- Preface
- Product Overview
- Command-line Interfaces
- Configuring the Switch for the First Time
- Administering the Switch
- Configuring Supervisor Engine Redundancy Using RPR and SSO
- Configuring the Cisco IOS In Service Software Upgrade Process
- Configuring Interfaces
- Checking Port Status and Connectivity
- Configuring Cisco NSF with SSO Supervisor Engine Redundancy
- Environmental Monitoring and Power Management
- Configuring Power over Ethernet
- Configuring VLANs, VTP, and VMPS
- Configuring IP Unnumbered Interface
- Configuring Layer 2 Ethernet Interfaces
- Configuring SmartPort Macros
- Configuring STP and MST
- Configuring Optional STP Features
- Configuring EtherChannels
- Configuring CDP
- Configuring IGMP Snooping and Filtering
- Configuring IPv6 MLD Snooping
- Configuring LLDP and LLDP-MED
- Configuring UDLD
- Configuring Unidirectional Ethernet
- Configuring Layer 3 Interfaces
- Configuring Cisco Express Forwarding
- Configuring Unicast Reverse Path Forwarding
- Configuring IP Multicast
- Configuring Policy-Based Routing
- Configuring VRF-lite
- Flexible NetFlow
- Configuring Quality of Service
- Configuring Voice Interfaces
- Configuring Private VLANs
- Configuring 802.1X Port-Based Authentication
- Configuring Web-Based Authentication
- Configuring Port Security
- Configuring Control Plane Policing
- Configuring DHCP Snooping, IP Source Guard, and IPSG for Static Hosts
- Configuring Dynamic ARP Inspection
- Configuring Network Security with ACLs
- Support for IPv6
- Port Unicast and Multicast Flood Blocking
- Configuring Storm Control
- Configuring SPAN and RSPAN
- Configuring System Message Logging
- Configuring OBFL
- Configuring SNMP
- Configuring Cisco IOS IP SLAs Operations
- Configuring RMON
- Configuring Call Home
- Performing Diagnostics
- ROM Monitor
- Configuring MIB Support
- Acronyms
- Index
- About 802.1X Port-Based Authentication
- Device Roles
- 802.1X and Network Access Control
- Authentication Initiation and Message Exchange
- Ports in Authorized and Unauthorized States
- 802.1X Host Mode
- Using 802.1X with VLAN Assignment
- Using 802.1X for Guest VLANs
- Using 802.1X with MAC Authentication Bypass
- Using 802.1X with Web-Based Authentication
- Using 802.1X with Inaccessible Authentication Bypass
- Using 802.1X with Unidirectional Controlled Port
- Using 802.1X with Authentication Failed VLAN Assignment
- Using 802.1X with Port Security
- Using 802.1X Authentication with ACL Assignments and Redirect URLs
- Using 802.1X with RADIUS-Provided Session Timeouts
- Using 802.1X with Voice VLAN Ports
- Using Multiple Domain Authentication and Multiple Authentication
- How 802.1X Fails on a Port
- Supported Topologies
- Configuring 802.1X Port-Based Authentication
- Default 802.1X Configuration
- 802.1X Configuration Guidelines
- Enabling 802.1X Authentication
- Configuring Switch-to-RADIUS-Server Communication
- Configuring Multiple Domain Authentication and Multiple Authorization
- Configuring 802.1X Authentication with ACL Assignments and Redirect URLs
- Configuring 802.1X Authentication with Per-User ACL and Filter-ID ACL
- Configuring RADIUS-Provided Session Timeouts
- Configuring 802.1X with Guest VLANs
- Configuring 802.1X with MAC Authentication Bypass
- Configuring 802.1X with Inaccessible Authentication Bypass
- Configuring 802.1X with Unidirectional Controlled Port
- Configuring 802.1X with Authentication Failed
- Configuring 802.1X with Voice VLAN
- Configuring 802.1X with VLAN Assignment
- Enabling Fallback Authentication
- Enabling Periodic Reauthentication
- Enabling Multiple Hosts
- Changing the Quiet Period
- Changing the Switch-to-Client Retransmission Time
- Setting the Switch-to-Client Frame-Retransmission Number
- Manually Reauthenticating a Client Connected to a Port
- Initializing the 802.1X Authentication State
- Removing 802.1X Client Information
- Resetting the 802.1X Configuration to the Default Values
- Displaying 802.1X Statistics and Status
- Displaying Authentication Details
- Determining the Authentication Methods Registered with the Auth Manager
- Displaying the Auth Manager Summary for an Interface
- Displaying the Summary of All Auth Manager Sessions on the Switch
- Displaying a Summary of All Auth Manager Sessions on the Switch Authorized for a Specified Authentication Method
- Verifying the Auth Manager Session for an Interface
- Displaying MAB Details
- EPM Logging
- -Cisco IOS Security Features in Cisco IOS XE 3.1.0 SG Release
Configuring 802.1X Port-Based Authentication
This chapter describes how to configure IEEE 802.1X port-based authentication on the Catalyst 4500 series switch to prevent unauthorized client devices from gaining access to the network.
This chapter includes the following major sections:
•![]() About 802.1X Port-Based Authentication
About 802.1X Port-Based Authentication
•![]() Configuring 802.1X Port-Based Authentication
Configuring 802.1X Port-Based Authentication
•![]() Displaying 802.1X Statistics and Status
Displaying 802.1X Statistics and Status
•![]() Displaying Authentication Details
Displaying Authentication Details
•![]() -Cisco IOS Security Features in Cisco IOS XE 3.1.0 SG Release
-Cisco IOS Security Features in Cisco IOS XE 3.1.0 SG Release

Note ![]() For complete syntax and usage information for the switch commands used in this chapter, look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
For complete syntax and usage information for the switch commands used in this chapter, look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
http://www.cisco.com/en/US/products/hw/switches/ps4324/index.html
If the command is not found in the Catalyst 4500 Command Reference, it is located in the larger Cisco IOS library. Refer to the Catalyst 4500 Series Switch Cisco IOS Command Reference and related publications at this location:
http://www.cisco.com/en/US/products/ps6350/index.html
About 802.1X Port-Based Authentication
802.1X defines 802.1X port-based authentication as a client-server based access control and authentication protocol that restricts unauthorized clients from connecting to a LAN through publicly accessible ports. An authentication server validates each supplicant (client) connected to an authenticator (network access switch) port before making available any services offered by the switch or the LAN.

Note ![]() 802.1X support requires an authentication server that is configured for Remote Authentication Dial-In User Service (RADIUS). 802.1X authentication does not work unless the network access switch can route packets to the configured RADIUS server. To verify that the switch can route packets, you must ping the server from the switch.
802.1X support requires an authentication server that is configured for Remote Authentication Dial-In User Service (RADIUS). 802.1X authentication does not work unless the network access switch can route packets to the configured RADIUS server. To verify that the switch can route packets, you must ping the server from the switch.
Until a client is authenticated, only Extensible Authentication Protocol over LAN (EAPOL) traffic is allowed through the port to which the client is connected. After authentication succeeds, normal traffic can pass through the port.
To configure 802.1X port-based authentication, you need to understand the concepts in these sections:
•![]() 802.1X and Network Access Control
802.1X and Network Access Control
•![]() Authentication Initiation and Message Exchange
Authentication Initiation and Message Exchange
•![]() Ports in Authorized and Unauthorized States
Ports in Authorized and Unauthorized States
•![]() Using 802.1X with VLAN Assignment
Using 802.1X with VLAN Assignment
•![]() Using 802.1X with MAC Authentication Bypass
Using 802.1X with MAC Authentication Bypass
•![]() Using 802.1X with Web-Based Authentication
Using 802.1X with Web-Based Authentication
•![]() Using 802.1X with Inaccessible Authentication Bypass
Using 802.1X with Inaccessible Authentication Bypass
•![]() Using 802.1X with Unidirectional Controlled Port
Using 802.1X with Unidirectional Controlled Port
•![]() Using 802.1X with Authentication Failed VLAN Assignment
Using 802.1X with Authentication Failed VLAN Assignment
•![]() Using 802.1X with Port Security
Using 802.1X with Port Security
•![]() Using 802.1X Authentication with ACL Assignments and Redirect URLs
Using 802.1X Authentication with ACL Assignments and Redirect URLs
•![]() Using 802.1X with RADIUS-Provided Session Timeouts
Using 802.1X with RADIUS-Provided Session Timeouts
•![]() Using 802.1X with Voice VLAN Ports
Using 802.1X with Voice VLAN Ports
•![]() Using Multiple Domain Authentication and Multiple Authentication
Using Multiple Domain Authentication and Multiple Authentication
Device Roles
With 802.1X port-based authentication, network devices have specific roles. Figure 36-1 shows the role of each device, which is described below.
Figure 36-1 802.1X Device Roles

•![]() Client—The workstation that requests access to the LAN, and responds to requests from the switch. The workstation must be running 802.1X-compliant client software.
Client—The workstation that requests access to the LAN, and responds to requests from the switch. The workstation must be running 802.1X-compliant client software.
•![]() Authenticator—Controls physical access to the network based on the authentication status of the client. The Catalyst 4500 series switch acts as an intermediary between the client and the authentication server, requesting identity information from the client, verifying that information with the authentication server, and relaying a response to the client. The switch encapsulates and decapsulates the Extensible Authentication Protocol (EAP) frames and interacts with the RADIUS authentication server.
Authenticator—Controls physical access to the network based on the authentication status of the client. The Catalyst 4500 series switch acts as an intermediary between the client and the authentication server, requesting identity information from the client, verifying that information with the authentication server, and relaying a response to the client. The switch encapsulates and decapsulates the Extensible Authentication Protocol (EAP) frames and interacts with the RADIUS authentication server.
When the switch receives EAPOL frames and relays them to the authentication server, the Ethernet header is stripped and the remaining EAP frame is reencapsulated in the RADIUS format. The EAP frames are not modified or examined during encapsulation, and the authentication server must support EAP within the native frame format. When the switch receives frames from the authentication server, the frame header is removed from the server, leaving the EAP frame, which is then encapsulated for Ethernet and sent to the client.

Note ![]() The Catalyst 4500 series switches must be running software that supports the RADIUS client and 802.1X.
The Catalyst 4500 series switches must be running software that supports the RADIUS client and 802.1X.
•![]() Authentication server—Performs the actual authentication of the client. The authentication server validates the identity of the client and notifies the switch that the client is authorized to access the LAN and switch services. (The only supported authentication server is the RADIUS authentication server with EAP extensions; it is available in Cisco Secure Access Control Server version 3.2 and later.)
Authentication server—Performs the actual authentication of the client. The authentication server validates the identity of the client and notifies the switch that the client is authorized to access the LAN and switch services. (The only supported authentication server is the RADIUS authentication server with EAP extensions; it is available in Cisco Secure Access Control Server version 3.2 and later.)
802.1X and Network Access Control
Network Access Control is a feature that allows port access policies to be influenced by the anti-virus posture of the authenticating device.
Anti-virus posture includes such elements as the operating system running on the device, the operating system version, whether anti-virus software is installed, what version of anti-virus signatures is available, etc. If the authenticating device has a NAC-aware 802.1X supplicant and the authentication server is configured to support NAC via 802.1X, anti-virus posture information is automatically included as part of the 802.1X authentication exchange.
For information on NAC, refer to the URL:
http://www.cisco.com/en/US/products/ps6128/index.html
Authentication Initiation and Message Exchange
The switch or the client can initiate authentication. If you enable authentication on a port with the
authentication port-control auto interface configuration command (dot1x port-control auto command in Cisco IOS Release 12.2(46)SG and earlier releases), the switch must initiate authentication when it determines that the port link state has changed. It then sends an EAP-request/identity frame to the client to request its identity (typically, the switch sends an initial identity/request frame followed by one or more requests for authentication information). Upon receipt of the frame, the client responds with an EAP-response/identity frame.
However, if during bootup, the client does not receive an EAP-request/identity frame from the switch, the client can initiate authentication by sending an EAPOL-start frame, which prompts the switch to request the client's identity.
If 802.1X is not enabled or supported on the network access switch, any EAPOL frames from the client are dropped. If the client does not receive an EAP-request/identity frame after three attempts to start authentication, the client transmits frames as if the port is in the authorized state. A port in the authorized state means that the client has been successfully authenticated. When the client supplies its identity, the switch begins its role as the intermediary, passing EAP frames between the client and the authentication server until authentication succeeds or fails. If the authentication succeeds, the switch port becomes authorized.
The specific exchange of EAP frames depends on the authentication method being used. Figure 36-2 shows a message exchange that is initiated by the client using the One-Time Password (OTP) authentication method with an authentication server.
Figure 36-2 Message Exchange

Ports in Authorized and Unauthorized States
The switch port state determines whether the client is granted access to the network. The port starts in the unauthorized state. While in this state, the port disallows all ingress and egress traffic except for 802.1X protocol packets. When a client is successfully authenticated, the port transitions to the authorized state, allowing all traffic for the client to flow normally.
If a non-802.1X capable client is connected to an unauthorized 802.1X port, the switch requests the client's identity. In this situation, the client does not respond to the request, the port remains in the unauthorized state, and the client is not granted access to the network. If a guest VLAN is configured on a port that connects to a client that does not support 802.1X, the port is placed in the configured guest VLAN and in the authorized state. For more information, see the "Using 802.1X for Guest VLANs" section.
In contrast, when an 802.1X-enabled client connects to a port that is not running the 802.1X protocol, the client initiates the authentication process by sending the EAPOL-start frame. When no response is received, the client sends the request a fixed number of times. Because no response is received, the client begins sending frames as if the port is in the authorized state.
You can control the port authorization state with the authentication port-control interface configuration command and these keywords:
•![]() force-authorized—Disables 802.1X authentication and causes the port to transition to the authorized state without requiring authentication exchange. The port transmits and receives normal traffic without 802.1X-based authentication of the client. This setting is the default.
force-authorized—Disables 802.1X authentication and causes the port to transition to the authorized state without requiring authentication exchange. The port transmits and receives normal traffic without 802.1X-based authentication of the client. This setting is the default.
•![]() force-unauthorized—Causes the port to remain in the unauthorized state, ignoring all attempts by the client to authenticate. The switch cannot provide authentication services to the client through the interface.
force-unauthorized—Causes the port to remain in the unauthorized state, ignoring all attempts by the client to authenticate. The switch cannot provide authentication services to the client through the interface.
•![]() auto—Enables 802.1X authentication and causes the port to begin in the unauthorized state, allowing only EAPOL frames to be sent and received through the port. The authentication process begins when the link state of the port transitions from down to up or when an EAPOL-start frame is received. The switch requests the identity of the client and begins relaying authentication messages between the client and the authentication server. The switch can uniquely identify each client attempting to access the network by the client's MAC address.
auto—Enables 802.1X authentication and causes the port to begin in the unauthorized state, allowing only EAPOL frames to be sent and received through the port. The authentication process begins when the link state of the port transitions from down to up or when an EAPOL-start frame is received. The switch requests the identity of the client and begins relaying authentication messages between the client and the authentication server. The switch can uniquely identify each client attempting to access the network by the client's MAC address.
If the client is successfully authenticated (receives an Accept frame from the authentication server), the port state changes to authorized, and all frames from the authenticated client are allowed through the port. If authentication fails, the port remains in the unauthorized state, but authentication can be retried. If the authentication server cannot be reached, the switch can retransmit the request. If no response is received from the server after the specified number of attempts, authentication fails and network access is not granted.
If the link state of a port transitions from up to down, or if an EAPOL-logoff frame is received by the port, the port returns to the unauthorized state.
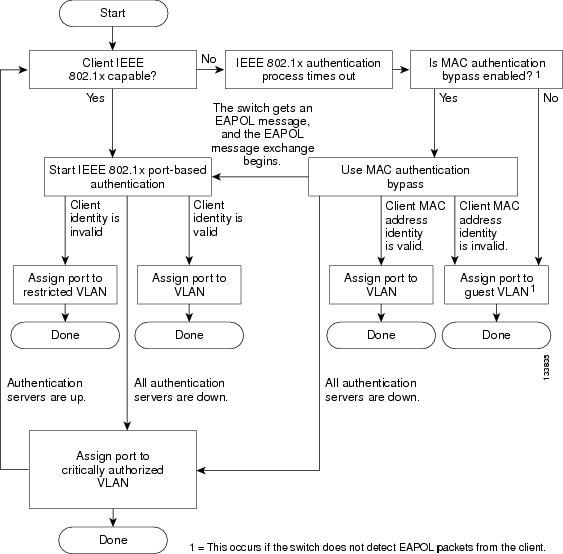
Figure 36-3 shows the authentication process.
If Multidomain Authentication (MDA) is enabled on a port, this flow can be used with some exceptions that are applicable to voice authorization. For more information on MDA, see the
"Using Multiple Domain Authentication and Multiple Authentication" section.
Figure 36-3 Authentication Flowchart
802.1X Host Mode
The 802.1X port's host mode determines whether more than one client can be authenticated on the port and how authentication is enforced. You can configure an 802.1X port to use any of the five host modes described in the following sections. In addition, each mode may be modified to allow pre-authentication open access:
•![]() Multidomain Authentication Mode
Multidomain Authentication Mode
•![]() Pre-Authentication Open Access
Pre-Authentication Open Access
Single-Host Mode
You can configure an 802.1X port for single-host or multiple-hosts mode. In single-host mode (see Figure 36-1), only one client can be connected to the 802.1X-enabled switch port. The switch detects the client by sending an EAPOL frame when the port link state changes to the up state. If a client leaves or is replaced with another client, the switch changes the port link state to down, and the port returns to the unauthorized state.
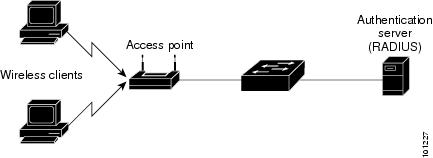
Multiple-Hosts Mode
In multiple-hosts mode, you can attach multiple hosts to a single 802.1X-enabled port. Figure 36-4 shows 802.1X port-based authentication in a wireless LAN. In this mode, only one of the attached clients must be authorized for all clients to be granted network access. If the port becomes unauthorized (re-authentication fails or an EAPOL-logoff message is received), the switch denies network access to all of the attached clients. In this topology, the wireless access point is responsible for authenticating the clients attached to it, and it also acts as a client to the switch.
With multiple-hosts mode enabled, use 802.1X authentication to authenticate the port and port security to manage network access for all MAC addresses, including that of the client.
Figure 36-4 Multiple Host Mode Example
Multidomain Authentication Mode
Multidomain Authentication (MDA), which allows an IP phone (Cisco or third-party) and a single host behind the IP phone to authenticate independently, using 802.1X, MAC authentication bypass (MAB) or (for the host only) web-based authentication. In this application, multidomain refers to two domains — data and voice — and only two MAC addresses are allowed per port. A switch can place the host in the data VLAN and the IP phone in the voice VLAN, even though they appear on the same switch port. The data VLAN and the voice VLAN can be specified in the CLI configuration. The devices are identified as either data or voice depending on the vendor-specific-atributes (VSAs) received from the authentication, authorization, and accounting (AAA) server. The data and voice VLANs can also be obtained from the VSAs received from the (AAA) server during authentication.
Figure 36-5 Multidomain Authentication Mode Example

Figure 36-5 shows a typical MDA application with a single host behind an IP phone connected to the 802.1X-enabled port. Because the client is not directly connected to the switch, the switch cannot detect a loss of port link if the client is disconnected. To prevent another device from using the established authentication of the disconnected client later, Cisco IP phones send a Cisco Discovery Protocol (CDP) host presence type length value (TLV) to notify the switch of changes in the attached client's port link state.
For details on how to configure MDA, see the "Using Multiple Domain Authentication and Multiple Authentication" section.
Multiauthentication Mode
Available starting in Cisco IOS Release 12.2(50)SG, multiauthentication mode allows one client on the voice VLAN and multiple authenticated clients on the data VLAN. When a hub or access point is connected to an 802.1X port, multiauthentication mode provides enhanced security over multiple-hosts mode by requiring authentication of each connected client. For non-802.1X devices, use MAB or web-based authentication as the fallback method for individual host authentications, allowing you to authenticate different hosts through different methods on a single port.
Multiauthentication also supports MDA functionality on the voice VLAN by assigning authenticated devices to either a data or voice VLAN depending on the VSAs received from the authentication server.

Note ![]() When a port is in multiauthentication mode, all VLAN assignment features including RADIUS server supplied VLAN assignment, Guest VLAN, Inaccessible Authentication Bypass, and Authentication Failed VLAN does not activate for data devices. However, RADIUS server supplied VLAN assignment is possible for voice devices.
When a port is in multiauthentication mode, all VLAN assignment features including RADIUS server supplied VLAN assignment, Guest VLAN, Inaccessible Authentication Bypass, and Authentication Failed VLAN does not activate for data devices. However, RADIUS server supplied VLAN assignment is possible for voice devices.
Pre-Authentication Open Access
Starting with Cisco IOS Release 12.2(50)SG, any of the four host modes may be additionally configured to allow a device to gain network access before authentication. This pre-authentication open access is useful in an application such as the Pre-boot eXecution Environment (PXE), where a device must access the network to download a bootable image containing an authentication client.
Enable pre-authentication open access by entering the authentication open command after host mode configuration. It acts as an extension to the configured host mode. For example, if pre-authentication open access is enabled with single-host mode, then the port allows only one MAC address. When pre-authentication open access is enabled, initial traffic on the port is restricted only by whatever other access restriction, independent of 802.1X, is configured on the port. If no access restriction other than 802.1X is configured on the port, then a client device has full access on the configured VLAN.
Using 802.1X with VLAN Assignment
VLAN assignment allows you to limit network access for certain users. With the VLAN assignment, 802.1X-authenticated ports are assigned to a VLAN based on the username of the client connected to that port. The RADIUS server database maintains the username-to-VLAN mappings. After successful 802.1X authentication of the port, the RADIUS server sends the VLAN assignment to the switch. The VLAN can be a standard VLAN or a private VLAN (PVLAN).
On platforms that support PVLANs, you can isolate hosts by assigning ports into PVLANs.
When configured on the switch and the RADIUS server, 802.1X with VLAN assignment has these characteristics:
•![]() If no VLAN is supplied by the RADIUS server, the port is configured in its access VLAN or isolated PVLAN when authentication succeeds.
If no VLAN is supplied by the RADIUS server, the port is configured in its access VLAN or isolated PVLAN when authentication succeeds.
•![]() If the authentication server provides invalid VLAN information, the port remains unauthorized. This situation prevents ports from appearing unexpectedly in an inappropriate VLAN due to a configuration error.
If the authentication server provides invalid VLAN information, the port remains unauthorized. This situation prevents ports from appearing unexpectedly in an inappropriate VLAN due to a configuration error.
•![]() If the multiauthentication mode is enabled on an 802.1X port, the VLAN assignment is ignored for data devices. VLAN assignment is possible for voice device even if the port is configured in multiauthentication mode.
If the multiauthentication mode is enabled on an 802.1X port, the VLAN assignment is ignored for data devices. VLAN assignment is possible for voice device even if the port is configured in multiauthentication mode.
•![]() If the authentication server provides valid VLAN information, the port is authorized and placed in the specified VLAN when authentication succeeds.
If the authentication server provides valid VLAN information, the port is authorized and placed in the specified VLAN when authentication succeeds.
•![]() If the multiple-hosts mode is enabled, all hosts are in the same VLAN as the first authenticated user.
If the multiple-hosts mode is enabled, all hosts are in the same VLAN as the first authenticated user.
•![]() If 802.1X is disabled on the port, the port is returned to the configured access VLAN.
If 802.1X is disabled on the port, the port is returned to the configured access VLAN.
•![]() A port must be configured as an access port (which can be assigned only into "regular" VLANs), or as a PVLAN host port (which can be assigned only into PVLANs). Configuring a port as a PVLAN host port implies that all hosts on the port are assigned into PVLANs, whether their posture is compliant or non-compliant. If the type of the VLAN named in the Access-Accept does not match the type of VLAN expected to be assigned to the port (regular VLAN to access port, secondary PVLAN to PVLAN host port), the VLAN assignment fails.
A port must be configured as an access port (which can be assigned only into "regular" VLANs), or as a PVLAN host port (which can be assigned only into PVLANs). Configuring a port as a PVLAN host port implies that all hosts on the port are assigned into PVLANs, whether their posture is compliant or non-compliant. If the type of the VLAN named in the Access-Accept does not match the type of VLAN expected to be assigned to the port (regular VLAN to access port, secondary PVLAN to PVLAN host port), the VLAN assignment fails.
•![]() If a guest VLAN is configured to handle non-responsive hosts, the type of VLAN configured as the guest VLAN must match the port type (that is, guest VLANs configured on access ports must be standard VLANs, and guest VLANs configured on PVLAN host ports must be PVLANs). If the guest VLAN's type does not match the port type, non-responsive hosts are treated as if no guest VLAN is configured (that is, they are denied network access).
If a guest VLAN is configured to handle non-responsive hosts, the type of VLAN configured as the guest VLAN must match the port type (that is, guest VLANs configured on access ports must be standard VLANs, and guest VLANs configured on PVLAN host ports must be PVLANs). If the guest VLAN's type does not match the port type, non-responsive hosts are treated as if no guest VLAN is configured (that is, they are denied network access).
•![]() To assign a port into a PVLAN, the named VLAN must be a secondary PVLAN. The switch determines the implied primary VLAN from the locally configured secondary-primary association.
To assign a port into a PVLAN, the named VLAN must be a secondary PVLAN. The switch determines the implied primary VLAN from the locally configured secondary-primary association.

Note ![]() If you change the access VLAN or PVLAN host VLAN mapping on a port that is already authorized in a RADIUS assigned VLAN, the port remains in the RADIUS assigned VLAN.
If you change the access VLAN or PVLAN host VLAN mapping on a port that is already authorized in a RADIUS assigned VLAN, the port remains in the RADIUS assigned VLAN.
To configure VLAN assignment you need to perform these tasks:
•![]() Enable AAA authorization with the network keyword to allow interface configuration from the RADIUS server. For an illustration of how to apply the aaa authorization network group radius command, refer to the section "Enabling 802.1X Authentication" on page 24.
Enable AAA authorization with the network keyword to allow interface configuration from the RADIUS server. For an illustration of how to apply the aaa authorization network group radius command, refer to the section "Enabling 802.1X Authentication" on page 24.
•![]() Enable 802.1X. (The VLAN assignment feature is automatically enabled when you configure 802.1X on an access port.)
Enable 802.1X. (The VLAN assignment feature is automatically enabled when you configure 802.1X on an access port.)
•![]() Assign vendor-specific tunnel attributes in the RADIUS server. To ensure proper VLAN assignment, the RADIUS server must return these attributes to the switch:
Assign vendor-specific tunnel attributes in the RADIUS server. To ensure proper VLAN assignment, the RADIUS server must return these attributes to the switch:
–![]() Tunnel-Type = VLAN
Tunnel-Type = VLAN
–![]() Tunnel-Medium-Type = 802
Tunnel-Medium-Type = 802
–![]() Tunnel-Private-Group-ID = VLAN NAME
Tunnel-Private-Group-ID = VLAN NAME
Using 802.1X for Guest VLANs
Guest VLANs allow you to enable non-802.1X-capable hosts to access networks that use 802.1X authentication. For example, use guest VLANs when you upgrade your system to support 802.1X authentication.
Guest VLANs are supported on individual ports. Any VLAN functions as a guest VLAN provided its type matches the port type. If a port is already forwarding on the guest VLAN and you enable 802.1X support on the network interface of the host, the port is immediately moved out of the guest VLAN and the authenticator waits for authentication to occur.
Enabling 802.1X authentication on a port starts the 802.1X protocol. If the host fails to respond to packets from the authenticator within a certain amount of time, the authenticator brings the port up in the configured guest VLAN.
If the port is configured as a PVLAN host port, the guest VLAN must be a secondary PVLAN. If the port is configured as an access port, the guest VLAN must be a regular VLAN. If the guest VLAN configured on a port is not appropriate for the type of the port, the switch behaves as if no guest VLAN is configured (that is, non-responsive hosts are denied network access).
For details on how to configure guest VLANs, see the "Configuring 802.1X with Guest VLANs" section.
Usage Guidelines for Using 802.1X Authentication with Guest VLANs
The usage guidelines for using 802.1X authentication with guest VLANs are as follows:
•![]() When you reconfigure a guest VLAN to a different VLAN, any authentication failed ports are also moved and the ports stay in their current authorized state.
When you reconfigure a guest VLAN to a different VLAN, any authentication failed ports are also moved and the ports stay in their current authorized state.
•![]() When you shut down or remove a guest VLAN from the VLAN database, any authentication failed ports are immediately moved to an unauthorized state and the authentication process is restarted.
When you shut down or remove a guest VLAN from the VLAN database, any authentication failed ports are immediately moved to an unauthorized state and the authentication process is restarted.

Note ![]() No periodic reauthentication is allowed with guest VLANs.
No periodic reauthentication is allowed with guest VLANs.
Usage Guidelines for Using 802.1X Authentication with Guest VLANs on Windows-XP Hosts
The usage guidelines for using 802.1X authentication with guest VLANs on Windows-XP hosts are as follows:
•![]() If the host fails to respond to the authenticator, the port attempts to connect three times (with a 30 second timeout between each attempt). After this time, the login/password window does not appear on the host, so you must unplug and reconnect the network interface cable.
If the host fails to respond to the authenticator, the port attempts to connect three times (with a 30 second timeout between each attempt). After this time, the login/password window does not appear on the host, so you must unplug and reconnect the network interface cable.
•![]() Hosts responding with an incorrect login/password fail authentication. Hosts failing authentication are not put in the guest VLAN. The first time that a host fails authentication, the quiet-period timer starts, and no activity occurs for the duration of the quiet-period timer. When the quiet-period timer expires, the host is presented with the login/password window. If the host fails authentication for the second time, the quiet-period timer starts again, and no activity occurs for the duration of the quiet-period timer. The host is presented with the login/password window a third time. If the host fails authentication the third time, the port is placed in the unauthorized state, and you must disconnect and reconnect the network interface cable.
Hosts responding with an incorrect login/password fail authentication. Hosts failing authentication are not put in the guest VLAN. The first time that a host fails authentication, the quiet-period timer starts, and no activity occurs for the duration of the quiet-period timer. When the quiet-period timer expires, the host is presented with the login/password window. If the host fails authentication for the second time, the quiet-period timer starts again, and no activity occurs for the duration of the quiet-period timer. The host is presented with the login/password window a third time. If the host fails authentication the third time, the port is placed in the unauthorized state, and you must disconnect and reconnect the network interface cable.
Using 802.1X with MAC Authentication Bypass
The 802.1X protocol has 3 entities: client (supplicant), authenticator, and authentication server. Typically, the host PC runs the supplicant software and tries to authenticate itself by sending its credentials to the authenticator which in turn relays that info to the authentication server for authentication.
However, not all hosts may have supplicant functionality. Devices that cannot authenticate themselves using 802.1X but still need network access can use MAC Authentication Bypass (MAB), which uses the connecting device's MAC address to grant or deny network access.
Typically, you would use this feature on ports where devices such as printers are connected. Such devices do not have 802.1X supplicant functionality.
In a typical deployment, the RADIUS server maintains a database of MAC addresses that require access. When this feature detects a new MAC address on a port, it generates a RADIUS request with both username and password as the device's MAC address. After authorization succeeds, the port is accessible to the particular device through the same code path that 802.1X authentication would take when processing an 802.1X supplicant. If authentication fails, the port moves to the guest VLAN if configured, or it remains unauthorized.
The Catalyst 4500 series switch also supports re-authentication of MACs on a per port level. Be aware that the re-authentication functionality is by 802.1X and is not MAB specific. In the re-authentication mode, a port stays in the previous RADIUS-sent VLAN and tries to re-authenticate itself. If the re-authentication succeeds, the port stays in the RADIUS-sent VLAN. Otherwise, the port becomes unauthorized and moves to the guest VLAN if one is configured.
For details on how to configure MAB, see the "Configuring 802.1X with MAC Authentication Bypass" section.
Feature Interaction
This section lists feature interactions and restrictions when MAB is enabled. If a feature is not listed, assume that it interacts seamlessly with MAB (such as Unidirectional Controlled Port).
•![]() MAB can only be enabled if 802.1X is configured on a port. MAB functions as a fall back mechanism for authorizing MACs. If you configure both MAB and 802.1X on a port, the port attempts to authenticate using 802.1X. If the host fails to respond to EAPOL requests and MAB is configured, the 802.1X port is opened up to listen to packets and to grab a MAC address, rather than attempt to authenticate endlessly.
MAB can only be enabled if 802.1X is configured on a port. MAB functions as a fall back mechanism for authorizing MACs. If you configure both MAB and 802.1X on a port, the port attempts to authenticate using 802.1X. If the host fails to respond to EAPOL requests and MAB is configured, the 802.1X port is opened up to listen to packets and to grab a MAC address, rather than attempt to authenticate endlessly.
Based on the default 802.1X timer values, the transition between mechanisms takes approximately 90 seconds. You can shorten the time by reducing the value of the transmission period time, which affects the frequency of EAPOL transmission. A smaller timer value results in EAPOLs sent during a shorter period of time. With MAB enabled, after 802.1X performs one full set of EAPOLs, the learned MAC address is forwarded to the authentication server for processing.
The MAB module performs authorization for the first MAC address detected on the wire. The port is considered authorized once a valid MAC address is received that RADIUS approves of.
802.1X authentication can re-start if an EAPOL packet is received on a port that was initially authorized as a result of MAB.
Figure 36-6 shows the message exchange during MAB.
Figure 36-6 Message Exchange during MAC Authentication Bypass

•![]() The authentication-failed VLAN is used only with dot1x-authentication-failed users. MAB is not attempted with dot1x-authentication-failed users. If 802.1X authentication fails, a port moves to the authentication-failed VLAN (if configured) whether MAB is configured or not.
The authentication-failed VLAN is used only with dot1x-authentication-failed users. MAB is not attempted with dot1x-authentication-failed users. If 802.1X authentication fails, a port moves to the authentication-failed VLAN (if configured) whether MAB is configured or not.
•![]() When both MAB and guest VLAN are configured and no EAPOL packets are received on a port, the 802.1X state-machine is moved to a MAB state where it opens the port to listen to traffic and grab MAC addresses. The port remains in this state forever waiting to see a MAC on the port. A detected MAC address that fails authorization causes the port to be moved to the guest VLAN if configured.
When both MAB and guest VLAN are configured and no EAPOL packets are received on a port, the 802.1X state-machine is moved to a MAB state where it opens the port to listen to traffic and grab MAC addresses. The port remains in this state forever waiting to see a MAC on the port. A detected MAC address that fails authorization causes the port to be moved to the guest VLAN if configured.
While in a guest VLAN, a port is open to all traffic on the specified guest VLAN. Therefore, non-802.1X supplicants that normally would be authorized but are in guest VLAN due to the earlier detection of a device that failed authorization, would remain in the guest VLAN indefinitely. However, loss of link or the detection of an EAPOL on the wire causes a transition out of the guest VLAN and back to the default 802.1X mode.
•![]() Once a new MAC has been authenticated by MAB, the responsibility to limit access falls upon the 802.1X Authenticator (or port security) to secure the port. The 802.1X default host parameter is defined only for a single host. If the port is changed to multi-user host, port security must be employed to enforce the number of MAC addresses allowed thru this port.
Once a new MAC has been authenticated by MAB, the responsibility to limit access falls upon the 802.1X Authenticator (or port security) to secure the port. The 802.1X default host parameter is defined only for a single host. If the port is changed to multi-user host, port security must be employed to enforce the number of MAC addresses allowed thru this port.
•![]() Catalyst 4500 series switch supports MAB with VVID, with the restriction that the MAC address appears on a port data VLAN only. All IP phone MACs learned via CDP are allowed on voice VLANs.
Catalyst 4500 series switch supports MAB with VVID, with the restriction that the MAC address appears on a port data VLAN only. All IP phone MACs learned via CDP are allowed on voice VLANs.
•![]() MAB and VMPS are mutually exclusive because their functionality overlaps.
MAB and VMPS are mutually exclusive because their functionality overlaps.
Using 802.1X with Web-Based Authentication
The web-based authentication feature, known as Web Authentication Proxy, enables you to authenticate end users on host systems that do not run the IEEE 802.1X supplicant.
When configuring web-based authentication, note the following guidelines:
•![]() Fallback to web-based authentication is configured on switch ports in access mode. Ports in trunk mode are not supported.
Fallback to web-based authentication is configured on switch ports in access mode. Ports in trunk mode are not supported.
•![]() Fallback to web-based authentication is not supported on EtherChannels or EtherChannel members.
Fallback to web-based authentication is not supported on EtherChannels or EtherChannel members.
•![]() Although fallback to web-based authentication is an interface-specific configuration, the web-based authentication fallback behavior is defined in a global fallback profile. If the global fallback configuration changes, the new profile is not used until the next instance of authentication fallback.
Although fallback to web-based authentication is an interface-specific configuration, the web-based authentication fallback behavior is defined in a global fallback profile. If the global fallback configuration changes, the new profile is not used until the next instance of authentication fallback.
For detailed information on configuring web-based authentication, see Chapter 37 "Configuring Web-Based Authentication."
Using 802.1X with Inaccessible Authentication Bypass
When a switch cannot reach the configured RADIUS servers and clients (supplicants) cannot be authenticated, you can configure a switch to allow network access to hosts connected to critical ports that are enabled for Inaccessible Authentication Bypass.
When this feature is enabled, a switch monitors the status of the configured RADIUS servers. If no RADIUS servers are available, ports with Inaccessible Authentication Bypass enabled are authorized. You can specify a Inaccessible Authentication Bypass VLAN on a per-port basis.
Ports that were already authorized when RADIUS becomes unavailable are unaffected by Inaccessible Authentication Bypass.
When RADIUS becomes available, critically-authorized ports may be configured to automatically reauthenticate themselves.
For details on how to configure Inaccessible Authentication Bypass, see the "Configuring 802.1X with Inaccessible Authentication Bypass" section.
Using 802.1X with Unidirectional Controlled Port
Unidirectional Controlled Port is a combined hardware/software feature that allows dormant PCs to be "powered on" based on the receipt of a specific Ethernet frame, known as the magic packet. Generally, Unidirectional Controlled Port is used in environments where administrators plan to manage remote systems during off-hours, when it's likely that the systems have been powered down.
Use of Unidirectional Controlled Port with hosts attached through 802.1X ports presents a unique problem; when the host powers down, a 802.1X port becomes unauthorized. In this state, the port allows the receipt and transmission of EAPoL packets only. Therefore, the Unidirectional Controlled Port magic packet cannot reach the host; without powering up, the PC cannot authenticate and open the port.
Unidirectional Controlled Port solves this problem by allowing packets to be transmitted on unauthorized 802.1X ports.

Note ![]() Unidirectional Controlled Port only works when Spanning Tree Portfast is enabled on the port.
Unidirectional Controlled Port only works when Spanning Tree Portfast is enabled on the port.
For details on how to configure 802.1X with Unidirectional Controlled Port, see the "Configuring 802.1X with Unidirectional Controlled Port" section
Unidirectional State
A unidirectional controlled port is typically configured when a connected host might enter a sleeping mode or power-down state. When either occurs, the host does not exchange traffic with other devices in the network. A host connected to the unidirectional port cannot send traffic to the network; it can only receive traffic from other devices in the network.
When you configure a port as unidirectional (with the authentication control-direction in interface configuration command), the port will receive traffic in VLANs on that port, but it is not put into a spanning-tree forwarding state. If a VLAN contains only unauthenticated ports, any SVI on that VLAN will be in a down state, during which packets will not be routed into the VLAN. For the SVI to be up, and so enable packets to be routed into the VLAN, at least one port in the VLAN must either be authenticated or in the spanning-tree forwarding state..
Bidirectional State
When you configure a port as bidirectional with the authentication control-direction both interface configuration command (or the dot1x control-direction both interface configuration command for Cisco IOS Release 12.2(46) or earlier), the port is access-controlled in both directions. In this state, except for EAPOL packets, a switch port does not receive or send packets.
Using 802.1X with Authentication Failed VLAN Assignment
Authentication-failed VLAN assignment allows you to provide access for authentication failed users on a per-port basis . Authentication failed users are end hosts that are 802.1X- capable but do not have valid credentials in an authentication server or end hosts that do not give any username and password combination in the authentication pop-up window on the user side.
If a user fails the authentication process, that port is placed in the authentication-failed VLAN. The port remains in the authentication-failed VLAN until the reauthentication timer expires. When the reauthentication timer expires the switch starts sending the port re-authentication requests. If the port fails reauthentication it remains in the authentication-failed VLAN. If the port is successfully reauthenticated, the port is moved either to the VLAN sent by RADIUS server or to the newly authenticated ports configured VLAN; the location depends on whether RADIUS is configured to send VLAN information.

Note ![]() When enabling periodic reauthentication (see the "Enabling Periodic Reauthentication" section), only local reauthentication timer values are allowed. You cannot use a RADIUS server to assign the reauthentication timer value.
When enabling periodic reauthentication (see the "Enabling Periodic Reauthentication" section), only local reauthentication timer values are allowed. You cannot use a RADIUS server to assign the reauthentication timer value.
You can set the maximum number of authentication attempts that the authenticator sends before moving a port into the authentication-failed VLAN. The authenticator keeps a count of the failed authentication attempts for each port. A failed authentication attempt is either an empty response or an EAP failure. The authenticator tracks any mix of failed authentication attempts towards the authentication attempt count. After the maximum number of attempts is reached the port is placed in the authentication-failed VLAN until the reauthentication timer expires again.

Note ![]() RADIUS may send a response without an EAP packet in it when it does not support EAP, and sometimes third party RADIUS servers also send empty responses. When this happens, the authentication attempt counter is incremented.
RADIUS may send a response without an EAP packet in it when it does not support EAP, and sometimes third party RADIUS servers also send empty responses. When this happens, the authentication attempt counter is incremented.
For details on how to configure Authentication Failed VLAN Assignment, see the "Configuring 802.1X with Authentication Failed" section.
Usage Guidelines for Using Authentication Failed VLAN Assignment
•![]() You should enable reauthentication. The ports in authentication-failed VLANs do not receive reauthentication attempts if reauthentication is disabled. In order to start the reauthentication process the authentication-failed VLAN must receive a link down event or an EAP logoff event from the port. If the host is behind a hub, you may never get a link down event and may not detect the new host until the next reauthentication occurs. Therefore, it is recommended to have re-authentication enabled in that case.
You should enable reauthentication. The ports in authentication-failed VLANs do not receive reauthentication attempts if reauthentication is disabled. In order to start the reauthentication process the authentication-failed VLAN must receive a link down event or an EAP logoff event from the port. If the host is behind a hub, you may never get a link down event and may not detect the new host until the next reauthentication occurs. Therefore, it is recommended to have re-authentication enabled in that case.
•![]() EAP failure messages are not sent to the user. If the user failures authentication the port is moved to an authentication-failed VLAN and a EAP success message is sent to the user. Because the user is not notified of the authentication failure there may be confusion as to why there is restricted access to the network. A EAP Success message is sent for the following reasons:
EAP failure messages are not sent to the user. If the user failures authentication the port is moved to an authentication-failed VLAN and a EAP success message is sent to the user. Because the user is not notified of the authentication failure there may be confusion as to why there is restricted access to the network. A EAP Success message is sent for the following reasons:
–![]() If the EAP Success message is not sent, the user tries to authenticate every 60 seconds (by default) by sending an EAP-start message.
If the EAP Success message is not sent, the user tries to authenticate every 60 seconds (by default) by sending an EAP-start message.
–![]() In some cases, users have configured DHCP to EAP-Success and unless the user sees a success, DHCP does not work on the port.
In some cases, users have configured DHCP to EAP-Success and unless the user sees a success, DHCP does not work on the port.
•![]() Sometimes a user caches an incorrect username and password combination after receiving a EAP success message from the authenticator and reuses that information in every re-authentication. Until the user passes the correct username and password combination the port remains in the authentication-failed VLAN.
Sometimes a user caches an incorrect username and password combination after receiving a EAP success message from the authenticator and reuses that information in every re-authentication. Until the user passes the correct username and password combination the port remains in the authentication-failed VLAN.
•![]() When an authentication failed port is moved to an unauthorized state the authentication process is restarted. If you should fail the authentication process again the authenticator waits in the held state. After you have correctly reauthenticated all 802.1X ports are reinitialized and treated as normal 802.1X ports.
When an authentication failed port is moved to an unauthorized state the authentication process is restarted. If you should fail the authentication process again the authenticator waits in the held state. After you have correctly reauthenticated all 802.1X ports are reinitialized and treated as normal 802.1X ports.
•![]() When you reconfigure an authentication-failed VLAN to a different VLAN, any authentication failed ports are also moved and the ports stay in their current authorized state.
When you reconfigure an authentication-failed VLAN to a different VLAN, any authentication failed ports are also moved and the ports stay in their current authorized state.
•![]() When you shut down or remove an authentication-failed VLAN from the VLAN database, any authentication failed ports are immediately moved to an unauthorized state and the authentication process is restarted. The authenticator does not wait in a held state because the authentication-failed VLAN configuration still exists. While the authentication-failed VLAN is inactive, all authentication attempts are counted, and as soon as the VLAN becomes active the port is placed in the authentication-failed VLAN.
When you shut down or remove an authentication-failed VLAN from the VLAN database, any authentication failed ports are immediately moved to an unauthorized state and the authentication process is restarted. The authenticator does not wait in a held state because the authentication-failed VLAN configuration still exists. While the authentication-failed VLAN is inactive, all authentication attempts are counted, and as soon as the VLAN becomes active the port is placed in the authentication-failed VLAN.
•![]() If you reconfigure the maximum number of authentication failures allowed by the VLAN, the change takes affect after the reauthentication timer expires.
If you reconfigure the maximum number of authentication failures allowed by the VLAN, the change takes affect after the reauthentication timer expires.
•![]() Internal VLANs that are used for Layer 3 ports cannot be configured as authentication-failed VLANs.
Internal VLANs that are used for Layer 3 ports cannot be configured as authentication-failed VLANs.
•![]() The authentication-failed VLAN is supported only in single-host mode (the default port mode).
The authentication-failed VLAN is supported only in single-host mode (the default port mode).
•![]() When a port is placed in an authentication-failed VLAN the user's MAC address is added to the mac-address-table. If a new MAC address appears on the port, it is treated as a security violation.
When a port is placed in an authentication-failed VLAN the user's MAC address is added to the mac-address-table. If a new MAC address appears on the port, it is treated as a security violation.
•![]() When an authentication failed port is moved to an authentication-failed VLAN, the Catalyst 4500 series switch does not transmit a RADIUS-Account Start Message like it does for regular 802.1X authentication.
When an authentication failed port is moved to an authentication-failed VLAN, the Catalyst 4500 series switch does not transmit a RADIUS-Account Start Message like it does for regular 802.1X authentication.
Using 802.1X with Port Security
You can enable port security on an 802.1X port in either single- or multiple-host mode. (To do so, you must configure port security with the switchport port-security interface configuration command.) When you enable port security and 802.1X on a port, 802.1X authenticates the port, and port security manages the number of MAC addresses allowed on that port, including that of the client. Hence, 802.1X port with port security allows you to limit the number or group of clients that can access the network.
For information on selecting multi-host mode, see the "Resetting the 802.1X Configuration to the Default Values" section.
These examples describe the interaction between 802.1X and port security on a switch:
•![]() When a client is authenticated, and the port security table is not full, the client's MAC address is added to the port security list of secure hosts. The port then proceeds to come up normally.
When a client is authenticated, and the port security table is not full, the client's MAC address is added to the port security list of secure hosts. The port then proceeds to come up normally.
When a client is authenticated and manually configured for port security, it is guaranteed an entry in the secure host table (unless port security static aging has been enabled).
A security violation occurs if an additional host is learned on the port. The action taken depends on which feature (802.1X or port security) detects the security violation:
–![]() If 802.1X detects the violation, the action is to err-disable the port.
If 802.1X detects the violation, the action is to err-disable the port.
–![]() If port security detects the violation, the action is to shutdown or restrict the port (the action is configurable).
If port security detects the violation, the action is to shutdown or restrict the port (the action is configurable).
The following describes when port security and 802.1X security violations occur:
–![]() In single host mode, after the port is authorized, any MAC address received other than the client's causes a 802.1X security violation.
In single host mode, after the port is authorized, any MAC address received other than the client's causes a 802.1X security violation.
–![]() In single host mode, if installation of an 802.1X client's MAC address fails because port security has already reached its limit (due to a configured secure MAC addresses), a port security violation is triggered.
In single host mode, if installation of an 802.1X client's MAC address fails because port security has already reached its limit (due to a configured secure MAC addresses), a port security violation is triggered.
–![]() In multi host mode, once the port is authorized, any additional MAC addresses that cannot be installed because the port security has reached its limit triggers a port security violation.
In multi host mode, once the port is authorized, any additional MAC addresses that cannot be installed because the port security has reached its limit triggers a port security violation.
•![]() When an 802.1X client logs off, the port transitions back to an unauthenticated state, and all dynamic entries in the secure host table are cleared, including the entry for the client. Normal authentication then ensues.
When an 802.1X client logs off, the port transitions back to an unauthenticated state, and all dynamic entries in the secure host table are cleared, including the entry for the client. Normal authentication then ensues.
•![]() If you administratively shut down the port, the port becomes unauthenticated, and all dynamic entries are removed from the secure host table.
If you administratively shut down the port, the port becomes unauthenticated, and all dynamic entries are removed from the secure host table.
•![]() Only 802.1X can remove the client's MAC address from the port security table. Note that in multi host mode, with the exception of the client's MAC address, all MAC addresses that are learned by port security can be deleted using port security CLIs.
Only 802.1X can remove the client's MAC address from the port security table. Note that in multi host mode, with the exception of the client's MAC address, all MAC addresses that are learned by port security can be deleted using port security CLIs.
•![]() Whenever port security ages out a 802.1X client's MAC address, 802.1X attempts to reauthenticate the client. Only if the reauthentication succeeds is the client's MAC address be retained in the port security table.
Whenever port security ages out a 802.1X client's MAC address, 802.1X attempts to reauthenticate the client. Only if the reauthentication succeeds is the client's MAC address be retained in the port security table.
•![]() All of the 802.1X client's MAC addresses are tagged with (dot1x) when you display the port security table by using CLI.
All of the 802.1X client's MAC addresses are tagged with (dot1x) when you display the port security table by using CLI.
Using 802.1X Authentication with ACL Assignments and Redirect URLs
You can download per-host policies such as ACLs and redirect URLs to the switch from the RADIUS server during 802.1X or MAB authentication of the host. ACL download is also supported with web authentication after a fallback from 802.1X or MAB.
When the 802.1X host mode of the port is either single-host, MDA, or multiauthentication, the downloaded ACLs (DACLs) are modified to use the authenticated host's IP address as the source address. When the host mode is multiple-hosts, the source address is configured as ANY, and the downloaded ACLs or redirects apply to all devices on the port.
If no ACLs are provided during the authentication of a host, the static default ACL configured on the port is applied to the host. On a voice VLAN port, only the static default ACL of the port is applied to the phone.
Topics include:
•![]() Cisco Secure ACS and AV Pairs for URL-Redirect
Cisco Secure ACS and AV Pairs for URL-Redirect
•![]() ACLs
ACLs
For details on how to configure downloadable ACL and URL redirect, refer to the "Configuring 802.1X Authentication with ACL Assignments and Redirect URLs" section.
Cisco Secure ACS and AV Pairs for URL-Redirect
When downloadable ACL is enabled, Cisco Secure ACS provides AAA services through RADIUS.
You can set these Attribute-Value (AV) pairs on the Cisco Secure ACS with RADIUS cisco-av-pair vendor-specific attributes (VSAs).
CiscoSecure-Defined-ACL specifies the names of the DACLs on the Cisco Secure ACS. The switch receives the ACL name through the CiscoSecure-Defined-ACL AV pair in the format: #ACL#-IP-name-number
name is the ACL name. number is the version number (like 3f783768).
The Auth-Manager code verifies whether the access control entries (ACEs) of the specified downloadable ACL were previously downloaded. If not, the Auth-Manager code sends an AAA request with the downloadable ACL name as the username so that the ACEs are downloaded. The downloadable ACL is then created as a named ACL on the switch. This ACL has ACEs with a source address of any and does not have an implicit deny statement at the end. When the downloadable ACL is applied to an interface after authentication completes, the source address changes from any to the host source IP address depending on the host mode of the interface. The ACEs are prepended to the downloadable ACL applied to the switch interface to which the endpoint device is connected. If traffic matches the CiscoSecure-Defined-ACL ACEs, the appropriate actions are taken.
url-redirect and url-redirect-acl specify the local URL policy on the switch. The switches use these cisco-av-pair VSAs as follows:
–![]() url-redirect = <HTTP or HTTPS URL>
url-redirect = <HTTP or HTTPS URL>
–![]() url-redirect-acl = switch ACL name or number
url-redirect-acl = switch ACL name or number
These AV pairs enable the switch to intercept an HTTP or HTTPS request from the endpoint device and forward the client web browser to the specified redirect address from which the latest antivirus files can be downloaded. The url-redirect AV pair on the Cisco Secure ACS contains the URL to which the web browser is redirected. The url-redirect-acl AV pair contains the name or number of an ACL that specifies the HTTP or HTTPS traffic to be redirected. Traffic that matches a permit entry in the redirect ACL is redirected.

Note ![]() The redirect or default ACL must be defined on the switch.
The redirect or default ACL must be defined on the switch.
ACLs
If downloadable ACL is configured for a particular client on the authentication server, you must configure a default port ACL on a client-facing switch port.
If the default ACL is configured on the switch and the Cisco Secure ACS sends a host access policy to the switch, it applies the policy to traffic from the host connected to a switch port. If the policy does not apply, the switch applies the default ACL. If the Cisco Secure ACS sends the switch a downloadable ACL, this ACL takes precedence over the default ACL already configured on the switch port. However, if the switch receives a host access policy from the Cisco Secure ACS, but the default ACL is not configured, the authorization failure is declared.
For details on how to configure a downloadable policy, refer to the "Configuring a Downloadable Policy" section.
Using 802.1X with RADIUS-Provided Session Timeouts
You can specify whether a switch uses a locally configured or a RADIUS-provided reauthentication timeout. If the switch is configured to use the local timeout, it reauthenticates the host when the timer expires.
If the switch is configured to use the RADIUS-provided timeout, it scans the RADIUS Access-Accept message for the Session-Timeout and optional Termination-Action attributes. The switch uses the value of the Session-Timeout attribute to determine the duration of the session, and it uses the value of the Termination-Action attribute to determine the switch action when the session's timer expires.
If the Termination-Action attribute is present and its value is RADIUS-Request, the switch reauthenticates the host. If the Termination-Action attribute is not present, or its value is Default, the switch terminates the session.

Note ![]() The supplicant on the port detects that its session has been terminated and attempts to initiate a new session. Unless the authentication server treats this new session differently, the client may see only a brief interruption in network connectivity as the switch sets up a new session.
The supplicant on the port detects that its session has been terminated and attempts to initiate a new session. Unless the authentication server treats this new session differently, the client may see only a brief interruption in network connectivity as the switch sets up a new session.
If the switch is configured to use the RADIUS-supplied timeout, but the Access-Accept message does not include a Session-Timeout attribute, the switch never reauthenticates the supplicant. This behavior is consistent with Cisco's wireless access points.
For details on how to configure RADIUS-provided session timeouts, see the "Configuring RADIUS-Provided Session Timeouts" section.
Using 802.1X with Voice VLAN Ports
A voice VLAN port is a special access port associated with two VLAN identifiers:
•![]() Voice VLAN ID (VVID) to carry voice traffic to and from the IP phone. The VVID is used to configure the IP phone connected to the port.
Voice VLAN ID (VVID) to carry voice traffic to and from the IP phone. The VVID is used to configure the IP phone connected to the port.
•![]() Port VLAN ID (PVID) to carry the data traffic to and from the workstation connected to the switch through the IP phone. The PVID is the native VLAN of the port.
Port VLAN ID (PVID) to carry the data traffic to and from the workstation connected to the switch through the IP phone. The PVID is the native VLAN of the port.
Each port that you configure for a voice VLAN is associated with a VVID and a PVID. This configuration allows voice traffic and data traffic to be separated onto different VLANs.
A voice VLAN port becomes active when a link exists whether the port is AUTHORIZED or UNAUTHORIZED. All traffic exiting the voice VLAN is obtained correctly and appears in the MAC address table. Cisco IP phones do not relay CDP messages from other devices. So, if several Cisco IP phones are connected in a series, the switch recognizes only the one directly connected to it. When 802.1X is enabled on a voice VLAN port, the switch drops packets from unrecognized Cisco IP phones more than one hop away.
When 802.1X is enabled on a port, you cannot configure a PVID that is equal to a VVID. For more information about voice VLANs, see Chapter 34 "Configuring Voice Interfaces."
Observe the following feature interactions:
•![]() 802.1X VLAN assignment cannot assign to the port the same VLAN as the voice VLAN; otherwise, the 802.1X authentication fails. The same holds true for dynamic VLAN assignment.
802.1X VLAN assignment cannot assign to the port the same VLAN as the voice VLAN; otherwise, the 802.1X authentication fails. The same holds true for dynamic VLAN assignment.
•![]() 802.1X guest VLAN works with the 802.1X voice VLAN port feature. However, the guest VLAN cannot be the same as the voice VLAN.
802.1X guest VLAN works with the 802.1X voice VLAN port feature. However, the guest VLAN cannot be the same as the voice VLAN.
•![]() 802.1X port security works with the 802.1X voice VLAN port feature and is configured per port. Two MAC addresses must be configured: one for the Cisco IP phone MAC address on the VVID and one for the PC MAC address on PVID.
802.1X port security works with the 802.1X voice VLAN port feature and is configured per port. Two MAC addresses must be configured: one for the Cisco IP phone MAC address on the VVID and one for the PC MAC address on PVID.
However, you cannot use the 802.1X voice VLAN port feature with 802.1X port security's sticky MAC address configuration and statically configured MAC address configuration.
•![]() 802.1X accounting is unaffected by the 802.1X voice VLAN port feature.
802.1X accounting is unaffected by the 802.1X voice VLAN port feature.
•![]() When 802.1X is configured on a port, you cannot connect multiple IP phones to a
When 802.1X is configured on a port, you cannot connect multiple IP phones to a
Catalyst 4500 series switch through a hub.
•![]() Because voice VLANs cannot be configured as PVLAN host ports, and because only PVLANs can be assigned to PVLAN host ports, VLAN assignment cannot assign a PVLAN to a port with a voice VLAN configured.
Because voice VLANs cannot be configured as PVLAN host ports, and because only PVLANs can be assigned to PVLAN host ports, VLAN assignment cannot assign a PVLAN to a port with a voice VLAN configured.
For details on how to configure 802.1X with voice VLANs, see the "Configuring 802.1X with Voice VLAN" section.
Using Multiple Domain Authentication and Multiple Authentication
Multiple Domain Authentication (MDA) allows both a data device and a voice device, such as an IP phone (Cisco or 3rd party non-Cisco), to authenticate on the same switch port, which is divided into a data domain and a voice domain.
Multiple Authentication allows multiple data devices and a voice device. When a voice VLAN is configured on a multi-authentication port, the port can perform authentication in the voice domain as on an MDA port.
MDA does not enforce the order of device authentication. For best results, however, you should authenticate a voice device before you authenticate a data device on an MDA-enabled port.
Observe the following guidelines for configuring MDA:

Note ![]() The same guidelines also apply for Multiple Authentication when voice VLAN is configured.
The same guidelines also apply for Multiple Authentication when voice VLAN is configured.
•![]() It is highly recommended that you enable CoPP on an MDA-enabled port to protect against a DoS attack. Refer to Chapter 39 "Configuring Control Plane Policing."
It is highly recommended that you enable CoPP on an MDA-enabled port to protect against a DoS attack. Refer to Chapter 39 "Configuring Control Plane Policing."
•![]() To configure a switch port for MDA or Multiple Authentication, see the "Configuring Multiple Domain Authentication and Multiple Authorization" section.
To configure a switch port for MDA or Multiple Authentication, see the "Configuring Multiple Domain Authentication and Multiple Authorization" section.
•![]() You must configure the voice VLAN for the IP phone when the host mode is set to multidomain. For more information, see Chapter 34 "Configuring Voice Interfaces."
You must configure the voice VLAN for the IP phone when the host mode is set to multidomain. For more information, see Chapter 34 "Configuring Voice Interfaces."
•![]() To authorize a voice device, the AAA server must be configured to send a Cisco Attribute-Value (AV) pair attribute with a value of device-traffic-class=voice. Without this value, the switch treats the voice device as a data device.
To authorize a voice device, the AAA server must be configured to send a Cisco Attribute-Value (AV) pair attribute with a value of device-traffic-class=voice. Without this value, the switch treats the voice device as a data device.
•![]() The guest VLAN and restricted VLAN features only apply to the data devices on an MDA-enabled port. The switch treats a voice device that fails authorization as a data device.
The guest VLAN and restricted VLAN features only apply to the data devices on an MDA-enabled port. The switch treats a voice device that fails authorization as a data device.
•![]() If more than one device attempts authorization on either the voice or the data domain of a port, it is error disabled.
If more than one device attempts authorization on either the voice or the data domain of a port, it is error disabled.
•![]() Until a device is authorized, the port drops its traffic. Non-Cisco IP phones or voice devices are allowed into both the data and voice VLANs. The data VLAN allows the voice device to contact a DHCP server to obtain an IP address and acquire the voice VLAN information. After the voice device starts sending on the voice VLAN, its access to the data VLAN is blocked. A security violation may occur in MDA if the voice device continues to send traffic on the data VLAN.
Until a device is authorized, the port drops its traffic. Non-Cisco IP phones or voice devices are allowed into both the data and voice VLANs. The data VLAN allows the voice device to contact a DHCP server to obtain an IP address and acquire the voice VLAN information. After the voice device starts sending on the voice VLAN, its access to the data VLAN is blocked. A security violation may occur in MDA if the voice device continues to send traffic on the data VLAN.
•![]() MDA can use MAC authentication bypass as a fallback mechanism to allow the switch port to connect to devices that do not support 802.1X authentication. This is especially useful for 3rd-party phones without 802.1X supplicant. For more information, see the "Using 802.1X with MAC Authentication Bypass" section.
MDA can use MAC authentication bypass as a fallback mechanism to allow the switch port to connect to devices that do not support 802.1X authentication. This is especially useful for 3rd-party phones without 802.1X supplicant. For more information, see the "Using 802.1X with MAC Authentication Bypass" section.
•![]() When a data or a voice device is detected on a port, its MAC address is blocked until authorization succeeds. If the authorization fails, the MAC address remains blocked for 5 minutes.
When a data or a voice device is detected on a port, its MAC address is blocked until authorization succeeds. If the authorization fails, the MAC address remains blocked for 5 minutes.
•![]() If more than one device is detected on the data VLAN or more than one voice device is detected on the voice VLAN while a port is unauthorized, the port is error disabled.
If more than one device is detected on the data VLAN or more than one voice device is detected on the voice VLAN while a port is unauthorized, the port is error disabled.
•![]() When a port host mode is changed from single- or multihost to multidomain mode, an authorized data device remains authorized on the port. However, a Cisco IP phone that has been allowed on the port in the voice VLAN is automatically removed and must be reauthenticated on that port.
When a port host mode is changed from single- or multihost to multidomain mode, an authorized data device remains authorized on the port. However, a Cisco IP phone that has been allowed on the port in the voice VLAN is automatically removed and must be reauthenticated on that port.
•![]() Active fallback mechanisms such as guest VLAN and restricted VLAN remain configured after a port changes from single- or multihost mode to multidomain mode.
Active fallback mechanisms such as guest VLAN and restricted VLAN remain configured after a port changes from single- or multihost mode to multidomain mode.
•![]() Switching a port host mode from multidomain to single- or multihost mode removes all authorized devices from the port.
Switching a port host mode from multidomain to single- or multihost mode removes all authorized devices from the port.
•![]() If a data domain is authorized first and placed in the guest VLAN, non-802.1X-capable voice devices need to tag their packets on the voice VLAN to trigger authentication.
If a data domain is authorized first and placed in the guest VLAN, non-802.1X-capable voice devices need to tag their packets on the voice VLAN to trigger authentication.
•![]() We do not recommend per-user ACLs with an MDA-enabled port. An authorized device with a per-user ACL policy might impact traffic on both the voice and data VLANs of the port. If used, only one device on the port should enforce per-user ACLs.
We do not recommend per-user ACLs with an MDA-enabled port. An authorized device with a per-user ACL policy might impact traffic on both the voice and data VLANs of the port. If used, only one device on the port should enforce per-user ACLs.
How 802.1X Fails on a Port
802.1X may fail on a port in three ways: timeout, explicit failure, and protocol timeout.
Timeout—A switch attempts 802.1X at link up but the attached endpoint is not 802.1X-capable. After the configured number of retries and timeouts, the switch attempts the next authentication method if one is configured (like MAB). If MAB fails, the switch deploys the Guest VLAN (also called the no-response VLAN), if configured. The Guest VLAN is configured with the authentication event no-response interface command.
Explicit Failure—A switch and the endpoint perform the entire 802.1X authentication sequence and the result is an explicit failure (usually indicated by an Access-Reject from the RADIUS server to the switch and an EAP-Failure sent from the switch to the endpoint). In this case, the switch attempts MAB (if "authentication event failure action next-method" is configured) or deploy the AuthFail VLAN (if "authentication event failure action authorize vlan" is configured).
Protocol Timeout—A switch and the endpoint start the 802.1X authentication process but do not complete it. For example, the endpoint may send an 802.1X EAPoL-Start message and then stop responding to the switch (perhaps, because the endpoint lacks a credential or because it is waiting for end user to enter some information). In this case, the switch knows that the connected device is EAPoL-capable, so it will not deploy the Guest VLAN after timing out. Instead, it restarts authentication after a timeout. The switch continues to label the port as EAPoL-capable until a physical link down event is detected. To force the switch to deploy the Guest VLAN in the case of a protocol timeout, configure dot1x guest-vlan supplicant globally. If the port is configured for hostmode multi-domain authentication, the switch behaves as if dot1x guest-vlan supplicant is configured.
Supported Topologies
The 802.1X port-based authentication supports two topologies:
•![]() Point-to-point
Point-to-point
•![]() Wireless LAN
Wireless LAN
In a point-to-point configuration (see Figure 36-1), only one client can be connected to the 802.1X-enabled switch port when the multi-host mode is not enabled (the default). The switch detects the client when the port link state changes to the up state. If a client leaves or is replaced with another client, the switch changes the port link state to down, and the port returns to the unauthorized state.
For 802.1X port-based authentication in a wireless LAN (Figure 36-7), you must configure the 802.1X port as a multiple-host port that is authorized as a wireless access point once the client is authenticated. (See the "Resetting the 802.1X Configuration to the Default Values" section.) When the port is authorized, all other hosts that are indirectly attached to the port are granted access to the network. If the port becomes unauthorized (reauthentication fails or an EAPOL-logoff message is received), the switch denies access to the network for all wireless access point-attached clients. In this topology, the wireless access point is responsible for authenticating clients attached to it, and the wireless access point acts as a client to the switch.
Figure 36-7 Wireless LAN Example

Configuring 802.1X Port-Based Authentication

Note ![]() Although we recommend using the authentication commands described in this section, legacy 802.1X commands in 12.2(46)SG and earlier releases are still accepted.
Although we recommend using the authentication commands described in this section, legacy 802.1X commands in 12.2(46)SG and earlier releases are still accepted.
To configure 802.1X, follow this procedure:
Step 1 ![]() Enable 802.1X authentication. See the "Enabling 802.1X Authentication" section.
Enable 802.1X authentication. See the "Enabling 802.1X Authentication" section.
Step 2 ![]() Configure switch to RADIUS server communication. See the "Configuring Switch-to-RADIUS-Server Communication" section.
Configure switch to RADIUS server communication. See the "Configuring Switch-to-RADIUS-Server Communication" section.
Step 3 ![]() Adjust the 802.1X timer values. See the "Changing the Quiet Period" section.
Adjust the 802.1X timer values. See the "Changing the Quiet Period" section.
Step 4 ![]() Configure optional features. See the "Configuring RADIUS-Provided Session Timeouts" section.
Configure optional features. See the "Configuring RADIUS-Provided Session Timeouts" section.
These sections describe how to configure 802.1X:
•![]() 802.1X Configuration Guidelines
802.1X Configuration Guidelines
•![]() Enabling 802.1X Authentication (required)
Enabling 802.1X Authentication (required)
•![]() Configuring Switch-to-RADIUS-Server Communication (required)
Configuring Switch-to-RADIUS-Server Communication (required)
•![]() Configuring Multiple Domain Authentication and Multiple Authorization
Configuring Multiple Domain Authentication and Multiple Authorization
•![]() Configuring 802.1X Authentication with ACL Assignments and Redirect URLs
Configuring 802.1X Authentication with ACL Assignments and Redirect URLs
•![]() Configuring 802.1X Authentication with Per-User ACL and Filter-ID ACL
Configuring 802.1X Authentication with Per-User ACL and Filter-ID ACL
•![]() Configuring RADIUS-Provided Session Timeouts (optional)
Configuring RADIUS-Provided Session Timeouts (optional)
•![]() Configuring 802.1X with Guest VLANs (optional)
Configuring 802.1X with Guest VLANs (optional)
•![]() Configuring 802.1X with MAC Authentication Bypass (optional)
Configuring 802.1X with MAC Authentication Bypass (optional)
•![]() Configuring 802.1X with Inaccessible Authentication Bypass (optional)
Configuring 802.1X with Inaccessible Authentication Bypass (optional)
•![]() Configuring 802.1X with Unidirectional Controlled Port (optional)
Configuring 802.1X with Unidirectional Controlled Port (optional)
•![]() Configuring 802.1X with Authentication Failed (optional)
Configuring 802.1X with Authentication Failed (optional)
•![]() Configuring 802.1X with Voice VLAN (optional)
Configuring 802.1X with Voice VLAN (optional)
•![]() Configuring 802.1X with VLAN Assignment
Configuring 802.1X with VLAN Assignment
•![]() Enabling Fallback Authentication
Enabling Fallback Authentication
•![]() Enabling Periodic Reauthentication (optional)
Enabling Periodic Reauthentication (optional)
•![]() Enabling Multiple Hosts (optional
Enabling Multiple Hosts (optional
•![]() Changing the Quiet Period (optional)
Changing the Quiet Period (optional)
•![]() Changing the Switch-to-Client Retransmission Time (optional)
Changing the Switch-to-Client Retransmission Time (optional)
•![]() Setting the Switch-to-Client Frame-Retransmission Number (optional)
Setting the Switch-to-Client Frame-Retransmission Number (optional)
•![]() Manually Reauthenticating a Client Connected to a Port (optional)
Manually Reauthenticating a Client Connected to a Port (optional)
•![]() Initializing the 802.1X Authentication State
Initializing the 802.1X Authentication State
•![]() Removing 802.1X Client Information
Removing 802.1X Client Information
•![]() Resetting the 802.1X Configuration to the Default Values (optional)
Resetting the 802.1X Configuration to the Default Values (optional)
Default 802.1X Configuration
Table 36-1 shows the default 802.1X configuration.
802.1X Configuration Guidelines
This section describes the guidelines for configuring 802.1X authentication:
•![]() The 802.1X protocol is supported only on Layer 2 static access, PVLAN host ports, and Layer 3 routed ports. You cannot configure 802.1X for any other port modes.
The 802.1X protocol is supported only on Layer 2 static access, PVLAN host ports, and Layer 3 routed ports. You cannot configure 802.1X for any other port modes.
•![]() If you are planning to use VLAN assignment, be aware that the features use general AAA commands. For information on how to configure AAA, refer to the "Enabling 802.1X Authentication" section. Alternatively, you can refer to the Cisco IOS security documentation:
If you are planning to use VLAN assignment, be aware that the features use general AAA commands. For information on how to configure AAA, refer to the "Enabling 802.1X Authentication" section. Alternatively, you can refer to the Cisco IOS security documentation:
–![]() http://www.cisco.com/en/US/products/ps6586/products_ios_technology_home.html
http://www.cisco.com/en/US/products/ps6586/products_ios_technology_home.html
Enabling 802.1X Authentication
To enable 802.1X port-based authentication, you first must enable 802.1X globally on your switch, then enable AAA and specify the authentication method list. A method list describes the sequence and authentication methods that must be queried to authenticate a user.
The software uses the first method listed in the method list to authenticate users; if that method fails to respond, the software selects the next authentication method in the list. This process continues until there is successful communication with a listed authentication method or until all defined methods are exhausted. If authentication fails at any point in this cycle, the authentication process stops, and no other authentication methods are attempted.

Note ![]() To allow VLAN assignment, you must enable AAA authorization to configure the switch for all network-related service requests.
To allow VLAN assignment, you must enable AAA authorization to configure the switch for all network-related service requests.
To configure 802.1X port-based authentication, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# dot1x system-auth-control |
Enables 802.1X on your switch. To disable 802.1X globally on the switch, use the |
Step 3 |
Switch(config)# aaa new-model |
Enables AAA. To disable AAA, use the no aaa new-model command. |
Step 4 |
Switch(config)# aaa authentication dot1x {default} method1 [method2...] |
Creates an 802.1X AAA authentication method list. To create a default list that is used when a named list is not specified in the authentication command, use the default keyword followed by the methods that are to be used in default situations. The default method list is automatically applied to all interfaces. Enter at least one of these keywords: • • To disable 802.1X AAA authentication, use the |
Step 5 |
Switch(config)# aaa authorization
network {default} group radius
|
(Optional) Configures the switch for user RADIUS authorization for all network-related service requests, such as VLAN assignment. |
Step 6 |
Switch(config)# interface interface-id |
Enters interface configuration mode and specifies the interface to be enabled for 802.1X authentication. |
Step 7 |
Switch(config-if)# switchport mode
access
|
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 8 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 9 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 10 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 11 |
Switch # show dot1x interface interface-id details |
Verifies your entries. Check the PortControl row in the 802.1X port summary section of this display. The PortControl value is set to auto. |
Step 12 |
Switch# show running-config |
Verifies your entries. |
Step 13 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |

Note ![]() Enabling Spanning Tree PortFast ensures that a port comes up immediately after authorization.
Enabling Spanning Tree PortFast ensures that a port comes up immediately after authorization.

Note ![]() Whenever you configure any 802.1X parameter on a port, a dot1x authenticator is automatically created on the port. As a result dot1x pae authenticator appears in the configuration. This is to ensure that dot1x authentication still works on legacy configurations without manual intervention. This is likely to change in future releases.
Whenever you configure any 802.1X parameter on a port, a dot1x authenticator is automatically created on the port. As a result dot1x pae authenticator appears in the configuration. This is to ensure that dot1x authentication still works on legacy configurations without manual intervention. This is likely to change in future releases.
This example shows how to enable 802.1X and AAA on Fast Ethernet port 2/1, and how to verify the configuration:
Switch# configure terminal
Switch(config)# dot1x system-auth-control
Switch(config)# aaa new-model
Switch(config)# aaa authentication dot1x default group radius
Switch(config)# interface fastethernet2/1
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch# show authentication sessions interface f9/2
Interface: FastEthernet9/2
MAC Address: 0007.e95d.83c4
IP Address: Unknown
Status: Running
Domain: UNKNOWN
Oper host mode: single-host
Oper control dir: both
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A050B160000009505106398
Acct Session ID: 0x0000009B
Handle: 0x0D000095
Runnable methods list:
Method State
dot1x Running
mab Not run
The following example illustrates when a port is authorized:
Switch# show authentication sessions int G4/5
Interface: GigabitEthernet4/5
MAC Address: 0015.e981.0531
IP Address: Unknown
User-Name: ctssxp
Status: Authz Success
Domain: DATA
Oper host mode: single-host
Oper control dir: both
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A053F0F00000004041E6B0C
Acct Session ID: 0x00000021
Handle: 0x2C000004
Runnable methods list:
Method State
dot1x Authc Success
Switch# show dot1x interface G4/5 details
Dot1x Info for GigabitEthernet4/5
-----------------------------------
PAE = AUTHENTICATOR
PortControl = AUTO
ControlDirection = Both
HostMode = SINGLE_HOST
QuietPeriod = 60
ServerTimeout = 0
SuppTimeout = 30
ReAuthMax = 2
MaxReq = 2
TxPeriod = 30
Dot1x Authenticator Client List
-------------------------------
Supplicant = 0015.e981.0531
Session ID = 0A053F0F00000004041E6B0C
Auth SM State = AUTHENTICATED
Auth BEND SM State = IDLE
Port Status = AUTHORIZED
Configuring Switch-to-RADIUS-Server Communication
A RADIUS security server is identified by its host name or IP address, host name and specific UDP port number, or IP address and specific UDP port numbers. The combination of the IP address and UDP port number creates a unique identifier, which enables RADIUS requests to be sent to multiple UDP ports on a server at the same IP address. If two different host entries on the same RADIUS server are configured for the same service—for example, authentication—the second host entry configured acts as the fail-over backup to the first one. The RADIUS host entries are tried in the order they were configured.
To configure the RADIUS server parameters on the switch, perform this task:
This example shows how to specify the server with IP address 172.120.39.46 as the RADIUS server. The first command specifies port 1612 as the authorization port, sets the encryption key to rad123.
The second command dictates that key matches are performed on the RADIUS server:
Switch# configure terminal
Switch(config)# radius-server host 172.l20.39.46 auth-port 1612 key rad123
Switch(config)# ip radius source-interface g3/2
Switch(config)# end
Switch#
You can globally configure the timeout, retransmission, and encryption key values for all RADIUS servers by using the radius-server host global configuration command. If you want to configure these options on a per-server basis, use the radius-server timeout, radius-server retransmit, and the radius-server key global configuration commands.
You also need to create a AAA client setting on the RADIUS server. These settings include the IP address of the switch and the key string to be shared by both the server and the switch.
Configuring Multiple Domain Authentication and Multiple Authorization
To configure MDA and Multiple Authentication, perform this task.
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# radius-server vsa
send authentication
|
Configures the network access server to recognize and use vendor-specific attributes (VSAs). |
Step 3 |
Switch(config)# interface interface-id |
Specifies the port to which multiple hosts are indirectly attached, and enters interface configuration mode. |
Step 4 |
Switch(config-if)# [no]
authentication host-mode
{single-host | multi-host |
multi-domain} | multi-auth}
|
The keywords allow the following: • • • Note • Ensure that the dot1x port-control interface configuration command is set to auto for the specified interface. To disable multiple hosts on the port, use the |
Step 5 |
Switch(config-if)# switchport voice vlan vlan-id |
(Optional) Configures the voice VLAN. |
Step 6 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 7 |
Switch# show dot1x interface interface-id [detail] |
Verifies your entries. |
Step 8 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to enable 802.1X authentication and to allow multiple hosts:
Switch(config)# interface gigabitethernet2/1
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication host-mode multi-host
Switch(config-if)# end
This example shows how to enable MDA and to allow both a host and a 802.1X voice device (a Cisco or third-party phone with 802.1X supplicant) on the port:
Switch# conf terminal
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# interface FastEthernet3/1
Switch(config-if)# shut
Switch(config-if)# switchport access vlan 12
Switch(config-if)# switchport mode access
Switch(config-if)# switchport voice vlan 10
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication host-mode multi-domain
Switch(config-if)# no shut
Switch(config-if)# end
This example shows how to enable MDA and to allow both a host and a non-802.1X voice device on the port:
Switch# conf t
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# interface FastEthernet3/1
Switch(config-if)# shut
Switch(config-if)# switchport access vlan 12
Switch(config-if)# switchport mode access
Switch(config-if)# switchport voice vlan 10
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication host-mode multi-domain
Switch(config-if)# mab eap
Switch(config-if)# no shut
Switch(config-if)# end
This example shows how to verify the dot1x MDA settings on interface FastEthernet3/1:
Switch# show dot1x interface FastEthernet3/1 detail
Dot1x Info for FastEthernet3/1
-----------------------------------
PAE = AUTHENTICATOR
PortControl = AUTO
ControlDirection = Both
HostMode = MULTI_DOMAIN
ReAuthentication = Disabled
QuietPeriod = 60
ServerTimeout = 30
SuppTimeout = 30
ReAuthPeriod = 3600 (Locally configured)
ReAuthMax = 2
MaxReq = 2
TxPeriod = 30
RateLimitPeriod = 0
Dot1x Authenticator Client List
-------------------------------
Domain = DATA
Supplicant = 0000.0000.ab01
Auth SM State = AUTHENTICATED
Auth BEND SM Stat = IDLE
Port Status = AUTHORIZED
Authentication Method = Dot1x
Authorized By = Authentication Server
Vlan Policy = 12
Domain = VOICE
Supplicant = 0060.b057.4687
Auth SM State = AUTHENTICATED
Auth BEND SM Stat = IDLE
Port Status = AUTHORIZED
Authentication Method = Dot1x
Authorized By = Authentication Server
Switch#
This example shows how to enable MDA and to authentication of multiple hosts and a voice device on an IEEE 802.1x-authorized port:
Switch# conf t
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# interface FastEthernet3/1
Switch(config-if)# shut
Switch(config-if)# switchport access vlan 12
Switch(config-if)# switchport mode access
Switch(config-if)# switchport voice vlan 10
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication host-mode multi-auth
Switch(config-if)# map eap
Switch(config-if)# no shut
Switch(config-if)# end
Configuring 802.1X Authentication with ACL Assignments and Redirect URLs
Topics include:
•![]() Configuring a Downloadable Policy
Configuring a Downloadable Policy
Downloadable ACL
The Downloadable ACL feature enables you to download device specific authorization policies from the authentication server. These policies activate after authentication succeeds for the respective client and the client's IP address has been populated in the IP device tracking table. (Downloadable ACL is applied on the port, once the port is authenticated and the IP device tracking table has the host IP address entry).
The following sections illustrates the configuration needed to complement the related authentication (802.1X or MAB) configuration. (No unique configuration is required on the switch. All of the configuration is on the ACS.) After authentication succeeds, enter the show ip access-list command to display the downloadable ACLs.
Switch Configuration
Step 1 ![]() Configure the IP device tracking table.
Configure the IP device tracking table.
Switch(config)# ip device tracking
Step 2 ![]() Configure RADIUS VSA to forward authentication.
Configure RADIUS VSA to forward authentication.
Switch(config)# radius-server vsa send authentication
Step 3 ![]() Configure Static ACL (PACL) for the interface.
Configure Static ACL (PACL) for the interface.
Switch(config)# int g2/9
Switch(config-if)# ip access-group pacl-4 in
Sample Interface Configuration
Switch# show running-configuration interface g2/9
Building configuration...
Current configuration : 617 bytes
!
interface GigabitEthernet2/9
switchport
switchport access vlan 29
switchport mode access
switchport voice vlan 1234
access-group mode prefer port
ip access-group pacl-4 in
speed 100
duplex full
authentication event fail action authorize vlan 111
authentication event server dead action authorize vlan 333
authentication event server alive action reinitialize
authentication host-mode multi-auth
authentication order dot1x
authentication port-control auto
authentication timer restart 100
authentication timer reauthenticate 20
authentication timer inactivity 200
mab eap
dot1x pae authenticator
end
Switch#
Switch# show ip access-list pacl-4
10 permit ip host 1.1.1.1 host 2.2.2.2
20 permit icmp host 1.1.1.1 host 2.2.2.2
Switch#
Debug Commands for DACL
The IP device tracking table contains the host IP address learned through ARP or DHCP.
The following commands displays the constraints on the IP device tracking table:
Switch# show ip device tracking all
IP Device Tracking = Enabled
IP Device Tracking Probe Count = 3
IP Device Tracking Probe Interval = 30
--------------------------------------------------------------
IP Address MAC Address Interface STATE
--------------------------------------------------------------
50.0.0.12 0015.60a4.5e84 GigabitEthernet2/9 ACTIVE
The following command shows that the EPM (Policy Enforced Module) session contains the DACL downloaded from ACS:
Switch# show epm session ip 50.0.0.12
Admission feature : DOT1X
AAA Policies :
ACS ACL : xACSACLx-IP-auth-48b79b6e
The following command reveals the contents of the downloadable ACL:
Switch# show ip accesslists xACSACLx-IP-auth-48b79b6e
Extended IP access list xACSACLx-IP-auth-48b79b6e (per-user)
10 permit udp any any
Switch(config)#
Cisco ACS Configuration for DACL

Note ![]() Only Cisco ACS supports DACL.
Only Cisco ACS supports DACL.
Follow these steps to ensure correct functioning of the ACS configuration required for DACL:
Step 1 ![]() Configure a downloadable IP ACL on the window that appears when you select
Configure a downloadable IP ACL on the window that appears when you select
Radius Shared Profile > Downloadable IP ACL Content:
Figure 36-8 Shared Profile Components
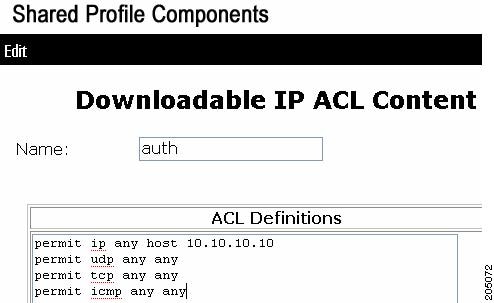
Step 2 ![]() Attach this DACL with the USER on the window that appears when you select User > DACLs:
Attach this DACL with the USER on the window that appears when you select User > DACLs:
Figure 36-9 Downloadable ACLs

URL-Redirect
This configuration consists of two configurations: one on ACS, and one on the switch.
ACS configuration
To configure two Cisco-AV pairs, add the following statements under the user or group Cisco IOS/PIX 6x RADIUS attributes:
url-redirect-acl=urlacl
url-redirect=http://www.cisco.com

Note ![]() A default port ACL must be configured on the interface.
A default port ACL must be configured on the interface.
Switch configuration
To configure the switch for URL redirect, do the following:
Step 1 ![]() Configure the IP device tracking table.
Configure the IP device tracking table.
Switch(config)# ip device tracking
Step 2 ![]() Configure RADIUS with the send authentication command.
Configure RADIUS with the send authentication command.
Switch(config)# radius-server vsa send authentication
Step 3 ![]() Configure the URL redirect ACL (URLACL).
Configure the URL redirect ACL (URLACL).
Switch# ip access-list urlacl
10 permit tcp any any
Switch#
Step 4 ![]() Configure static ACL (PACL) for the interface.
Configure static ACL (PACL) for the interface.
Switch(config)# int g2/9
Switch(config-if)# ip access-group pacl-4 in
Sample Interface Configuration
Switch# show running-configuration int g2/9
Building configuration...
Current configuration : 617 bytes
!
interface GigabitEthernet2/9
switchport
switchport access vlan 29
switchport mode access
switchport voice vlan 1234
access-group mode prefer port
ip access-group pacl-4 in
speed 100
duplex full
authentication event fail action authorize vlan 111
authentication event server dead action authorize vlan 333
authentication event server alive action reinitialize
authentication host-mode multi-auth
authentication order dot1x
authentication port-control auto
authentication timer restart 100
authentication timer reauthenticate 20
authentication timer inactivity 200
mab
dot1x pae authenticator
end
Switch#
Switch# show access-list pacl-4
10 permit ip host 1.1.1.1 host 2.2.2.2
20 permit icmp host 1.1.1.1 host 2.2.2.2
Switch#
Verify URL-redirect with the following commands.
The show ip device tracking command illustrates the constraints on the IP device tracking table:
Switch(config)# show ip device tracking all
IP Device Tracking = Enabled
IP Device Tracking Probe Count = 3
IP Device Tracking Probe Interval = 30
--------------------------------------------------------------
IP Address MAC Address Interface STATE
--------------------------------------------------------------
50.0.0.12 0015.60a4.5e84 GigabitEthernet2/9 ACTIVE
The show epm session ip command displays the EPM session table for a particular host. Observe the
URL- redirect-acl and URL-redirect URL information that downloads from the ACS.
Switch# show epm session ip 50.0.0.12
Admission feature : DOT1X
AAA Policies :
URL Redirect ACL : urlacl
URL Redirect : http://www.cisco.com
For more information about AV pairs that are supported by Cisco IOS software, see the
ACS configuration and command reference documentation about the software releases running on the AAA clients.
Guidelines and Restrictions for DACL and URL Redirect
For downloadable ACL or URL redirect, the ACL source must be ANY
(permit TCP ANY host 1.1.1.1 eq 80 or permit TCP ANY host 1.1.1.1 eq 443).
Configuring a Downloadable Policy
To configure downloadable policies, perform this task:
The following example illustrates how to configure a switch for downloadable policy:
Switch# config terminal
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# aaa new-model
Switch(config)# aaa authorization network default local
Switch(config)# ip device tracking
Switch(config)# ip access-list extended default_acl
Switch(config-ext-nacl)# permit ip any any
Switch(config-ext-nacl)# exit
Switch(config)# radius-server vsa send authentication
Switch(config)# int fastEthernet 2/13
Switch(config-if)# ip access-group default_acl in
Switch(config-if)# exit
Configuring 802.1X Authentication with Per-User ACL and Filter-ID ACL
Topics include:
•![]() Per-User ACL and Filter-ID ACL
Per-User ACL and Filter-ID ACL
•![]() Configuring a Per-User ACL and Filter-ID ACL
Configuring a Per-User ACL and Filter-ID ACL
Per-User ACL and Filter-ID ACL
Prior to Cisco IOS Release 12.2(52)SG, the Cat4K platform only supported downloadable ACLs, which work with the Cisco ACS server but not with third-party AAA servers. With
Cisco IOS Release 12.2(52)SG, the Catalyst 4500 switch offers the Filter-ID/Per-user-acl enhancement(s), which allow ACL policy enforcement using a third-party AAA server.
The Filter-ID feature provides the following capabilities:
Filter-ID option allows an administrator to define the ACL name on the AAA server using IETF standard Radius attribute. The ACL itself must be pre-configured locally on the switch.
The Per-user-acl feature provides the following capabilities:
Per-user ACL allows an administrator to define the per-user ACL on the AAA server using Cisco Radius AV pairs. This allows third-party AAA server to interoperate by loading Cisco Radius dictionary. Cisco radius dictionary has Cisco Radius AV pairs configured as a VSA.

Note ![]() The Radius Vendor-specific attributes (VSAs) allow vendors to support their own proprietary RADIUS attributes that are not included in standard radius attributes.
The Radius Vendor-specific attributes (VSAs) allow vendors to support their own proprietary RADIUS attributes that are not included in standard radius attributes.
Switch Configuration
Step 1 ![]() Configure the IP device tracking table.
Configure the IP device tracking table.
Switch(config)# ip device tracking
Step 2 ![]() Configure Static ACL (PACL) for the interface.
Configure Static ACL (PACL) for the interface.
Switch(config)# int g2/9
Switch(config-if)# ip access-group pacl-4 in
Sample Interface Configuration
Switch# show running-configuration interface g2/9
Building configuration...
Current configuration : 617 bytes
!
interface GigabitEthernet2/9
switchport
switchport access vlan 29
switchport mode access
switchport voice vlan 1234
access-group mode prefer port
ip access-group pacl-4 in
speed 100
duplex full
authentication event fail action authorize vlan 111
authentication event server dead action authorize vlan 333
authentication event server alive action reinitialize
authentication host-mode multi-auth
authentication order dot1x
authentication port-control auto
authentication timer restart 100
authentication timer reauthenticate 20
authentication timer inactivity 200
mab eap
dot1x pae authenticator
end
Switch#
Switch# show ip access-list pacl-4
10 permit ip host 1.1.1.1 host 2.2.2.2
20 permit icmp host 1.1.1.1 host 2.2.2.2
Switch#
Per-User-Acl configuration in ACS
In the Group/User Setting page, scroll down to the Cisco IOS/PIX 6.x RADIUS Attributes section. Select the box next to [009\001 cisco-av-pair] and enter the elements of the per-user ACL. Per-user ACLS take this format:
<protocol>:inacl#<sequence number>=<ACE>
<protocol> can be either "ip" for IP-based ACLs or "mac" for MAC-based ACLs.
In the following example, members of the group you are configuring are denied all access to the 10.100.60.0 subnet, denied http access to the server at 10.100.10.116, and permitted everywhere else.
Figure 36-10 Define the ACEs for the per-user ACL


Note ![]() outbound ACLs (outacl) are not supported.
outbound ACLs (outacl) are not supported.
Filter-Id configuration in ACS:
In the Group/User Setting page, scroll down to the " IETF RADIUS Attributes" section. Select the box next to [011] Filter-Id and enter the ACL to apply for members of this group (Figure 36-11).
The Filter-Id takes this format:
<ACL>.in
<ACL> is the number of the ACL that was configured on the switch in the previous step
Figure 36-11 Configuring the Filter-ID Attribute


Note ![]() Outbound ACLs (e.g. "100.out") are not supported.
Outbound ACLs (e.g. "100.out") are not supported.
Debug Commands for Per-User ACL and Filter-ID ACL
The IP device tracking table contains the host IP address learned through ARP or DHCP. The following command displays the constraints on the IP device tracking table:
Switch# show ip device tracking all
IP Device Tracking = Enabled
IP Device Tracking Probe Count = 3
IP Device Tracking Probe Interval = 30
--------------------------------------------------------------
IP Address MAC Address Interface STATE
--------------------------------------------------------------
50.0.0.12 0015.60a4.5e84 GigabitEthernet2/9 ACTIVE
The following command shows that the EPM (Policy Enforced Module) session contains the per-user-acl from ACS:
Switch# show epm session ip 50.0.0.12
Admission feature : DOT1X
AAA Policies :
Per-User ACL : deny ip any host 20.20.10.10
The following command reveals the contents of the per-user-acl (note that per-user-acl are shown above the default port ACL configured on the interface, 151 is the default port ACL in the following example):
Switch# show access-list
Extended IP access list 151
deny ip host 20.20.0.3 host 20.20.10.10
10 permit ip any any (57 estimate matches)
The following commands reveals the number of sessions and the corresponding client ip addresses,
Switch# show epm session summary
EPM Session Information
-----------------------
Total sessions seen so far : 1
Total active sessions : 1
Session IP Address :
-------------------
50.0.0.12
The following command shows that the EPM (Policy Enforced Module) session contains the per-user-acl(both ip and mac acl from ACS):
Switch# show epm session ip 50.0.0.12
Admission feature : DOT1X
AAA Policies :
Per-User ACL : deny ip any host 20.20.10.10
Per-User ACL : deny any host 0000.AAAA.AAAA
The following command reveals the contents of the per-user-acl (note that per-user-acl are shown above the default port acl configured on the interface, 151 is the default port acl in the example below):
Switch# show access-list
Extended IP access list 151
deny ip host 20.20.0.3 host 20.20.10.10
10 permit ip any any (57 estimate matches)
..
..
..(check for the mac access-list created)..
..
Extended MAC access list PerUser_MAC_ACL-589079192 (per-user)
deny any host 0000.aaaa.aaaa
..
The following command shows that the EPM (Policy Enforced Module) session contains the Filter-Id 155 from ACS:

Note ![]() The 156 IP extended acl is to be pre-configured on the switch, so that the policy enforcement can happen.
The 156 IP extended acl is to be pre-configured on the switch, so that the policy enforcement can happen.
Switch# show ip access-list 156
Extended IP access list 156
10 deny ip any host 155.155.155.156
20 deny ip any 156.100.60.0 0.0.0.255
30 deny tcp any host 156.100.10.116 eq www
Switch# show epm session ip 50.0.0.12
Admission feature : DOT1X
AAA Policies :
Filter-Id : 155
The following command reveals the contents of the Filter-Id applied on the interface:
Switch# show ip access-list int <gi6/3>
Switch# show ip access-list interface gi6/3
deny ip host 20.20.0.2 host 155.155.155.156
deny ip host 20.20.0.2 156.100.60.0 0.0.0.255
deny tcp host 20.20.0.2 host 156.100.10.116 eq www
Guidelines and Restrictions for Per-User-ACL and Filter-ID ACL
For Per-User-ACL and Filter-ID ACL, the ACL source must be ANY
(permit TCP ANY host 1.1.1.1 eq 80 or permit TCP ANY host 1.1.1.1 eq 443).
Configuring a Per-User ACL and Filter-ID ACL
To configure Per-User-ACL and Filter-ID ACL, perform this task:
The following example illustrates how to configure a switch for downloadable policy:
Switch# config terminal
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# aaa new-model
Switch(config)# aaa authorization network default local
Switch(config)# ip device tracking
Switch(config)# ip access-list extended default_acl
Switch(config-ext-nacl)# permit ip any any
Switch(config-ext-nacl)# exit
Switch(config)# int fastEthernet 2/13
Switch(config-if)# ip access-group default_acl in
Switch(config-if)# exit
Configuring RADIUS-Provided Session Timeouts
You can configure the Catalyst 4500 series switch to use a RADIUS-provided reauthentication timeout.
To configure RADIUS-provided timeouts, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode. |
Step 3 |
Switch(config-if)# switchport mode
access
|
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# authentication
timer reauthenticate {interface |
server}
|
Sets the re-authentication period (seconds). |
Step 6 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 7 |
Switch# show dot1x interface interface-id details |
Verifies your entries. |
Step 8 |
Switch # copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to configure a switch to derive the re-authentication period from the server and to verify the configuration:
Switch# configure terminal
Switch(config)# interface f7/1
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication timer reauthenticate server
Switch(config-if)# end
Switch# show dot1x interface f7/1 det
Dot1x Info for FastEthernet7/11
-----------------------------------
PAE = AUTHENTICATOR
PortControl = FORCE_AUTHORIZED
ControlDirection = Both
HostMode = SINGLE_HOST
ReAuthentication = Disabled
QuietPeriod = 60
ServerTimeout = 30
SuppTimeout = 30
ReAuthPeriod = (From Authentication Server)
ReAuthMax = 2
MaxReq = 2
TxPeriod = 30
RateLimitPeriod = 0
Dot1x Authenticator Client List Empty
Port Status = AUTHORIZED
Switch#
Configuring 802.1X with Guest VLANs
You can configure a guest VLAN for each 802.1X port on the Catalyst 4500 series switch to provide limited services to clients, such as downloading the 802.1X client. These clients might be upgrading their system for 802.1X authentication, and some hosts, such as Windows 98 systems, might not be 802.1X-capable.
When you enable a guest VLAN on an 802.1X port, the Catalyst 4500 series switch assigns clients to a guest VLAN provided the authentication server does not receive a response to its EAPOL request (or identity frame), or the EAPOL packets are not sent by the client.
Starting with Cisco IOS Release 12.2(25)EWA, the Catalyst 4500 series switch maintains the EAPOL packet history. If another EAPOL packet is detected on the interface during the lifetime of the link, network access is denied. The EAPOL history is reset upon loss of the link.
Any number of 802.1X-incapable clients are allowed access when the switch port is moved to the guest VLAN. If an 802.1X-capable client joins the same port on which the guest VLAN is configured, the port is put into the unauthorized state in the user-configured access VLAN, and authentication is restarted.
Guest VLANs are supported on 802.1X ports in single-host or multiple-hosts mode.

Note ![]() When a port is put into a guest VLAN, it is automatically placed into multihost mode, and an unlimited number of hosts can connect through the port. Changing the multihost configuration does not effect a port in a guest VLAN.
When a port is put into a guest VLAN, it is automatically placed into multihost mode, and an unlimited number of hosts can connect through the port. Changing the multihost configuration does not effect a port in a guest VLAN.

Note ![]() Except for an RSPAN VLAN or a voice VLAN, you can configure any active VLAN as an 802.1X guest VLAN.
Except for an RSPAN VLAN or a voice VLAN, you can configure any active VLAN as an 802.1X guest VLAN.
To configure 802.1X with guest VLAN on a port, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode and specifies the interface to be enabled for 802.1X authentication. |
Step 3 |
Switch(config-if)# switchport mode access or Switch(config-if)# switchport mode private-vlan host |
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# authentication
event no-response action authorize
vlan vlan-id
|
Enables a guest VLAN on a particular interface. To disable the guest VLAN feature on a particular port, use the |
Step 6 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 7 |
Switch(config-if)# end |
Returns to configuration mode. |
Step 8 |
Switch(config)# end |
Returns to privileged EXEC mode. |
This example shows how to enable regular VLAN 50 on Fast Ethernet 4/3 as a guest VLAN on a static access port:
Switch# configure terminal
Switch(config)# interface fa4/3
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication event no-response action authorize vlan 50
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch#
This example shows how to enable a secondary PVLAN 100 as a guest VLAN on a PVLAN host port:
Switch# configure terminal
Switch(config)# interface fa4/3
Switch(config-if)# switchport mode private-vlan host
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication event no-response action authorize vlan 100
Switch(config-if)# end
Switch#
To allow supplicants into a guest VLAN on a switch, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch# dot1x guest-vlan supplicant |
(Optional) Enables supplicants to be allowed into the guest VLANs globally on the switch. To disable the supplicant guest VLAN feature on a switch, use the |
Step 3 |
Switch(config)# interface interface-id |
Enters interface configuration mode and specifies the interface to be enabled for 802.1X authentication. |
Step 4 |
Switch(config-if)# switchport mode access or Switch(config-if)# switchport mode private-vlan host |
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 5 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 6 |
Switch(config-if)# dot1x guest-vlan
vlan-id
|
Specifies an active VLAN as an 802.1X guest VLAN. The range is 1 to 4094. |
Step 7 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 8 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 9 |
Switch# show dot1x interface
interface-id
|
Verifies your entries. |
Step 10 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to enable the guest VLAN feature and to specify VLAN 5 as a guest VLAN:
Switch# configure terminal
Switch(config)# dot1x guest-vlan supplicant
Switch(config)# interface gigabitethernet5/9
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication event no-response action authorize vlan 5
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch#
Configuring 802.1X with MAC Authentication Bypass
To enable MAB, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Specifies the port to be configured, and enters interface configuration mode. |
Step 3 |
Switch(config-if)# switchport mode access or Switch(config-if)# switchport mode private-vlan host |
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 6 |
Switch(config-if)# mab [eap] |
Enables MAB on a switch. The eap option specifies that a complete EAP conversation should be used, as opposed to standard RADIUS Access-Request, Access-Accept conversation. By default, the eap option is not enabled for MAB. |
Step 7 |
Switch(config)# end |
Returns to privileged EXEC mode. |
Step 8 |
Switch# show mab interface interface-id details |
(Optional) Verifies your entries. |
Step 9 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |

Note ![]() Removing a 802.1X MAB configuration from a port does not impact the authorized or authenticated state of the port. If the port is in an unauthenticated state, it remains in that state. If the port is in an authenticated state because of MAB, the switch reverts to the 802.1X Authenticator. If the port was already authorized with a MAC address and the MAB configuration was removed, the port remains in an authorized state until re-authentication occurs. At that time, if an 802.1X supplicant is detected on the wire, the MAC address is removed.
Removing a 802.1X MAB configuration from a port does not impact the authorized or authenticated state of the port. If the port is in an unauthenticated state, it remains in that state. If the port is in an authenticated state because of MAB, the switch reverts to the 802.1X Authenticator. If the port was already authorized with a MAC address and the MAB configuration was removed, the port remains in an authorized state until re-authentication occurs. At that time, if an 802.1X supplicant is detected on the wire, the MAC address is removed.
This example shows how to enable MAB on Gigabit Ethernet interface 3/3 and to verify the configuration:
Switch# configure terminal
Switch(config)# interface gigabitethernet3/3
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# mab
Switch(config-if)# end
Switch# show mab int g3/3 details
MAB details for GigabitEthernet3/3
-------------------------------------
Mac-Auth-Bypass = Enabled
MAB Client List
---------------
Client MAC = 0001.0001.0001
Session ID = C0A8016F0000002304175914
MAB SM state = TERMINATE
Auth Status = AUTHORIZED
Configuring 802.1X with Inaccessible Authentication Bypass

To configure a port as a critical port and to enable the Inaccessible Authentication Bypass feature, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# authentication critical eapol |
(Optional) Configures whether to send an EAPOL-Success packet when a port is critically authorized partway through an EAP exchange. Note The default is not to send EAPOL-Success packets when ports are critically authorized. |
Step 3 |
Switch(config)# authentication
critical recovery delay msec
|
(Optional) Specifies a throttle rate for the reinitialization of critically authorized ports when the RADIUS server becomes available. The default throttle rate is 100 milliseconds. This means that 10 ports reinitialize per second. |
Step 4 |
Switch(config)# interface
interface-id
|
Specifies the port to be configured and enters interface configuration mode. |
Step 5 |
Switch(config-if)# switchport mode access or Switch(config-if)# switchport mode private-vlan host |
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 6 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 7 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 8 |
Switch(config-if)# authentication event server dead action authorize [vlan vlan-id] |
Enables the Inaccessible Authentication Bypass feature on the port. To disable the feature, use the |
Step 9 |
Switch(config-if)# authentication event server alive action reinitialize |
(Optional) Specifies that the port should be reinitialized if it is critically authorized and RADIUS becomes available. The default is not to reinitialize the port. |
Step 10 |
Switch(config)# end |
Returns to privileged EXEC mode. |
Step 11 |
Switch# show dot1x interface interface-id details |
(Optional) Verifies your entries. |
Step 12 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
The following example shows a full configuration of 802.1X with Inaccessible Authentication Bypass, including required AAA and RADIUS configuration as specified in the "Enabling 802.1X Authentication" sectionand "Configuring Switch-to-RADIUS-Server Communication" section.
The RADIUS server configured is at IP address 10.1.2.3, using port 1645 for authentication and 1646 for accounting. The RADIUS secret key is mykey. The username used for the test server probes is randomuser. The test probes for both living and dead servers are generated once per minute. The interface FastEthernet 3/1 is configured to critically authenticate into VLAN 17 when AAA becomes unresponsive, and to reinitialize automatically when AAA becomes available again.
Switch# configure terminal
Switch(config)# aaa new-model
Switch(config)# aaa authentication dot1x default group radius
Switch(config)# dot1x system-auth-control
Switch(config)# radius-server host 10.1.2.3 auth-port 1645 acct-port 1646 test username
randomuser idle-time 1 key mykey
Switch(config)# radius deadtime 1
Switch(config)# radius dead-criteria time 15 tries 3
Switch(config)# interface f3/1
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication event server dead action authorize vlan 17
Switch(config-if)# end
Switch# show dot1x int fastethernet 3/1 details
Dot1x Info for FastEthernet3/1
-----------------------------------
PAE = AUTHENTICATOR
PortControl = AUTO
ControlDirection = Both
HostMode = SINGLE_HOST
ReAuthentication = Disabled
QuietPeriod = 60
ServerTimeout = 30
SuppTimeout = 30
ReAuthPeriod = 3600 (Locally configured)
ReAuthMax = 2
MaxReq = 2
TxPeriod = 30
RateLimitPeriod = 0
Critical-Auth = Enabled
Critical Recovery Action = Reinitialize
Critical-Auth VLAN = 17
Dot1x Authenticator Client List
-------------------------------
Supplicant = 0000.0000.0001
Auth SM State = AUTHENTICATING
Auth BEND SM Stat = RESPONSE
Port Status = AUTHORIZED
Authentication Method = Dot1x
Authorized By = Critical-Auth
Operational HostMode = SINGLE_HOST
Vlan Policy = 17
Switch#
Configuring 802.1X with Unidirectional Controlled Port
To configure unidirectional controlled port, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Specifies the port to be configured and enters interface configuration mode. |
Step 3 |
Switch(config-if)# switchport mode access or Switch(config-if)# switchport mode private-vlan host |
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 6 |
Switch(config-if)# authentication
control-direction {in | both}
|
Enables unidirectional port control on each port. |
Step 7 |
Switch(config)# end |
Returns to privileged EXEC mode. |
Step 8 |
Switch# show dot1x interface interface-id details |
(Optional) Verifies your entries. |
Step 9 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |

Note ![]() Unidirectional Controlled Port only works when Spanning Tree Portfast is enabled on the port. Unidirectional Controlled Port and Spanning Tree Portfast should be configured on a switch port that connects to a host. If two such ports are connected together with an Ethernet cable, high CPU utilization may result because host learning is flapping between the two ports.
Unidirectional Controlled Port only works when Spanning Tree Portfast is enabled on the port. Unidirectional Controlled Port and Spanning Tree Portfast should be configured on a switch port that connects to a host. If two such ports are connected together with an Ethernet cable, high CPU utilization may result because host learning is flapping between the two ports.
This example shows how to enable unidirectional port control:
Switch# configure terminal
Switch(config)# interface gigabitethernet3/3
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication control-direction in
Switch(config-if)# end
Switch# show dot1x int g3/3
Dot1x Info for GigabitEthernet3/3
-----------------------------------
PAE = AUTHENTICATOR
PortControl = AUTO
ControlDirection = In
HostMode = SINGLE_HOST
ReAuthentication = Disabled
QuietPeriod = 60
ServerTimeout = 30
SuppTimeout = 30
ReAuthPeriod = 3600 (Locally configured)
ReAuthMax = 2
MaxReq = 2
TxPeriod = 30
RateLimitPeriod = 0
Switch#
Configuring 802.1X with Authentication Failed
By configuring authentication-failed VLAN alignment on any Layer 2 port on the Catalyst 4500 series switch, you can provide limited network services to clients that fail the authentication process.

Note ![]() Use the authentication-failed VLAN assignment with other security features, such as Dynamic ARP Inspection (DAI), Dynamic Host Configuration Protocol (DHCP) snooping, and IP Source Guard. Each of these features can be enabled and disabled independently on the authentication-failed VLAN.
Use the authentication-failed VLAN assignment with other security features, such as Dynamic ARP Inspection (DAI), Dynamic Host Configuration Protocol (DHCP) snooping, and IP Source Guard. Each of these features can be enabled and disabled independently on the authentication-failed VLAN.
To configure 802.1X with authentication-failed VLAN assignment, perform this task:
This example shows how to enable a regular VLAN 40 on Fast Ethernet 4/3 as a authentication-failed VLAN on a static access port:
Switch# configure terminal
Switch(config)# interface gigabitEthernet3/1
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# authentication event fail retry 5 action authorize vlan 40
Switch(config-if)# end
Switch# show dot1x all
Sysauthcontrol Enabled
Dot1x Protocol Version 2
Dot1x Info for GigabitEthernet3/1
-----------------------------------
PAE = AUTHENTICATOR
PortControl = AUTO
ControlDirection = Both
HostMode = SINGLE_HOST
QuietPeriod = 60
ServerTimeout = 0
SuppTimeout = 30
ReAuthMax = 2
MaxReq = 2
TxPeriod = 30
Switch#
Configuring 802.1X with Voice VLAN

Note ![]() You must configure 802.1X and voice VLAN simultaneously.
You must configure 802.1X and voice VLAN simultaneously.

Note ![]() You cannot configure an authentication-failed VLAN and a voice VLAN on the same port. When you try to configure these two features on the same port, a syslog message appears.
You cannot configure an authentication-failed VLAN and a voice VLAN on the same port. When you try to configure these two features on the same port, a syslog message appears.
To enable 802.1X with voice VLAN, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode. |
Step 3 |
Switch(config-if)# switchport
access vlan vlan-id
|
Sets the VLAN for a switched interface in access mode. |
Step 4 |
Switch(config-if)# switchport mode access |
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 5 |
Switch(config-if)# switchport voice
vlan vlan-id
|
Sets the voice VLAN for the interface. |
Step 6 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 7 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 8 |
Switch(config-if)# end |
Returns to configuration mode. |
Step 9 |
Switch(config)# end |
Returns to privileged EXEC mode. |
Step 10 |
Switch# show dot1x interface interface-id details |
(Optional) Verifies your entries. |
Step 11 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to enable 802.1X with voice VLAN feature on Fast Ethernet interface 5/9:
Switch# configure terminal
Switch(config)# interface fastethernet5/9
Switch(config-if)# switchport access vlan 2
Switch(config-if)# switchport mode access
Switch(config-if)# switchport voice vlan 10
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch(config# end
Switch#
Configuring 802.1X with VLAN Assignment
For enabling dynamic VLAN assignment, there is no additional configuration required in the switch. For configuring MDA or Multi-authentication refer "Configuring Multiple Domain Authentication and Multiple Authorization" section on page 39-29. To enable VLAN assignment, Cisco ACS Server has to be configured correspondingly.
To enable 802.1X with VLAN assignment, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode. |
Step 3 |
Switch(config-if)# switchport
access vlan-id
|
Sets the VLAN for a switched interface in access mode. |
Step 4 |
Switch(config-if)# switchport mode access |
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 5 |
Switch(config-if)# switchport voice
vlan vlan-id
|
Sets the voice VLAN for the interface. |
Step 6 |
Switch(config-if)# authentication host-mode multi-domain |
Enables MDA on the interface. |
Step 7 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 8 |
Switch(config-if)# dot1x pae
authenticator
|
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 9 |
Switch(config)# end |
Returns to privileged EXEC mode. |
Step 10 |
Switch# show dot1x interface interface-id details |
(Optional) Verifies your entries. |
Step 11 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
The following example shows how to configure MDA on an interface and 802.1X as the authentication mechanism:

Note ![]() You must configure VLAN assignment in the ACS server. No configuration changes are required on the switch.
You must configure VLAN assignment in the ACS server. No configuration changes are required on the switch.
Switch(config)# interface FastEthernet3/3
Switch(config-if)# switchport access vlan 10
Switch(config-if)# switchport mode access
Switch(config-if)# switchport voice vlan 16
Switch(config-if)# authentication host-mode multi-domain
Switch(config-if)# authentication port-control auto
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# end
Cisco ACS Configuration for VLAN Assignment
The procedure for enabling MDA with Voice VLAN assignment is the same as that for activating MDA except for one step: Configure a VLAN for dynamic VLAN Assignment after selecting
User > IETF RADIUS Attributes (Figure 36-12). This step ensures correct functioning of the ACS configuration required for dynamic VLAN assignment.
Figure 36-12 User Setup


Note ![]() The procedure is the same for voice devices except that the AAA server must be configured to send a Cisco Attribute-Value (AV) pair attribute with a value of device-traffic-class=voice.
The procedure is the same for voice devices except that the AAA server must be configured to send a Cisco Attribute-Value (AV) pair attribute with a value of device-traffic-class=voice.
Enabling Fallback Authentication
On a port in multiauthentication mode, either or both of MAB and web-based authentication can be configured as fallback authentication methods for non-802.1X hosts (those that do not respond to EAPOL). You can configure the order and priority of the authentication methods.
For detailed configuration information for MAB, see the "Configuring 802.1X with MAC Authentication Bypass" section.
For detailed configuration information for web-based authentication, see Chapter 37 "Configuring Web-Based Authentication."

Note ![]() When Webauth and other authentication methods are configured on an MDA or multiauthentication port, downloadable ACL policies must be configured for all devices attached to that port.
When Webauth and other authentication methods are configured on an MDA or multiauthentication port, downloadable ACL policies must be configured for all devices attached to that port.
To enable fallback authentication, perform this task:
This example shows how to enable 802.1X fallback to MAB, and then to enable web-based authentication, on an 802.1X-enabled port:
Switch(config)# ip admission name rule1 proxy http
Switch(config)# fallback profile fallback1
Switch(config-fallback-profile)# ip access-group default-policy in
Switch(config-fallback-profile)# ip admission rule1
Switch(config-fallback-profile)# exit
Switch(config)# interface gigabit5/9
Switch(config-if)# switchport mode access
Switch(config-if)# authentication port-control auto
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication order dot1x mab webauth
Switch(config-if)# mab eap
Switch(config-if)# authentication fallback fallback1
Switch(config-if)# exit
Switch(config)# ip device tracking
Switch(config)# exit
To determine if a host has been authenticated using 802.1X when fallback authentication is configured on the port, enter the following commands:
Switch# show authentication sessions interface g7/2
Interface: GigabitEthernet7/2
MAC Address: 0060.b057.4687
IP Address: Unknown
User-Name: test2
Status: Authz Success
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: C0A8013F0000000901BAB560
Acct Session ID: 0x0000000B
Handle: 0xE8000009
Runnable methods list:
Method State
dot1x Authc Success
mab Not run
Switch# show dot1x interfaces g7/2 detail
Dot1x Info for GigabitEthernet7/2
-----------------------------------
PAE = AUTHENTICATOR
PortControl = AUTO
ControlDirection = Both
HostMode = MULTI_AUTH
QuietPeriod = 60
ServerTimeout = 0
SuppTimeout = 30
ReAuthMax = 2
MaxReq = 2
TxPeriod = 2
Dot1x Authenticator Client List
-------------------------------
Supplicant = 0060.b057.4687
Session ID = C0A8013F0000000901BAB560
Auth SM State = AUTHENTICATED
Auth BEND SM State = IDLE
Port Status = AUTHORIZED
To determine if a host has been authenticated using MAB when fallback authentication is configured on the port, enter the following commands:
Switch# show authentication sessions interface g7/2
Interface: GigabitEthernet7/2
MAC Address: 0060.b057.4687
IP Address: 192.168.22.22
User-Name: 0060b0574687
Status: Authz Success
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: C0A8013F0000000B01BBD278
Acct Session ID: 0x0000000D
Handle: 0xF500000B
Runnable methods list:
Method State
dot1x Failed over
mab Authc Success
Switch# show mab interface g7/2 detail
MAB details for GigabitEthernet7/2
-------------------------------------
Mac-Auth-Bypass = Enabled
MAB Client List
---------------
Client MAC = 0060.b057.4687
Session ID = C0A8013F0000000B01BBD278
MAB SM state = TERMINATE
Auth Status = AUTHORIZED
To determine if a host has been authenticated using web authentication when fallback authentication is configured on the port, enter the following commands:
Switch# show authentication sessions interface G4/3
Interface: GigabitEthernet4/3
MAC Address: 0015.e981.0531
IP Address: 10.5.63.13
Status: Authz Success
Domain: DATA
Oper host mode: single-host
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A053F0F0000000200112FFC
Acct Session ID: 0x00000003
Handle: 0x09000002
Runnable methods list:
Method State
dot1x Failed over
mab Failed over
webauth Authc Success
Switch# show ip admission cache
Authentication Proxy Cache
Total Sessions: 1 Init Sessions: 0
Client IP 10.5.63.13 Port 4643, timeout 1000, state ESTAB
Enabling Periodic Reauthentication
You can enable periodic 802.1X client reauthentication and specify how often it occurs. If you do not specify a time value before enabling reauthentication, the interval between reauthentication attempts is 3600 seconds.
Automatic 802.1X client reauthentication is a per-interface setting and can be set for clients connected to individual ports. To manually reauthenticate the client connected to a specific port, see the "Changing the Quiet Period" section.
To enable periodic reauthentication of the client and to configure the number of seconds between reauthentication attempts, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode and specifies the interface to be enabled for periodic reauthentication. |
Step 3 |
Switch(config-if)# switchport mode
access
|
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# authentication periodic |
Enables periodic reauthentication of the client, which is disabled by default. To disable periodic reauthentication, use the no authentication periodic interface configuration command (for earlier releases, use the |
Step 6 |
Switch(config-if)# authentication
timer reauthenticate {seconds |
server}
|
Specifies the number of seconds between reauthentication attempts or have the switch use a RADIUS-provided session timeout. The range is 1 to 65,535; the default is 3600 seconds. To return to the default number of seconds between reauthentication attempts, use the no authentication timer reauthenticate global configuration command (for earlier releases, use the This command affects the behavior of the switch only if periodic reauthentication is enabled. |
Step 7 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 8 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
This example shows how to enable periodic reauthentication and set the number of seconds between reauthentication attempts to 4000:
Switch# configure terminal
Switch(config)# interface fastethernet5/9
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication periodic
Switch(config-if)# authentication timer reauthenticate 4000
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch#
Enabling Multiple Hosts
You can attach multiple hosts (clients) to a single 802.1X-enabled port as shown in Figure 36-7. In this mode, when the port is authorized, all other hosts that are indirectly attached to the port are granted access to the network. If the port becomes unauthorized (reauthentication fails or an EAPOL-logoff message is received), the switch denies access to the network for all wireless access point-attached clients.
To allow multiple hosts (clients) on an 802.1X-authorized port that has the dot1x port-control interface configuration command set to auto, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface
interface-id
|
Enters interface configuration mode and specifies the interface to which multiple hosts are indirectly attached. |
Step 3 |
Switch(config-if)# switchport mode
access
|
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# authentication host-mode multi-host |
Allows multiple hosts (clients) on an 802.1X-authorized port. Note To disable multiple hosts on the port, use the |
Step 6 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 7 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 8 |
Switch# show dot1x all interface
interface-id
|
Verifies your entries. |
Step 9 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to enable 802.1X on Fast Ethernet interface 5/9 and to allow multiple hosts:
Switch# configure terminal
Switch(config)# interface fastethernet5/9
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# authentication host-mode multi-host
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch#
Changing the Quiet Period
When the switch cannot authenticate the client, the switch remains idle for a set period of time, and then tries again. The idle time is determined by the quiet-period value. A failed authentication of the client might occur because the client provided an invalid password. You can provide a faster response time to the user by entering a number smaller than the default.
To change the quiet period, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode and specifies the interface to be enabled for timeout quiet-period. |
Step 3 |
Switch(config-if)# switchport mode
access
|
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# dot1x timeout quiet-period seconds |
Sets the number of seconds that the switch remains in the quiet-period following a failed authentication exchange with the client. To return to the default quiet-period, use the The range is 0 to 65,535 seconds; the default is 60. |
Step 6 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 7 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 8 |
Switch# show dot1x all |
Verifies your entries. |
Step 9 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to set the quiet period on the switch to 30 seconds:
Switch# configure terminal
Switch(config)# interface fastethernet4/1
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# dot1x timeout quiet-period 30
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch#
Changing the Switch-to-Client Retransmission Time
The client responds to the EAP-request/identity frame from the switch with an EAP-response/identity frame. If the switch does not receive this response, it waits a set period of time (known as the retransmission time) and then retransmits the frame.

Note ![]() You should change the default value of this command only to adjust for unusual circumstances, such as unreliable links or specific behavioral problems with certain clients and authentication servers.
You should change the default value of this command only to adjust for unusual circumstances, such as unreliable links or specific behavioral problems with certain clients and authentication servers.
To change the amount of time that the switch waits for client notification, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode and specifies the interface to be enabled for timeout tx-period. |
Step 3 |
Switch(config-if)# switchport mode
access
|
Specifies a nontrunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# dot1x timeout tx-period seconds |
Sets the number of seconds that the switch waits for a response to an EAP-request/identity frame from the client before retransmitting the request. The range is 1 to 65,535 seconds; the default is 30. To return to the default retransmission time, use the |
Step 6 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 7 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 8 |
Switch# show dot1x all |
Verifies your entries. |
Step 9 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to set the retransmission time to 60 seconds:
Switch# configure terminal
Switch(config)# interface fastethernet5/9
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# dot1x timeout tx-period 60
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch#
Setting the Switch-to-Client Frame-Retransmission Number
In addition to changing the switch-to-client retransmission times, you can change the number of times that the switch sends EAP-Request/Identity and other EAP-Request frames to the client before restarting the authentication process. The number of EAP-Request/Identity retransmissions is controlled by the dot1x max-reauth-req command; the number of retransmissions for other EAP-Request frames is controlled by the dot1x max-req command.

Note ![]() You should change the default values of these commands only to adjust for unusual circumstances such as unreliable links or specific behavioral problems with certain clients and authentication servers.
You should change the default values of these commands only to adjust for unusual circumstances such as unreliable links or specific behavioral problems with certain clients and authentication servers.
To set the switch-to-client frame-retransmission numbers, perform this task:
|
|
|
|
|---|---|---|
Step 1 |
Switch# configure terminal |
Enters global configuration mode. |
Step 2 |
Switch(config)# interface interface-id |
Enters interface configuration mode and specifies the interface to be enabled for max-reauth-req and/or max-req. |
Step 3 |
Switch(config-if)# switchport mode
access
|
Specifies a non-trunking, nontagged single VLAN Layer 2 interface. |
Step 4 |
Switch(config-if)# dot1x pae authenticator |
Enables 802.1X authentication on the port with default parameters. Refer to the "Default 802.1X Configuration" section. |
Step 5 |
Switch(config-if)# dot1x max-req count or Switch(config-if)# dot1x max-reauth-req count |
Specifies the number of times EAPOL DATA packets are re-transmitted (if lost or not replied to). For example, if you have a supplicant in the midst of authenticating and it experiences a problem, the authenticator re-transmits requests for data three times before abandoning the authentication request. The range for count is 1 to 10; the default is 2. Specifies the timer for EAPOL-Identity-Request frames (only). If you plug in a device incapable of 802.1X, three EAPOL-Id-Req frames are sent before the state machine resets. Alternatively, if you have configured Guest-VLAN, three frames are sent before the port is enabled. This parameter has a default value of 2. To return to the default retransmission number, use the no dot1x max-req and no dot1x max-reauth-req global configuration command. |
Step 6 |
Switch(config-if)# authentication port-control auto |
Enables 802.1X authentication on the interface. |
Step 7 |
Switch(config-if)# end |
Returns to privileged EXEC mode. |
Step 8 |
Switch# show dot1x all |
Verifies your entries. |
Step 9 |
Switch# copy running-config startup-config |
(Optional) Saves your entries in the configuration file. |
This example shows how to set 5 as the number of times that the switch retransmits an EAP-request/identity request before restarting the authentication process:
Switch# configure terminal
Switch(config)# interface fastethernet5/9
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x pae authenticator
Switch(config-if)# dot1x max-reauth-req 5
Switch(config-if)# authentication port-control auto
Switch(config-if)# end
Switch#
Manually Reauthenticating a Client Connected to a Port
You can manually reauthenticate a client connected to a specific port at any time by entering the
dot1x re-authenticate interface privileged EXEC command. If you want to enable or disable periodic reauthentication, see the "Enabling Periodic Reauthentication" section.
This example shows how to manually reauthenticate the client connected to Fast Ethernet port 1/1:
Switch# dot1x re-authenticate interface fastethernet1/1
Starting reauthentication on FastEthernet1/1
Initializing the 802.1X Authentication State
The dot1x initialize command causes the authentication process to be restarted irrespective of the state it is in currently.
This example shows how to restart the authentication process on Fast Ethernet port 1/1:
Switch# dot1x initialize interface fastethernet1/1
This example shows how to restart the authentication process on all ports of the switch:
Switch# dot1x initialize
Removing 802.1X Client Information
The clear dot1x command causes all existing supplicants to be completely deleted from an interface or from all the interfaces on a switch.
This example shows how to remove 802.1X client information on Fast Ethernet port 1/1:
Switch# clear dot1x interface fastethernet1/1
This example shows how to remove 802.1X client information on all ports of the switch:
Switch# clear dot1x all
Resetting the 802.1X Configuration to the Default Values
To reset the 802.1X configuration to the default values, perform this task:
Displaying 802.1X Statistics and Status
To display 802.1X statistics for all interfaces, use the show dot1x all statistics privileged EXEC command.
To display the 802.1X administrative and operational status for the switch, use the
show dot1x all details privileged EXEC command. To display the 802.1X administrative and operational status for a specific interface, use the show dot1x interface details privileged EXEC command.
Displaying Authentication Details
Topics in this section include:
•![]() Determining the Authentication Methods Registered with the Auth Manager
Determining the Authentication Methods Registered with the Auth Manager
•![]() Displaying the Auth Manager Summary for an Interface
Displaying the Auth Manager Summary for an Interface
•![]() Displaying the Summary of All Auth Manager Sessions on the Switch
Displaying the Summary of All Auth Manager Sessions on the Switch
•![]() Verifying the Auth Manager Session for an Interface
Verifying the Auth Manager Session for an Interface
Determining the Authentication Methods Registered with the Auth Manager
Enter the following:
Switch# show authentication registrations
Handle Priority Name
3 0 dot1x
2 1 mab
1 2 webauth
Displaying the Auth Manager Summary for an Interface
In the following example, MAB has been configured for a higher priority (lower value) than 802.1X:
Switch# show authentication int gi1/5
Client list:
Interface MAC Address Method Domain Status Session ID
Gi1/5 000f.23c4.a401 mab DATA Authz Success 0A3462B10000000D24F80B58
Gi1/5 0014.bf5d.d26d dot1x DATA Authz Success 0A3462B10000000E29811B94
Available methods list:
Handle Priority Name
3 0 dot1x
2 1 mab
Runnable methods list:
Handle Priority Name
2 0 mab
3 1 dot1x
Displaying the Summary of All Auth Manager Sessions on the Switch
Enter the following:
Switch# show authentication sessions
Interface MAC Address Method Domain Status Session ID
Gi1/48 0015.63b0.f676 dot1x DATA Authz Success 0A3462B1000000102983C05C
Gi1/5 000f.23c4.a401 mab DATA Authz Success 0A3462B10000000D24F80B58
Gi1/5 0014.bf5d.d26d dot1x DATA Authz Success 0A3462B10000000E29811B94
Displaying a Summary of All Auth Manager Sessions on the Switch Authorized for a Specified Authentication Method
Enter the following:
Switch# show authentication method dot1x
Interface MAC Address Method Domain Status Session ID
Gi1/48 0015.63b0.f676 dot1x DATA Authz Success 0A3462B1000000102983C05C
Gi1/5 0014.bf5d.d26d dot1x DATA Authz Success 0A3462B10000000E29811B94
Verifying the Auth Manager Session for an Interface
The Auth manage session could be verified with the show authentication sessions command.
Switch# show authentication sessions int gi1/5
Interface: GigabitEthernet1/5
MAC Address: 000f.23c4.a401
IP Address: Unknown
User-Name: 000f23c4a401
Status: Authz Success
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A3462B10000000D24F80B58
Acct Session ID: 0x0000000F
Handle: 0x2400000D
Runnable methods list:
Method State
dot1x Failed over
mab Authc Success
----------------------------------------
Interface: GigabitEthernet1/5
MAC Address: 0014.bf5d.d26d
IP Address: 20.0.0.7
User-Name: johndoe
Status: Authz Success
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A3462B10000000E29811B94
Acct Session ID: 0x00000010
Handle: 0x1100000E
Runnable methods list:
Method State
dot1x Authc Success
mab Not run
The individual output could be further refined with the handle, interface, MAC, session-id, or method keywords:
Switch# show authentication sessions mac 000f.23c4.a401
Interface: GigabitEthernet1/5
MAC Address: 000f.23c4.a401
IP Address: Unknown
User-Name: 000f23c4a401
Status: Authz Success
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A3462B10000000D24F80B58
Acct Session ID: 0x0000000F
Handle: 0x2400000D
Runnable methods list:
Method State
dot1x Failed over
mab Authc Success
Switch# show authentication sessions session-id 0A3462B10000000D24F80B58
Interface: GigabitEthernet1/5
MAC Address: 000f.23c4.a401
IP Address: Unknown
User-Name: 000f23c4a401
Status: Authz Success
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A3462B10000000D24F80B58
Acct Session ID: 0x0000000F
Handle: 0x2400000D
Runnable methods list:
Method State
dot1x Failed over
mab uthc Success
Switch# show authentication session method dot1x int gi1/5
Interface: GigabitEthernet1/5
MAC Address: 0014.bf5d.d26d
IP Address: 20.0.0.7
User-Name: johndoe
Status: Authz Success
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Authorized By: Authentication Server
Vlan Policy: N/A
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0A3462B10000000E29811B94
Acct Session ID: 0x00000010
Handle: 0x1100000E
Runnable methods list:
Method State
dot1x Authc Success
mab Not run
Displaying MAB Details
Enter one of the following commands:
Switch# show mab all
MAB details for FastEthernet5/9
-------------------------------------
Mac-Auth-Bypass = Enabled
Inactivity Timeout = None
Switch# show mab all detail
MAB details for FastEthernet5/9
-------------------------------------
Mac-Auth-Bypass = Enabled
Inactivity Timeout = None
MAB Client List
---------------
Client MAC = 000f.23c4.a401
MAB SM state = TERMINATE
Auth Status = AUTHORIZED
Switch# show mab int fa5/9
MAB details for FastEthernet5/9
-------------------------------------
Mac-Auth-Bypass = Enabled
Inactivity Timeout = None
Switch# show mab int fa5/9 detail
MAB details for FastEthernet5/9
-------------------------------------
Mac-Auth-Bypass = Enabled
Inactivity Timeout = None
MAB Client List
---------------
Client MAC = 000f.23c4.a401
MAB SM state = TERMINATE
Auth Status = AUTHORIZED
EPM Logging
EPM logging enables you to display EPM logging messages with the epm logging command in global configuration mode. To disable EPM logging, enter no epm logging.
Logging messages are displayed during the following events:
POLICY_APP_SUCCESS - Policy application success events on Named ACLs, Proxy ACLs, and service policies, URL redirect policies.
POLICY_APP_FAILURE - Policy application failure conditions like unconfigured policies, wrong policies, download request failures and download failures from AAA.
IPEVENT - IP assignment, IP release and IP wait events for clients.
AAA - AAA events (like download requests, or download successes from AAA)
Example 1
Switch# conf t
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# epm logging
Switch# clear dot1x all
Switch#
*May 15 08:31:26.561: %EPM-6-POLICY_REQ: IP=100.0.0.222| MAC=0000.0000.0001|
AUDITSESID=0A050B2C000000030004956C| AUTHTYPE=DOT1X|
EVENT=REMOVE
*May 15 08:31:26.581: %AUTHMGR-5-START: Starting 'dot1x' for client (0000.0000.0001) on Interface Fa9/25
*May 15 08:31:26.681: %DOT1X-5-SUCCESS: Authentication successful for client (0000.0000.0001) on Interface Fa9/25
*May 15 08:31:26.681: %AUTHMGR-7-RESULT: Authentication result 'success' from 'dot1x' for client (0000.0000.0001) on Interface Fa9/25
Example 2
Switch# conf t
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# epm logging
Switch(config)# int f9/25
Switch(config-if)# shut
Switch(config-if)# no shut
*May 15 08:41:56.329: %EPM-6-IPEVENT: IP=100.0.0.222| MAC=0000.0000.0001|
AUDITSESID=0A050B2C0000026108FB7924| AUTHTYPE=DOT1X|
EVENT=IP-RELEASE
*May 15 08:41:56.333: %EPM-6-IPEVENT: IP=100.0.0.222| MAC=0000.0000.0001|
AUDITSESID=0A050B2C0000026108FB7924| AUTHTYPE=DOT1X|
EVENT=IP-WAIT
-Cisco IOS Security Features in Cisco IOS XE 3.1.0 SG Release
This document provides a list of security software features that are supported in Cisco IOS XE 3.1.0 SG. Links to the feature documentation are included.
Feature guides may contain information about more than one feature. To find information about a specific feature within a feature guide, see the Feature Information table at the end of the guide.
Feature guides document features that are supported on many different software releases and platforms. Your Cisco software release or platform may not support all the features documented in a feature guide. See the Feature Information table at the end of the feature guide for information about which features in that guide are supported in your software release. Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Role-Based Access Control CLI Commands
http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/sec_role_base_cli.html
Authentication Proxy Accounting for HTTP
http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/sec_cfg_authen_prxy.html
Enhanced Password Security
http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/sec_cfg_sec_4cli.html
IEEE 802.1X - Flexible Authentication
http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/sec_cfg_authen_prxy.html
Image Verification
http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/sec_image_verifctn.html
Manual Certificate Enrollment via TFTP
Pre-fragmentation For Ipsec VPNs
Router Security Audit Manageability
http://www.cisco.com/en/US/prod/collateral/routers/ps10537/product_bulletin_ISRG2_Manageability.pdf
Trusted Root Certification Authority
http://www.cisco.com/en/US/partner/tech/tk59/technologies_tech_note09186a00804b976b.shtml
 Feedback
Feedback