ASDM Requirements
ASDM Java Requirements
You can install ASDM using Oracle JRE 8.0 (asdm-version.bin) or OpenJRE 1.8.x (asdm-openjre-version.bin).
 Note |
ASDM is not supported on Linux. |
|
Operating System |
Browser |
Oracle JRE |
OpenJRE |
||||||
|---|---|---|---|---|---|---|---|---|---|
|
Firefox |
Safari |
Chrome |
|||||||
|
Microsoft Windows (English and Japanese):
|
Yes |
No support |
Yes |
8.0 version 8u261 or later |
1.8
|
||||
|
Apple OS X 10.4 and later |
Yes |
Yes |
Yes (64-bit version only) |
8.0 version 8u261 or later |
1.8 |
||||
ASDM Compatibility Notes
The following table lists compatibility caveats for ASDM.
|
Conditions |
Notes |
||
|---|---|---|---|
|
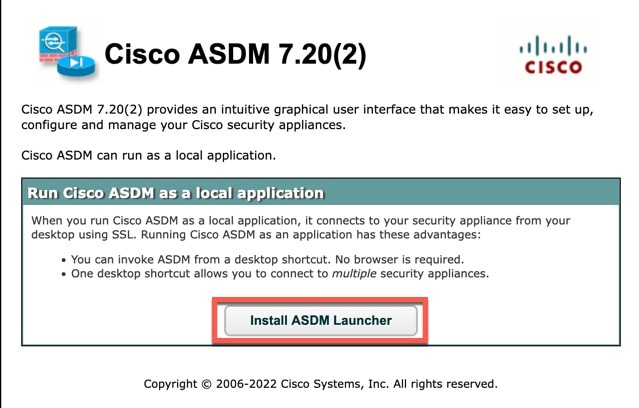
ASDM Launcher compatibility with ASDM version |
"Unable to Launch Device Manager" error message. If you upgrade to a new ASDM version and then get this error, you may need to re-install the latest Launcher.
|
||
|
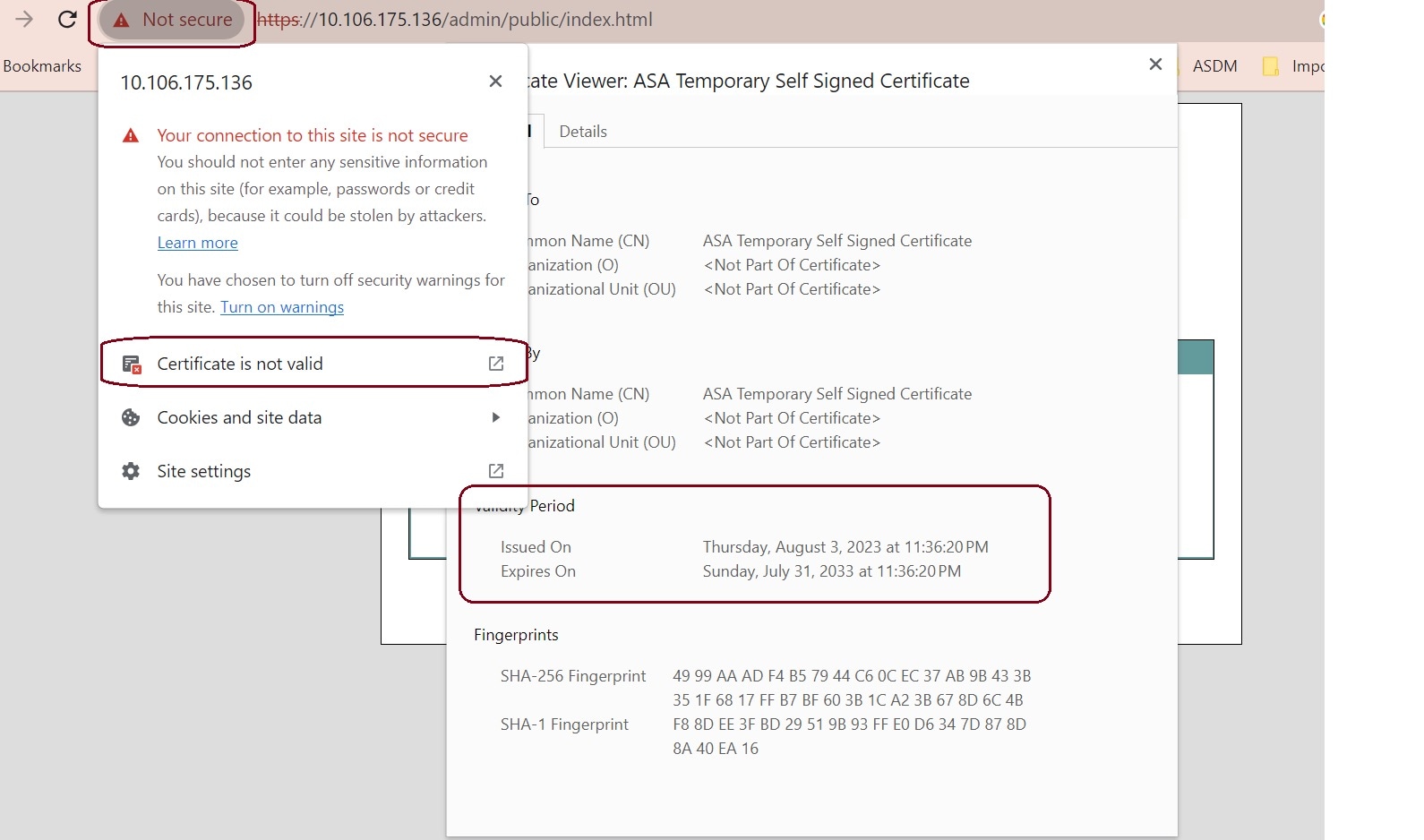
Self-signed certificate not valid due to a time and date mismatch with ASA |
ASDM validates the self-signed SSL certificate, and if the ASA's date is not within the certificate's Issued On and Expires On date, ASDM will not launch. If there is a time and date mismatch, you will see the following error: 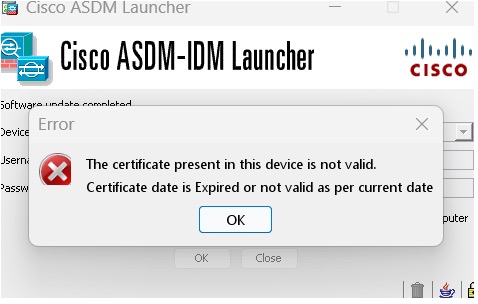
To fix the issue: Set the correct time on the ASA and reload. To check the certificate dates, (example shown is Chrome):
|
||
|
Windows Active Directory directory access |
In some cases, Active Directory settings for Windows users may restrict access to program file locations needed to successfully launch ASDM on Windows. Access is needed to the following directories:
If your Active Directory is restricting directory access, you need to request access from your Active Directory administrator. |
||
|
Windows 10 |
"This app can't run on your PC" error message. When you install the ASDM Launcher, Windows 10 might replace the ASDM shortcut target with the Windows Scripting Host path, which causes this error. To fix the shortcut target:
|
||
|
OS X |
On OS X, you may be prompted to install Java the first time you run ASDM; follow the prompts as necessary. ASDM will launch after the installation completes. |
||
|
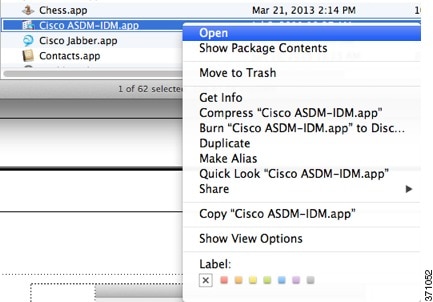
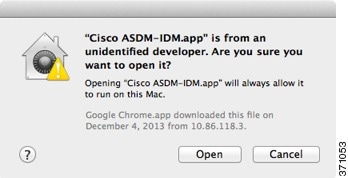
OS X 10.8 and later |
You need to allow ASDM to run because it is not signed with an Apple Developer ID. If you do not change your security preferences, you see an error screen. 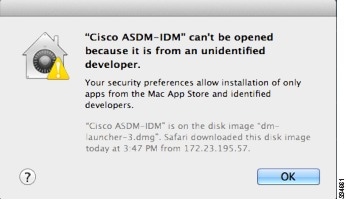
|
||
|
(ASA 5500 and ISA 3000) Requires Strong Encryption license (3DES/AES) on ASA
|
ASDM requires an SSL connection to the ASA. You can request a 3DES PAK license from Cisco:
|
||
|
When the ASA uses a self-signed certificate or an untrusted certificate, Firefox and Safari are unable to add security exceptions when browsing using HTTPS over IPv6. See https://bugzilla.mozilla.org/show_bug.cgi?id=633001. This caveat affects all SSL connections originating from Firefox or Safari to the ASA (including ASDM connections). To avoid this caveat, configure a proper certificate for the ASA that is issued by a trusted certificate authority. |
||
|
If you change the SSL encryption on the ASA to exclude both RC4-MD5 and RC4-SHA1 algorithms (these algorithms are enabled by default), then Chrome cannot launch ASDM due to the Chrome “SSL false start” feature. We suggest re-enabling one of these algorithms (see the pane); or you can disable SSL false start in Chrome using the --disable-ssl-false-start flag according to Run Chromium with flags. |
 Feedback
Feedback