- Information About Completing Interface Configuration in Transparent Mode
- Licensing Requirements for Completing Interface Configuration in Transparent Mode
- Guidelines and Limitations
- Default Settings
- Completing Interface Configuration in Transparent Mode (8.4 and Later)
- Task Flow for Completing Interface Configuration
- Configuring Bridge Groups
- Configuring General Interface Parameters
- Configuring a Management Interface (ASA 5512-X and Higher and ASAv)
- Configuring the MAC Address, MTU, and TCP MSS
- Configuring IPv6 Addressing
- Allowing Same Security Level Communication
- Turning Off and Turning On Interfaces
- Monitoring Interfaces
Transparent Mode Interfaces
This chapter includes tasks to complete the interface configuration for all models in transparent firewall mode.
This chapter includes the following sections:
- Information About Completing Interface Configuration in Transparent Mode
- Licensing Requirements for Completing Interface Configuration in Transparent Mode
- Guidelines and Limitations
- Default Settings
- Completing Interface Configuration in Transparent Mode (8.4 and Later)
- Turning Off and Turning On Interfaces
- Monitoring Interfaces
- Feature History for Interfaces in Transparent Mode

Note![]() For multiple context mode, complete the tasks in this section in the context execution space. In the Configuration > Device List pane, double-click the context name under the active device IP address.
For multiple context mode, complete the tasks in this section in the context execution space. In the Configuration > Device List pane, double-click the context name under the active device IP address.
Information About Completing Interface Configuration in Transparent Mode
This section includes the following topics:
Bridge Groups in Transparent Mode
If you do not want the overhead of security contexts, or want to maximize your use of security contexts, you can group interfaces together in a bridge group, and then configure multiple bridge groups, one for each network. Bridge group traffic is isolated from other bridge groups; traffic is not routed to another bridge group within the ASA, and traffic must exit the ASA before it is routed by an external router back to another bridge group in the ASA. Although the bridging functions are separate for each bridge group, many other functions are shared between all bridge groups. For example, all bridge groups share a syslog server or AAA server configuration. For complete security policy separation, use security contexts with one bridge group in each context. At least one bridge group is required per context or in single mode.
Each bridge group requires a management IP address. For another method of management, see Management Interface.

Note![]() The ASA does not support traffic on secondary networks; only traffic on the same network as the management IP address is supported.
The ASA does not support traffic on secondary networks; only traffic on the same network as the management IP address is supported.
Security Levels
Each interface must have a security level from 0 (lowest) to 100 (highest). For example, you should assign your most secure network, such as the inside host network, to level 100. While the outside network connected to the Internet can be level 0. Other networks, such as DMZs can be in between. You can assign interfaces to the same security level. See Allowing Same Security Level Communication for more information.
The level controls the following behavior:
- Network access—By default, there is an implicit permit from a higher security interface to a lower security interface (outbound). Hosts on the higher security interface can access any host on a lower security interface. You can limit access by applying an ACL to the interface.
If you enable communication for same security interfaces (see Allowing Same Security Level Communication), there is an implicit permit for interfaces to access other interfaces on the same security level or lower.
- Inspection engines—Some application inspection engines are dependent on the security level. For same security interfaces, inspection engines apply to traffic in either direction.
–![]() NetBIOS inspection engine—Applied only for outbound connections.
NetBIOS inspection engine—Applied only for outbound connections.
–![]() SQL*Net inspection engine—If a control connection for the SQL*Net (formerly OraServ) port exists between a pair of hosts, then only an inbound data connection is permitted through the ASA.
SQL*Net inspection engine—If a control connection for the SQL*Net (formerly OraServ) port exists between a pair of hosts, then only an inbound data connection is permitted through the ASA.
- Filtering—HTTP(S) and FTP filtering applies only for outbound connections (from a higher level to a lower level).
If you enable communication for same security interfaces, you can filter traffic in either direction.
- established command—This command allows return connections from a lower security host to a higher security host if there is already an established connection from the higher level host to the lower level host.
If you enable communication for same security interfaces, you can configure established commands for both directions.
Licensing Requirements for Completing Interface Configuration in Transparent Mode
|
|
|
|---|---|
VLANs1: Interfaces of all types2: |
|
VLANs 1 : Interfaces of all types 2 : |
|
VLANs 1 : Interfaces of all types 2 : |
|
VLANs 1 : Interfaces of all types 2 : |
|
VLANs 1 : Interfaces of all types 2 : |
|
VLANs 1 : Base and Security Plus License: 1024 Interface Speed for SSP-10 and SSP-20: Base License—1-Gigabit Ethernet for fiber interfaces 10 GE I/O License (Security Plus)—10-Gigabit Ethernet for fiber interfaces (SSP-40 and SSP-60 support 10-Gigabit Ethernet by default.) Interfaces of all types 2 : |
|
|
|
|---|---|
Guidelines and Limitations
This section includes the guidelines and limitations for this feature.
- For the ASA 5512-X and higher in multiple context mode, configure the physical interfaces in the system execution space according to Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)” Then, configure the logical interface parameters in the context execution space according to this chapter. For the ASASM in multiple context mode, configure switch ports and VLANs on the switch, and then assign VLANs to the ASASM according to Chapter2, “Switch Configuration for the ASA Services Module”
The ASA 5505 and ASAv do not support multiple context mode.
- You can only configure context interfaces that you already assigned to the context in the system configuration.
- You can configure up to 8 bridge groups in single mode or per context in multiple mode. Note that you must use at least 1 bridge group; data interfaces must belong to a bridge group.

Note![]() Although you can configure multiple bridge groups on the ASA 5505, the restriction of 2 data interfaces in transparent mode on the ASA 5505 means you can only effectively use 1 bridge group.
Although you can configure multiple bridge groups on the ASA 5505, the restriction of 2 data interfaces in transparent mode on the ASA 5505 means you can only effectively use 1 bridge group.
- Each bridge group can include up to 4 interfaces.
- For IPv4, a management IP address is required for each bridge group for both management traffic and for traffic to pass through the ASA.
Unlike routed mode, which requires an IP address for each interface, a transparent firewall has an IP address assigned to the entire bridge group. The ASA uses this IP address as the source address for packets originating on the ASA, such as system messages or AAA communications. In addition to the bridge group management address, you can optionally configure a management interface for some models; see Management Interface for more information.
The management IP address must be on the same subnet as the connected network. You cannot set the subnet to a host subnet (255.255.255.255). The ASA does not support traffic on secondary networks; only traffic on the same network as the management IP address is supported. See Configuring Bridge Groups for more information about management IP subnets.
- For IPv6, at a minimum you need to configure link-local addresses for each interface for through traffic. For full functionality, including the ability to manage the ASA, you need to configure a global IPv6 address for each bridge group.
- For multiple context mode, each context must use different interfaces; you cannot share an interface across contexts.
- For multiple context mode, each context typically uses a different subnet. You can use overlapping subnets, but your network topology requires router and NAT configuration to make it possible from a routing standpoint.
Do not finish configuring failover interfaces with the procedures in this chapter. See “Failover,” to configure the failover and state links. In multiple context mode, failover interfaces are configured in the system configuration.
VLAN ID Guidelines for the ASASM
You can add any VLAN ID to the configuration, but only VLANs that are assigned to the ASA by the switch can pass traffic. To view all VLANs assigned to the ASA, use the show vlan command.
If you add an interface for a VLAN that is not yet assigned to the ASA by the switch, the interface will be in the down state. When you assign the VLAN to the ASA, the interface changes to an up state. See the show interface command for more information about interface states.
Default Settings
This section lists default settings for interfaces if you do not have a factory default configuration. For information about the factory default configurations, see Factory Default Configurations.
The default security level is 0. If you name an interface “inside” and you do not set the security level explicitly, then the ASA sets the security level to 100.

Note![]() If you change the security level of an interface, and you do not want to wait for existing connections to time out before the new security information is used, you can clear the connections using the clear local-host command.
If you change the security level of an interface, and you do not want to wait for existing connections to time out before the new security information is used, you can clear the connections using the clear local-host command.
Default State of Interfaces for the ASASM
- In single mode or in the system execution space, VLAN interfaces are enabled by default.
- In multiple context mode, all allocated interfaces are enabled by default, no matter what the state of the interface is in the system execution space. However, for traffic to pass through the interface, the interface also has to be enabled in the system execution space. If you shut down an interface in the system execution space, then that interface is down in all contexts that share it.
By default, the ASASM supports jumbo frames. Just configure the MTU for the desired packet size according to the Configuring the MAC Address, MTU, and TCP MSS.
Completing Interface Configuration in Transparent Mode (8.4 and Later)
This section includes the following topics:
- Task Flow for Completing Interface Configuration
- Configuring Bridge Groups
- Configuring General Interface Parameters
- Configuring a Management Interface (ASA 5512-X and Higher and ASAv)
- Configuring the MAC Address, MTU, and TCP MSS
- Configuring IPv6 Addressing
- Allowing Same Security Level Communication
Task Flow for Completing Interface Configuration
Step 1![]() Set up your interfaces depending on your model:
Set up your interfaces depending on your model:
Step 2![]() (Multiple context mode) Allocate interfaces to the context according to the Configuring Multiple Contexts.
(Multiple context mode) Allocate interfaces to the context according to the Configuring Multiple Contexts.
Step 3![]() (Multiple context mode) In the Configuration > Device List pane, double-click the context name under the active device IP address.
(Multiple context mode) In the Configuration > Device List pane, double-click the context name under the active device IP address.
Step 4![]() Configure one or more bridge groups, including the IPv4 address. See Configuring Bridge Groups.
Configure one or more bridge groups, including the IPv4 address. See Configuring Bridge Groups.
Step 5![]() Configure general interface parameters, including the bridge group it belongs to, the interface name, and security level. See Configuring General Interface Parameters.
Configure general interface parameters, including the bridge group it belongs to, the interface name, and security level. See Configuring General Interface Parameters.
Step 6![]() (Optional; not supported for the ASA 5505) Configure a management interface. See Configuring a Management Interface (ASA 5512-X and Higher and ASAv).
(Optional; not supported for the ASA 5505) Configure a management interface. See Configuring a Management Interface (ASA 5512-X and Higher and ASAv).
Step 7![]() (Optional) Configure the MAC address and the MTU. See Configuring the MAC Address, MTU, and TCP MSS.
(Optional) Configure the MAC address and the MTU. See Configuring the MAC Address, MTU, and TCP MSS.
Step 8![]() (Optional) Configure IPv6 addressing. See Configuring IPv6 Addressing.
(Optional) Configure IPv6 addressing. See Configuring IPv6 Addressing.
Step 9![]() (Optional) Allow same security level communication, either by allowing communication between two interfaces or by allowing traffic to enter and exit the same interface. See Allowing Same Security Level Communication.
(Optional) Allow same security level communication, either by allowing communication between two interfaces or by allowing traffic to enter and exit the same interface. See Allowing Same Security Level Communication.
Configuring Bridge Groups
Each bridge group requires a management IP address. The ASA uses this IP address as the source address for packets originating from the bridge group. The management IP address must be on the same subnet as the connected network. For IPv4 traffic, the management IP address is required to pass any traffic. For IPv6 traffic, you must, at a minimum, configure the link-local addresses to pass traffic, but a global management address is recommended for full functionality, including remote management and other management operations.
Guidelines and Limitations
You can configure up to 8 bridge groups in single mode or per context in multiple mode. Note that you must use at least one bridge group; data interfaces must belong to a bridge group.

Note![]() For a separate management interface (for supported models), a non-configurable bridge group (ID 101) is automatically added to your configuration. This bridge group is not included in the bridge group limit.
For a separate management interface (for supported models), a non-configurable bridge group (ID 101) is automatically added to your configuration. This bridge group is not included in the bridge group limit.
Detailed Steps
Step 1![]() Choose the Configuration > Interfaces pane, and choose Add > Bridge Group Interface.
Choose the Configuration > Interfaces pane, and choose Add > Bridge Group Interface.
The Add Bridge Group dialog box appears.

Step 2![]() In the Bridge Group ID field, enter the bridge group ID between 1 and 100.
In the Bridge Group ID field, enter the bridge group ID between 1 and 100.
Step 3![]() In the IP Address field, enter the management IPv4 address.
In the IP Address field, enter the management IPv4 address.
The ASA does not support traffic on secondary networks; only traffic on the same network as the management IP address is supported.
Step 4![]() In the Subnet Mask field, enter the subnet mask or choose one from the menu.
In the Subnet Mask field, enter the subnet mask or choose one from the menu.
Do not assign a host address (/32 or 255.255.255.255) to the transparent firewall. Also, do not use other subnets that contain fewer than 3 host addresses (one each for the upstream router, downstream router, and transparent firewall) such as a /30 subnet (255.255.255.252). The ASA drops all ARP packets to or from the first and last addresses in a subnet. For example, if you use a /30 subnet and assign a reserved address from that subnet to the upstream router, then the ASA drops the ARP request from the downstream router to the upstream router.
Step 5![]() (Optional) In the Description field, enter a description for this bridge group.
(Optional) In the Description field, enter a description for this bridge group.
Step 7![]() A Bridge Group Virtual Interface (BVI) is added to the interface table, along with the physical and subinterfaces.
A Bridge Group Virtual Interface (BVI) is added to the interface table, along with the physical and subinterfaces.

What to Do Next
Configure general interface parameters. See Configuring General Interface Parameters.
Configuring General Interface Parameters
This procedure describes how to set the name, security level, and bridge group for each transparent interface.
To configure a separate management interface, see Configuring a Management Interface (ASA 5512-X and Higher and ASAv).
For the ASA 5512-X and higher and the ASAv, you must configure interface parameters for the following interface types:
For the ASA 5505 and the ASASM, you must configure interface parameters for the following interface types:
Guidelines and Limitations
- You can configure up to four interfaces per bridge group.
- For information about security levels, see Security Levels.
- If you are using failover, do not use this procedure to name interfaces that you are reserving for failover and Stateful Failover communications. See “Failover,” to configure the failover and state links.
Prerequisites
–![]() ASA 5512-X and higher—Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)”
ASA 5512-X and higher—Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)”
–![]() ASA 5505—Chapter13, “Basic Interface Configuration (ASA 5505)”
ASA 5505—Chapter13, “Basic Interface Configuration (ASA 5505)”
–![]() ASASM—Chapter2, “Switch Configuration for the ASA Services Module”
ASASM—Chapter2, “Switch Configuration for the ASA Services Module”
–![]() ASAv—Chapter14, “Basic Interface Configuration (ASAv)”
ASAv—Chapter14, “Basic Interface Configuration (ASAv)”
- In multiple context mode, you can only configure context interfaces that you already assigned to the context in the system configuration according to Configuring Multiple Contexts.
- In multiple context mode, complete this procedure in the context execution space. To change from the system to a context configuration, in the Configuration > Device List pane, double-click the context name under the active device IP address.
Detailed Steps
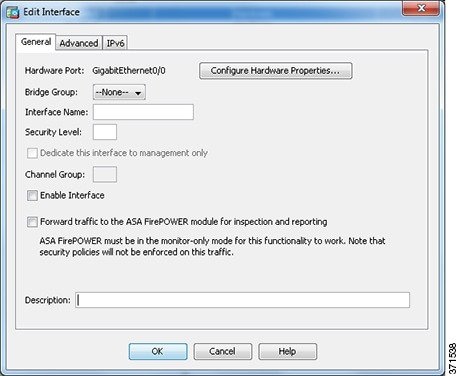
Step 1![]() Choose the Configuration > Device Setup > Interfaces pane.
Choose the Configuration > Device Setup > Interfaces pane.
BVIs appear in the table alongside physical interfaces, subinterfaces, redundant interfaces, and EtherChannel port-channel interfaces. In multiple context mode, only interfaces that were assigned to the context in the System execution space appear in the table.
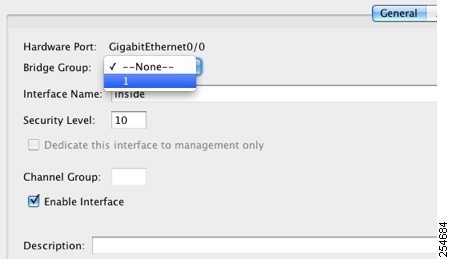
Step 2![]() Choose the row for a non-BVI interface, and click Edit.
Choose the row for a non-BVI interface, and click Edit.
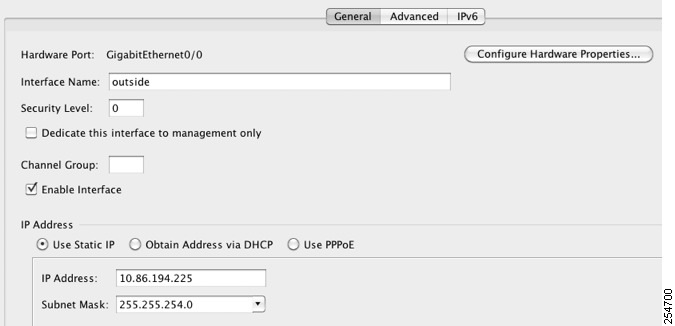
The Edit Interface dialog box appears with the General tab selected.
Do not use this procedure for Management interfaces; see Configuring a Management Interface (ASA 5512-X and Higher and ASAv) to configure the Management interface.
Step 3![]() In the Bridge Group drop-down menu, choose the bridge group to which you want to assign this interface.
In the Bridge Group drop-down menu, choose the bridge group to which you want to assign this interface.
Step 4![]() In the Interface Name field, enter a name up to 48 characters in length.
In the Interface Name field, enter a name up to 48 characters in length.
Step 5![]() In the Security level field, enter a level between 0 (lowest) and 100 (highest).
In the Security level field, enter a level between 0 (lowest) and 100 (highest).
See Security Levels for more information.

Note![]() Do not click the Dedicate this interface to management only check box; see Configuring a Management Interface (ASA 5512-X and Higher and ASAv) for this option.
Do not click the Dedicate this interface to management only check box; see Configuring a Management Interface (ASA 5512-X and Higher and ASAv) for this option.
Step 6![]() If the interface is not already enabled, check the Enable Interface check box.
If the interface is not already enabled, check the Enable Interface check box.

Note![]() The Channel Group field is read-only and indicates if the interface is part of an EtherChannel.
The Channel Group field is read-only and indicates if the interface is part of an EtherChannel.
Step 7![]() (Optional) If you install an ASA CX or ASA FirePOWER module, and you want to demonstrate the module functionality on a non-production ASA, check the Forward traffic to the ASA module for inspection and reporting check box. See the module chapter in the firewall configuration guide for more information.
(Optional) If you install an ASA CX or ASA FirePOWER module, and you want to demonstrate the module functionality on a non-production ASA, check the Forward traffic to the ASA module for inspection and reporting check box. See the module chapter in the firewall configuration guide for more information.
Step 8![]() (Optional) In the Description field, enter a description for this interface.
(Optional) In the Description field, enter a description for this interface.
The description can be up to 240 characters on a single line, without carriage returns. In the case of a failover or state link, the description is fixed as “LAN Failover Interface,” “STATE Failover Interface,” or “LAN/STATE Failover Interface,” for example. You cannot edit this description. The fixed description overwrites any description you enter here if you make this interface a failover or state link.

Note![]() (ASA 5512-X and higher, single mode) For information about the Configure Hardware Properties button, see Enabling the Physical Interface and Configuring Ethernet Parameters.
(ASA 5512-X and higher, single mode) For information about the Configure Hardware Properties button, see Enabling the Physical Interface and Configuring Ethernet Parameters.
What to Do Next
- (Optional) Configure a management interface. see Configuring a Management Interface (ASA 5512-X and Higher and ASAv).
- (Optional) Configure the MAC address and the MTU. see Configuring the MAC Address, MTU, and TCP MSS.
- (Optional) Configure IPv6 addressing. see Configuring IPv6 Addressing.
Configuring a Management Interface (ASA 5512-X and Higher and ASAv)
You can configure one management interface separate from the bridge group interfaces in single mode or per context. For more information, see Management Interface.
Restrictions
- See Management Interface.
- Do not assign this interface to a bridge group; a non-configurable bridge group (ID 101) is automatically added to your configuration. This bridge group is not included in the bridge group limit.
- If your model does not include a Management interface, you must manage the transparent firewall from a data interface; skip this procedure. (For example, on the ASA 5505.)
- In multiple context mode, you cannot share any interfaces, including the Management interface, across contexts. To provide management per context, you can create subinterfaces of the Management interface and allocate a Management subinterface to each context. Note that the ASA 5512-X through ASA 5555-X do not allow subinterfaces on the Management interface, so for per-context management, you must connect to a data interface.
Prerequisites
- Complete the procedures in Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)”
- In multiple context mode, you can only configure context interfaces that you already assigned to the context in the system configuration according to Configuring Multiple Contexts.
- In multiple context mode, complete this procedure in the context execution space. To change from the system to a context configuration, in the Configuration > Device List pane, double-click the context name under the active device IP address.
Detailed Steps
Step 1![]() Choose the Configuration > Device Setup > Interfaces pane.
Choose the Configuration > Device Setup > Interfaces pane.
BVIs appear in the table alongside physical interfaces, subinterfaces, redundant interfaces, and EtherChannel port-channel interfaces. In multiple context mode, only interfaces that were assigned to the context in the System execution space appear in the table.
Step 2![]() Choose the row for a Management interface, subinterface, or EtherChannel port-channel interface comprised of Management interfaces, and click Edit.
Choose the row for a Management interface, subinterface, or EtherChannel port-channel interface comprised of Management interfaces, and click Edit.
The Edit Interface dialog box appears with the General tab selected.

Step 3![]() In the Bridge Group drop-down menu, leave the default --None--. You cannot assign a management interface to a bridge group.
In the Bridge Group drop-down menu, leave the default --None--. You cannot assign a management interface to a bridge group.
Step 4![]() In the Interface Name field, enter a name up to 48 characters in length.
In the Interface Name field, enter a name up to 48 characters in length.
Step 5![]() In the Security level field, enter a level between 0 (lowest) and 100 (highest).
In the Security level field, enter a level between 0 (lowest) and 100 (highest).
see Security Levels for more information.

Note![]() The Dedicate this interface to management only check box is enabled by default and is non-configurable.
The Dedicate this interface to management only check box is enabled by default and is non-configurable.
Step 6![]() If the interface is not already enabled, check the Enable Interface check box.
If the interface is not already enabled, check the Enable Interface check box.
Step 7![]() To set the IP address, use one of the following options.
To set the IP address, use one of the following options.

Note![]() For use with failover, you must set the IP address and standby address manually; DHCP is not supported. Set the standby IP addresses on the Configuration > Device Management > High Availability > Failover > Interfaces tab.
For use with failover, you must set the IP address and standby address manually; DHCP is not supported. Set the standby IP addresses on the Configuration > Device Management > High Availability > Failover > Interfaces tab.
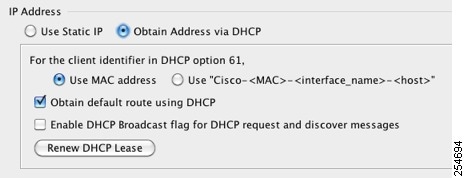
a.![]() To force a MAC address to be stored inside a DHCP request packet for option 61, click the Use MAC Address radio button.
To force a MAC address to be stored inside a DHCP request packet for option 61, click the Use MAC Address radio button.
Some ISPs expect option 61 to be the interface MAC address. If the MAC address is not included in the DHCP request packet, then an IP address will not be assigned.
b.![]() To use a generated string for option 61, click Use “Cisco-<MAC>-<interface_name>-<host>”.
To use a generated string for option 61, click Use “Cisco-<MAC>-<interface_name>-<host>”.
c.![]() (Optional) To obtain the default route from the DHCP server, check Obtain Default Route Using DHCP.
(Optional) To obtain the default route from the DHCP server, check Obtain Default Route Using DHCP.
d.![]() (Optional) To set the broadcast flag to 1 in the DHCP packet header when the DHCP client sends a discover requesting an IP address, check Enable DHCP Broadcast flag for DHCP request and discover messages.
(Optional) To set the broadcast flag to 1 in the DHCP packet header when the DHCP client sends a discover requesting an IP address, check Enable DHCP Broadcast flag for DHCP request and discover messages.
The DHCP server listens to this broadcast flag and broadcasts the reply packet if the flag is set to 1.
e.![]() (Optional) To renew the lease, click Renew DHCP Lease.
(Optional) To renew the lease, click Renew DHCP Lease.
Step 8![]() (Optional) In the Description field, enter a description for this interface.
(Optional) In the Description field, enter a description for this interface.
The description can be up to 240 characters on a single line, without carriage returns.

Note![]() (ASA 5512-X and higher, single mode) For information about the Configure Hardware Properties button, see Enabling the Physical Interface and Configuring Ethernet Parameters.
(ASA 5512-X and higher, single mode) For information about the Configure Hardware Properties button, see Enabling the Physical Interface and Configuring Ethernet Parameters.
What to Do Next
- (Optional) Configure the MAC address and the MTU. see Configuring the MAC Address, MTU, and TCP MSS.
- (Optional) Configure IPv6 addressing. see Configuring IPv6 Addressing.
Configuring the MAC Address, MTU, and TCP MSS
This section describes how to configure MAC addresses for interfaces, how to set the MTU, and set the TCP MSS.
Information About MAC Addresses
By default, the physical interface uses the burned-in MAC address, and all subinterfaces of a physical interface use the same burned-in MAC address.
For the ASASM, all VLANs use the same MAC address provided by the backplane.
A redundant interface uses the MAC address of the first physical interface that you add. If you change the order of the member interfaces in the configuration, then the MAC address changes to match the MAC address of the interface that is now listed first. If you assign a MAC address to the redundant interface using this command, then it is used regardless of the member interface MAC addresses.
For an EtherChannel, all interfaces that are part of the channel group share the same MAC address. This feature makes the EtherChannel transparent to network applications and users, because they only see the one logical connection; they have no knowledge of the individual links. The port-channel interface uses the lowest numbered channel group interface MAC address as the port-channel MAC address. Alternatively you can manually configure a MAC address for the port-channel interface. In multiple context mode, you can automatically assign unique MAC addresses to interfaces, including an EtherChannel port interface. We recommend manually, or in multiple context mode, automatically configuring a unique MAC address in case the group channel interface membership changes. If you remove the interface that was providing the port-channel MAC address, then the port-channel MAC address changes to the next lowest numbered interface, thus causing traffic disruption.
In multiple context mode, if you share an interface between contexts, you can assign a unique MAC address to the interface in each context. This feature lets the ASA easily classify packets into the appropriate context. Using a shared interface without unique MAC addresses is possible, but has some limitations. see How the ASA Classifies Packets for more information. You can assign each MAC address manually, or you can automatically generate MAC addresses for shared interfaces in contexts. see Automatically Assigning MAC Addresses to Context Interfaces to automatically generate MAC addresses. If you automatically generate MAC addresses, you can use this procedure to override the generated address.
For single context mode, or for interfaces that are not shared in multiple context mode, you might want to assign unique MAC addresses to subinterfaces. For example, your service provider might perform access control based on the MAC address.
Information About the MTU and TCP MSS
See Controlling Fragmentation with the Maximum Transmission Unit and TCP Maximum Segment Size.
Prerequisites
–![]() ASA 5512-X and higher—Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)”
ASA 5512-X and higher—Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)”
–![]() ASA 5505—Chapter13, “Basic Interface Configuration (ASA 5505)”
ASA 5505—Chapter13, “Basic Interface Configuration (ASA 5505)”
–![]() ASASM—Chapter2, “Switch Configuration for the ASA Services Module”
ASASM—Chapter2, “Switch Configuration for the ASA Services Module”
–![]() ASAv—Chapter14, “Basic Interface Configuration (ASAv)”
ASAv—Chapter14, “Basic Interface Configuration (ASAv)”
- In multiple context mode, you can only configure context interfaces that you already assigned to the context in the system configuration according to Configuring Multiple Contexts.
- In multiple context mode, complete this procedure in the context execution space. To change from the system to a context configuration, in the Configuration > Device List pane, double-click the context name under the active device IP address.
Detailed Steps
Step 1![]() Choose the Configuration > Device Setup > Interfaces pane.
Choose the Configuration > Device Setup > Interfaces pane.
For the ASA 5505, the Interfaces tab shows by default.
Step 2![]() Choose the interface row, and click Edit.
Choose the interface row, and click Edit.
The Edit Interface dialog box appears with the General tab selected.
Step 3![]() Click the Advanced tab.
Click the Advanced tab.
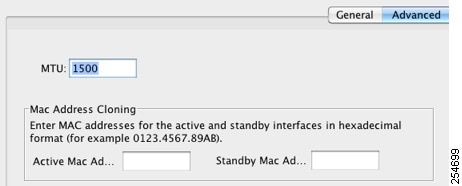
Step 4![]() To set the MTU or to enable jumbo frame support (supported models only), enter the value in the MTU field, between 300 and 9198 bytes (9000 for the ASAv).
To set the MTU or to enable jumbo frame support (supported models only), enter the value in the MTU field, between 300 and 9198 bytes (9000 for the ASAv).

Note![]() When you set the MTU for a redundant or port-channel interface, the ASA applies the setting to all member interfaces.
When you set the MTU for a redundant or port-channel interface, the ASA applies the setting to all member interfaces.
- For models that support jumbo frames in single mode—If you enter a value for any interface that is greater than 1500, then you enable jumbo frame support automatically for all interfaces. If you set the MTU for all interfaces back to a value under 1500, then jumbo frame support is disabled.
- For models that support jumbo frames in multiple mode—If you enter a value for any interface that is greater than 1500, then be sure to enable jumbo frame support in the system configuration. see Enabling Jumbo Frame Support.

Note![]() Enabling or disabling jumbo frame support requires you to reload the ASA.
Enabling or disabling jumbo frame support requires you to reload the ASA.
Step 5![]() To manually assign a MAC address to this interface, enter a MAC address in the Active Mac Address field in H.H.H format, where H is a 16-bit hexadecimal digit.
To manually assign a MAC address to this interface, enter a MAC address in the Active Mac Address field in H.H.H format, where H is a 16-bit hexadecimal digit.
For example, the MAC address 00-0C-F1-42-4C-DE would be entered as 000C.F142.4CDE. The first two bytes of a manual MAC address cannot be A2 if you also want to use auto-generated MAC addresses.
Step 6![]() If you use failover, enter the standby MAC address in the Standby Mac Address field. If the active unit fails over and the standby unit becomes active, the new active unit starts using the active MAC addresses to minimize network disruption, while the old active unit uses the standby address.
If you use failover, enter the standby MAC address in the Standby Mac Address field. If the active unit fails over and the standby unit becomes active, the new active unit starts using the active MAC addresses to minimize network disruption, while the old active unit uses the standby address.
Step 7![]() To set the TCP MSS, choose Configuration > Firewall > Advanced > TCP Options. Set the following options:
To set the TCP MSS, choose Configuration > Firewall > Advanced > TCP Options. Set the following options:
- Force Maximum Segment Size for TCP—Sets the maximum TCP segment size in bytes, between 48 and any maximum number. The default value is 1380 bytes. You can disable this feature by setting the bytes to 0.
- Force Minimum Segment Size for TCP — Overrides the maximum segment size to be no less than the number of bytes you set, between 48 and any maximum number. This feature is disabled by default (set to 0).
What to Do Next
(Optional) Configure IPv6 addressing. see Configuring IPv6 Addressing.
Configuring IPv6 Addressing
Information About IPv6
This section includes information about how to configure IPv6, and includes the following topics:
IPv6 Addressing
You can configure two types of unicast addresses for IPv6:
- Global—The global address is a public address that you can use on the public network. This address needs to be configured for each bridge group, and not per-interface. You can also configure a global IPv6 address for the management interface.
- Link-local—The link-local address is a private address that you can only use on the directly-connected network. Routers do not forward packets using link-local addresses; they are only for communication on a particular physical network segment. They can be used for address configuration or for the ND functions such as address resolution and neighbor discovery. Because the link-local address is only available on a segment, and is tied to the interface MAC address, you need to configure the link-local address per interface.
At a minimum, you need to configure a link-local address for IPv6 to operate. If you configure a global address, a link-local addresses is automatically configured on each interface, so you do not also need to specifically configure a link-local address. If you do not configure a global address, then you need to configure the link-local address, either automatically or manually.
Modified EUI-64 Interface IDs
RFC 3513: Internet Protocol Version 6 (IPv6) Addressing Architecture requires that the interface identifier portion of all unicast IPv6 addresses, except those that start with binary value 000, be 64 bits long and be constructed in Modified EUI-64 format. The ASA can enforce this requirement for hosts attached to the local link.
When this feature is enabled on an interface, the source addresses of IPv6 packets received on that interface are verified against the source MAC addresses to ensure that the interface identifiers use the Modified EUI-64 format. If the IPv6 packets do not use the Modified EUI-64 format for the interface identifier, the packets are dropped and the following system log message is generated:
The address format verification is only performed when a flow is created. Packets from an existing flow are not checked. Additionally, the address verification can only be performed for hosts on the local link. Packets received from hosts behind a router will fail the address format verification, and be dropped, because their source MAC address will be the router MAC address and not the host MAC address.
Unsupported Commands
The following IPv6 commands are not supported in transparent firewall mode, because they require router capabilities:
Configuring a Global IPv6 Address
To configure a global IPv6 address for a bridge group or management interface, perform the following steps.

Note![]() Configuring the global address automatically configures the link-local address, so you do not need to configure it separately.
Configuring the global address automatically configures the link-local address, so you do not need to configure it separately.
Restrictions
Prerequisites
–![]() ASA 5512-X and higher—Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)”
ASA 5512-X and higher—Chapter12, “Basic Interface Configuration (ASA 5512-X and Higher)”
–![]() ASA 5505—Chapter13, “Basic Interface Configuration (ASA 5505)”
ASA 5505—Chapter13, “Basic Interface Configuration (ASA 5505)”
–![]() ASASM—Chapter2, “Switch Configuration for the ASA Services Module”
ASASM—Chapter2, “Switch Configuration for the ASA Services Module”
–![]() ASAv—Chapter14, “Basic Interface Configuration (ASAv)”
ASAv—Chapter14, “Basic Interface Configuration (ASAv)”
- In multiple context mode, you can only configure context interfaces that you already assigned to the context in the system configuration according to Configuring Multiple Contexts.
- In multiple context mode, complete this procedure in the context execution space. To change from the system to a context configuration, in the Configuration > Device List pane, double-click the context name under the active device IP address.
Detailed Steps
Step 1![]() Choose the Configuration > Device Setup > Interfaces pane.
Choose the Configuration > Device Setup > Interfaces pane.
Step 2![]() Choose a BVI or management interface, and click Edit.
Choose a BVI or management interface, and click Edit.
The Edit Interface dialog box appears with the General tab selected.
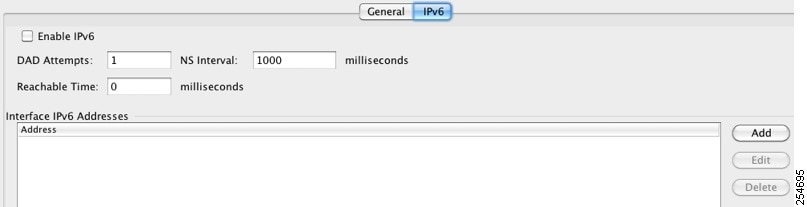
Step 4![]() Check the Enable IPv6 check box.
Check the Enable IPv6 check box.
Step 5![]() (Optional) To enforce the use of Modified EUI-64 format interface identifiers in IPv6 addresses on a local link, check the Enforce EUI-64 check box.
(Optional) To enforce the use of Modified EUI-64 format interface identifiers in IPv6 addresses on a local link, check the Enforce EUI-64 check box.
see Modified EUI-64 Interface IDs for more information.
Step 6![]() (Optional) In the top area, customize the IPv6 configuration by referring to Chapter32, “IPv6 Neighbor Discovery”
(Optional) In the top area, customize the IPv6 configuration by referring to Chapter32, “IPv6 Neighbor Discovery”
Step 7![]() To configure the global IPv6 address:
To configure the global IPv6 address:
a.![]() In the Interface IPv6 Addresses area, click Add.
In the Interface IPv6 Addresses area, click Add.
The Add IPv6 Address for Interface dialog box appears.

b.![]() In the Address/Prefix Length field, enter the global IPv6 address and the IPv6 prefix length. For example, 2001:0DB8::BA98:0:3210/48. see IPv6 Addresses for more information about IPv6 addressing.
In the Address/Prefix Length field, enter the global IPv6 address and the IPv6 prefix length. For example, 2001:0DB8::BA98:0:3210/48. see IPv6 Addresses for more information about IPv6 addressing.
You return to the Configuration > Device Setup > Interfaces pane.
Configuring IPv6 Neighbor Discovery
See “IPv6 Neighbor Discovery,” to configure IPv6 neighbor discovery.
(Optional) Configuring the Link-Local Addresses Automatically
If you do not want to configure a global address, and only need to configure a link-local address, you have the option of generating the link-local addresses based on the interface MAC addresses (Modified EUI-64 format. Because MAC addresses use 48 bits, additional bits must be inserted to fill the 64 bits required for the interface ID.)
To manually assign the link-local address (not recommended), see (Optional) Configuring the Link-Local Addresses Manually.
For other IPv6 options, including enforcing the Modified EUI-64 format, and DAD settings, see Configuring a Global IPv6 Address.
To automatically configure the link-local addresses for a management interface or bridge group member interfaces, perform the following steps:
Step 1![]() Choose the Configuration > Device Setup > Interfaces pane.
Choose the Configuration > Device Setup > Interfaces pane.
Step 2![]() Select a BVI or management interface, and click Edit.
Select a BVI or management interface, and click Edit.
The Edit Interface dialog box appears with the General tab selected.
Step 4![]() In the IPv6 configuration area, check Enable IPv6.
In the IPv6 configuration area, check Enable IPv6.
This option enables IPv6 and automatically generates the link-local addresses for member interfaces using the Modified EUI-64 interface ID based on the interface MAC address.
(Optional) Configuring the Link-Local Addresses Manually
If you do not want to configure a global address, and only need to configure a link-local address on the physical interfaces or subinterfaces, you have the option of manually defining the link-local address. Note that we recommend automatically assigning the link-local address based on the Modified EUI-64 format. For example, if other devices enforce the use of the Modified EUI-64 format, then a manually-assigned link-local address may cause packets to be dropped.
To automatically assign the link-local address (recommended), see (Optional) Configuring the Link-Local Addresses Automatically.
For other IPv6 options, including enforcing the Modified EUI-64 format, and DAD settings, see Configuring a Global IPv6 Address.
To assign a link-local address to a physical interface or subinterface, including the management interface, perform the following steps:
Step 1![]() Choose the Configuration > Device Setup > Interfaces pane.
Choose the Configuration > Device Setup > Interfaces pane.
Step 2![]() Select an interface, and click Edit.
Select an interface, and click Edit.
The Edit Interface dialog box appears with the General tab selected.
Step 4![]() To set the link-local address, enter an address in the Link-local address field.
To set the link-local address, enter an address in the Link-local address field.
A link-local address should start with FE8, FE9, FEA, or FEB, for example fe80::20d:88ff:feee:6a82. see IPv6 Addresses for more information about IPv6 addressing.
Allowing Same Security Level Communication
By default, interfaces on the same security level cannot communicate with each other, and packets cannot enter and exit the same interface. This section describes how to enable inter-interface communication when interfaces are on the same security level.
Information About Inter-Interface Communication
Allowing interfaces on the same security level to communicate with each other is useful if you want traffic to flow freely between all same security interfaces without ACLs.
If you enable same security interface communication, you can still configure interfaces at different security levels as usual.
Detailed Steps
To enable interfaces on the same security level to communicate with each other, from the Configuration > Interfaces pane, check Enable traffic between two or more interfaces which are configured with same security level.
Turning Off and Turning On Interfaces
This section describes how to turn off and on an interface.
All interfaces are enabled by default. In multiple context mode, if you disable or reenable the interface within a context, only that context interface is affected. But if you disable or reenable the interface in the system execution space, then you affect that interface for all contexts.
Detailed Steps
Step 1![]() Depending on your context mode:
Depending on your context mode:
By default, all physical interfaces are listed.
Step 2![]() Click a VLAN interface that you want to configure, and click Edit.
Click a VLAN interface that you want to configure, and click Edit.
The Edit Interface dialog box appears.
Step 3![]() To enable or disable the interface, check or uncheck the Enable Interface check box.
To enable or disable the interface, check or uncheck the Enable Interface check box.
Monitoring Interfaces
This section includes the following topics:
ARP Table
The Monitoring > Interfaces > ARP Table pane displays the ARP table, including static and dynamic entries. The ARP table includes entries that map a MAC address to an IP address for a given interface.
- Interface —Lists the interface name associated with the mapping.
- IP Address —Shows the IP address.
- MAC Address —Shows the MAC address.
- Proxy ARP—Displays Yes if proxy ARP is enabled on the interface. Displays No if proxy ARP is not enabled on the interface.
- Clear —Clears the dynamic ARP table entries. Static entries are not cleared.
- Refresh —Refreshes the table with current information from the ASA and updates Last Updated date and time.
- Last Updated — Display only . Shows the date and time the display was updated.
DHCP
The ASA lets you monitor DHCP status, including the addresses assigned to clients, the lease information for a ASA interface, and DHCP statistics.
DHCP Server Table
The Monitoring > Interfaces > DHCP > DHCP Server Table lists the IP addresses assigned to DHCP clients.
- IP Address—Shows the IP address assigned to the client.
- Client-ID—Shows the client MAC address or ID.
- Lease Expiration—Shows the date that the DHCP lease expires. The lease indicates how long the client can use the assigned IP address. Remaining time is also specified in the number of seconds and is based on the timestamp in the Last Updated display-only field.
- Number of Active Leases—Shows the total number of DHCP leases.
- Refresh—Refreshes the information from the ASA.
- Last Updated—Shows when the data in the table was last updated.
DHCP Client Lease Information
If you obtain the ASA interface IP address from a DHCP server, the Monitoring > Interfaces > DHCP > DHCP Server Table > DHCP Client Lease Information pane shows information about the DHCP lease.
- Select an interface—Lists the ASA interfaces. Choose the interface for which you want to view the DHCP lease. If an interface has multiple DHCP leases, then choose the interface and IP address pair you want to view.
- Attribute and Value—Lists the attributes and values of the interface DHCP lease.
–![]() Temp IP addr— Display only. The IP address assigned to the interface.
Temp IP addr— Display only. The IP address assigned to the interface.
–![]() Temp sub net mask— Display only. The subnet mask assigned to the interface.
Temp sub net mask— Display only. The subnet mask assigned to the interface.
–![]() DHCP lease server— Display only. The DHCP server address.
DHCP lease server— Display only. The DHCP server address.
–![]() state— Display only. The state of the DHCP lease, as follows:
state— Display only. The state of the DHCP lease, as follows:
Initial—The initialization state, where the ASA begins the process of acquiring a lease. This state is also shown when a lease ends or when a lease negotiation fails.
Selecting—The ASA is waiting to receive DHCPOFFER messages from one or more DHCP servers, so it can choose one.
Requesting—The ASA is waiting to hear back from the server to which it sent its request.
Purging—The ASA is removing the lease because of an error.
Bound—The ASA has a valid lease and is operating normally.
Renewing—The ASA is trying to renew the lease. It regularly sends DHCPREQUEST messages to the current DHCP server, and waits for a reply.
Rebinding—The ASA failed to renew the lease with the original server, and now sends DHCPREQUEST messages until it gets a reply from any server or the lease ends.
Holddown—The ASA started the process to remove the lease.
Releasing—The ASA sends release messages to the server indicating that the IP address is no longer needed.
–![]() Lease— Display only. The length of time, specified by the DHCP server, that the interface can use this IP address.
Lease— Display only. The length of time, specified by the DHCP server, that the interface can use this IP address.
–![]() Renewal— Display only. The length of time until the interface automatically attempts to renew this lease.
Renewal— Display only. The length of time until the interface automatically attempts to renew this lease.
–![]() Rebind— Display only. The length of time until the ASA attempts to rebind to a DHCP server. Rebinding occurs if the ASA cannot communicate with the original DHCP server, and 87.5 percent of the lease time has expired. The ASA then attempts to contact any available DHCP server by broadcasting DHCP requests.
Rebind— Display only. The length of time until the ASA attempts to rebind to a DHCP server. Rebinding occurs if the ASA cannot communicate with the original DHCP server, and 87.5 percent of the lease time has expired. The ASA then attempts to contact any available DHCP server by broadcasting DHCP requests.
–![]() Next timer fires after— Display only. The number of seconds until the internal timer triggers.
Next timer fires after— Display only. The number of seconds until the internal timer triggers.
–![]() Retry count— Display only. If the ASA is attempting to establish a lease, this field shows the number of times the ASA tried sending a DHCP message. For example, if the ASA is in the Selecting state, this value shows the number of times the ASA sent discover messages. If the ASA is in the Requesting state, this value shows the number of times the ASA sent request messages.
Retry count— Display only. If the ASA is attempting to establish a lease, this field shows the number of times the ASA tried sending a DHCP message. For example, if the ASA is in the Selecting state, this value shows the number of times the ASA sent discover messages. If the ASA is in the Requesting state, this value shows the number of times the ASA sent request messages.
–![]() Client-ID— Display only. The client ID used in all communication with the server.
Client-ID— Display only. The client ID used in all communication with the server.
–![]() Proxy— Display only. Specifies if this interface is a proxy DHCP client for VPN clients, True or False.
Proxy— Display only. Specifies if this interface is a proxy DHCP client for VPN clients, True or False.
DHCP Statistics
The Monitoring > Interfaces > DHCP > DHCP Statistics pane shows statistics for the DHCP server feature.
- Count—Shows the number of times a specific message was processed.
- Direction—Shows if the message type is Sent or Received.
- Total Messages Received—Shows the total number of messages received by the ASA.
- Total Messages Sent—Shows the total number of messages sent by the ASA.
- Counter—Shows general statistical DHCP data, including the following:
MAC Address Table
The Monitoring > Interfaces > MAC Address Table pane shows the static and dynamic MAC address entries. see MAC Address Table for more information about the MAC address table and adding static entries.
- Interface—Shows the interface name associated with the entry.
- MAC Address—Shows the MAC address.
- Type—Shows if the entry is static or dynamic.
- Age—Shows the age of the entry, in minutes. To set the timeout, see MAC Address Table.
- Refresh—Refreshes the table with current information from the ASA.
Dynamic ACLs
The Monitoring > Interfaces > Dynamic ACLs pane shows a table of the Dynamic ACLs, which are functionally identical to the user-configured ACLs except that they are created, activated and deleted automatically by the ASA. These ACLs do not show up in the configuration and are only visible in this table. They are identified by the “(dynamic)” keyword in the ACL header.
When you choose an ACL in this table, the contents of the ACL are shown in the bottom text field.
Interface Graphs
The Monitoring > Interfaces > Interface Graphs pane lets you view interface statistics in graph or table form. If an interface is shared among contexts, the ASA shows only statistics for the current context. The number of statistics shown for a subinterface is a subset of the number of statistics shown for a physical interface.
- Available Graphs for—Lists the types of statistics available for monitoring. You can choose up to four types of statistics to show in one graph window. You can open multiple graph windows at the same time.
–![]() Byte Counts—Shows the number of bytes input and output on the interface.
Byte Counts—Shows the number of bytes input and output on the interface.
–![]() Packet Counts—Shows the number of packets input and output on the interface.
Packet Counts—Shows the number of packets input and output on the interface.
–![]() Packet Rates—Shows the rate of packets input and output on the interface.
Packet Rates—Shows the rate of packets input and output on the interface.
–![]() Bit Rates—Shows the bit rate for the input and output of the interface.
Bit Rates—Shows the bit rate for the input and output of the interface.
–![]() Drop Packet Count—Shows the number of packets dropped on the interface.
Drop Packet Count—Shows the number of packets dropped on the interface.
These additional statistics display for physical interfaces:
–![]() Buffer Resources—Shows the following statistics:
Buffer Resources—Shows the following statistics:
Overruns—The number of times that the ASA was incapable of handing received data to a hardware buffer because the input rate exceeded the ASA capability to handle the data.
Underruns—The number of times that the transmitter ran faster than the ASA could handle.
No Buffer—The number of received packets discarded because there was no buffer space in the main system. Compare this with the ignored count. Broadcast storms on Ethernet networks are often responsible for no input buffer events.
–![]() Packet Errors—Shows the following statistics:
Packet Errors—Shows the following statistics:
CRC—The number of Cyclical Redundancy Check errors. When a station sends a frame, it appends a CRC to the end of the frame. This CRC is generated from an algorithm based on the data in the frame. If the frame is altered between the source and destination, the ASA notes that the CRC does not match. A high number of CRCs is usually the result of collisions or a station transmitting bad data.
Frame—The number of frame errors. Bad frames include packets with an incorrect length or bad frame checksums. This error is usually the result of collisions or a malfunctioning Ethernet device.
Input Errors—The number of total input errors, including the other types listed here. Other input-related errors can also cause the input error count to increase, and some datagrams might have more than one error; therefore, this sum might exceed the number of errors listed for the other types.
Runts—The number of packets that are discarded because they are smaller than the minimum packet size, which is 64 bytes. Runts are usually caused by collisions. They might also be caused by poor wiring and electrical interference.
Giants—The number of packets that are discarded because they exceed the maximum packet size. For example, any Ethernet packet that is greater than 1518 bytes is considered a giant.
Deferred—For FastEthernet interfaces only. The number of frames that were deferred before transmission due to activity on the link.
–![]() Miscellaneous—Shows statistics for received broadcasts.
Miscellaneous—Shows statistics for received broadcasts.
–![]() Collision Counts—For FastEthernet interfaces only. Shows the following statistics:
Collision Counts—For FastEthernet interfaces only. Shows the following statistics:
Output Errors—The number of frames not transmitted because the configured maximum number of collisions was exceeded. This counter should only increment during heavy network traffic.
Collisions—The number of messages retransmitted due to an Ethernet collision (single and multiple collisions). This usually occurs on an overextended LAN (Ethernet or transceiver cable too long, more than two repeaters between stations, or too many cascaded multiport transceivers). A packet that collides is counted only once by the output packets.
Late Collisions—The number of frames that were not transmitted because a collision occurred outside the normal collision window. A late collision is a collision that is detected late in the transmission of the packet. Normally, these should never happen. When two Ethernet hosts try to talk at once, they should collide early in the packet and both back off, or the second host should see that the first one is talking and wait. If you get a late collision, a device is jumping in and trying to send the packet on the Ethernet while the ASA is partly finished sending the packet. The ASA does not resend the packet, because it may have freed the buffers that held the first part of the packet. This is not a real problem because networking protocols are designed to cope with collisions by resending packets. However, late collisions indicate a problem exists in your network. Common problems are large repeated networks and Ethernet networks running beyond the specification.
–![]() Input Queue—Shows the number of packets in the input queue, the current and the maximum, including the following statistics:
Input Queue—Shows the number of packets in the input queue, the current and the maximum, including the following statistics:
Hardware Input Queue—The number of packets in the hardware queue.
Software Input Queue—The number of packets in the software queue.
–![]() Output Queue—Shows the number of packets in the output queue, the current and the maximum, including the following statistics:
Output Queue—Shows the number of packets in the output queue, the current and the maximum, including the following statistics:
Hardware Output Queue—The number of packets in the hardware queue.
Software Output Queue—The number of packets in the software queue.
- Add—Adds the selected statistic type to the selected graph window.
- Remove—Removes the selected statistic type from the selected graph window. This button name changes to Delete if the item you are removing was added from another panel, and is not being returned to the Available Graphs pane.
- Show Graphs—Shows the graph window name to which you want to add a statistic type. If you have a graph window already open, a new graph window is listed by default. If you want to add a statistic type to an already open graph, choose the open graph window name. The statistics already included on the graph are shown in the Selected Graphs pane, to which you can add additional types. Graph windows are named for ASDM followed by the interface IP address and the name “Graph”. Subsequent graphs are named “Graph (2)” and so on.
- Selected Graphs—Shows the statistic types you want to show in the selected graph window. You an include up to four types.
–![]() Show Graphs—Shows the graph window or updates the graph with additional statistic types if added.
Show Graphs—Shows the graph window or updates the graph with additional statistic types if added.
Graph/Table
The Mon itoring > Interfaces > Interface Graphs > Graph/Table window shows a graph for the selected statistics. The Graph window can show up to four graphs and tables at a time. By default, the graph or table displays the real-time statistics. If you enable History Metrics (see Enabling History Metrics), you can view statistics for past time periods.
- View—Sets the time period for the graph or table. To view any time period other than real-time, enable History Metrics (see Enabling History Metrics). The data is updated according to the specification of the following options:
–![]() Real-time, data every 10 sec
Real-time, data every 10 sec
–![]() Last 10 minutes, data every 10 sec
Last 10 minutes, data every 10 sec
–![]() Last 60 minutes, data every 1 min
Last 60 minutes, data every 1 min
–![]() Last 12 hours, data every 12 min
Last 12 hours, data every 12 min
–![]() Last 5 days, data every 2 hours
Last 5 days, data every 2 hours
- Export—Exports the graph in comma-separated value format. If there is more than one graph or table on the Graph window, the Export Graph Data dialog box appears. Choose one or more of the graphs and tables listed by checking the box next to the name.
- Print—Prints the graph or table. If there is more than one graph or table on the Graph window, the Print Graph dialog box appears. Choose the graph or table you want to print from the Graph/Table Name list.
- Bookmark—Opens a browser window with a single link for all graphs and tables on the Graphs window, as well as individual links for each graph or table. You can then copy these URLs as bookmarks in your browser. ASDM does not have to be running when you open the URL for a graph; the browser launches ASDM and then displays the graph.
PPPoE Client
The Monitoring > Interfaces > PPPoE Client > PPPoE Client Lease Information pane displays information about current PPPoE connections.
Select a PPPoE interface—Select an interface that you want to view PPPoE client lease information.
Refresh—loads the latest PPPoE connection information from the ASA for display.
Interface Connection
The Monitoring > Interfaces > interface connection node in the Monitoring > Interfaces tree only appears if static route tracking is configured. If you have several routes tracked, there will be a node for each interface that contains a tracked route.
See the following for more information about the route tracking information available:
Track Status for
The Monitoring > Interfaces > interface connection > Track Status for pane displays information about the tracked object.
Monitoring Statistics for
The Monitoring > Interfaces > interface connection > Monitoring Statistics for pane displays statistics for the SLA monitoring process.
Feature History for Interfaces in Transparent Mode
Table 16-1 lists each feature change and the platform release in which it was implemented. ASDM is backwards-compatible with multiple platform releases, so the specific ASDM release in which support was added is not listed.
 Feedback
Feedback