Upgrade the Software
See the Cisco ASA Upgrade Guide for full upgrade procedures.
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
This chapter describes how to manage the ASA software and configurations.
See the Cisco ASA Upgrade Guide for full upgrade procedures.
To load a software image onto an ASA from the ROMMON mode using TFTP, perform the following steps.
|
Step 1 |
Connect to the ASA console port according to the instructions in Access the ISA 3000 Console. |
||
|
Step 2 |
Power off the ASA, then power it on. |
||
|
Step 3 |
During startup, press the Escape key when you are prompted to enter ROMMON mode. |
||
|
Step 4 |
In ROMMOM mode, define the interface settings to the ASA, including the IP address, TFTP server address, gateway address, software image file, and port, as follows:
|
||
|
Step 5 |
Validate your settings: |
||
|
Step 6 |
Ping the TFTP server: |
||
|
Step 7 |
Save the network settings for future use: |
||
|
Step 8 |
Load the software image: After the software image is successfully loaded, the ASA automatically exits ROMMON mode. |
||
|
Step 9 |
Booting the ASA from ROMMON mode does not preserve the system image across reloads; you must still download the image to flash memory. See the Cisco ASA Upgrade Guide for full upgrade procedures. |
Follow these steps to upgrade the ROMMON image for the ISA 3000. For the ASA models, the ROMMON version on your system must be 1.1.8 or greater. We recommend that you upgrade to the latest version.
You can only upgrade to a new version; you cannot downgrade.
 Caution |
The ISA 3000 ROMMON upgrade for 1.0.5 takes twice as long as previous ROMMON versions, approximately 15 minutes. Do not power cycle the device during the upgrade. If the upgrade is not complete within 30 minutes or it fails, contact Cisco technical support; do not power cycle or reset the device. |
Obtain the new ROMMON image from Cisco.com, and put it on a server to copy to the ASA. The ASA supports FTP, TFTP, SCP, HTTP(S), and SMB servers. Download the image from:
|
Step 1 |
Copy the ROMMON image to the ASA flash memory. This procedure shows an FTP copy; enter copy ? for the syntax for other server types. copy ftp://[username:password@]server_ip/asa5500-firmware-xxxx.SPA disk0:asa5500-firmware-xxxx.SPA |
|
Step 2 |
To see your current version, enter the show module command and look at the Fw Version in the output for Mod 1 in the MAC Address Range table: |
|
Step 3 |
Upgrade the ROMMON image: upgrade rommon disk0:asa5500-firmware-xxxx.SPA Example: |
|
Step 4 |
Confirm to reload the ASA when you are prompted. The ASA upgrades the ROMMON image, and then reloads the operating system. |
In many cases, you can downgrade your ASA software and restore a backup configuration from the previous software version. The method of downgrading depends on your ASA platform.
See the following guidelines before downgrading:
There is no official Zero Downtime Downgrade support for clustering—However, in some cases, Zero Downtime Downgrading will work. See the following known issues for downgrading; note that there may be other issues that require you to reload your cluster units, thus causing downtime.
Downgrade to a pre-9.9(1) release with clustering—9.9(1) and later includes an improvement in the backup distribution. If you have 3 or more units in the cluster, you must perform the following steps:
Remove all secondary units from the cluster (so the cluster consists only of the primary unit).
Downgrade 1 secondary unit, and rejoin it to the cluster.
Disable clustering on the primary unit; downgrade it, and rejoin the cluster.
Downgrade the remaining secondary units, and join them back to the cluster, one at a time.
Downgrade to a pre-9.9(1) release when you enable cluster site redundancy—You should disable site redundancy if you want to downgrade (or if you want to add a pre-9.9(1) unit to a cluster). Otherwise, you will see side effects, for example, dummy forwarding flows on the unit running the old version.
Downgrade from 9.8(1) with clustering and crypto-map—There is no Zero Downtime Downgrade support when downgrading from 9.8(1) when you have a crypto-map configured. You should clear the crypto-map configuration before downgrading, and then re-apply the configuration after the downgrade.
Downgrade from 9.8(1) with clustering unit health check set to .3 to .7 seconds—If you downgrade your ASA software after setting the hold time to .3 - .7 (health-check holdtime ), this setting will revert to the default of 3 seconds because the new setting is unsupported.
Downgrade from 9.5(2) or later to 9.5(1) or earlier with clustering (CSCuv82933)—There is no Zero Downtime Downgrade support when downgrading from 9.5(2). You must reload all units at roughly the same time so that a new cluster is formed when the units come back online. If you wait to reload the units sequentially, then they will be unable to form a cluster.
Downgrade from 9.2(1) or later to 9.1 or earlier with clustering—Zero Downtime Downgrade is not supported.
Downgrade issue from 9.22 or later—If you disable the USB port using the usb-port disable command, but then downgrade to an earlier release, the port will remain disabled, and you cannot re-enable it without erasing the NVRAM (the FXOS local-mgmt erase secure all command).
Downgrade issue from 9.18 or later—There is a behavior change in 9.18 where the access-group command will be listed before its access-list commands. If you downgrade, the access-group command will be rejected because it has not yet loaded the access-list commands. This outcome occurs even if you had previously enabled the forward-reference enable command, because that command is now removed. Before you downgrade, be sure to copy all access-group commands manually, and then after downgrading, re-enter them.
Downgrade from 9.10(1) for smart licensing—Due to changes in the smart agent, if you downgrade, you must re-register your device to the Cisco Smart Software Manager. The new smart agent uses an encrypted file, so you need to re-register to use an unencrypted file required by the old smart agent.
Downgrade to 9.5 and earlier with passwords using PBKDF2 (Password-Based Key Derivation Function 2) hash—Versions before 9.6 do not support PBKDF2 hashing. In 9.6(1), enable and username passwords longer than 32 characters use PBKDF2 hashing. In 9.7(1), new passwords of all lengths use PBKDF2 hashing (existing passwords continue to use MD5 hashing). If you downgrade, the enable password reverts to the default (which is blank). Usernames will not parse correctly, and the username commands will be removed. You must re-create your local users.
Downgrade from Version 9.5(2.200) for the ASA Virtual—The ASA virtual does not retain the licensing registration state. You need to re-register with the license smart register idtoken id_token force command (for ASDM: see the Configuration > Device Management > Licensing > Smart Licensing page, and use the Force registration option); obtain the ID token from the Smart Software Manager.
VPN tunnels are replicated to the standby unit even if the standby unit is running a version of software that does not support the Ciphersuite that the original tunnel negotiated—This scenario occurs when downgrading. In this case, disconnect your VPN connection and reconnect.
When you downgrade to an old version, commands that were introduced in later versions will be removed from the configuration. There is no automated way to check the configuration against the target version before you downgrade. You can view when new commands were added in ASA new features by release.
You can view rejected commands after you downgrade using the show startup-config errors command. If you can perform a downgrade on a lab device, you can preview the effects using this command before you perform the downgrade on a production device.
In some cases, the ASA migrates commands to new forms automatically when you upgrade, so depending on your version, even if you did not manually configure new commands, the downgrade could be affected by configuration migrations. We recommend that you have a backup of your old configuration that you can use when you downgrade. In the case of upgrading to 8.3, a backup is automatically created (<old_version>_startup_cfg.sav). Other migrations do not create back-ups. See the "Version-Specific Guidelines and Migrations" in the ASA Upgrade guide for more information about automatic command migrations that could affect downgrading.
See also known downgrade issues in Guidelines and Limitations for Downgrading.
For example, an ASA running version 9.8(2) includes the following commands:
access-list acl1 extended permit sctp 192.0.2.0 255.255.255.0 198.51.100.0 255.255.255.0
username test1 password $sha512$1234$abcdefghijklmnopqrstuvwxyz privilege 15
snmp-server user snmpuser1 snmpgroup1 v3 engineID abcdefghijklmnopqrstuvwxyz encrypted auth md5 12:ab:34 priv aes 128 12:ab:34
When you downgrade to 9.0(4), you will see the following errors on startup:
access-list acl1 extended permit sctp 192.0.2.0 255.255.255.0 198.51.100.0 255.255.255.0
^
ERROR: % Invalid input detected at '^' marker.
username test1 password $sha512$1234$abcdefghijklmnopqrstuvwxyz pbkdf2 privilege 15
^
ERROR: % Invalid input detected at '^' marker.
snmp-server user snmpuser1 snmpgroup1 v3 engineID abcdefghijklmnopqrstuvwxyz encrypted auth md5 12:ab:34 priv aes 128 12:ab:34
^
ERROR: % Invalid input detected at '^' marker.In this example, support for sctp in the access-list extended command was added in version 9.5(2), support for pbkdf2 in the username command was added in version 9.6(1), and support for engineID in the snmp-server user command was added in version 9.5(3).
You can downgrade the ASA software version by setting the ASA version to the old version, restoring the backup configuration to the startup configuration, and then reloading.
This procedure requires a backup configuration of the ASA before you upgraded, so you can restore the old configuration. If you do not restore the old configuration, you may have incompatible commands representing new or changed features. Any new commands will be rejected when you load the old software version.
|
Step 1 |
Load the old ASA software version using the upgrade procedure in the ASA upgrade guide for standalone, failover, or clustering deployments. In this case, specify the old ASA version instead of a new version. Important: Do not reload the ASA yet. |
|
Step 2 |
At the ASA CLI, copy the backup ASA configuration to the startup configuration. For failover, perform this step on the active unit. This step replicates the command to the standby unit. copy old_config_url startup-config It's important that you do not save the running configuration to the startup configuration using write memory ; this command will overwrite your backup configuration. Example: |
|
Step 3 |
Reload the ASA. ASA CLI reload ASDM Choose . |
You can downgrade the ASA software version by restoring the backup configuration to the startup configuration, setting the ASA version to the old version, and then reloading.
This procedure requires a backup configuration of the ASA before you upgraded, so you can restore the old configuration. If you do not restore the old configuration, you may have incompatible commands representing new or changed features. Any new commands will be rejected when you load the old software version.
Make sure the old ASA version is compatibile with the current FXOS version. If not, downgrade FXOS as the first step before you restore the old ASA configuration. Just make sure the downgraded FXOS is also compatible with the current ASA version (before you downgrade it). If you cannot achieve compatibility, we suggest you do not perform a downgrade.
|
Step 1 |
At the ASA CLI, copy the backup ASA configuration to the startup configuration. For failover or clustering, perform this step on the active/control unit. This step replicates the command to the standby/data units. copy old_config_url startup-config It's important that you do not save the running configuration to the startup configuration using write memory ; this command will overwrite your backup configuration. Example: |
|
Step 2 |
In FXOS, use the chassis manager or FXOS CLI to use the old ASA software version using the upgrade procedure in the ASA upgrade guide for standalone, failover, or clustering deployments. In this case, specify the old ASA version instead of a new version. |
|
Step 3 |
If you are also downgrading FXOS, use the chassis manager or FXOS CLI to set the old FXOS software version to be the current version using the upgrade procedure in the ASA upgrade guide for standalone, failover, or clustering deployments. |
The downgrade feature provides a shortcut for completing the following functions on ISA 3000 models:
Clearing the boot image configuration (clear configure boot ).
Setting the boot image to be the old image (boot system ).
(Optional) Entering a new activation key (activation-key ).
Saving the running configuration to startup (write memory ). This sets the BOOT environment variable to the old image, so when you reload, the old image is loaded.
Copying the old configuration backup to the startup configuration (copy old_config_url startup-config ).
Reloading (reload ).
This procedure requires a backup configuration of the ASA before you upgraded, so you can restore the old configuration.
|
Step 1 |
Choose . The Downgrade Software dialog box appears. |
|
Step 2 |
For the ASA Image, click Select Image File. The Browse File Locations dialog box appears. |
|
Step 3 |
Click one of the following radio buttons:
|
|
Step 4 |
For the Configuration, click Browse Flash to choose the pre-migration configuration file. |
|
Step 5 |
(Optional) In the Activation Key field, enter the old activation key if you need to revert to a pre-8.3 activation key. |
|
Step 6 |
Click Downgrade. |
ASDM provides a set of file management tools to help you perform basic file management tasks. The File Management tool lets you view, move, copy, and delete files stored in flash memory, transfer files, and to manage files on remote storage devices (mount points).
 Note |
In multiple context mode, this tool is only available in the system security context. |
The ASA can use an FTP client, secure copy client, or TFTP client. You can also configure the ASA as a secure copy server so you can use a secure copy client on your computer.
The ASA can use FTP to upload or download image files or configuration files to or from an FTP server. In passive FTP, the client initiates both the control connection and the data connection. The server, which is the recipient of the data connection in passive mode, responds with the port number to which it is listening for the specific connection.
|
Step 1 |
From the Configuration > Device Management > Management Access > File Access > FTP Client pane, check the Specify FTP mode as passive check box. |
|
Step 2 |
Click Apply. The FTP client configuration is changed and the change is saved to the running configuration. |
You can configure SCP settings when the ASA acts as an SCP client using the copy command.
The performance of SCP depends partly on the encryption cipher used. By default, the ASA negotiates one of the following algorithms in order: 3des-cbc aes128-cbc aes192-cbc aes256-cbc aes128-ctr aes192-ctr aes256-ctr. If the first algorithm proposed (3des-cbc) is chosen, then the performance is much slower than a more efficient algorithm such as aes128-cbc. To change the proposed ciphers, use the pane; for example, choose Custom and set it to aes128-cbc.
The ASA license must have the strong encryption (3DES/AES) license to support SSH Version 2 connections.
Unless otherwise specified, for multiple context mode, complete this procedure in the system execution space. If you are not already in the System configuration mode, in the Configuration > Device List pane, double-click System under the active device IP address.
For the SCP server, enable SSH on the ASA according to Configure HTTPS Access for ASDM, Other Clients.
|
Step 1 |
Depending on your context mode:
|
|
Step 2 |
(Optional) The ASA stores the SSH host key for each SCP server to which it connects. You can manually add or delete servers and their keys from the ASA database if desired. To add a key: To delete a key, select the server from the Trusted SSH Hosts table, and click Delete. |
|
Step 3 |
(Optional) To be informed when a new host key is detected, check the Inform me when a new host key is detected check box. By default, this option is enabled. When this option is enabled, you are prompted to accept or reject the host key if it is not already stored on the ASA. When this option is disabled, the ASA accepts the host key automatically if it was not stored before. |
|
Step 4 |
Click Apply. |
TFTP is a simple client/server file transfer protocol, which is described in RFC 783 and RFC 1350 Rev. 2. You can configure the ASA as a TFTP client so that it can copy files to or from a TFTP server. In this way, you can back up and propagate configuration files to multiple ASAs.
This section lets you predefine the path to a TFTP server so you do not need to enter it in commands such as copy and configure net.
|
Step 1 |
Choose, and check the Enable check box. |
|
Step 2 |
From the Interface Name drop-down list, choose the interface to use as a TFTP client. |
|
Step 3 |
In the IP Address field, enter the IP address of the TFTP server on which configuration files will be saved. |
|
Step 4 |
In the Path field, enter the path to the TFTP server on which configuration files will be saved. For example: /tftpboot/asa/config3 |
|
Step 5 |
Click Apply . |
You can add a CIFS or FTP mount point.
To define a Common Internet File System (CIFS) mount point, perform the following steps.
|
Step 1 |
Choose , and click . The Add CIFS Mount Point dialog box appears. |
|
Step 2 |
Check the Enable mount point check box. This option attaches the CIFS file system on the ASA to the UNIX file tree. |
|
Step 3 |
In the Mount Point Name field, enter the name of an existing CIFS location. |
|
Step 4 |
In the Server Name or IP Address field, enter the name or IP address of the server in which the mount point is located. |
|
Step 5 |
In the Share Name field, enter the name of the folder on the CIFS server. |
|
Step 6 |
In the NT Domain Name field, enter the name of the NT Domain in which the server resides. |
|
Step 7 |
In the User Name field, enter the name of the user authorized for file system mounting on the server. |
|
Step 8 |
In the Password field, enter the password for the user authorized for file system mounting on the server. |
|
Step 9 |
In the Confirm Password field, reenter the password. |
|
Step 10 |
Click OK. The Add CIFS Mount Point dialog box closes. |
|
Step 11 |
Click Apply. |
For an FTP mount point, the FTP server must have a UNIX directory listing style. Microsoft FTP servers have a default of the MS-DOS directory listing style.
|
Step 1 |
Choose , and click . The Add FTP Mount Point dialog box appears. |
|
Step 2 |
Check the Enable check box. This option attaches the FTP file system on the ASA to the UNIX file tree. |
|
Step 3 |
In the Mount Point Name field, enter the name of an existing FTP location. |
|
Step 4 |
In the Server Name or IP Address field, enter the name or IP address of the server where the mount point is located. |
|
Step 5 |
In the Mode field, click the radio button for the FTP mode (Active or Passive). When you choose Passive mode, the client initiates both the FTP control connection and the data connection. The server responds with the number of its listening port for this connection. |
|
Step 6 |
In the Path to Mount field, enter the directory path name to the FTP file server. |
|
Step 7 |
In the User Name field, enter the name of the user authorized for file system mounting on the server. |
|
Step 8 |
In the Password field, enter the password for the user authorized for file system mounting on the server. |
|
Step 9 |
In the Confirm Password field, reenter the password. |
|
Step 10 |
Click OK. The Add FTP Mount Point dialog box closes. |
|
Step 11 |
Click Apply. |
To use the file management tools, perform the following steps.
|
Step 1 |
In the main ASDM application window, choose . The File Management dialog box appears.
|
|
Step 2 |
Click View to display the selected file in your browser. |
|
Step 3 |
Click Cut to cut the selected file for pasting to another directory. |
|
Step 4 |
Click Copy to copy the selected file for pasting to another directory. |
|
Step 5 |
Click Paste to paste the copied file to the selected destination. |
|
Step 6 |
Click Delete to remove the selected file from flash memory. |
|
Step 7 |
Click Rename to rename a file. |
|
Step 8 |
Click New Directory to create a new directory for storing files. |
|
Step 9 |
Click File Transfer to open the File Transfer dialog box. See Transfer Files for more information. |
|
Step 10 |
Click Mount Points to open the Manage Mount Points dialog box. See Add Mount Points for more information. |
The File Transfer tool lets you transfer files from either a local or remote location. You can transfer a local file on your computer or a flash file system to and from the ASA. You can transfer a remote file to and from the ASA using HTTP, HTTPS, TFTP, FTP, or SMB.
 Note |
For the IPS SSP software module, before you download the IPS software to disk0, make sure at least 50% of the flash memory is free. When you install IPS, IPS reserves 50% of the internal flash memory for its file system. |
To transfer files between your local computer and a flash file system, perform the following steps.
|
Step 1 |
In the main ASDM application window, choose . The File Management dialog box appears. |
|
Step 2 |
Click the down arrow next to File Transfer, and then click Between Local PC and Flash. The File Transfer dialog box appears. |
|
Step 3 |
Select and drag the file(s) from either your local computer or the flash file system that you want to upload or download to the desired location. Alternatively, select the file(s) from either your local computer or the flash file system that you want to upload or download, and click the right arrow or left arrow to transfer the file(s) to the desired location. |
|
Step 4 |
Click Close when you are done. |
To transfer files between a remote server and a flash file system, perform the following steps.
|
Step 1 |
In the main ASDM application window, choose . The File Management dialog box appears. |
|
Step 2 |
Click the down arrow from the File Transfer drop-down list, and then click Between Remote Server and Flash. The File Transfer dialog box appears. |
|
Step 3 |
To transfer a file from a remote server, click the Remote server option. |
|
Step 4 |
Define the source file to be transferred. |
|
Step 5 |
To transfer the file from the flash file system, click the Flash file system option. |
|
Step 6 |
Enter the path to the location of the file or click Browse Flash to find the file location. |
|
Step 7 |
In addition, you can copy a file from your startup configuration, running configuration, or an SMB file system through the CLI. For instructions about using the copy command, see the CLI configuration guide. |
|
Step 8 |
Define the destination of the file to be transferred.
|
|
Step 9 |
To transfer a file to a remote server, choose the Remote server option. |
|
Step 10 |
Click Transfer to start the file transfer. The Enter Username and Password dialog box appears. |
|
Step 11 |
Enter the username, password, and domain (if required) for the remote server. |
|
Step 12 |
Click OK to continue the file transfer. The file transfer process might take a few minutes; make sure that you wait until it is finished. |
|
Step 13 |
Click Close when the file transfer is finished. |
If you have more than one ASA or ASDM image, you should specify the image that you want to boot. If you do not set the image, the default boot image is used, and that image may not be the one intended. For the startup configuration, you can optionally specify a file in the visible file system instead of a hidden directory.
See the following model guidelines:
Firepower 4100/9300 chassis—ASA upgrades are managed by FXOS; you cannot upgrade the ASA within the ASA operating system, so do not use this procedure for the ASA image. You can upgrade the ASA and FXOS separately from each other, and they are listed separately in the FXOS directory listing. The ASA package always includes ASDM.
Firepower 1000, Secure Firewall 1200/3100/4200—The ASA, ASDM, and FXOS images are bundled together into a single package. Package updates are managed by the ASA using this procedure. Although these platforms use the ASA to identify the image to boot, the underlying mechanism is different from legacy ASAs. See the command description below for more information.
ASDM for the models—ASDM can be upgraded from within the ASA operating system, so you do not need to only use the bundled ASDM image. For Firepower 4100/9300, ASDM images that you upload manually do not appear in the FXOS image list; you must manage ASDM images from the ASA.
 Note |
When you upgrade the ASA bundle, the ASDM image in the bundle replaces the previous ASDM bundle image on the ASA because they have the same name (asdm.bin). But if you manually chose a different ASDM image that you uploaded (for example, asdm-782.bin), then you continue to use that image even after a bundle upgrade. To make sure that you are running a compatible version of ASDM, you should either upgrade ASDM before you upgrade the bundle, or you should reconfigure the ASA to use the bundled ASDM image (asdm.bin) just before upgrading the ASA bundle. |
ASA Virtual—The initial deployment ASA virtual package puts the ASA image in the read-only boot:/ partition. When you upgrade the ASA virtual, you specify a different image in flash memory. Note that if you later clear your configuration, then the ASA virtual will revert to loading the original deployment image. The initial deployment ASA virtual package also includes an ASDM image that it places in flash memory. You can upgrade the ASDM image separately.
disk0: is the internal memory. Other drive numbers represent external storage such as a USB drive, SSD, or SD card.
See the following default settings:
ASA image:
Firepower 1000, Secure Firewall 1200/3100/4200—Boots the previously-running boot image.
ISA 3000—Boots the first application image that it finds in internal flash memory.
ASA Virtual—Boots the image in the read-only boot:/ partition that was created when you first deployed.
Firepower 4100/9300 chassis—The FXOS system determines which ASA image to boot. You cannot use this procedure to set the ASA image.
ASDM image on all ASAs—Boots the first ASDM image that it finds in internal flash memory, or if one does not exist in this location, then in external flash memory.
Startup configuration—By default, the ASA boots from a startup configuration that is a hidden file.
|
Step 1 |
Choose . Firepower 1000 Secure Firewall 1200/3100/4200: You can only add a single image. If you upgrade to a new image, then you must delete the previous image you set. When you apply this change, the system performs an action: the system validates and unpacks the image and copies it to the boot location (an internal location on disk0 managed by FXOS). The new image will load when you reload the ASA. If you change your mind prior to reloading, you can delete the Boot Image Location and reapply to remove the new image from the boot location, so the current image continues to run. You can even delete the original image file from the ASA flash memory after you apply this change, and the ASA will boot correctly from the boot location. Unlike other models, this command in the startup configuration does not affect the booting image. The last-loaded boot image will always run upon reload. You can only load images with the original filename from the Cisco download site. If you change the filename, it will not load. ASA virtual and ISA 3000:You can specify up to four local binary image files for use as the startup image, and one image located on a TFTP server for the device to boot from. If you specify an image located on a TFTP server, it must be first in the list. If the device cannot reach the TFTP server to load the image, it tries to load the next image file in the list located in flash. |
|
Step 2 |
Click Add in the Boot Image/Configuration pane. |
|
Step 3 |
Browse to the image from which you want to boot. For a TFTP image, enter the TFTP URL in the File Name field. Click OK. |
|
Step 4 |
Arrange the images in order by using the Move Up and Move Down buttons. |
|
Step 5 |
(Optional) In the Boot Configuration File Path field, specify the startup configuration file by clicking Browse Flash and choosing the configuration. Click OK. This feature is important for when you work with large configurations that do not fit in the hidden directory. If you save a large configuration and see the following error message, be sure to instead save the configuration to a new file using this command:
|
|
Step 6 |
In the ASDM Image File Path field, specify the ASDM image by clicking Browse Flash and choosing the image. Click OK. |
|
Step 7 |
Click Apply. |
We recommend that you make regular backups of your configuration and other system files to guard against system failure.
These procedures describe how to back up and restore configurations and images to a zip file and transfer it to your local computer.
You should have at least 300 MB of disk space available at the backup or restore location before you start a backup or restore.
The ASA must be in single context mode.
If you make any configuration changes during or after a backup, those changes will not be included in the backup. If you change a configuration after making the backup, then perform a restore, this configuration change will be overwritten. As a result, the ASA might behave differently.
You can start only one backup or restore at a time.
You can only restore a configuration to the same ASA version as when you performed the original backup. You cannot use the restore tool to migrate a configuration from one ASA version to another. If a configuration migration is required, the ASA automatically upgrades the resident startup configuration when it loads the new ASA OS.
If you use clustering, you can only back up or restore the startup-configuration, running-configuration, and identity certificates. You must create and restore a backup separately for each unit.
If you use failover, you must create and restore a backup separately for the active and standby units.
If you set a master passphrase for the ASA, then you need that master passphrase to restore the backup configuration that you create with this procedure. If you do not know the master passphrase for the ASA, see Configure the Master Passphrase to learn how to reset it before continuing with the backup.
If you import PKCS12 data (with the crypto ca trustpoint command) and the trustpoint uses RSA keys, the imported key pair is assigned the same name as the trustpoint. Because of this limitation, if you specify a different name for the trustpoint and its key pair after you have restored an ASDM configuration, the startup configuration will be the same as the original configuration, but the running configuration will include a different key pair name. This means that if you use different names for the key pair and trustpoint, you cannot restore the original configuration. To work around this issue, make sure that you use the same name for the trustpoint and its key pair.
You cannot back up using the CLI and restore using ASDM, or vice versa.
Each backup file includes the following content:
Running-configuration
Startup-configuration
All security images
Cisco Secure Desktop and Host Scan images
Cisco Secure Desktop and Host Scan settings
Secure Client (SVC) images and profiles
Secure Client (SVC) customizations and transforms
Identity certificates (includes RSA key pairs tied to identity certificates; excludes standalone keys)
VPN pre-shared keys
SSL VPN configurations
Application Profile Custom Framework (APCF)
Bookmarks
Customizations
Dynamic Access Policy (DAP)
Plug-ins
Pre-fill scripts for connection profiles
Proxy Auto-config
Translation table
Web content
Version information
This procedure describes how to perform a complete system backup.
 Note |
If the backup process stalls, your ASDM may not have enough memory to load the configuration. You can monitor the Java console for the "java.lang.OutOfMemoryError" message to see if running out of memory is the problem. To increaes the ASDM memory, see Increase the ASDM Configuration Memory. |
|
Step 1 |
Create a folder on your computer to store backup files so they will be easy to find in case you need to restore them later. |
||
|
Step 2 |
Choose . The Backup Configurations dialog box appears. Click the down arrow in the SSL VPN Configuration area to view the backup options for SSL VPN configurations. By default, all configuration files are checked and will be backed up if they are available. If you want to back up all of the files in the list, go to Step 5. |
||
|
Step 3 |
Uncheck the Backup All check box if you want to select the configurations to back up. |
||
|
Step 4 |
Check the check box next to the option that you want to back up. |
||
|
Step 5 |
Click Browse Local to specify a directory and file name for the backup .zip file. |
||
|
Step 6 |
In the Select dialog box, choose the directory in which you want to store the backup file. |
||
|
Step 7 |
Click Select. The path appears in the Backup File field. |
||
|
Step 8 |
Enter the name of the destination backup file after the directory path. The backup file name must be between 3 and 232 characters long. |
||
|
Step 9 |
Click Backup. The backup proceeds immediately unless you are backing up certificates or the ASA is using a master passphrase. |
||
|
Step 10 |
If you have configured and enabled a master passphrase on your ASA, you receive a warning message with a suggestion to change the master passphrase, if you do not know it, before proceeding with the backup. Click Yes to proceed with the backup if you know the master passphrase. The backup proceeds immediately unless you are backing up identity certificates. |
||
|
Step 11 |
If you are backing up an identity certificate, you are asked to enter a separate passphrase to be used for encoding the certificates in PKCS12 format. You can enter a passphrase or skip this step.
After clicking OK or Cancel, the backup begins immediately. |
||
|
Step 12 |
After the backup is complete, the status window closes and the Backup Statistics dialog box appears to provide success and failure messages.
|
||
|
Step 13 |
Click OK to close the Backup Statistics dialog box. |
You can specify configurations and images to restore from a zip tar.gz file on your local computer.
 Note |
If the restore process stalls, your ASDM may not have enough memory to load the configuration. You can monitor the Java console for the "java.lang.OutOfMemoryError" message to see if running out of memory is the problem. To increaes the ASDM memory, see Increase the ASDM Configuration Memory. |
|
Step 1 |
Choose . |
|
Step 2 |
In the Restore Configurations dialog box, click Browse Local Directory, choose the zip file on your local computer that contains the configuration to restore, then click Select. The path and the zip filename appear in the Local File field. The zip file that you restore must be created by choosing the Tools > Backup Configurations option. |
|
Step 3 |
Click Next. The second Restore Configuration dialog box appears. Check the check boxes next to the configurations that you want to restore. All available SSL VPN configurations are selected by default. |
|
Step 4 |
Click Restore. |
|
Step 5 |
If you specified a certificate passphrase with which to encrypt the certificates when you created the backup file, ASDM prompts you to enter the passphrase. |
|
Step 6 |
If you chose to restore the running configuration, you are asked if you want to merge the running configuration, replace the running configuration, or skip this part of the restoration process.
ASDM displays a status dialog box until the restore operation is finished. |
|
Step 7 |
If you replaced or merged the running configuration, close ASDM and restart it. If you did not restore the running configuration or the running configuration, refresh the ASDM session for the changes to take effect. |
On the ISA 3000, you can configure automatic backups to a particular location every time you save your configuration.
Automatic restore lets you easily configure new devices with a complete configuration loaded on an SD flash memory card. Automatic restore is enabled in the default factory configuration.
On the ISA 3000, you can configure automatic backups to a particular location every time you save your configuration.
This feature is only available on the ISA 3000.
|
Step 1 |
Choose . |
|
Step 2 |
Check or uncheck Automate Backup Configuration to enable or disable automatic backups. If you enable automatic backups, when you save the configuration, the configuration is automatically saved to the backup location as well as to the startup configuration. The backup file has the name "auto-backup-asa.tgz". Set the following parameters:
|
Automatic restore mode restores the system configuration on a device without any user intervention. For example, you insert an SD memory card containing a saved backup configuration into a new device and then power the device on. When the device comes up, it checks the SD card to decide if the system configuration needs to be restored. (The restoration is only initiated if the backup file has the "fingerprint" of a different device. The fingerprint of the backup file is updated to match the current device during a backup or restore operation. So if the device has already completed a restore, or if it has created its own backup, then the automatic restore is skipped.) If the fingerprint shows a restoration is required, the device replaces the system configuration (startup-config, running-config, SSL VPN configuration, and so on; see Back Up the System for details about the contents of the backup). When the device finishes booting, it is running the saved configuration.
Automatic restore is enabled in the default factory configuration, so you can easily configure new devices with a complete configuration loaded on an SD memory card without having to perform any pre-configuration of the device.
Because the device needs to decide early in the boot process if the system configuration needs to be restored, it checks ROMMON variables to determine if the device is in automatic restore mode and to obtain the location of the backup configuration. The following ROMMON variables are used:
RESTORE_MODE = {auto | manual}
The default is auto.
RESTORE_LOCATION = {disk0: | disk1: | disk2: | disk3:}
The default is disk3:.
RESTORE_PASSPHRASE = key
The default is cisco.
To change the automatic restore settings, complete the following procedure.
This feature is only available on the ISA 3000.
If you use the default restore settings, you need an SD memory card installed (part number SD-IE-1GB=).
If you need to restore the default configuration to ensure that automatic restore is enabled, use the configure factory default command. This command is only available in transparent firewall mode, so if you are in routed firewall mode, use the firewall transparent command first.
|
Step 1 |
Choose . |
|
Step 2 |
Check or uncheck Automate Restore Configuration to enable or disable automatic restore. The name of the file that is restored is "auto-backup-asa.tgz". If you enable automatic restore, set the following parameters:
|
This feature stores a copy of the current running configuration file on a TFTP server.
|
Step 1 |
Choose . The Save Running Configuration to TFTP Server dialog box appears. |
||
|
Step 2 |
Enter the TFTP server IP address and file path on the TFTP server in which the configuration file will be saved, and then click Save Configuration.
|
The System Reload tool lets you schedule a system restart or cancel a pending restart.
|
Step 1 |
Choose . |
|
Step 2 |
In the Reload Scheduling area, define the following settings: |
|
Step 3 |
Choose one of the following:
|
If you have two SSDs, they form a RAID when you boot up. You can perform the following tasks at the CLI while the firewall is powered up:
Hot swap one of the SSDs—If an SSD is faulty, you can replace it. Note that if you only have one SSD, you cannot remove it while the firewall is powered on.
Remove one of the SSDs—If you have two SSDs, you can remove one.
Add a second SSD—If you have one SSD, you can add a second SSD and form a RAID.
 Caution |
Do not remove an SSD without first removing it from the RAID using this procedure. You can cause data loss. |
|
Step 1 |
Remove one of the SSDs. |
|
Step 2 |
Add an SSD. |
By default, the type-A USB port is enabled. You might want to disable USB port access for security purposes. Disabling USB is supported on the following models:
Firepower 1000 Series
Secure Firewall 3100
Secure Firewall 4200
Guidelines
Enabling or disabling the USB port requires a reload.
If the USB port is disabled and you downgrade to a version that does not support this feature, the port will remain disabled, and you cannot re-enable it without erasing the NVRAM (the FXOS local-mgmt erase secure all command).
If you perform a ROMMON factory-reset or FXOS local-mgmt erase secure , the USB port will be re-enabled.
For high availability or clustering, disable or enable the USB port on the active unit or control node. The command is replicated to the other nodes. However, you need to reload each unit for the change to take effect.
 Note |
This feature does not affect the USB console port, if present. |
|
Step 1 |
Choose . 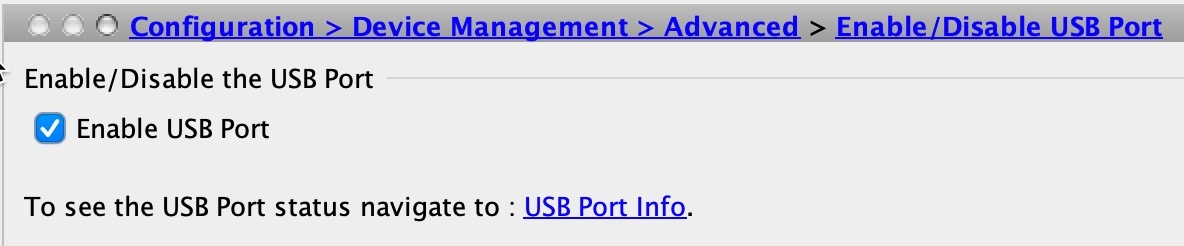
|
|
Step 2 |
Uncheck the Enable USB Port checkbox and click Apply. Click OK on the Information dialog box. To re-enable the USB port, check the Enable USB Port checkbox and click Apply. |
|
Step 3 |
Click Save. |
|
Step 4 |
Choose to reload the device for your changes to take effect. |
|
Step 5 |
Choose to view the port status. 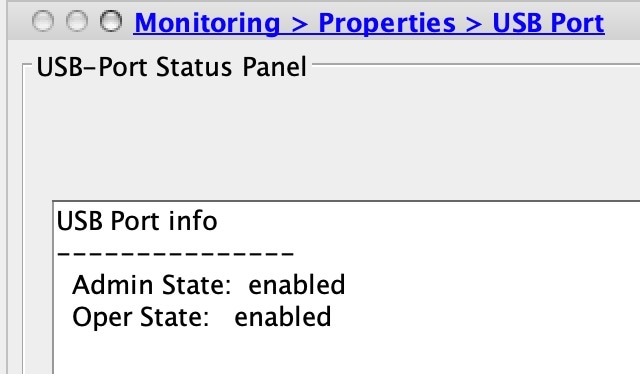
The Admin State shows the USB port configuration. The Oper State shows the current operation. For example, if you disable the USB port but do not reload, the Admin State will show disabled while the Oper State would will enabled. |
|
Feature Name |
Platform Releases |
Feature Information |
||
|---|---|---|---|---|
|
Secure Copy client and server |
9.1(5)/9.2(1) |
The ASA now supports the Secure Copy (SCP) client and server to transfer files to and from a SCP server. We modified the following screens: Tools > File Management > File Transfer > Between Remote Server and Flash Configuration > Device Management > Management Access > File Access > Secure Copy (SCP) Server |
||
|
Configurable SSH encryption and integrity ciphers |
9.1(7)/9.4(3)/9.5(3)/9.6(1) |
Users can select cipher modes when doing SSH encryption management and can configure HMAC and encryption for varying key exchange algorithms. You might want to change the ciphers to be more or less strict, depending on your application. Note that the performance of secure copy depends partly on the encryption cipher used. By default, the ASA negotiates one of the following algorithms in order: 3des-cbc aes128-cbc aes192-cbc aes256-cbc aes128-ctr aes192-ctr aes256-ctr. If the first algorithm proposed (3des-cbc) is chosen, then the performance is much slower than a more efficient algorithm such as aes128-cbc. To change the proposed ciphers, use ssh cipher encryption custom aes128-cbc , for example. We introduced the following screen: |
||
|
Auto Update server certificate verification enabled by default |
9.2(1) |
The Auto Update server certificate verification is now enabled by default; for new configurations, you must explicitly disable certificate verification. If you are upgrading from an earlier release, and you did not enable certificate verification, then certificate verification is not enabled, and you see the following warning: The configuration will be migrated to explicitly configure no verification. We modified the following screen: Configuration > Device Management > System/Image Configuration > Auto Update > Add Auto Update Server. |
||
|
System backup and restore using the CLI |
9.3(2) |
You can now back up and restore complete system configurations, including images and certificates, using the CLI. We did not modify any ASDM screens. |
||
|
Recovering and loading a new ASA 5506W-X image |
9.4(1) |
We now support the recovery and loading of a new ASA 5506W-X image. We did not modify any ASDM screens. |
||
|
Automatic Backup and Restore for the ISA 3000 |
9.7(1) |
You can enable auto-backup and/or auto-restore functionality using pre-set parameters in the backup and restore commands. The use cases for these features include initial configuration from external media; device replacement; roll back to an operable state. We introduced the following screen: |
||
|
CiscoSSH stack requires SSH access when using the SCP client |
9.17(1) |
If you use the CiscoSSH stack, to use the ASA copy command to copy a file to or from an SCP server, you have to enable SSH access on the ASA for the SCP server subnet/host |
||
|
RAID support for SSDs on the Secure Firewall 3100 |
9.17(1) |
The SSDs are self-encrypting drives (SEDs), and if you have 2 SSDs, they form a software RAID. New/Modified commands: raid, show raid, show ssd |
||
|
Disable the USB port |
9.22(1) |
By default, the type-A USB port is enabled and could not be disabled. You can now disable USB port access for security purposes on the following models:
This setting is stored in firmware and requires a reload. Moreover, if the USB port is disabled and you downgrade to a version that does not support this feature, the port will remain disabled and you cannot re-enable it without erasing the NVRAM.
New/Modified screens: . |