise, you encounter traffic flooding in one direction and unicast flooding in the other direction.
- To disable MAC address learning on a VLAN, consider the flooding implications.
Deployment Scenarios
Metro (Point to Point Links)
In this topology, you have two ports on a VLAN; traffic enters one and must exit the other. On a point-to-point link in metro networks, numerous MAC addresses are on these types of ports by disabling learning on the VLAN to which these two ports belong, many entries in the MAC address table space can be saved. Because there is only one egress port for the traffic, you can flood the packet and avoid having to learn all the MAC addresses seen on this port. This process saves considerable space in the MAC address table.
To obtain source learning, packets are bridged as Layer 2 flood packets. Replicated packets use a distinct dedicated bandwidth. Regardless of the number of ports in a flood set, a flood packet always consumes replication packet bandwidth, which consumes some multicast and broadcast packet-processing bandwidth (Figure 4-2).
Figure 4-2 Disabling MAC Address Learning: Point-to-Point Links

Network Load Balancers
In this topology, you have two devices: one active and one standby. To perform load balancing, both devices must receive all packets. You could place both devices on the same VLAN. If learning can be disabled on this VLAN, the packet is flooded and both devices receive all traffic destined to any MAC address on the VLAN. You also can assign a multicast MAC address to both load balancers to ensure that all packets reach them. (Figure 4-3).
Figure 4-3 Disabling MAC Address Learning: Network Load Balancers

Layer 2 Firewall or Cache
In this topology, a rewritten Layer 3 packet is routed back to a Layer 2 firewall (or cache) before exiting. When the packet reenters the switch from the firewall, it possesses the switch’s MAC address because the packet was previously routed. If the ingress port is a switch port, the switch learns the router’s MAC address. For a routed port or SVI, however, the switch does not learn the address. Source misses are generated continuously for all arriving data packets and the switch shows a very high CPU utilization.
By disabling learning on the VLAN that the firewall or cache egress is connected to, you will routinely suppress the source miss and do not observe high CPU utilization (Figure 4-4).
Figure 4-4 Disabling MAC Address Learning: Layer 2 Firewall/Cache

Feature Compatibility
The following features are compatible with disabling MAC address learning on a VLAN:
- EtherChannel—The learning disable feature has no impact on EtherChannel provided that the MAC learning state is either disabled or enabled for a VLAN on EtherChannel ports.
- Switch Virtual Interface (SVI, Layer 3 on a VLAN)— The learning disable feature has no impact on SVI. Although disabling MAC address learning on a SVI VLAN causes flooding, it does not impact any Layer 3 feature.
- REP—The learning disable feature has no impact on REP provided that the MAC learning state is either disabled or enabled for an active VLAN on a port where REP is running.
- Unicast, Multicast, and Broadcast—When you enable learning on a VLAN, learning is disabled on all types of traffic.
- DAI, ESMP, and IGMP snooping— These features do not interact with the learning disable feature.
- Control packets— Control packets arrive at the CPU even if learning is disabled.
- RSPAN— Learning on a VLAN and on an RSPAN are compatible.
- VLAN translation—To disable learning on a VLAN that is being translated, you must disable learning on the translated VLAN.
Feature Incompatibility
The following features are incompatible with disabling MAC address learning and do not work properly when the feature is enabled:
- 802.1X—The 802.1X class of features does not work when learning is disabled because some of these features require source miss, which is ignored.
- Port security— Port security VLANs requires learning to be enabled. To secure MAC addresses, packets must first arrive at the CPU. However, if you disable learning on a VLAN, SA suppression ensures that packets do not operate this way.
- Unicast flood blocking— When unicast flood blocking is enabled on a port, it is removed from the VLAN flood set. If learning is disabled on the same VLAN, the host connected to that port do not receive traffic.
- DHCP snooping—To send the packet out the correct port once a DHCP request has been resolved, DHCP snooping must learn the MAC address. If you disable learning, the switch do not know on which port to exit the packet; the two features are incompatible.
- Broadcast storm control— This feature does not interact with the learning disable feature.
- Flooding of packets in a VLAN domain in which learning is disabled through PVL.
Partial Feature Incompatibility
Although the following features are partially incompatible with disabling MAC address learning, they still retain a large portion of their functionality:
- FlexLink—FlexLink functions and upstream convergence is not impacted. However, downstream fast convergence uses a MAC table to send dummy multicast packets for each learned MAC address upstream to expedite downstream convergence. This situation does not happen if you enable learning disable. FlexLink downstream convergence occurs naturally, but it is slower if learning is enabled on that VLAN.
- PVLAN—To observe correct behavior, you must disable learning on the primary VLAN and all secondary VLANs associated with the primary VLAN.

Note![]() To avoid confusion, configure PVLAN similarly on both the primary and secondary VLANs in the PVLAN space.
To avoid confusion, configure PVLAN similarly on both the primary and secondary VLANs in the PVLAN space.
Displaying Address Table Entries
You can display the MAC address table by using one or more of the privileged EXEC commands described in Table 4-4 .
Managing the ARP Table
To communicate with a device (over Ethernet, for example), the software first must learn the 48-bit MAC address or the local data link address of that device. The process of learning the local data link address from an IP address is called address resolution.
The Address Resolution Protocol (ARP) associates a host IP address with the corresponding media or MAC addresses and the VLAN ID. Using an IP address, ARP finds the associated MAC address. When a MAC address is found, the IP-MAC address association is stored in an ARP cache for rapid retrieval and the IP datagram is encapsulated in a link-layer frame and sent over the network. Encapsulation of IP datagrams and ARP requests and replies on IEEE 802 networks other than Ethernet is specified by the Subnetwork Access Protocol (SNAP). By default, standard Ethernet-style ARP encapsulation (represented by the arpa keyword) is enabled on the IP interface.
ARP entries added manually to the table do not age and must be manually removed.
For CLI procedures, see the Cisco IOS Release 12.3 documentation on Cisco.com.
Configuring Embedded CiscoView Support
The Catalyst 4500 series switch supports CiscoView web-based administration using the Catalyst Web Interface (CWI) tool. CiscoView is a device management application that can be embedded on the switch flash and provides dynamic status, monitoring, and configuration information for your switch. CiscoView displays a physical view of your switch chassis with color-coded modules and ports and monitoring capabilities that display the switch status, performance, and other statistics. Configuration capabilities allow comprehensive changes to devices, if the required security privileges have been granted. The configuration and monitoring capabilities for the Catalyst 4500 series of switches mirror those available in CiscoView in all server-based CiscoWorks solutions, including CiscoWorks LAN Management Solution (LMS) and CiscoWorks Routed WAN Management Solution (RWAN).
These sections describe the Embedded CiscoView support available with Cisco IOS Release 12.1(20)EW and later releases:
- Understanding Embedded CiscoView
- Installing and Configuring Embedded CiscoView
- Displaying Embedded CiscoView Information
Understanding Embedded CiscoView
The Embedded CiscoView network management system is a web-based interface that uses HTTP and SNMP to provide a graphical representation of the switch and to provide a GUI-based management and configuration interface.
Installing and Configuring Embedded CiscoView
To install and configure Embedded CiscoView, perform this task:
|
|
|
|
|---|---|---|
Displays the contents of the device. If you are installing Embedded CiscoView for the first time, or if the CiscoView directory is empty, skip to Step 5. |
||
Switch# archive tar /xtract tftp:// ip address of tftp server /ciscoview.tar device_name :cv |
Extracts the CiscoView files from the tar file on the TFTP server to the CiscoView directory. |
|
Displays the contents of the device. In a redundant configuration, repeat Step 1 through Step 6 for the file system on the redundant supervisor engine. |
||

Note![]() The default password for accessing the switch web page is the enable-level password of the switch.
The default password for accessing the switch web page is the enable-level password of the switch.
The following example shows how to install and configure Embedded CiscoView on your switch:
For more information about web access to the switch, refer to the “Using the Cisco Web Browser” chapter in the Cisco IOS Configuration Fundamentals Configuration Guide at this URL:
http://www.cisco.com/en/US/docs/ios/fundamentals/configuration/guide/12_4t/cf_12_4t_book.html
Displaying Embedded CiscoView Information
To display the Embedded CiscoView information, enter the following commands:
|
|
|
|---|---|
The following example shows how to display the Embedded CiscoView file and version information:
 Feedback
Feedback