About Site-to-Site VPN
Secure Firewall Threat Defense site-to-site VPN supports the following features:
-
Both IPsec IKEv1 & IKEv2 protocols.
-
Certificates and automatic or manual preshared keys for authentication.
-
IPv4 & IPv6. All combinations of inside and outside are supported.
-
IPsec IKEv2 Site-to-Site VPN topologies provide configuration settings to comply with security certifications.
-
Static and dynamic Interfaces.
-
HA environments for both management center and threat defense.
-
VPN alerts when the tunnel goes down.
-
Tunnel statistics available using the threat defense Unified CLI.
-
IKEv1 and IKEv2 back-up peer configuration for point-to-point extranet and hub-and-spoke VPNs.
-
Extranet device as hub in 'Hub and Spokes' deployments.
-
Dynamic IP address for a managed endpoint pairing with extranet device in 'Point to Point' deployments.
-
Dynamic IP address for extranet device as an endpoint.
-
Hub as extranet in 'Hub and Spokes' deployments.
VPN Topology
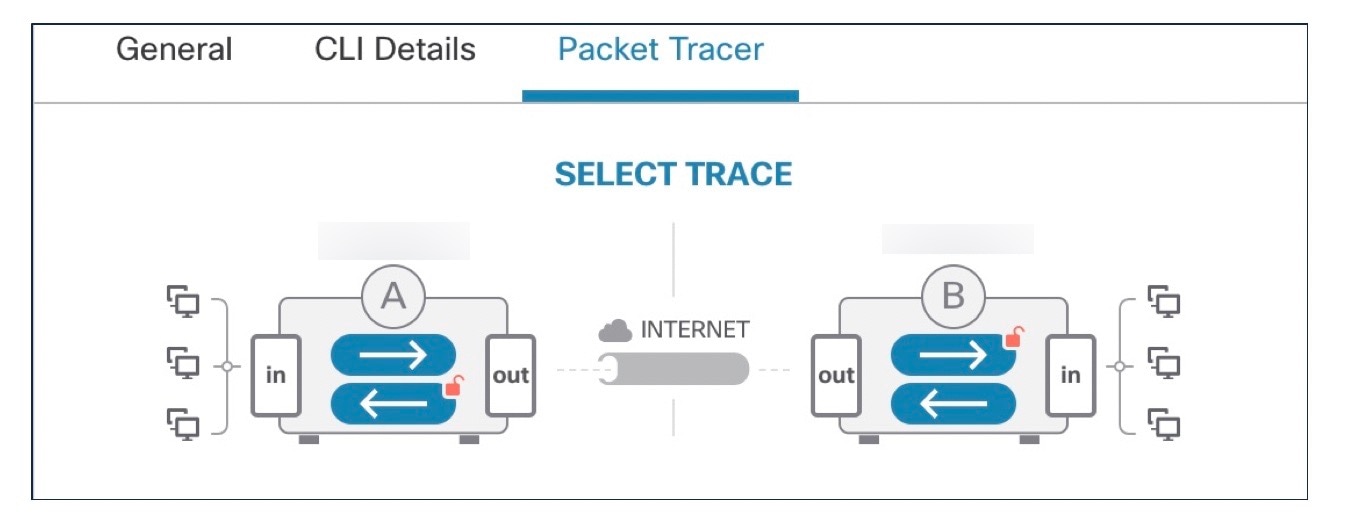
To create a new site-to-site VPN topology you must, specify a unique name, a topology type, choose the IKE version that is used for IPsec IKEv1 or IKEv2, or both. Also, determine your authentication method. Once configured, you deploy the topology to threat defense devices. The Secure Firewall Management Center configures site-to-site VPNs on threat defense devices only.
You can select from three types of topologies, containing one or more VPN tunnels:
-
Point-to-point (PTP) deployments establish a VPN tunnel between two endpoints.
-
Hub and Spoke deployments establish a group of VPN tunnels connecting a hub endpoint to a group of spoke nodes.
-
Full Mesh deployments establish a group of VPN tunnels among a set of endpoints.
IPsec and IKE
In the Secure Firewall Management Center, site-to-site VPNs are configured based on IKE policies and IPsec proposals that are assigned to VPN topologies. Policies and proposals are sets of parameters that define the characteristics of a site-to-site VPN, such as the security protocols and algorithms that are used to secure traffic in an IPsec tunnel. Several policy types may be required to define a full configuration image that can be assigned to a VPN topology.
Authentication
For authentication of VPN connections, configure a preshared key in the topology, or a trustpoint on each device. Preshared keys allow for a secret key, used during the IKE authentication phase, to be shared between two peers. A trustpoint includes the identity of the CA, CA-specific parameters, and an association with a single enrolled identity certificate.
Extranet Devices
Each topology type can include extranet devices, devices that you don’t manage in management center. These include:
-
Cisco devices that Secure Firewall Management Center supports, but for which your organization isn’t responsible. Such as spokes in networks managed by other organizations within your company, or a connection to a service provider or partner's network.
-
Non-Cisco devices. You can’t use Secure Firewall Management Center to create and deploy configurations to non-Cisco devices.
Add non-Cisco devices, or Cisco devices not managed by the Secure Firewall Management Center, to a VPN topology as "Extranet" devices. Also specify the IP address of each remote device.
Secure Firewall Threat Defense Site-to-site VPN Guidelines and Limitations
-
Site-to-site VPN supports ECMP zone interfaces.
-
You must configure all nodes in a topology with either crypto ACL or a protected network. You cannot configure a topology with crypto ACL on one node and protected network on another.
-
You can configure a VPN connection across domains by using an extranet peer for the endpoint not in the current domain.
-
You can backup Threat Defense VPNs using the management center backup.
-
IKEv1 does not support CC/UCAPL-compliant devices. We recommend that you use IKEv2 for these devices.
-
You cannot move a VPN topology between domains.
-
VPN does not support network objects with a 'range' option.
-
Threat Defense VPNs do not currently support PDF export and policy comparison.
-
There is no per-tunnel or per-device edit option for threat defense VPNs, you can edit only the whole topology.
-
The management center does not verify the device interface address verification for transport mode when you select a crypto ACL.
-
There is no support for automatic mirror ACE generation. Mirror ACE generation for the peer is a manual process on either side.
-
With crypto ACL, the management center supports only point to point VPN and does not support tunnel health events.
-
Whenever IKE ports 500/4500 are in use or when there are some active PAT translations, you cannot configure a site-to-site VPN on the same ports as it fails to start the service on those ports.
-
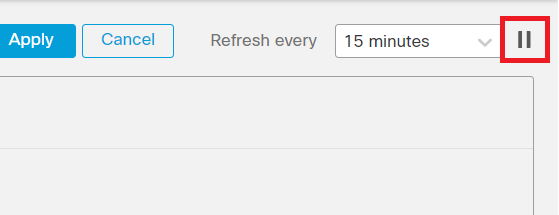
Tunnel status is not updated in realtime, but at an interval of five minutes in the management center.
-
You cannot use the character " (double quote) as part of pre-shared keys. If you have used " in a pre-shared key, ensure that you change the character.
-
In a site-to-site VPN configuration with two devices managed by the same management center, you cannot configure the devices as backup peers. You must configure one of peer devices in the topology as an extranet device.











 to view the following details about the topology:
to view the following details about the topology:



 Feedback
Feedback