About User Accounts for FMC
You can add three kinds of custom user accounts on the FMC: internal users, external users on an LDAP or RADIUS server, or SSO users on a SAML 2.0-compliant SSO identity provider. The FMC maintains separate user accounts from managed devices. For example, when you add a user to the FMC, that user only has access to the FMC; you cannot then use that username to log directly into a managed device. You must separately add a user on the managed device.
Internal, External, and SSO Users
The FMC supports three types of users:
-
Internal user—The FMC checks a local database for user authentication. For more information about internal users, see Add an Internal User.
-
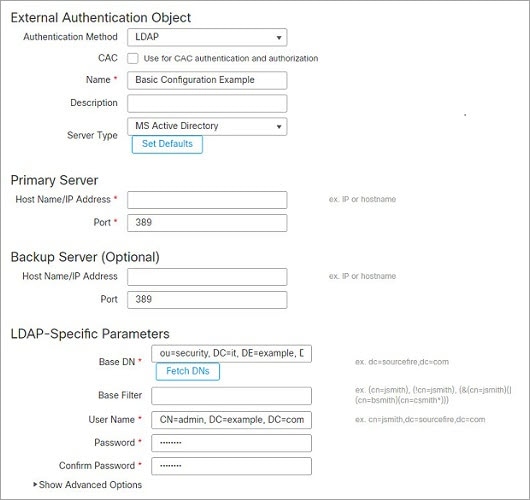
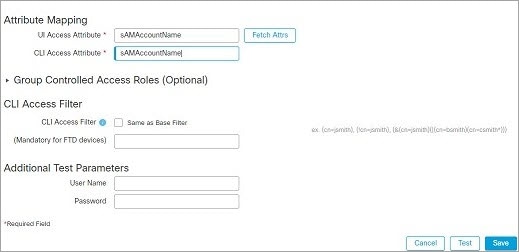
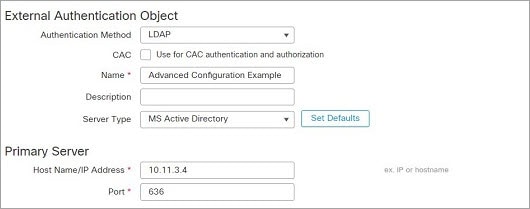
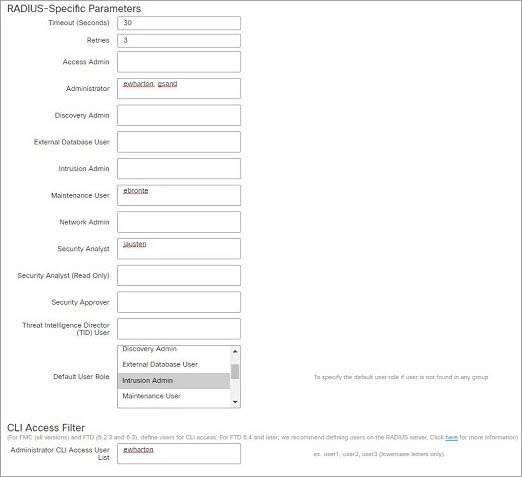
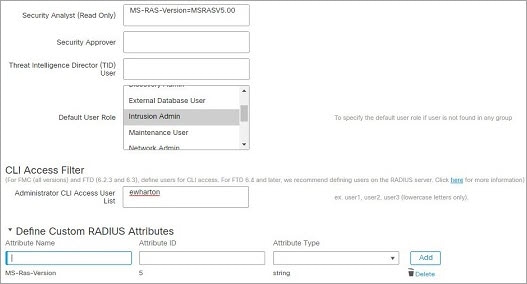
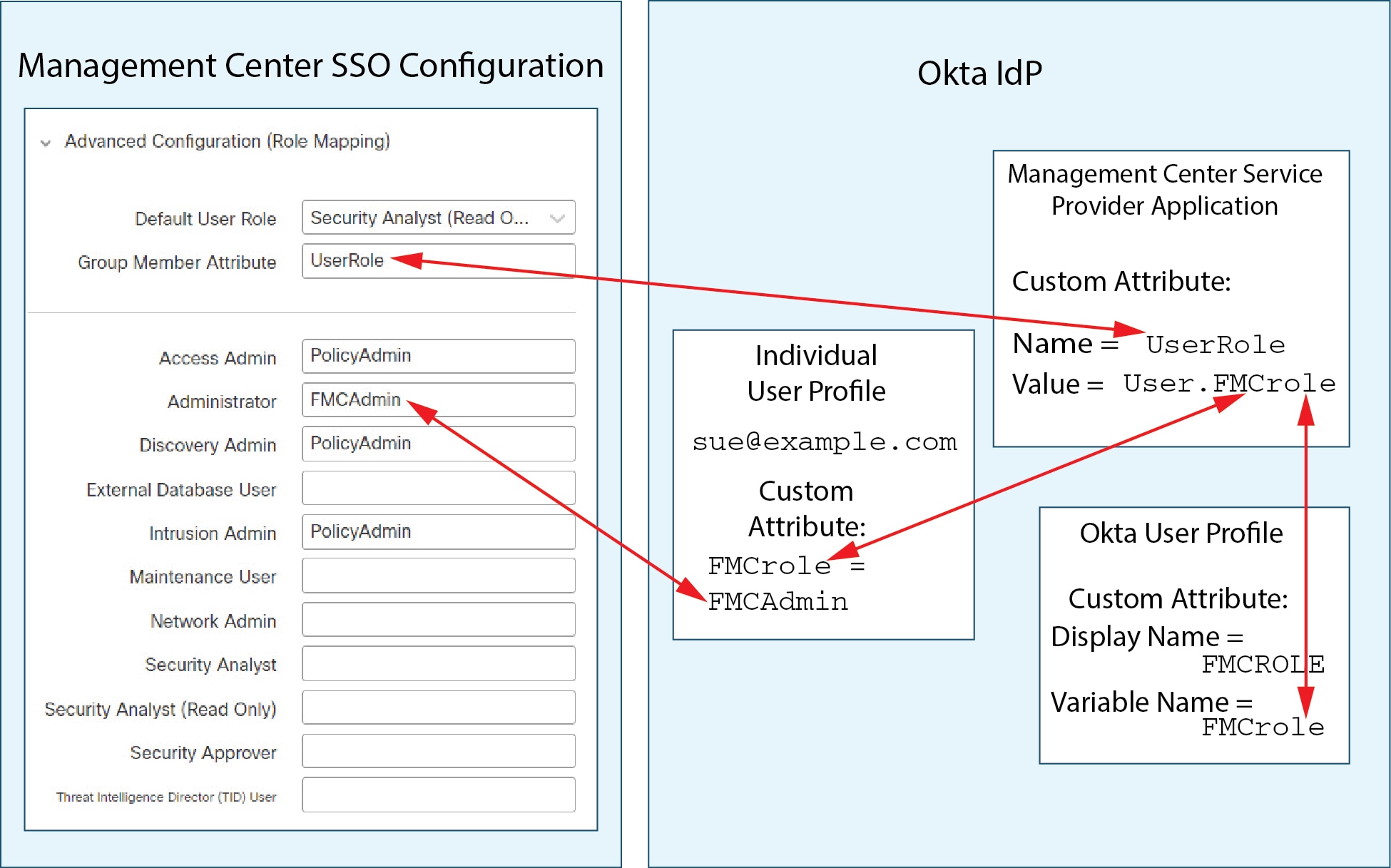
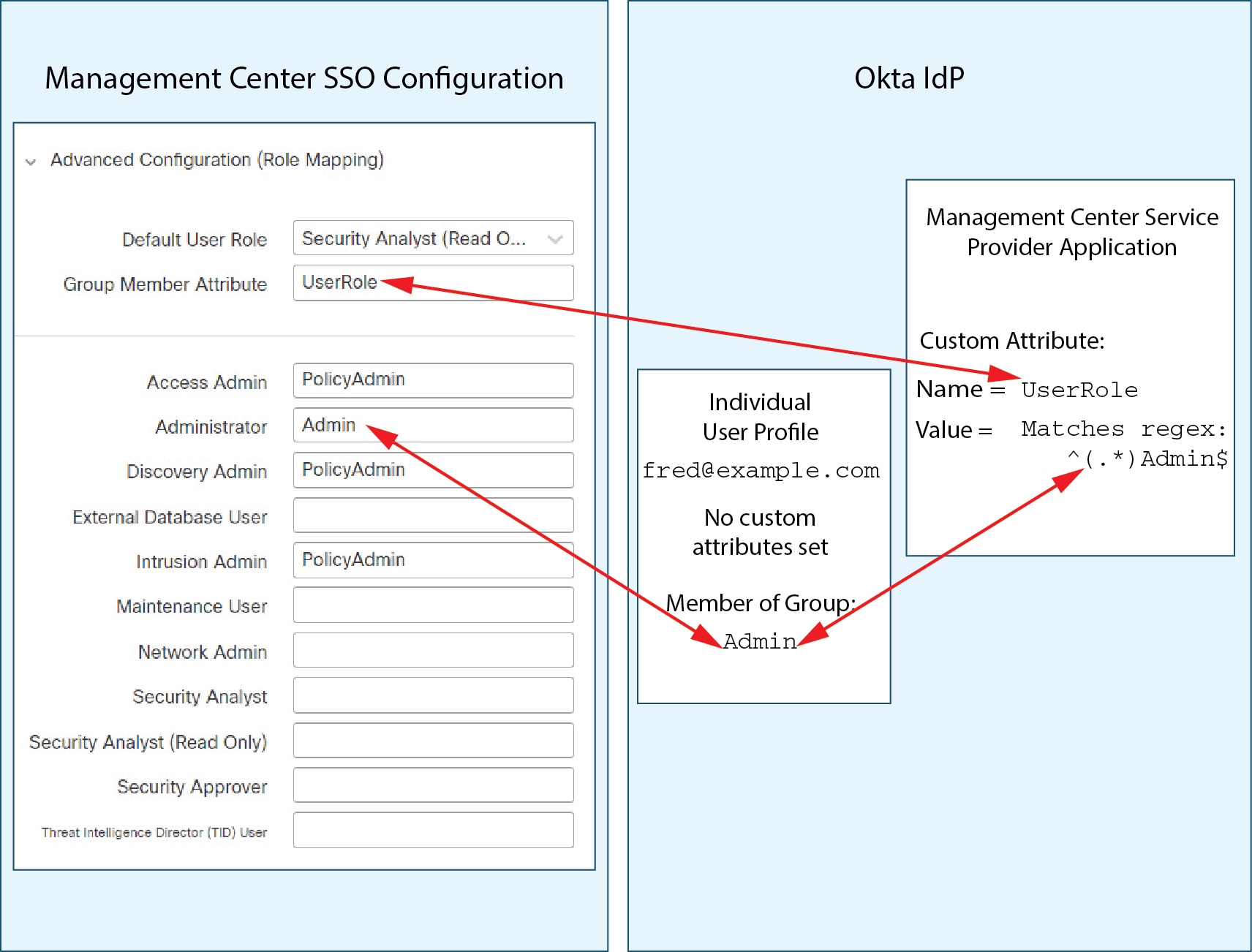
External user—If the user is not present in the local database, the system queries an external LDAP or RADIUS authentication server. For more information about external users, see Configure External Authentication .
-
SSO user—If the account is configured at an SSO identity provider, the user logs in using a Single Sign-On link on the FMC login page, and the FMC redirects the user to the IdP for authentication and authorization. For more information about SSO users see Configure SAML Single Sign-On.
Web Interface and CLI Access
The FMC has a web interface, CLI (accessible from the console (either the serial port or the keyboard and monitor) or using SSH to the management interface), and Linux shell. For detailed information about the management UIs, see Firepower System User Interfaces.
See the following information about FMC user types, and which UI they can access:
-
admin user—The FMC supports two different internal admin users: one for the web interface, and another with CLI access. The system initialization process synchronizes the passwords for these two admin accounts so they start out the same, but they are tracked by different internal mechanisms and may diverge after initial configuration. See the Getting Started Guide for your model for more information on system initialization. (To change the password for the web interface admin, use > Users. To change the password for the CLI admin, use the FMC CLI command configure password .)
-
Internal users—Internal users added in the web interface have web interface access only.
-
External users—External users have web interface access, and you can optionally configure CLI access.
-
SSO users—SSO users have web interface access only.
 Caution |
CLI users can access the Linux shell using the
expert command. We
strongly recommend that you do not use the Linux
shell unless directed by Cisco TAC or explicit
instructions in the FMC documentation. CLI users can obtain
|
User Roles
CLI User Role
CLI external users on the FMC do not have a user role; they can use all available commands.
Web Interface User Roles
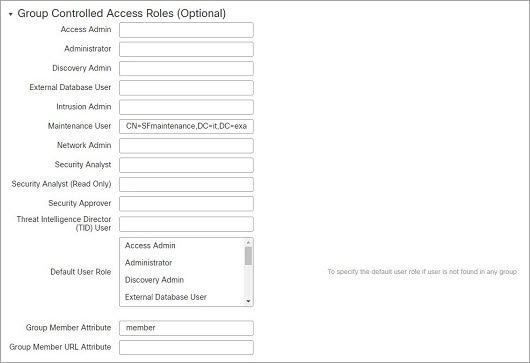
User privileges are based on the assigned user role. For example, you can grant analysts predefined roles such as Security Analyst and Discovery Admin and reserve the Administrator role for the security administrator managing the device. You can also create custom user roles with access privileges tailored to your organization’s needs.
The FMC includes the following predefined user roles:
 Note |
Predefined user roles that the system considers read-only for the purposes of concurrent session limits, are labeled with (Read Only) in the role name under and . If a user role does not contain (Read Only) in the role name, the system considers the role to be read/write. For more information on concurrent session limits, see Global User Configuration Settings. |
- Access Admin
-
Provides access to access control policy and associated features in the Policies menu. Access Admins cannot deploy policies.
- Administrator
-
Administrators have access to everything in the product; their sessions present a higher security risk if compromised, so you cannot make them exempt from login session timeouts.
You should limit use of the Administrator role for security reasons.
- Discovery Admin
-
Provides access to network discovery, application detection, and correlation features in the Policies menu. Discovery Admins cannot deploy policies.
- External Database User (Read Only)
-
Provides read-only access to the Firepower System database using an application that supports JDBC SSL connections. For the third-party application to authenticate to the Firepower System appliance, you must enable database access in the system settings. On the web interface, External Database Users have access only to online help-related options in the Help menu. Because this role’s function does not involve the web interface, access is provided only for ease of support and password changes.
- Intrusion Admin
-
Provides access to all intrusion policy, intrusion rule, and network analysis policy features in the Policies and Objects menus. Intrusion Admins cannot deploy policies.
- Maintenance User
-
Provides access to monitoring and maintenance features. Maintenance Users have access to maintenance-related options in the Health and System menus.
- Network Admin
-
Provides access to access control, SSL inspection, DNS policy, and identity policy features in the Policies menu, as well as device configuration features in the Devices menus. Network Admins can deploy configuration changes to devices.
- Security Analyst
-
Provides access to security event analysis features, and read-only access to health events, in the Overview, Analysis, Health, and System menus.
- Security Analyst (Read Only)
-
Provides read-only access to security event analysis features and health event features in the Overview, Analysis, Health, and System menus.
User with this role can also:
-
From the health monitor pages for specific devices, generate and download troubleshooting files.
-
Under user preferences, set file download preferences.
-
Under user preferences, set the default time window for event views (with the exception of the Audit Log Time Window).
-
- Security Approver
-
Provides limited access to access control and associated policies and network discovery policies in the Policies menu. Security Approvers can view and deploy these policies, but cannot make policy changes.
- Threat Intelligence Director (TID) User
-
Provides access to Threat Intelligence Director configurations in the Intelligence menu. Threat Intelligence Director (TID) Users can view and configure TID.
User Passwords
The following rules apply to passwords for internal user accounts on the FMC, with Lights-Out Management (LOM) enabled or disabled. Different password requirements apply for externally authenticated accounts or in systems with security certifications compliance enabled. See Configure External Authentication and Security Certifications Compliance for more information.
During FMC initial configuration, the system requires the admin user to set the account password to comply with strong password requirements for LOM-enabled users as described in the table below. At this time the system synchronizes the passwords for the web interface admin and the CLI access admin. After initial configuation, the web interface admin can remove the strong password requirement, but the CLI access admin must always comply with strong password requirements.
|
LOM Not Enabled |
LOM Enabled, admin user |
|
|---|---|---|
|
Password Strength Checking On |
Passwords must include:
The system checks passwords against a special dictionary containing not only many English dictionary words, but also other character strings that could be easily cracked with common password hacking techniques. |
Passwords must include:
The rules for special characters vary between different series of physical FMCs. We recommend restricting your choice of special characters to those listed in the final bullet above. Do not include the user name in the password. The system checks passwords against a special dictionary containing not only many English dictionary words, but also other character strings that could be easily cracked with common password hacking techniques. |
|
Password Strength Checking Off |
Passwords must include the minimum number of characters configured for the user by the administrator. (See Add an Internal User for more information.) |
Passwords must include:
The rules for special characters vary between different series of physical FMCs. We recommend restricting your choice of special characters to those listed in the final bullet above. Do not include the user name in the password. |



 )
)









 )
) )
) Feedback
Feedback