Restrictions for HSRP
-
HSRP is designed for use over multiaccess, multicast, or broadcast capable Ethernet LANs. HSRP is not intended as a replacement for existing dynamic protocols.
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
The Hot Standby Router Protocol (HSRP) is a First Hop Redundancy Protocol (FHRP) designed to allow for transparent failover of the first-hop IP device. HSRP provides high network availability by providing first-hop routing redundancy for IP hosts on networks configured with a default gateway IP address. HSRP is used in a group of routers for selecting an active device and a standby device. In a group of device interfaces, the active device is the device of choice for routing packets; the standby device is the device that takes over when the active device fails or when preset conditions are met.
HSRP is designed for use over multiaccess, multicast, or broadcast capable Ethernet LANs. HSRP is not intended as a replacement for existing dynamic protocols.
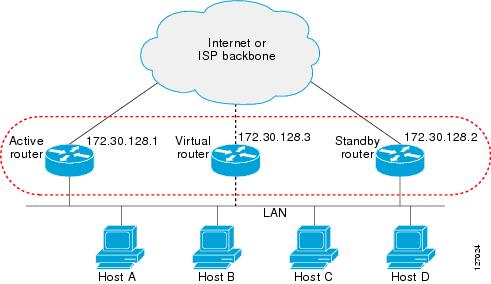
Most IP hosts have an IP address of a single device configured as the default gateway. When HSRP is used, the HSRP virtual IP address is configured as the host’s default gateway instead of the IP address of the device.
HSRP is useful for hosts that do not support a discovery protocol (such as ICMP Router Discovery Protocol [IRDP]) and cannot switch to a new device when their selected device reloads or loses power. Because existing TCP sessions can survive the failover, this protocol also provides a more transparent recovery for hosts that dynamically choose a next hop for routing IP traffic.
When HSRP is configured on a network segment, it provides a virtual MAC address and an IP address that is shared among a group of devices running HSRP. The address of this HSRP group is referred to as the virtual IP address. One of these devices is selected by the protocol to be the active device. The active device receives and routes packets destined for the MAC address of the group. For n devices running HSRP, n + 1 IP and MAC addresses are assigned.
HSRP detects when the designated active device fails, at which point a selected standby device assumes control of the MAC and IP addresses of the Hot Standby group. A new standby device is also selected at that time.
HSRP uses a priority mechanism to determine which HSRP configured device is to be the default active device. To configure a device as the active device, you assign it a priority that is higher than the priority of all the other HSRP-configured devices. The default priority is 100, so if you configure just one device to have a higher priority, that device will be the default active device.
Devices that are running HSRP send and receive multicast UDP-based hello messages to detect device failure and to designate active and standby devices. When the active device fails to send a hello message within a configurable period of time, the standby device with the highest priority becomes the active device. The transition of packet forwarding functions between devices is completely transparent to all hosts on the network.
You can configure multiple Hot Standby groups on an interface, thereby making fuller use of redundant devices and load sharing.
The figure below shows a network configured for HSRP. By sharing a virtual MAC address and IP address, two or more devices can act as a single virtual router. The virtual device does not physically exist but represents the common default gateway for devices that are configured to provide backup to each other. You do not need to configure the hosts on the LAN with the IP address of the active device. Instead, you configure them with the IP address (virtual IP address) of the virtual device as their default gateway. If the active device fails to send a hello message within the configurable period of time, the standby device takes over and responds to the virtual addresses and becomes the active device, assuming the active device duties.
HSRP version 2 is designed to address the following restrictions in HSRP version 1:
In HSRP version 1, millisecond timer values are not advertised or learned. HSRP version 2 advertises and learns millisecond timer values. This change ensures stability of the HSRP groups in all cases.
In HSRP version 1, group numbers are restricted to the range from 0 to 255. HSRP version 2 expands the group number range from 0 to 4095.
HSRP version 2 provides improved management and troubleshooting. With HSRP version 1, you cannot use HSRP active hello messages to identify which physical device sent the message because the source MAC address is the HSRP virtual MAC address. The HSRP version 2 packet format includes a 6-byte identifier field that is used to uniquely identify the sender of the message. Typically, this field is populated with the interface MAC address.
The multicast address 224.0.0.2 is used to send HSRP hello messages. This address can conflict with Cisco Group Management Protocol (CGMP) leave processing.
Version 1 is the default version of HSRP.
HSRP version 2 uses the new IP multicast address 224.0.0.102 to send hello packets instead of the multicast address of 224.0.0.2, used by HSRP version 1. This new multicast address allows CGMP leave processing to be enabled at the same time as HSRP.
HSRP version 2 permits an expanded group number range, 0 to 4095, and consequently uses a new MAC address range 0000.0C9F.F000 to 0000.0C9F.FFFF. The increased group number range does not imply that an interface can, or should, support that many HSRP groups. The expanded group number range was changed to allow the group number to match the VLAN number on subinterfaces.
When the HSRP version is changed, each group will reinitialize because it now has a new virtual MAC address.
HSRP version 2 has a different packet format than HSRP version 1. The packet format uses a type-length-value (TLV) format. HSRP version 2 packets received by an HSRP version 1 device will have the type field mapped to the version field by HSRP version 1 and subsequently ignored.
The Gateway Load Balancing Protocol (GLBP) also addresses the same restrictions relative to HSRP version 1 that HSRP version 2 does. See the Configuring GLBP document for more information on GLBP.
Jitter timers are used in HSRP. They are recommended for timers running on services that work realtime and scale. Jitter timers are intended to significantly improve the reliability of HSRP, and other FHRP protocols, by reducing the chance of bunching of HSRP groups operations, and thus help reduce CPU and network traffic spikes. In the case of HSRP, a given device may have up to 4000 operational groups configured. In order to distribute the load on the device and network, the HSRP timers use a jitter. A given timer instance may take up to 20% more than the configured value. For example, for a hold time set to 15 seconds, the actual hold time may take 18 seconds.
In HSRP, the Hello timer (which sends the Hello Packet) has a negative Jitter, while the Holddown timer (which checks for failure of a peer) has a positive jitter.
With CSCsv12265, an HSRP group may be configured with a virtual IP address that matches the subnet of an IP address of a secondary interface.
When the virtual IP address of an HSRP group is configured with the same network ID as a secondary interface IP address, the source address of HSRP messages is automatically set to the most appropriate interface address. This configuration change allows the following configuration:
interface Ethernet1/0
ip address 192.168.1.1 255.255.255.0
ip address 192.168.2.1 255.255.255.0 secondary
standby 1 ip 192.168.1.254
standby 1 priority 105
standby 1 preempt
standby 2 ip 192.168.2.254 !Same network ID as secondary interface Prior to CSCsv12265, an HSRP group remained in INIT state unless the HSRP virtual IP address had the same network ID as the primary interface address.
In addition, the following warning message is displayed if an HSRP group address is configured when no interface addresses are configured:
% Warning: address is not within a subnet on this interfaceHSRP employs a redundancy scheme that is time proven and deployed extensively in large networks.
HSRP provides transparent fast failover of the first-hop device.
Preemption allows a standby device to delay becoming active for a configurable amount of time.
HSRP message digest 5 (MD5) algorithm authentication protects against HSRP-spoofing software and uses the industry-standard MD5 algorithm for improved reliability and security.
You can use the CLI to apply group attributes to:
A single HSRP group—performed in interface configuration mode and applies to a group.
All groups on the interface—performed in interface configuration mode and applies to all groups on the interface.
All groups on all interfaces—performed in global configuration mode and applies to all groups on all interfaces.
When a newly reloaded device becomes HSRP active, and there is already an HSRP active device on the network, HSRP preemption may appear to not function. HSRP preemption may appear not function correctly because the new HSRP active device did not receive any hello packets from the current HSRP active device, and the preemption configuration never factored into the new device's decision making.
HSRP may appear to not function on some larger hardware platforms where there can be a delay in an interface receiving packets.
In general, we recommend that all HSRP devices have the following configuration:
standby delay minimum 30 reload 60
The standby delay minimum reload interface configuration command delays HSRP groups from initializing for the specified time after the interface comes up.
This is a different command than the standby preempt delay interface configuration command, which enables HSRP preemption delay.
Preemption enables the HSRP router with the highest priority to immediately become the active router. Priority is determined first by the configured priority value, and then by the IP address. In case of ties, the primary IP addresses are compared, and the higher IP address has priority. This scenario only occurs during the initial election phase when no Active router is currently present. Once an Active router has been elected, a router with a higher IP address will not cause a preemption, in order to avoid unnecessary disruptions. The only way to preempt the current Active router is by increasing its priority.
In each case, a higher value is of greater priority. If you do not use the standby preempt interface configuration command in the configuration for a router, that router will not become the active router, even if its priority is higher than all other routers.
A standby router with equal priority but a higher IP address will not preempt the active router.
When a router first comes up, it does not have a complete routing table. You can set a preemption delay that allows preemption to be delayed for a configurable time period. This delay period allows the router to populate its routing table before becoming the active router.
If preemption is not enabled, then a router may appear to preempt the active router if it does not receive any Hello messages from the active router.
The priority of a device can change dynamically if it has been configured for object tracking and the object that is being tracked goes down. The tracking process periodically polls the tracked objects and notes any change of value. The changes in the tracked object are communicated to HSRP, either immediately or after a specified delay. The object values are reported as either up or down. Examples of objects that can be tracked are the line protocol state of an interface or the reachability of an IP route. If the specified object goes down, the HSRP priority is reduced. The HSRP device with the higher priority can become the active device if it has the standby preempt command configured.
HSRP devices communicate between each other by exchanging HSRP hello packets. These packets are sent to the destination IP multicast address 224.0.0.2 (reserved multicast address used to communicate to all devices) on UDP port 1985. The active device sources hello packets from its configured IP address and the HSRP virtual MAC address while the standby device sources hellos from its configured IP address and the interface MAC address, which may or may not be the burned-in MAC address (BIA).
Because hosts are configured with their default gateway as the HSRP virtual IP address, hosts must communicate with the MAC address associated with the HSRP virtual IP address. This MAC address will be a virtual MAC address in the format of 0000.0C07.ACxy, where xy is the HSRP group number in hexadecimal based on the respective interface. For example, HSRP group one will use the HSRP virtual MAC address of 0000.0C07.AC01. Hosts on the adjoining LAN segment use the normal Address Resolution Protocol (ARP) process to resolve the associated MAC addresses.
HSRP version 2 uses the new IP multicast address 224.0.0.102 to send hello packets instead of the multicast address of 224.0.0.2, which is used by version 1. This new multicast address allows Cisco Group Management Protocol (CGMP) leave processing to be enabled at the same time as HSRP.
HSRP version 2 permits an expanded group number range, 0 to 4095, and consequently uses a new MAC address range 0000.0C9F.F000 to 0000.0C9F.FFFF.
A device automatically generates a virtual MAC address for each HSRP device. However, some network implementations, such as Advanced Peer-to-Peer Networking (APPN), use the MAC address to identify the first hop for routing purposes. In this case, specify the virtual MAC address by using the standby mac-address command in the group; the virtual IP address is unimportant for these protocols.
The standby use-bia command was implemented to overcome the limitations of using a functional address for the HSRP MAC address on Token Ring interfaces. This command allows HSRP groups to use the burned-in MAC address of an interface instead of the HSRP virtual MAC address. When HSRP runs on a multiple-ring, source-routed bridging environment and the HSRP devices reside on different rings, configuring the standby use-bia command can prevent confusion about the routing information field (RFI).
The standby use-bia command is used for an interface and the standby mac-address command is used for an HSRP group.
For HSRP version 1, nonactive devices learn timer values from the active device, unless millisecond timer values are being used. If millisecond timer values are being used, all devices must be configured with the millisecond timer values. This rule applies if either the hello time or the hold time is specified in milliseconds. This configuration is necessary because the HSRP hello packets advertise the timer values in seconds. HSRP version 2 does not have this limitation; it advertises the timer values in milliseconds.
Jitter timers are used in HSRP. They are recommended for timers running on services that work realtime and scale. Jitter timers are intended to significantly improve the reliability of HSRP, and other FHRP protocols, by reducing the chance of bunching of HSRP groups operations, and thus help reduce CPU and network traffic spikes. In the case of HSRP, a given device may have up to 4000 operational groups configured. In order to distribute the load on the device and network, the HSRP timers use a jitter. A given timer instance may take up to 20% more than the configured value. For example, for a hold time set to 15 seconds, the actual hold time may take 18 seconds.
In HSRP, the Hello timer (which sends the Hello Packet) has a negative Jitter, while the Holddown timer (which checks for failure of a peer) has a positive jitter.
When HSRP runs over FDDI, you can change the interval at which a packet is sent to refresh the MAC cache on learning bridges and switches. HSRP hello packets on FDDI interfaces use the burned-in address (BIA) instead of the MAC virtual address. Refresh packets keep the MAC cache on switches and learning bridges current. Refresh packets are also used for HSRP groups configured as multigroup subordinates because these do not send regular Hello messages.
You can change the refresh interval on FDDI rings to a longer or shorter interval, thereby using bandwidth more efficiently. You can prevent the sending of any MAC refresh packets if you do not need them (if you have FDDI but do not have a learning bridge or switch).
HSRP ignores unauthenticated HSRP protocol messages. The default authentication type is text authentication.
HSRP authentication protects against false HSRP hello packets causing a denial-of-service attack. For example, Device A has a priority of 120 and is the active device. If a host sends spoof HSRP hello packets with a priority of 130, then Device A stops being the active device. If Device A has authentication configured such that the spoof HSRP hello packets are ignored, Device A will remain the active device
HSRP packets will be rejected in any of the following cases:
The authentication schemes differ on the device and in the incoming packets.
Text authentication strings differ on the device and in the incoming packet.
Before the introduction of HSRP MD5 authentication, HSRP authenticated protocol packets with a simple plain text string. HSRP MD5 authentication is an enhancement to generate an MD5 digest for the HSRP portion of the multicast HSRP protocol packet. This functionality provides added security and protects against the threat from HSRP-spoofing software.
MD5 authentication provides greater security than the alternative plain text authentication scheme. MD5 authentication allows each HSRP group member to use a secret key to generate a keyed MD5 hash that is part of the outgoing packet. A keyed hash of an incoming packet is generated and if the hash within the incoming packet does not match the generated hash, the packet is ignored.
The key for the MD5 hash can be either given directly in the configuration using a key string or supplied indirectly through a key chain.
HSRP has two authentication schemes:
Plain text authentication
MD5 authentication
HSRP authentication protects against false HSRP hello packets causing a denial-of-service attack. For example, Device A has a priority of 120 and is the active device. If a host sends spoof HSRP hello packets with a priority of 130, then Device A stops being the active device. If Device A has authentication configured such that the spoof HSRP hello packets are ignored, Device A will remain the active device.
HSRP packets will be rejected in any of the following cases:
The authentication schemes differ on the device and in the incoming packets.
MD5 digests differ on the device and in the incoming packet.
Text authentication strings differ on the device and in the incoming packet.
Most IPv4 hosts have a single router’s IP address configured as the default gateway. When HSRP is used, then the HSRP virtual IP address is configured as the host’s default gateway instead of the router’s IP address. Simple load sharing may be achieved by using two HSRP groups and configuring half the hosts with one virtual IP address and half the hosts with the other virtual IP address.
In contrast, IPv6 hosts learn of available IPv6 routers through IPv6 neighbor discovery Router Advertisement (RA) messages. These are multicast periodically, or may be solicited by hosts. HSRP is designed to provide only a virtual first hop for IPv6 hosts.
An HSRP IPv6 group has a virtual MAC address that is derived from the HSRP group number, and a virtual IPv6 link-local address that is, by default, derived from the HSRP virtual MAC address. HSRP IPv6 uses the MAC address range 0005.73A0.0000 to 0005.73A0.0FFF. Periodic RAs are sent for the HSRP virtual IPv6 link-local address when the HSRP group is active. These RAs stop after a final RA is sent when the group leaves the active state.
Periodic RAs for the interface link-local address stop after a final RA is sent while at least one virtual IPv6 link-local address is configured on the interface. No restrictions occur for the interface IPv6 link-local address other than that mentioned for the RAs. Other protocols continue to receive and send packets to this address.
HSRP uses a priority mechanism to determine which HSRP configured router is to be the default active router. To configure a router as the active router, you assign it a priority that is higher than the priority of all the other HSRP-configured routers. The default priority is 100, so if you configure just one router to have a higher priority, that router will be the default active router.
For more information see the "Configuring First Hop Redundancy Protocols in IPv6" chapter of the Cisco IOS IPv6 Configuration Guide.
Devices configured with HSRP exchange three types of multicast messages:
Coup—When a standby device wants to assume the function of the active device, it sends a coup message.
Hello—The hello message conveys to other HSRP device the HSRP priority and state information of the device.
Resign—A device that is the active device sends this message when it is about to shut down or when a device that has a higher priority sends a hello or coup message.
At any time, a device configured with HSRP is in one of the following states:
Active—The device is performing packet-transfer functions.
Init or Disabled—The device is not yet ready or able to participate in HSRP, possibly because the associated interface is not up. HSRP groups configured on other devices on the network that are learned via snooping are displayed as being in the Init state. Locally configured groups with an interface that is down or groups without a specified interface IP address appear in the Init state.
Learn—The device has not determined the virtual IP address and has not yet seen an authenticated hello message from the active device. In this state, the device still waits to hear from the active device.
Listen—The device is receiving hello messages.
Speak—The device is sending and receiving hello messages.
Standby—The device is prepared to assume packet-transfer functions if the active device fails.
HSRP uses logging Level 5 for syslog messages related to HSRP state changes to allow logging of an event without filling up the syslog buffer on the device with low-priority Level 6 messaging.
HSRP provides stateless redundancy for IP routing. HSRP by itself is limited to maintaining its own state. Linking an IP redundancy client to an HSRP group provides a mechanism that allows HSRP to provide a service to client applications so they can implement stateful failover.
IP redundancy clients are other Cisco IOS processes or applications that use HSRP to provide or withhold a service or resource dependent upon the state of the group.
HSRP groups have a default name of hsrp-interface-group so specifying a group name is optional. For example, Group 1 on Ethernet0/0 has a default group name of "hsrp-Et0/0-1."
Object tracking separates the tracking mechanism from HSRP and creates a separate standalone tracking process that can be used by any other process as well as HSRP. The priority of a device can change dynamically when it has been configured for object tracking and the object that is being tracked goes down. Examples of objects that can be tracked are the line protocol state of an interface or the reachability of an IP route. If the specified object goes down, the HSRP priority is reduced.
A client process such as HSRP, Virtual Router Redundancy Protocol (VRRP), or Gateway Load Balancing Protocol (GLBP) can register its interest in tracking objects and then be notified when the tracked object changes state.
For more information about object tracking, see the "Configuring Enhanced Object Tracking" document.
The FHRP—HSRP Group Shutdown feature enables you to configure an HSRP group to become disabled (its state changed to Init) instead of having its priority decremented when a tracked object goes down. Use the standby track command with the shutdown keyword to configure HSRP group shutdown.
If an object is already being tracked by an HSRP group, you cannot change the configuration to use the HSRP Group Shutdown feature. You must first remove the tracking configuration using the no standby track command and then reconfigure it using the standby track command with the shutdown keyword.
By default, HSRP filtering of Internet Control Message Protocol (ICMP) redirect messages is enabled on devices running HSRP.
ICMP is a network layer Internet protocol that provides message packets to report errors and other information relevant to IP processing. ICMP can send error packets to a host and can send redirect packets to a host.
When HSRP is running, preventing hosts from discovering the interface (or real) IP addresses of devices in the HSRP group is important. If a host is redirected by ICMP to the real IP address of a device, and that device later fails, then packets from the host will be lost.
ICMP redirect messages are automatically enabled on interfaces configured with HSRP. This functionality works by filtering outgoing ICMP redirect messages through HSRP, where the next hop IP address may be changed to an HSRP virtual IP address.
The next-hop IP address is compared to the list of active HSRP devices on that network; if a match is found, then the real next-hop IP address is replaced with a corresponding virtual IP address and the redirect message is allowed to continue.
If no match is found, then the ICMP redirect message is sent only if the device corresponding to the new next hop IP address is not running HSRP. Redirects to passive HSRP devices are not allowed (a passive HSRP device is a device running HSRP, but which contains no active HSRP groups on the interface).
For optimal operation, every device in a network that is running HSRP should contain at least one active HSRP group on an interface to that network. Every HSRP device need not be a member of the same group. Each HSRP device will snoop on all HSRP packets on the network to maintain a list of active devices (virtual IP addresses versus real IP addresses).
Consider the network shown in the figure below, which supports the HSRP ICMP redirection filter.
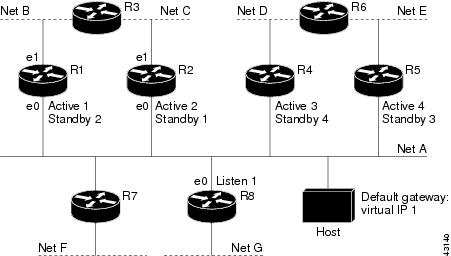
If the host wants to send a packet to another host on Net D, then it first sends it to its default gateway, the virtual IP address of HSRP group 1.
The following is the packet received from the host:
dest MAC = HSRP group 1 virtual MAC
source MAC = Host MAC
dest IP = host-on-netD IP
source IP = Host IP
Device R1 receives this packet and determines that device R4 can provide a better path to Net D, so it prepares to send a redirect message that will redirect the host to the real IP address of device R4 (because only real IP addresses are in its routing table).
The following is the initial ICMP redirect message sent by device R1:
dest MAC = Host MAC
source MAC = router R1 MAC
dest IP = Host IP
source IP = router R1 IP
gateway to use = router R4 IP
Before this redirect occurs, the HSRP process of device R1 determines that device R4 is the active HSRP device for group 3, so it changes the next hop in the redirect message from the real IP address of device R4 to the virtual IP address of group 3. Furthermore, it determines from the destination MAC address of the packet that triggered the redirect message that the host used the virtual IP address of group 1 as its gateway, so it changes the source IP address of the redirect message to the virtual IP address of group 1.
The modified ICMP redirect message showing the two modified fields (*) is as follows:
dest MAC = Host MAC
source MAC = router R1 MAC
dest IP = Host IP
source IP* = HSRP group 1 virtual IP
gateway to use* = HSRP group 3 virtual IP
This second modification is necessary because hosts compare the source IP address of the ICMP redirect message with their default gateway. If these addresses do not match, the ICMP redirect message is ignored. The routing table of the host now consists of the default gateway, virtual IP address of group 1, and a route to Net D through the virtual IP address of group 3.
ICMP redirects to passive HSRP devices are not permitted. Redundancy may be lost if hosts learn the real IP addresses of HSRP devices.
In the "Network Supporting the HSRP ICMP Redirection Filter" figure, redirection to device R8 is not allowed because R8 is a passive HSRP device. In this case, packets from the host to Net D will first go to device R1 and then be forwarded to device R4; that is, they will traverse the network twice.
A network configuration with passive HSRP devices is considered a misconfiguration. For HSRP ICMP redirection to operate optimally, every device on the network that is running HSRP should contain at least one active HSRP group.
ICMP redirects to devices not running HSRP on their local interface are permitted. No redundancy is lost if hosts learn the real IP address of non-HSRP devices.
In the "Network Supporting the HSRP ICMP Redirection Filter" figure, redirection to device R7 is allowed because R7 is not running HSRP. In this case, the next hop IP address is unchanged. The source IP address is changed dependent upon the destination MAC address of the original packet. You can specify the no standby redirect unknown command to stop these redirects from being sent.
Passive HSRP devices send out HSRP advertisement messages both periodically and when entering or leaving the passive state. Thus, all HSRP devices can determine the HSRP group state of any HSRP device on the network. These advertisements inform other HSRP devices on the network of the HSRP interface state, as follows:
Active—Interface has at least one active group. A single advertisement is sent out when the first group becomes active.
Dormant—Interface has no HSRP groups. A single advertisement is sent once when the last group is removed.
Passive—Interface has at least one nonactive group and no active groups. Advertisements are sent out periodically.
You can adjust the advertisement interval and hold-down time using the standby redirect timers command.
If the HSRP device cannot uniquely determine the IP address used by the host when it sends the packet that caused the redirect, the redirect message will not be sent. The device uses the destination MAC address in the original packet to make this determination. In certain configurations, such as the use of the standby use-bia interface configuration command specified on an interface, redirects cannot be sent. In this case, the HSRP groups use the interface MAC address as their virtual MAC address. The device now cannot determine if the default gateway of the host is the real IP address or one of the HSRP virtual IP addresses that are active on the interface.
The IP source address of an ICMP packet must match the gateway address used by the host in the packet that triggered the ICMP packet, otherwise the host will reject the ICMP redirect packet. An HSRP device uses the destination MAC address to determine the gateway IP address of the host. If the HSRP device is using the same MAC address for multiple IP addresses, uniquely determining the gateway IP address of the host is not possible, and the redirect message is not sent.
The following is sample output from the debug standby events icmp EXEC command if HSRP could not uniquely determine the gateway used by the host:
10:43:08: HSRP: ICMP redirect not sent to 10.0.0.4 for dest 10.0.1.2
10:43:08: HSRP: could not uniquely determine IP address for mac 00d0.bbd3.bc22HSRP support for a Multiprotocol Label Switching (MPLS) VPN interface is useful when an Ethernet LAN is connected between two provider edge (PE) devices with either of the following conditions:
A customer edge (CE) device with a default route to the HSRP virtual IP address
One or more hosts with the HSRP virtual IP address configured as the default gateway
Each VPN is associated with one or more VPN routing and forwarding (VRF) instances. A VRF consists of the following elements:
IP routing table
Cisco Express Forwarding table
Set of interfaces that use the Cisco Express Forwarding forwarding table
Set of rules and routing protocol parameters to control the information in the routing tables
VPN routing information is stored in the IP routing table and the Cisco Express Forwarding table for each VRF. A separate set of routing and Cisco Express Forwarding tables is maintained for each VRF. These tables prevent information from being forwarded outside a VPN and also prevent packets that are outside a VPN from being forwarded to a device within the VPN.
HSRP adds ARP entries and IP hash table entries (aliases) using the default routing table instance. However, a different routing table instance is used when VRF forwarding is configured on an interface, causing ARP and ICMP echo requests for the HSRP virtual IP address to fail.
HSRP support for MPLS VPNs ensures that the HSRP virtual IP address is added to the correct IP routing table and not to the default routing table.
The configuration of many hundreds of subinterfaces on the same physical interface, with each subinterface having its own HSRP group, can cause the processes of negotiation and maintenance of multiple HSRP groups to have a detrimental impact on network traffic and CPU utilization.
Only one HSRP group is required on a physical interface for the purposes of electing active and standby devices. This group is known as the primary group. Other HSRP groups may be created on each subinterface and linked to the primary group via the group name. These linked HSRP groups are known as client or subordinate groups.
In a scenario where a following group is in the backup state and its peer is in the master state, the following group stays in the backup state even if the peer’s subinterface goes down. MGO client groups do not participate in the HSRP election process. Instead, they inherit the state of their master group. These client groups do not maintain peer state awareness and do not exchange protocol election packets.
The only traffic sent by MGO client groups includes periodic MAC refresh packets. These packets maintain the Virtual MAC address entries on connected switches. These MAC refresh packets are sent based on a configurable MAC refresh timer. They do not participate in the election process.
The In Service Software Upgrade (ISSU) process allows Cisco software to be updated or otherwise modified while packet forwarding continues. In most networks, planned software upgrades are a significant cause of downtime. ISSU allows Cisco software to be modified while packet forwarding continues, which increases network availability and reduces downtime caused by planned software upgrades.
For detailed information about ISSU, see the Cisco IOS In Service Software Upgrade Process document in the High Availability Configuration Guide.
SSO HSRP alters the behavior of HSRP when a device with redundant Route Processors (RPs) is configured for stateful switchover (SSO) redundancy mode. When an RP is active and the other RP is standby, SSO enables the standby RP to take over if the active RP fails.
With this functionality, HSRP SSO information is synchronized to the standby RP, allowing traffic that is sent using the HSRP virtual IP address to be continuously forwarded during a switchover without a loss of data or a path change. Additionally, if both RPs fail on the active HSRP device, then the standby HSRP device takes over as the active HSRP device.
The feature is enabled by default when the redundancy mode of operation is set to SSO.
SSO functions in networking devices (usually edge devices) that support dual RPs. SSO provides RP redundancy by establishing one of the RPs as the active processor and the other RP as the standby processor. SSO also synchronizes critical state information between the RPs so that network state information is dynamically maintained between RPs.
SSO is generally used with Cisco nonstop forwarding (NSF). Cisco NSF enables forwarding of data packets to continue along known routes while the routing protocol information is being restored following a switchover. With NSF, users are less likely to experience service outages.
The SSO HSRP feature enables the Cisco IOS HSRP subsystem software to detect that a standby RP is installed and the system is configured in SSO redundancy mode. Further, if the active RP fails, no change occurs to the HSRP group itself and traffic continues to be forwarded through the current active gateway device.
Prior to introduction of the SSO HSRP feature, when the primary RP of the active device failed, it would stop participating in the HSRP group and trigger another switch in the group to take over as the active HSRP switch.
SSO HSRP is required to preserve the forwarding path for traffic destined to the HSRP virtual IP address through an RP switchover.
Configuring SSO on the edge device enables the traffic on the Ethernet links to continue during an RP failover without the Ethernet traffic switching over to an HSRP standby device (and then back, if preemption is enabled).
 Note |
You may want to disable SSO HSRP by using the no standby sso command if you have LAN segments that should switch HSRP traffic to a redundant device while SSO maintains traffic flow for other connections. |
The HSRP BFD Peering feature introduces Bidirectional Forwarding Detection (BFD) in the Hot Standby Router Protocol (HSRP) group member health monitoring system. HSRP supports BFD as a part of the HSRP group member health monitoring system. Without BFD, HSRP runs as a process in a multiprocess system and cannot be guaranteed to be scheduled in time to service large numbers of groups with hello and hold timers, in milliseconds. BFD runs as a pseudopreemptive process and can therefore be guaranteed to run when required. Only one BFD session between two devices can provide early failover notification for multiple HSRP groups.
This feature is enabled by default. The HSRP standby device learns the real IP address of the HSRP active device from the HSRP hello messages. The standby device registers as a BFD client and asks to be notified if the active device becomes unavailable. When BFD determines that the connections between standby and active devices has failed, it will notify HSRP on the standby device which will immediately take over as the active device.
BFD provides a low-overhead, short-duration method of detecting failures in the forwarding path between two adjacent devices, including the interfaces, data links, and forwarding planes. BFD is a detection protocol that you enable at the interface and routing protocol levels. Cisco supports the BFD asynchronous mode, which depends on the sending of BFD control packets between two systems to activate and maintain BFD neighbor sessions between devices. Therefore, to create a BFD session, you must configure BFD on both systems (or BFD peers). When BFD is enabled on the interfaces and at the device level for HSRP, a BFD session is created, BFD timers are negotiated, and the BFD peers will begin to send BFD control packets to each other at the negotiated interval.
BFD provides fast BFD peer failure detection times independently of all media types, encapsulations, topologies, and routing protocols such as, Border Gateway Protocol (BGP), Enhanced Interior Gateway Routing Protocol (EIGRP), Hot Standby Router Protocol (HSRP), Intermediate System To Intermediate System (IS-IS), and Open Shortest Path First (OSPF). By sending rapid failure detection notices to the routing protocols in the local device to initiate the routing table recalculation process, BFD contributes to greatly reduce overall network convergence time. The figure below shows a simple network with two devices running HSRP and BFD.

For more information about BFD, see the IP Routing: BFD Configuration Guide.
HSRP MIB supports Simple Network Management Protocol (SNMP) Get operations, to allow network devices to get reports about HSRP groups in a network from the network management station.
Enabling HSRP MIB trap support is performed through the CLI, and the MIB is used for getting the reports. A trap notifies the network management station when a device leaves or enters the active or standby state. When an entry is configured from the CLI, the RowStatus for that group in the MIB immediately goes to the active state.
Cisco software supports a read-only version of the MIB, and set operations are not supported.
This functionality supports four MIB tables, as follows:
cHsrpGrpEntry table defined in CISCO-HSRP-MIB.my
cHsrpExtIfTrackedEntry, defined in CISCO-HSRP-EXT-MIB.my
cHsrpExtSecAddrEntry, defined in CISCO-HSRP-EXT-MIB.my
cHsrpExtIfEntry defined in CISCO-HSRP-EXT-MIB.my
The cHsrpGrpEntry table consists of all the group information defined in RFC 2281, Cisco Hot Standby Router Protocol; the other tables consist of the Cisco extensions to RFC 2281, which are defined in CISCO-HSRP-EXT-MIB.my.
Perform this task to enable HSRP.
The standby ip interface configuration command activates HSRP on the configured interface. If an IP address is specified, that address is used as the virtual IP address for the Hot Standby group. For HSRP to elect a designated device, you must configure the virtual IP address for at least one of the devices in the group; it can be learned on the other devices in the group.
You can configure many attributes in HSRP such as authentication, timers, priority, and preemption. You should configure the attributes before enabling the HSRP group. This practice avoids authentication error messages and unexpected state changes in other routers that can occur if the group is enabled first and then there is a long enough delay (one or two hold times) before the other attribues are configured.
We recommend that you always specify an HSRP IP address.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask Example: |
Configures an IP address for an interface. |
|
Step 5 |
standby [group-number] ip [ip-address [secondary]] Example: |
|
|
Step 6 |
end Example: |
Returns to privileged EXEC mode. |
|
Step 7 |
show standby [all] [brief] Example: |
(Optional) Displays HSRP information.
|
|
Step 8 |
show standby type number [group-number | all] [brief] Example: |
(Optional) Displays HSRP information about specific groups or interfaces. |
The standby delay command is used to delay HSRP initialization either after a reload and/or after an interface comes up. This configuration allows the interface and device time to settle down after the interface up event and helps prevent HSRP state flapping.
We recommend that you use the standby minimum reload command if the standby timers command is configured in milliseconds or if HSRP is configured on a VLAN interface.
| Command or Action | Purpose | |||
|---|---|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
||
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
||
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
||
|
Step 4 |
ip address ip-address mask Example: |
Specifies an IP address for an interface. |
||
|
Step 5 |
standby delay minimum min-seconds reload reload-seconds Example: |
(Optional) Configures the delay period before the initialization of HSRP groups.
|
||
|
Step 6 |
standby [group-number ] ip [ip-address [secondary]] Example: |
Activates HSRP. |
||
|
Step 7 |
end Example: |
Returns to privileged EXEC mode. |
||
|
Step 8 |
show standby delay [typenumber] Example: |
(Optional) Displays HSRP information about delay periods. |
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask Example: |
Specifies an IP address for an interface. |
|
Step 5 |
standby [group-number] priority priority Example: |
Configures HSRP priority.
|
|
Step 6 |
standby [group-number] preempt [delay {minimum | reload | sync} seconds] Example: |
Configures HSRP preemption and preemption delay.
|
|
Step 7 |
standby [group-number] ip ip-address [secondary]] Example: |
Activates HSRP. |
|
Step 8 |
end Example: |
Returns to privileged EXEC mode. |
|
Step 9 |
show standby [all] [brief] Example: |
(Optional) Displays HSRP information.
|
|
Step 10 |
show standby type number [group-number | all] [brief] Example: |
(Optional) Displays HSRP information about specific groups or interfaces. |
Perform this task to configure HSRP to track an object and change the HSRP priority based on the state of the object.
Each tracked object is identified by a unique number that is specified on the tracking CLI. Client processes use this number to track a specific object.
| Command or Action | Purpose | |||
|---|---|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
||
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
||
|
Step 3 |
track object-number interface type number {line-protocol | ip routing} Example: |
Configures an interface to be tracked and enters tracking configuration mode. |
||
|
Step 4 |
exit Example: |
Returns to global configuration mode. |
||
|
Step 5 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
||
|
Step 6 |
standby [group-number] track object-number [decrement priority-decrement] [shutdown] Example: |
Configures HSRP to track an object and change the Hot Standby priority on the basis of the state of the object.
|
||
|
Step 7 |
standby [group-number] ip [ip-address [secondary]] Example: |
|
||
|
Step 8 |
end Example: |
Returns to privileged EXEC mode. |
||
|
Step 9 |
show track [object-number | brief] [interface [brief] | ip route [brief] | resolution | timers] Example: |
Displays tracking information. |
 Note |
Text authentication cannot be combined with MD5 authentication for an HSRP group at any one time. When MD5 authentication is configured, the text authentication field in HSRP hello messages is set to all zeroes on transmit and ignored on receipt, provided the receiving device also has MD5 authentication enabled. |
 Note |
If you are changing a key string in a group of devices, change the active device last to prevent any HSRP state change. The active device should have its key string changed no later than one hold-time period, specified by the standy timers interface configuration command, after the nonactive devices. This procedure ensures that the nonactive devices do not time out the active device. |
| Command or Action | Purpose | |||
|---|---|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
||
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
||
|
Step 3 |
terminal interface type number Example: |
Configures an interface type and enters interface configuration mode. |
||
|
Step 4 |
ip address ip-address mask [secondary] Example: |
Specifies a primary or secondary IP address for an interface. |
||
|
Step 5 |
standby [group-number] priority priority Example: |
Configures HSRP priority. |
||
|
Step 6 |
standby [group-number] preempt [delay {minimum | reload | sync} seconds] Example: |
Configures HSRP preemption. |
||
|
Step 7 |
standby [group-number] authentication md5 key-string [0 | 7] key [timeout seconds] Example: |
Configures an authentication string for HSRP MD5 authentication.
|
||
|
Step 8 |
standby [group-number] ip [ip-address] [secondary]] Example: |
Activates HSRP. |
||
|
Step 9 |
Repeat Steps 1 through 8 on each device that will communicate. |
— |
||
|
Step 10 |
end Example: |
Returns to privileged EXEC mode. |
||
|
Step 11 |
show standby Example: |
(Optional) Displays HSRP information.
|
Perform this task to configure HSRP MD5 authentication using a key chain. Key chains allow a different key string to be used at different times according to the key chain configuration. HSRP will query the appropriate key chain to obtain the current live key and key ID for the specified key chain.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
key chain name-of-chain Example: |
Enables authentication for routing protocols, identifies a group of authentication keys, and enters key-chain configuration mode. |
|
Step 4 |
key key-id Example: |
Identifies an authentication key on a key chain and enters key-chain key configuration mode.
|
|
Step 5 |
key-string string Example: |
Specifies the authentication string for a key.
|
|
Step 6 |
exit Example: |
Returns to key-chain configuration mode. |
|
Step 7 |
exit Example: |
Returns to global configuration mode. |
|
Step 8 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 9 |
ip address ip-address mask [secondary] Example: |
Specifies a primary or secondary IP address for an interface. |
|
Step 10 |
standby [group-number] priority priority Example: |
Configures HSRP priority. |
|
Step 11 |
standby [group-number] preempt [delay {minimum | reload | sync} seconds] Example: |
Configures HSRP preemption. |
|
Step 12 |
standby [group-number] authentication md5 key-chain key-chain-name Example: |
Configures an authentication MD5 key chain for HSRP MD5 authentication.
|
|
Step 13 |
standby [group-number] ip [ip-address [secondary]] Example: |
Activates HSRP. |
|
Step 14 |
Repeat Steps 1 through 12 on each device that will communicate. |
— |
|
Step 15 |
end Example: |
Returns to privileged EXEC mode. |
|
Step 16 |
show standby Example: |
(Optional) Displays HSRP information.
|
Perform this task if HSRP MD5 authentication is not operating correctly.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
debug standby errors Example: |
Displays error messages related to HSRP.
|
In the following example, Device A has MD5 text string authentication configured, but Device B has the default text authentication:
Device# debug standby errors
A:Jun 16 12:14:50.337:HSRP:Et0/1 Grp 0 Auth failed for Hello pkt from 10.21.0.5, MD5 confgd but no tlv
B:Jun 16 12:16:34.287:HSRP:Et0/1 Grp 0 Auth failed for Hello pkt from 10.21.0.4, Text auth failed
In the following example, both Device A and Device B have different MD5 authentication strings:
Device# debug standby errors
A:Jun 16 12:19:26.335:HSRP:Et0/1 Grp 0 Auth failed for Hello pkt from 10.21.0.5, MD5 auth failed
B:Jun 16 12:18:46.280:HSRP:Et0/1 Grp 0 Auth failed for Hello pkt from 10.21.0.4, MD5 auth failed| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask [secondary] Example: |
Specifies a primary or secondary IP address for an interface. |
|
Step 5 |
standby [group-number] priority priority Example: |
Configures HSRP priority. |
|
Step 6 |
standby [group-number] preempt [delay {minimum | reload | sync} seconds] Example: |
Configures HSRP preemption. |
|
Step 7 |
standby [group-number] authentication text string Example: |
Configures an authentication string for HSRP text authentication.
|
|
Step 8 |
standby [group-number] ip [ip-address [secondary]] Example: |
Activates HSRP. |
|
Step 9 |
Repeat Steps 1 through 8 on each device that will communicate. |
-- |
|
Step 10 |
end Example: |
Returns to privileged EXEC mode. |
|
Step 11 |
show standby Example: |
(Optional) Displays HSRP information.
|
 Note |
We recommend configuring a minimum hello-time value of 250 milliseconds and a minimum hold-time value of 800 milliseconds. |
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask [secondary]] Example: |
Specifies a primary or secondary IP address for an interface. |
|
Step 5 |
standby [group-number] timers [msec] hellotime [msec] holdtime Example: |
Configures the time between hello packets and the time before other devices declare the active Hot Standby or standby device to be down. |
|
Step 6 |
standby [group-number] ip [ip-address [secondary]] Example: |
Activates HSRP. |
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask [secondary] Example: |
Specifies a primary or secondary IP address for an interface. |
|
Step 5 |
standby mac-refresh seconds Example: |
Changes the interval at which packets are sent to refresh the MAC cache when HSRP is running over FDDI.
|
|
Step 6 |
standby [group-number] ip [ip-address [secondary]] Example: |
Activates HSRP. |
Perform this task to configure multiple HSRP groups for load balancing.
Multiple HSRP groups enable redundancy and load-sharing within networks and allow redundant devices to be more fully utilized. A device actively forwarding traffic for one HSRP group can be in standby or in the listen state for another group.
If two devices are used, then Device A would be configured as active for group 1 and standby for group 2. Device B would be standby for group 1 and active for group 2. Fifty percent of the hosts on the LAN would be configured with the virtual IP address of group 1 and the remaining hosts would be configured with the virtual IP address of group 2. See the Example: Multiple HSRP for Load Balancing section for a diagram and configuration example.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask [secondary] Example: |
Specifies a primary or secondary IP address for an interface. |
|
Step 5 |
standby [group-number] priority priority Example: |
Configures HSRP priority. |
|
Step 6 |
standby [group-number] preempt [delay {minimum | reload | sync} delay] Example: |
Configures HSRP preemption. |
|
Step 7 |
standby [group-number] ip [ip-address] secondary] Example: |
Activates HSRP. |
|
Step 8 |
On the same device, repeat Steps 5 through 7 to configure the device attributes for different standby groups. |
For example, Device A can be configured as an active device for group 1 and be configured as an active or standby device for another HSRP group with different priority and preemption values. |
|
Step 9 |
exit Example: |
Exits to global configuration mode. |
|
Step 10 |
Repeat Steps 3 through 9 on another device. |
Configures multiple HSRP and enables load balancing on another device. |
Perform this task to configure multiple HSRP client groups.
The standby follow command configures an HSRP group to become a subordinate of another HSRP group.
HSRP client groups follow the master HSRP with a slight, random delay so that all client groups do not change at the same time.
Use the standby mac-refresh seconds command to directly change the HSRP client group refresh interval. The default interval is 10 seconds and can be configured to as much as 255 seconds.
 Note |
|
Configure the HSRP master group using the steps in the Configuring Multiple HSRP Groups for Load Balancing section.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask [secondary] Example: |
Specifies a primary or secondary IP address for an interface. |
|
Step 5 |
standby mac-refresh seconds Example: |
Configures the HSRP client group refresh interval. |
|
Step 6 |
standby group-number follow group-name Example: |
Configures an HSRP group as a client group. |
|
Step 7 |
exit Example: |
Exits to global configuration mode. |
|
Step 8 |
Repeat Steps 3 through 6 to configure additional HSRP client groups. |
Configures multiple HSRP client groups. |
By default, HSRP filtering of ICMP redirect messages is enabled on devices running HSRP. Perform this task to reenable this feature on your device if it is disabled.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
standby redirect [timers advertisement holddown] [unknown] Example: |
Enables HSRP filtering of ICMP redirect messages.
|
|
Step 5 |
end Example: |
Returns to privileged EXEC mode. |
|
Step 6 |
show standby redirect [ip-address] [interface-type interface-number] [active] [passive] [timers] Example: |
(Optional) Displays ICMP redirect information on interfaces configured with HSRP. |
 Note |
You cannot use the standby use-bia and standby mac-address commands in the same configuration; they are mutually exclusive. The standby use-bia command has the following disadvantages:
|
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask [secondary] Example: |
Configures an IP address for an interface. |
|
Step 5 |
Enter one of the following commands:
Example:Example: |
Specifies a virtual MAC address for HSRP.
or Configures HSRP to use the burned-in address of the interface as its virtual MAC address.
|
|
Step 6 |
standby [group-number] ip [ip-address [secondary]] Example: |
Activates HSRP. |
Within the client application, you must first specify the same name as configured in the standby name command.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
|
Step 4 |
ip address ip-address mask Example: |
Specifies an IP address for an interface. |
|
Step 5 |
standby [group-number] name [redundancy-name] Example: |
Configures the name of the standby group.
|
|
Step 6 |
standby [group-number] ip [ip-address [secondary]] Example: |
Activates HSRP. |
HSRP version 2 was introduced to prepare for further enhancements and to expand the capabilities beyond what is possible with HSRP version 1. HSRP version 2 has a different packet format than HSRP version 1.
 Note |
|
| Command or Action | Purpose | |||
|---|---|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
||
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
||
|
Step 3 |
interface type number Example: |
Configures an interface type and enters interface configuration mode. |
||
|
Step 4 |
ip address ip-address mask Example: |
Sets an IP address for an interface. |
||
|
Step 5 |
standby version {1 | 2} Example: |
Changes the HSRP version.
|
||
|
Step 6 |
standby [group-number] ip [ip-address [secondary]] Example: |
Activates HSRP.
|
||
|
Step 7 |
end Example: |
Ends the current configuration session and returns to privileged EXEC mode. |
||
|
Step 8 |
show standby Example: |
(Optional) Displays HSRP information.
|
The SSO aware HSRP is enabled by default when the redundancy mode is set to SSO. Perform this task to reenable HSRP to be SSO aware if it has been disabled.
 Note |
You may want to disable SSO HSRP by using the no standby sso command if you have LAN segments that should switch HSRP traffic to a redundant device while SSO maintains traffic flow for other connections. |
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
redundancy Example: |
Enters redundancy configuration mode. |
|
Step 4 |
mode sso Example: |
Enables the redundancy mode of operation to SSO.
|
|
Step 5 |
exit Example: |
Exits redundancy configuration mode. |
|
Step 6 |
no standby sso Example: |
Disables HSRP SSO mode for all HSRP groups. |
|
Step 7 |
standby sso Example: |
Enables the SSO HSRP feature if you have disabled the functionality. |
|
Step 8 |
end Example: |
Ends the current configuration session and returns to privileged EXEC mode. |
To verify or debug HSRP SSO operation, perform the following steps from the active RP console.
|
Step 1 |
show standby Use the show standby command to display the state of the standby RP, for example: Example: |
|
Step 2 |
debug standby events ha Use thedebug standby events ha command to display the active and standby RPs, for example: Example: |
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
snmp-server enable traps hsrp Example: |
Enables the device to send SNMP traps and informs, and HSRP notifications. |
|
Step 4 |
snmp-server host host community-string hsrp Example: |
Specifies the recipient of an SNMP notification operation, and that HSRP notifications be sent to the host. |
Perform this task to configure Bidirectional Forwarding Detection (BFD) on an interface by setting the baseline BFD session parameters on the interface. Repeat the steps in this task for each interface on which you want to run BFD sessions to BFD neighbors.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
interface type number Example: |
Enters interface configuration mode. |
|
Step 4 |
bfd interval milliseconds min_rx milliseconds multiplier interval-multiplier Example: |
Enables BFD on the interface. |
|
Step 5 |
end Example: |
Exits interface configuration mode. |
Perform this task to enable Hot Standby Router Protocol (HSRP) Bidirectional Forwarding Detection (BFD) peering. Repeat the steps in this task for each interface over which you want to run BFD sessions to HSRP peers.
HSRP supports BFD peering by default. If HSRP BFD peering is disabled, you can reenable it at the device level to enable BFD support globally for all interfaces or you can reenable it on a per-interface basis at the interface level.
Before you proceed with this task:
HSRP must be running on all participating devices.
Cisco Express Forwarding must be enabled.
| Command or Action | Purpose | |
|---|---|---|
|
Step 1 |
enable Example: |
Enables privileged EXEC mode.
|
|
Step 2 |
configure terminal Example: |
Enters global configuration mode. |
|
Step 3 |
ip cef [distributed ] Example: |
Enables Cisco Express Forwarding or distributed Cisco Express Forwarding. |
|
Step 4 |
interface type number Example: |
Enters interface configuration mode. |
|
Step 5 |
ip address ip-address mask Example: |
Configures an IP address for the interface. |
|
Step 6 |
standby [group-number ] ip [ip-address [secondary ]] Example: |
Activates HSRP. |
|
Step 7 |
standby bfd Example: |
(Optional) Enables HSRP support for BFD on the interface. |
|
Step 8 |
exit Example: |
Exits interface configuration mode. |
|
Step 9 |
standby bfd all-interfaces Example: |
(Optional) Enables HSRP support for BFD on all interfaces. |
|
Step 10 |
exit Example: |
Exits global configuration mode. |
|
Step 11 |
show standby [neighbors ] Example: |
(Optional) Displays information about HSRP support for BFD. |
To verify Hot Standby Router Protocol (HSRP) Bidirectional Forwarding Detection (BFD) peering, use any of the following optional commands.
|
Step 1 |
show standby Use the show standby command to display HSRP information. Example: |
|
Step 2 |
show standby brief Use the show standby brief command to display HSRP standby device information in brief. Example: |
|
Step 3 |
show standby neighbors [type number ] Use the show standby neighbors command to display information about HSRP peer devices on an interface. Example: |
|
Step 4 |
show bfd neighbors Use the show bfd neighbors command to display a line-by-line listing of existing Bidirectional Forwarding Detection (BFD) adjacencies. Example: |
|
Step 5 |
show bfd neighbors details Use the details keyword to display BFD protocol parameters and timers for each neighbor. Example: |
In the following example, Device A is configured to be the active device for group 1 because it has the higher priority and standby device for group 2. Device B is configured to be the active device for group 2 and standby device for group 1.
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# ip address 10.1.0.21 255.255.0.0
Device(config-if)# standby 1 priority 110
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 ip 10.1.0.1
Device(config-if)# standby 2 priority 95
Device(config-if)# standby 2 preempt
Device(config-if)# standby 2 ip 10.1.0.2
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# ip address 10.1.0.22 255.255.0.0
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 priority 105
Device(config-if)# standby 1 ip 10.1.0.1
Device(config-if)# standby 2 priority 110
Device(config-if)# standby 2 preempt
Device(config-if)# standby 2 ip 10.1.0.2
In the following example, the tracking process is configured to track the IP-routing capability of serial interface 1/0. HSRP on Gigabit Ethernet interface 0/0/0 then registers with the tracking process to be informed of any changes to the IP-routing state of serial interface 1/0. If the IP state on serial interface 1/0 goes down, the priority of the HSRP group is reduced by 10.
If both serial interfaces are operational, Device A will be the HSRP active device because it has the higher priority. However, if IP routing on serial interface 1/0 in Device A fails, the HSRP group priority will be reduced and Device B will take over as the active device, thus maintaining a default virtual gateway service to hosts on the 10.1.0.0 subnet.
Device(config)# track 100 interface serial 1/0/0 ip routing
!
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# ip address 10.1.0.21 255.255.0.0
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 priority 110
Device(config-if)# standby 1 track 100 decrement 10
Device(config-if)# standby 1 ip 10.1.0.1
Device(config)# track 100 interface serial 1/0/0 ip routing
!
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# ip address 10.1.0.22 255.255.0.0
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 priority 105
Device(config-if)# standby 1 track 100 decrement 10
Device(config-if)# standby 1 ip 10.1.0.1
In the following example, the tracking process is configured to track the IP-routing capability of Gigabit Ethernet interface 0/0/0. HSRP on Gigabit Ethernet interface 0/0/1 then registers with the tracking process to be informed of any changes to the IP-routing state of Gigabit Ethernet interface 0/0/0. If the IP state on Gigabit Ethernet interface 0/0/0 goes down, the HSRP group is disabled.
If both Gigabit Ethernet interfaces are operational, Device A will be the HSRP active device because it has the higher priority. However, if IP routing on Gigabit Ethernet interface 0/0/0 in Device A fails, the HSRP group will be disabled and Device B will take over as the active device, thus maintaining a default virtual gateway service to hosts on the 10.1.0.0 subnet.
Device(config)# track 100 interface GigabitEthernet 0/0/0 ip routing
!
Device(config)# interface GigabitEthernet 0/0/1
Device(config-if)# ip address 10.1.0.21 255.255.0.0
Device(config-if)# standby 1 ip 10.1.0.1
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 priority 110
Device(config-if)# standby 1 track 100 shutdown
Device(config)# track 100 interface GigabitEthernet 0/0/0 ip routing
!
Device(config)# interface GigabitEthernet 0/0/1
Device(config-if)# ip address 10.1.0.22 255.255.0.0
Device(config-if)# standby 1 ip 10.1.0.1
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 priority 105
Device(config-if)# standby 1 track 100 shutdown
If an object is already being tracked by an HSRP group, you cannot change the configuration to use the HSRP Group Shutdown feature. You must first remove the tracking configuration using the no standby track command and then reconfigure it using the standby track command with the shutdown keyword.
The following example shows how to change the configuration of a tracked object to include the HSRP Group Shutdown feature:
Device(config)# no standby 1 track 100 decrement 10
Device(config)# standby 1 track 100 shutdown
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# standby 1 priority 110
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 authentication md5 key-string 0 54321098452103ab timeout 30
Device(config-if)# standby 1 ip 10.21.0.10
In the following example, HSRP queries the key chain “hsrp1” to obtain the current live key and key ID for the specified key chain:
Device(config)# key chain hsrp1
Device(config-keychain)# key 1
Device(config-keychain-key)# key-string 54321098452103ab
Device(config-keychain-key)# exit
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# standby 1 priority 110
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 authentication md5 key-chain hsrp1
Device(config-if)# standby 1 ip 10.21.0.10
The key ID for key-string authentication is always zero. If a key chain is configured with a key ID of zero, then the following configuration will work:
Device(config)# key chain hsrp1
Device(config-keychain)# key 0
Device(config-keychain-key)# key-string 54321098452103ab
Device(config-keychain-key)# exit
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# standby 1 authentication md5 key-chain hsrp1
Device(config-if)# standby 1 ip 10.21.0.10
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# standby 1 authentication md5 key-string 0 54321098452103ab
Device(config-if)# standby 1 ip 10.21.0.10
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# standby 1 priority 110
Device(config-if)# standby 1 preempt
Device(config-if)# standby 1 authentication text company2
Device(config-if)# standby 1 ip 10.21.0.10
You can use HSRP or multiple HSRP groups when you configure load sharing. In the figure below, half of the clients are configured for Router A, and half of the clients are configured for Router B. Together, the configuration for Routers A and B establish two Hot Standby groups. For group 1, Router A is the default active router because it has the assigned highest priority, and Router B is the standby router. For group 2, Router B is the default active router because it has the assigned highest priority, and Router A is the standby router. During normal operation, the two routers share the IP traffic load. When either router becomes unavailable, the other router becomes active and assumes the packet-transfer functions of the router that is unavailable. The standby preempt interface configuration command is necessary so that if a router goes down and then comes back up, preemption occurs and restores load sharing.
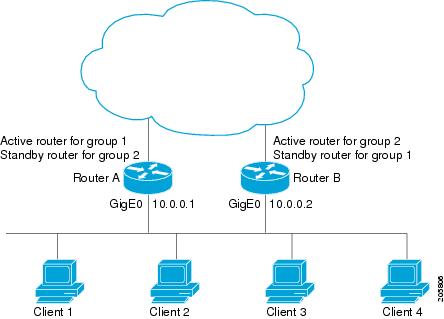
The following example shows Router A configured as the active router for group 1 with a priority of 110 and Router B configured as the active router for group 2 with a priority of 110. The default priority level is 100. Group 1 uses a virtual IP address of 10.0.0.3 and Group 2 uses a virtual IP address of 10.0.0.4.
Router(config)# hostname RouterA
!
Router(config)# interface GigabitEthernet 0/0/0
Router(config-if)# ip address 10.0.0.1 255.255.255.0
Router(config-if)# standby 1 priority 110
Router(config-if)# standby 1 preempt
Router(config-if)# standby 1 ip 10.0.0.3
Router(config-if)# standby 2 preempt
Router(config-if)# standby 2 ip 10.0.0.4
Router(config)# hostname RouterB
!
Router(config)# interface GigabitEthernet 0/0/0
Router(config-if)# ip address 10.0.0.2 255.255.255.0
Router(config-if)# standby 1 preempt
Router(config-if)# standby 1 ip 10.0.0.3
Router(config-if)# standby 2 priority 110
Router(config-if)# standby 2 preempt
Router(config-if)# standby 2 ip 10.0.0.4
The following example shows how to configure an HSRP client and primary group:
Device(config)# interface GigabitEthernet0/0/0
Device(config-if)# no shutdown
Device(config-if)# standby mac-refresh 30
! Client Hello message interval
!
Device(config)# interface GigabitEthernet0/0/0.10
Device(config-subif)# encapsulation dot1q 10
Device(config-subif)# ip address 10.10.10.2 255.255.255.0
Device(config-subif)# standby 1 ip 10.10.10.1
Device(config-subif)# standby 1 priority 110
Device(config-subif)# standby 1 preempt
Device(config-subif)# standby 1 name HSRP1
! Server group
!
Device(config)# interface GigabitEthernet0/0/0.20
Device(config-subif)# encapsulation dot1q 20
Device(config-subif)# ip address 10.10.20.2 255.255.255.0
Device(config-subif)# standby 2 ip 10.10.20.1
Device(config-subif)# standby 2 follow HSRP1
! Client group
!
Device(config)# interface GigabitEthernet0/0/0.30
Device(config-subif)# encapsulation dot1q 30
Device(config-subif)# ip address 10.10.30.2 255.255.255.0
Device(config-subif)# standby 3 ip 10.10.30.1
Device(config-subif)# standby 3 follow HSRP1
! Client groupThe following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.In an Advanced Peer-to-Peer Networking (APPN) network, an end node is typically configured with the MAC address of the adjacent network node. In the following example, if the end nodes are configured to use 4000.1000.1060, HSRP group 1 is configured to use the same MAC address:
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# ip address 10.0.0.1
Device(config-if)# standby 1 mac-address 4000.1000.1060
Device(config-if)# standby 1 ip 10.0.0.11
In the following example, the burned-in address of Token Ring interface 3/0 will be the virtual MAC address mapped to the virtual IP address:
Device(config)# interface token 3/0
Device(config-if)# standby use-bia
 Note |
You cannot use the standby use-bia command and the standby mac-address command in the same configuration. |
The following example shows HSRP support for a static Network Address Translation (NAT) configuration. The NAT client application is linked to HSRP via the correlation between the name specified by the standby name command. Two devices are acting as HSRP active and standby, and the NAT inside interfaces are HSRP enabled and configured to belong to the group named “group1.”
Device(config)# interface BVI 10
Device(config-if)# ip address 192.168.5.54 255.255.255.255.0
Device(config-if)# no ip redirects
Device(config-if)# ip nat inside
Device(config-if)# standby 10 ip 192.168.5.30
Device(config-if)# standby 10 priority 110
Device(config-if)# standby 10 preempt
Device(config-if)# standby 10 name group1
Device(config-if)# standby 10 track Ethernet 2/1
!
!
Device(config)# ip default-gateway 10.0.18.126
Device(config)# ip nat inside source static 192.168.5.33 10.10.10.5 redundancy group1
Device(config)# ip classless
Device(config)# ip route 10.10.10.0 255.255.255.0 Ethernet 2/1
Device(config)# ip route 172.22.33.0 255.255.255.0 Ethernet 2/1
Device(config)# no ip http server
Device(config)# interface BVI 10
Device(config-if)# ip address 192.168.5.56 255.255.255.255.0
Device(config-if)# no ip redirects
Device(config-if)# ip nat inside
Device(config-if)# standby 10 priority 95
Device(config-if)# standby 10 preempt
Device(config-if)# standby 10 name group1
Device(config-if)# standby 10 ip 192.168.5.30
Device(config-if)# standby 10 track Ethernet 3/1
Device(config-if)# exit
Device(config)# ip default-gateway 10.0.18.126
Device(config)# ip nat inside source static 192.168.5.33 3.3.3.5 redundancy group1
Device(config)# ip classless
Device(config)# ip route 10.0.32.231 255.255.255 Ethernet 3/1
Device(config)# ip route 10.10.10.0 255.255.255.0 Ethernet 3/1
Device(config)# no ip http server
The following example shows how to configure HSRP version 2 on an interface with a group number of 350:
Device(config)# interface vlan 350
Device(config-if)# standby version 2
Device(config-if)# standby 350 priority 110
Device(config-if)# standby 350 preempt
Device(config-if)# standby 350 timers 5 15
Device(config-if)# standby 350 ip 172.20.100.10
The following example shows how to set the redundancy mode to SSO. HSRP is automatically SSO-aware when this mode is enabled.
Device(config)# redundancy
Device(config-red)# mode sso
If SSO HSRP is disabled using the no standby sso command, you can reenable it as shown in the following example:
Device(config)# interface GigabitEthernet 1/0/0
Device(config-if)# ip address 10.1.1.1 255.255.0.0
Device(config-if)# standby priority 200
Device(config-if)# standby preempt
Device(config-if)# standby sso
The following examples show how to configure HSRP on two devices and enable the HSRP MIB trap support functionality. As in many environments, one device is preferred as the active one. To configure a device’s preference as the active device, configure the device at a higher priority level and enable preemption. In the following example, the active device is referred to as the primary device. The second device is referred to as the backup device:
Device(config)# interface GigabitEthernet 0/0/0
Device(config-if)# ip address 10.1.1.1 255.255.0.0
Device(config-if)# standby priority 200
Device(config-if)# standby preempt
Device(config-if)# standby ip 10.1.1.3
Device(config-if)# exit
Device(config)# snmp-server enable traps hsrp
Device(config)# snmp-server host yourhost.cisco.com public hsrp
Device(config)#interface GigabitEthernet 1/0/0
Device(config-if)# ip address 10.1.1.2 255.255.0.0
Device(config-if)# standby priority 101
Device(config-if)# standby ip 10.1.1.3
Device(config-if)# exit
Device(config)# snmp-server enable traps hsrp
Device(config)# snmp-server host myhost.cisco.com public hsrp
Hot Standby Router Protocol (HSRP) supports Bidirectional Forwarding Detection (BFD) as a part of the HSRP group member health monitoring system. Without BFD, HSRP runs as a process in a multiprocess system and cannot be guaranteed to be scheduled in time to service large numbers of groups with millisecond hello and hold timers. BFD runs as a pseudo-preemptive process and can therefore, be guaranteed to run when required. Only one BFD session between two devices can provide early failover notification for multiple HSRP groups.
In the following example, the standby bfd and the standby bfd all-interfaces commands are not displayed. HSRP support for BFD is enabled by default when BFD is configured on a device or an interface by using the bfd interval command. The standby bfd and standby bfd all-interfaces commands are needed only if BFD has been manually disabled on a device or an interface.
DeviceA(config)# ip cef
DeviceA(config)# interface FastEthernet2/0
DeviceA(config-if)# no shutdown
DeviceA(config-if)# ip address 10.0.0.2 255.0.0.0
DeviceA(config-if)# ip router-cache cef
DeviceA(config-if)# bfd interval 200 min_rx 200 multiplier 3
DeviceA(config-if)# standby 1 ip 10.0.0.11
DeviceA(config-if)# standby 1 preempt
DeviceA(config-if)# standby 1 priority 110
DeviceA(config-if)# standby 2 ip 10.0.0.12
DeviceA(config-if)# standby 2 preempt
DeviceA(config-if)# standby 2 priority 110
DeviceB(config)# interface FastEthernet2/0
DeviceB(config-if)# ip address 10.1.0.22 255.255.0.0
DeviceB(config-if)# no shutdown
DeviceB(config-if)# bfd interval 200 min_rx 200 multiplier 3
DeviceB(config-if)# standby 1 ip 10.0.0.11
DeviceB(config-if)# standby 1 preempt
DeviceB(config-if)# standby 1 priority 90
DeviceB(config-if)# standby 2 ip 10.0.0.12
DeviceB(config-if)# standby 2 preempt
DeviceB(config-if)# standby 2 priority 80
|
Related Topic |
Document Title |
|---|---|
|
Cisco IOS commands |
|
|
HSRP commands: complete command syntax, command mode, command history, defaults, usage guidelines, and examples |
Cisco IOS First Hop redundancy Protocols Command Reference |
|
HSRP for IPv6 |
“HSRP for IPv6” module |
|
Troubleshooting HSRP |
|
Standards |
Title |
|---|---|
|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
-- |
|
MIBs |
MIBs Link |
|---|---|
|
CISCO-HSRP-MIB CISCO-HSRP-EXT-MIB |
To locate and download MIBs for selected platforms, Cisco software releases, and feature sets, use Cisco MIB Locator found at the following URL: |
|
RFCs |
Title |
|---|---|
|
RFC 792 |
Internet Control Message Protocol |
|
RFC 1828 |
IP Authentication Using Keyed MD5 |
|
RFC 2281 |
Cisco Hot Standby Router Protocol |
|
Description |
Link |
|---|---|
|
The Cisco Support and Documentation website provides online resources to download documentation, software, and tools. Use these resources to install and configure the software and to troubleshoot and resolve technical issues with Cisco products and technologies. Access to most tools on the Cisco Support and Documentation website requires a Cisco.com user ID and password. |
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.|
Feature Name |
Releases |
Feature Information |
|---|---|---|
|
HSRP |
Cisco IOS XE 17.3.2 |
This feature was introduced for the Catalyst 8000 Series platforms. |
ARP—Address Resolution Protocol (ARP). ARP performs a required function in IP routing. ARP finds the hardware address, also known as Media Access Control (MAC) address, of a host from its known IP address. ARP maintains a cache (table) in which MAC addresses are mapped to IP addresses. ARP is part of all Cisco IOS systems running IP.
active device—The primary device in an HSRP group that is currently forwarding packets for the virtual device.
active RP—The active RP that controls the system, provides network services, runs the routing protocols, and presents the system management interface.
client group—An HSRP group that is created on a subinterface and linked to the primary group via the group name.
HSRP—Hot Standby Router Protocol. Protocol that provides high network availability and transparent network-topology changes. HSRP creates a router group with a lead device that services all packets sent to the HSRP address. The lead device is monitored by other devices in the group, and if it fails, one of these standby HSRP devices inherits the lead position and the HSRP group address.
ISSU—In Service Software Upgrade. A process that allows Cisco IOS software to be updated or otherwise modified while packet forwarding continues. In most networks, planned software upgrades are a significant cause of downtime. ISSU allows Cisco IOS software to be modified while packet forwarding continues, which increases network availability and reduces downtime caused by planned software upgrades.
primary group—An HSRP group that is required on a physical interface for the purposes of electing active and standby devices.
RF—Redundancy Facility. A structured, functional interface used to notify its clients of active and standby state progressions and events.
RP—Route Processor. A generic term for the centralized control unit in a chassis.
RPR—Route Processor Redundancy. RPR provides an alternative to the High System Availability (HSA) feature. HSA enables a system to reset and use a standby Route Processor (RP) if the active RP fails. Using RPR, you can reduce unplanned downtime because RPR enables a quicker switchover between an active and standby RP if the active RP experiences a fatal error.
RPR+—An enhancement to RPR in which the standby RP is fully initialized.
standby group—The set of devices participating in HSRP that jointly emulate a virtual device.
standby device—The backup device in an HSRP group.
standby RP—The backup RP.
switchover—An event in which system control and routing protocol execution are transferred from the active RP to the standby RP. Switchover may be a manual operation or may be induced by a hardware or software fault. Switchover may include transfer of the packet forwarding function in systems that combine system control and packet forwarding in an indivisible unit.
virtual IP address—The default gateway IP address configured for an HSRP group.
virtual MAC address—For Ethernet and FDDI, the automatically generated MAC address when HSRP is configured. The standard virtual MAC address used is: 0000.0C07.ACxy, where xy is the group number in hexadecimal. The functional address is used for Token Ring. The virtual MAC address is different for HSRP version 2.