About Device Management
Use the management center to manage your devices.
About the Management Center and Device Management
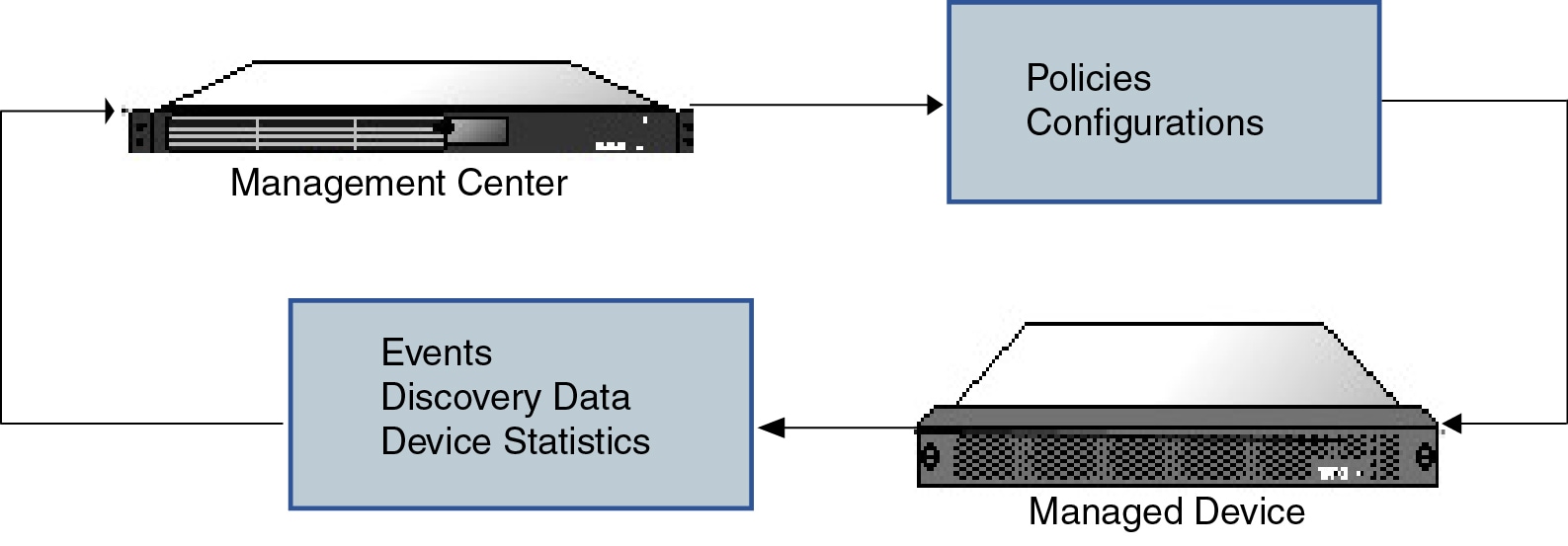
When the management center manages a device, it sets up a two-way, SSL-encrypted communication channel between itself and the device. The management center uses this channel to send information to the device about how you want to analyze and manage your network traffic to the device. As the device evaluates the traffic, it generates events and sends them to the management center using the same channel.
By using the management center to manage devices, you can:
-
configure policies for all your devices from a single location, making it easier to change configurations
-
install various types of software updates on devices
-
push health policies to your managed devices and monitor their health status from the management center
 Note |
If you have a CDO-managed device and are using the on-prem management center for analytics only, then the on-prem management center does not support policy configuration or upgrading. Chapters and procedures in this guide related to device configuration and other unsupported features do not apply to devices whose primary manager is CDO. |
The management center aggregates and correlates intrusion events, network discovery information, and device performance data, allowing you to monitor the information that your devices are reporting in relation to one another, and to assess the overall activity occurring on your network.
You can use the management center to manage nearly every aspect of a device’s behavior.
 Note |
Although the management center can manage devices running certain previous releases as specified in the compatibility matrix available at http://www.cisco.com/c/en/us/support/security/defense-center/products-device-support-tables-list.html, new features that require the latest version of threat defense software are not available to these previous-release devices. Some management center features may be available for earlier versions. |
What Can Be Managed by a Secure Firewall Management Center?
You can use the Secure Firewall Management Center as a central management point to manage threat defense devices.
When you manage a device, information is transmitted between the management center and the device over a secure, TLS-1.3-encrypted communication channel. You do not need to run this traffic over an additional encrypted tunnel such as Site-to-Site VPN for security purposes. If the VPN goes down, for example, you will lose your management connection, so we recommend a simple management path.
The following illustration lists what is transmitted between the management center and its managed devices. Note that the types of events and policies that are sent between the appliances are based on the device type.
About the Management Connection
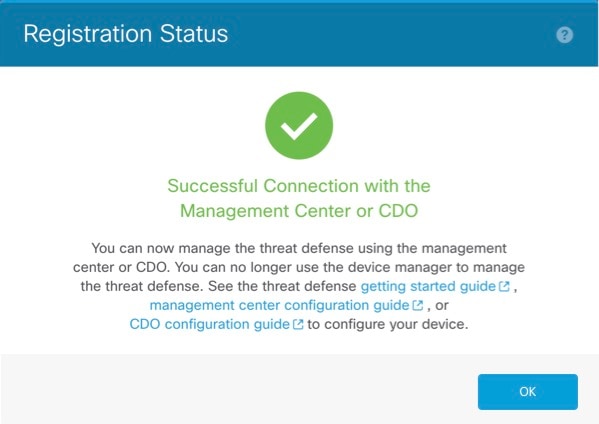
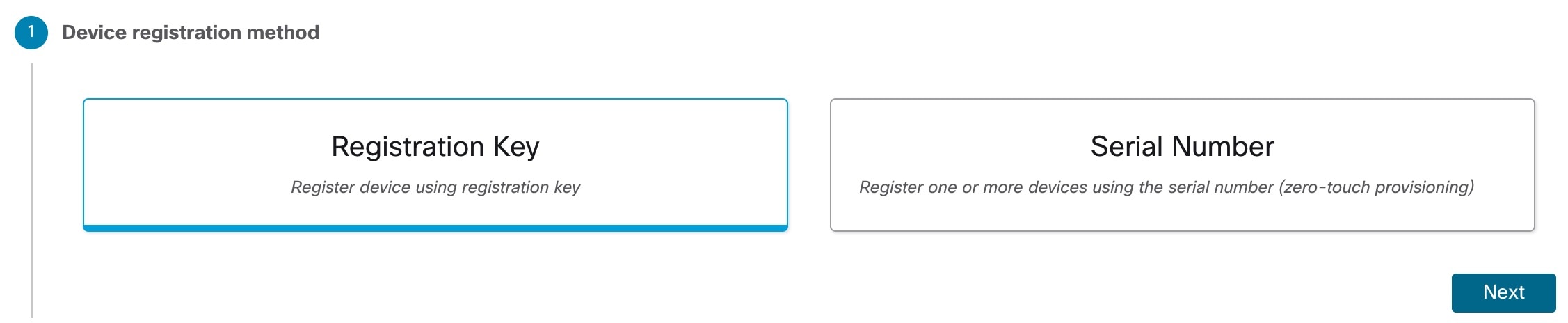
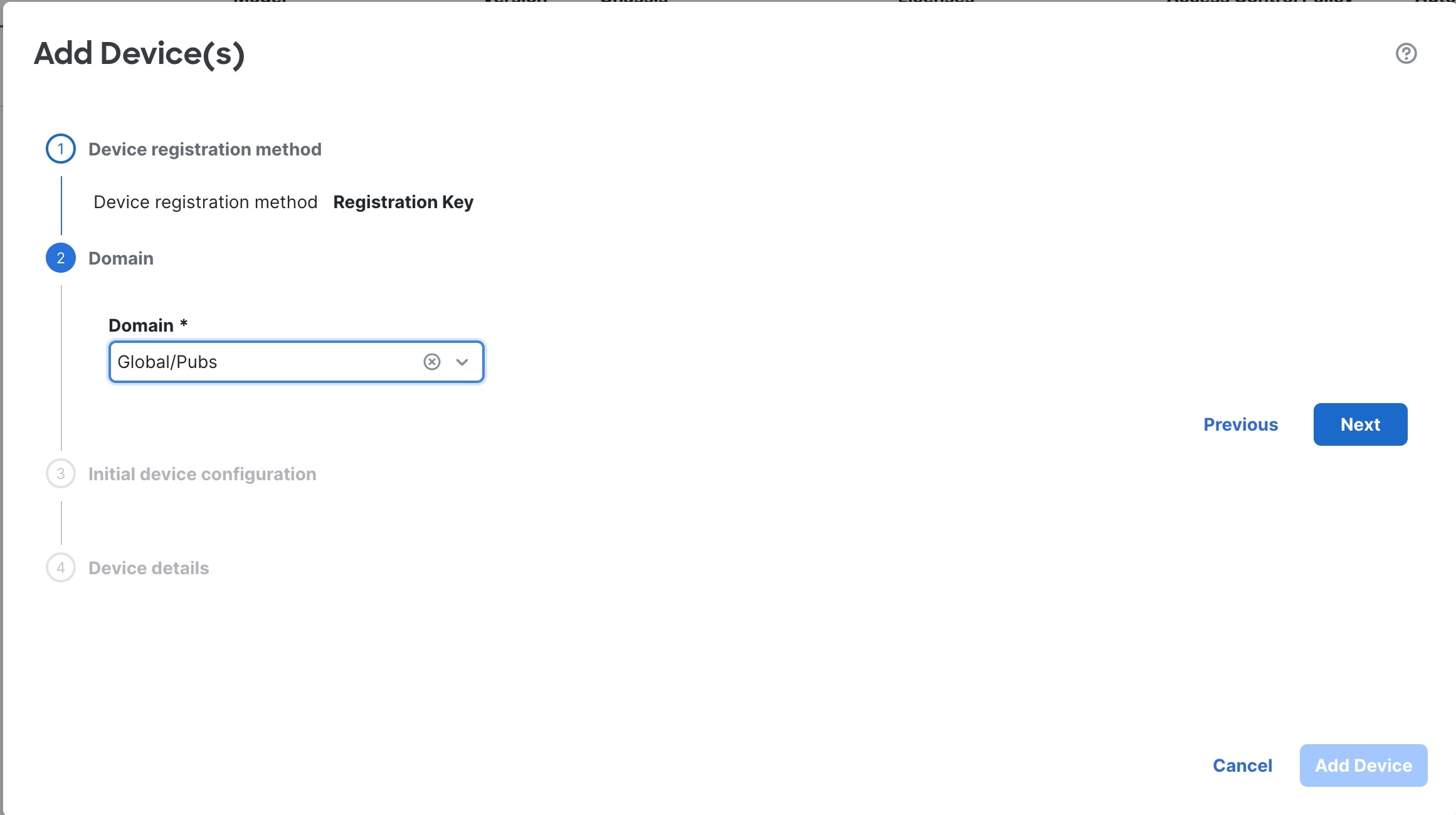
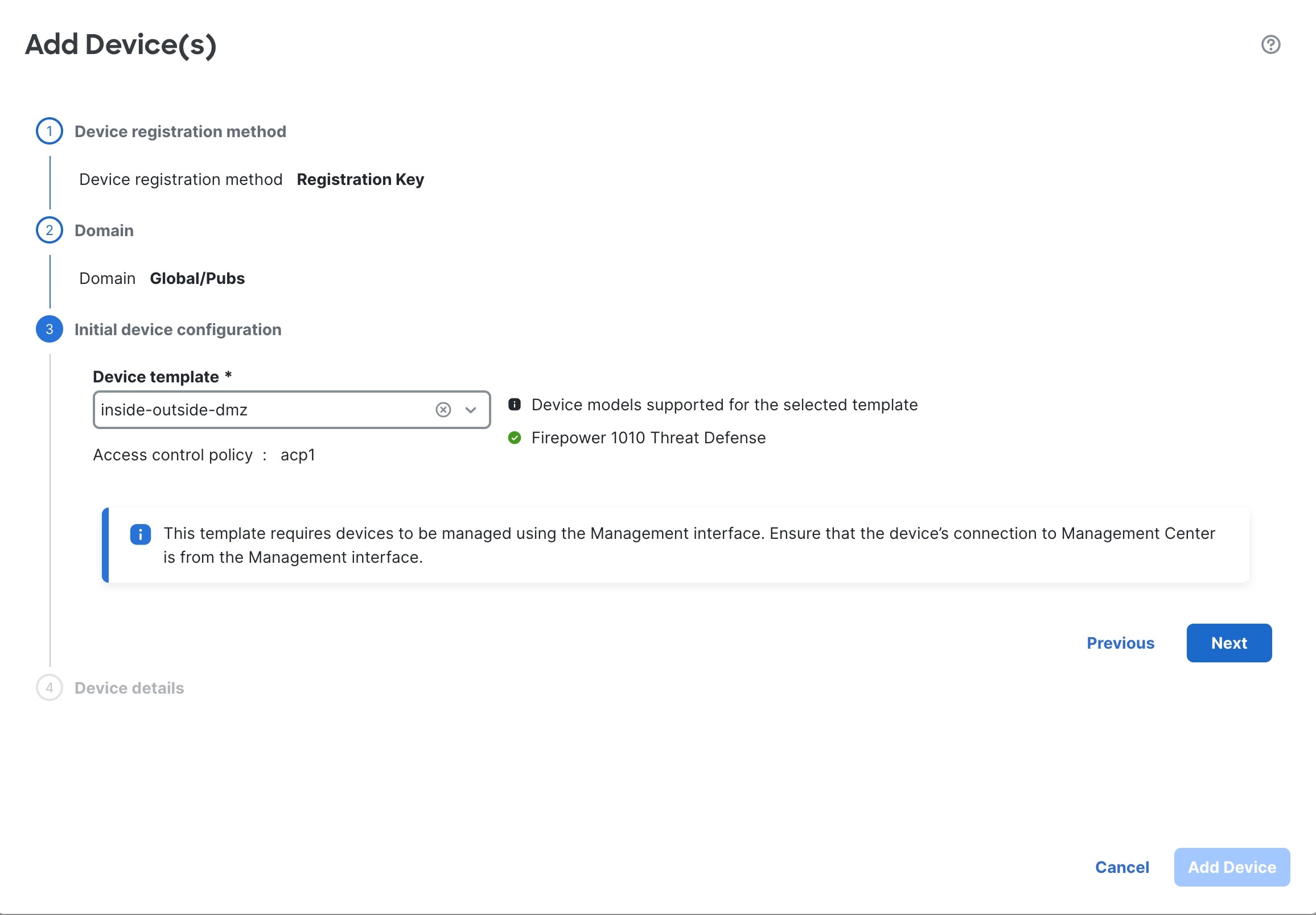
After you configure the device with the management center information and after you add the device to the management center, either the device or the management center can establish the management connection. Depending on initial setup:
-
Either the device or the management center can initiate.
-
Only the device can initiate.
-
Only the management center can initiate.
Initiation always originates with eth0 on the management center or with the lowest-numbered management interface on the device. Additional management interfaces are tried if the connection is not established. Multiple management interfaces on the management center let you connect to discrete networks or to segregate management and event traffic. However, the initiator does not choose the best interface based on the routing table.
Make sure the management connection is stable, without excessive packet loss, with at least 5 Mbps throughput. By default, the management connection uses TCP port 8305 (this port is configurable). If you place another threat defense between devices and the management center, to prevent potential management disruption, be sure to exempt management traffic from deep inspection by applying a prefilter policy for it.
 Note |
The management connection is a secure, TLS-1.3-encrypted communication channel between itself and the device. You do not need to run this traffic over an additional encrypted tunnel such as Site-to-Site VPN for security purposes. If the VPN goes down, for example, you will lose your management connection, so we recommend a simple management path. |
Beyond Policies and Events
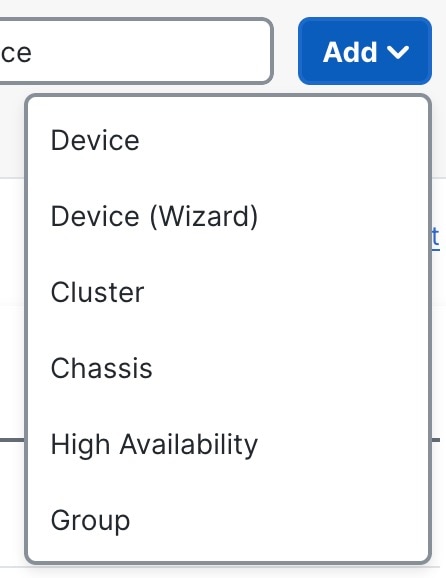
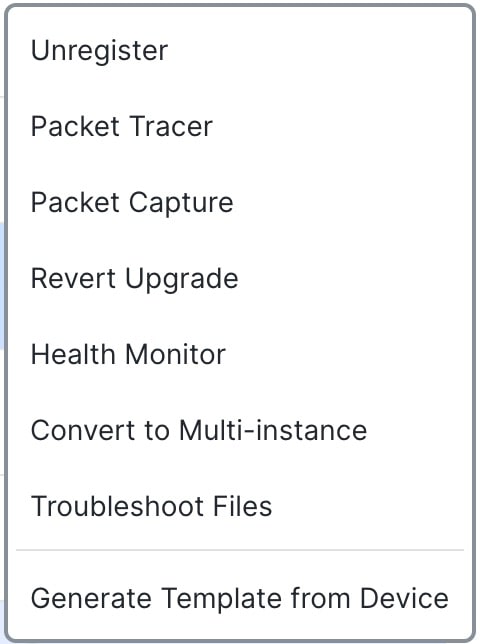
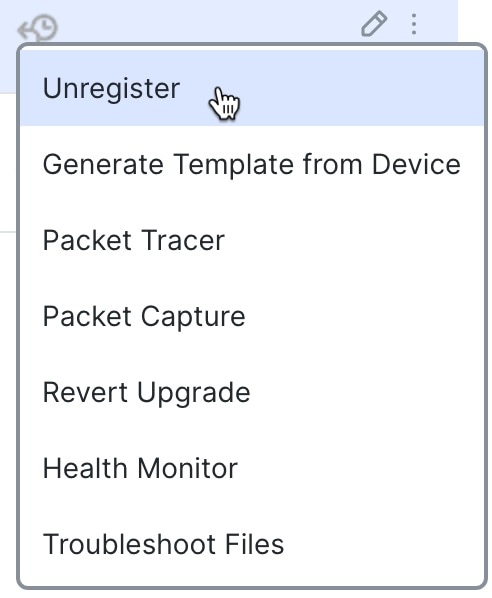
In addition to deploying policies to devices and receiving events from them, you can also perform other device-related tasks on the management center.
Backing Up a Device
You cannot backup a physical managed device from the FTD CLI. To back up configuration data, and, optionally, unified files, perform a backup of the device using the management center that is managing the device.
To back up event data, perform a backup of the management center that is managing the device.
Updating Devices
From time to time, Cisco releases updates to the Firepower System, including:
-
intrusion rule updates, which may contain new and updated intrusion rules
-
vulnerability database (VDB) updates
-
geolocation updates
-
software patches and updates
You can use the management center to install an update on the devices it manages.
About Device Management Interfaces
Each device includes a single dedicated Management interface for communicating with the management center. You can optionally configure the device to use a data interface for management instead of the dedicated Management interface.
You can perform initial setup on the management interface, or on the console port.
Management interfaces are also used to communicate with the Smart Licensing server, to download updates, and to perform other management functions.
Management and Event Interfaces on the Threat Defense
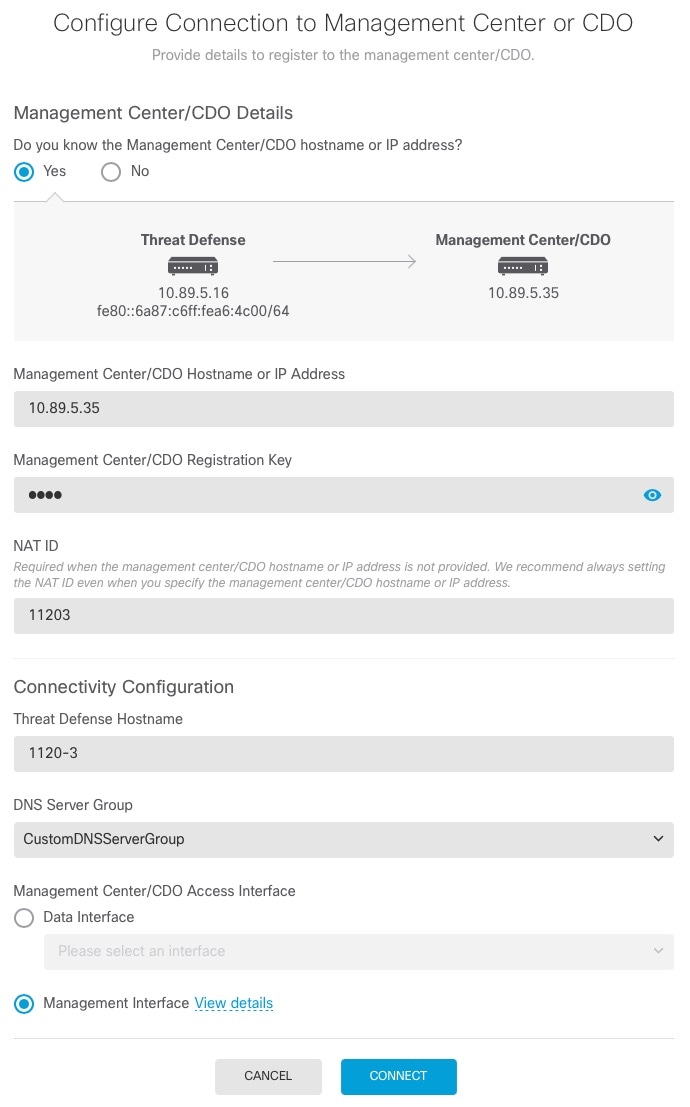
When you set up your device, you specify the management center IP address or hostname that you want to connect to, if known. In this case, the device initiates the connection, and both management and event traffic go to this address at initial registration. If the management center is not known, then the management center establishes the initial connection. In this case, it might initially connect from a different management center management interface than specified on the threat defense. Subsequent connections should use the management center management interface with the specified IP address.
If the management center has a separate event-only interface, the managed device sends subsequent event traffic to the management center event-only interface if the network allows. In addition, some managed-device models include an additional management interface that you can configure for event-only traffic. Note that if you configure a data interface for management, you cannot use separate management and event interfaces. If the event network goes down, then event traffic reverts to the regular management interfaces on the management center and/or on the managed device.
Using the Threat Defense Data Interface for Management
You can use either the dedicated Management interface or a regular data interface for communication with the management center. Manager access on a data interface is useful if you want to manage the threat defense remotely from the outside interface, or you do not have a separate management network. Moreover, using a data interface lets you configure a redundant secondary interface to take over management functions if the primary interface goes down.
Manager Access Requirements
Manager access from a data interface has the following requirements.
-
You can only enable manager access on a physical, data interface. You cannot use a subinterface or EtherChannel, nor can you create a subinterface on the manager access interface. You can also use the management center to enable manager access on a single secondary interface for redundancy.
-
This interface cannot be management-only.
-
Routed firewall mode only, using a routed interface.
-
PPPoE is not supported. If your ISP requires PPPoE, you will have to put a router with PPPoE support between the threat defense and the WAN modem.
-
The interface must be in the global VRF only.
-
SSH is not enabled by default for data interfaces, so you will have to enable SSH later using the management center. Because the Management interface gateway will be changed to be the data interfaces, you also cannot SSH to the Management interface from a remote network unless you add a static route for the Management interface using the configure network static-routes command. For threat defense virtual on Amazon Web Services, a console port is not available, so you should maintain your SSH access to the Management interface: add a static route for Management before you continue with your configuration. Alternatively, be sure to finish all CLI configuration (including the configure manager add command) before you configure the data interface for manager access and you are disconnected.
-
You cannot use separate management and event-only interfaces.
-
Clustering is not supported. You must use the Management interface in this case.
High Availability Requirements
When using a data interface with device high availability, see the following requirements.
-
Use the same data interface on both devices for manager access.
-
Redundant manager access data interface is not supported.
-
You cannot use DHCP; only a static IP address is supported. Features that rely on DHCP cannot be used, including DDNS and zero-touch provisioning.
-
Have different static IP addresses in the same subnet.
-
Use either IPv4 or IPv6; you cannot set both.
-
Use the same manager configuration (configure manager add command) to ensure that the connectivity is the same.
-
You cannot use the data interface as the failover or state link.
Management Interface Support Per Device Model
See the hardware installation guide for your model for the management interface locations.
 Note |
For the Firepower 4100/9300, the MGMT interface is for chassis management, not for threat defense logical device management. You must configure a separate interface to be of type mgmt (and/or firepower-eventing), and then assign it to the threat defense logical device. |
See the following table for supported management interfaces on each managed device model.
|
Model |
Management Interface |
Optional Event Interface |
||||
|---|---|---|---|---|---|---|
|
Firepower 1000 |
management0
|
No Support |
||||
|
Secure Firewall 1200 |
management0
|
No Support |
||||
|
Secure Firewall 3100 |
management0
|
No Support |
||||
|
Secure Firewall 4200 |
management0
|
management1
|
||||
|
Firepower 4100 and 9300 |
management0
|
management1
|
||||
|
ISA 3000 |
br1
|
No support |
||||
|
Secure Firewall Threat Defense Virtual |
eth0 |
No support |
Network Routes on Device Management Interfaces
Management interfaces (including event-only interfaces) support only static routes to reach remote networks. When you set up your managed device, the setup process creates a default route to the gateway IP address that you specify. You cannot delete this route; you can only modify the gateway address.
 Note |
The routing for management interfaces is completely separate from routing that you configure for data interfaces. If you configure a data interface for management instead of using the dedicated Management interface, traffic is routed over the backplane to use the data routing table. The information in this section does not apply. |
You can configure multiple management interfaces on some platforms (a management interface and an event-only interface). The default route does not include an egress interface, so the interface chosen depends on the gateway address you specify, and which interface's network the gateway belongs to. In the case of multiple interfaces on the default network, the device uses the lower-numbered interface as the egress interface.
At least one static route is recommended per management interface to access remote networks. We recommend placing each interface on a separate network to avoid potential routing problems, including routing problems from other devices to the threat defense.
 Note |
The interface used for management connections is not determined by the routing table. Connections are always tried using the lowest-numbered interface first. |
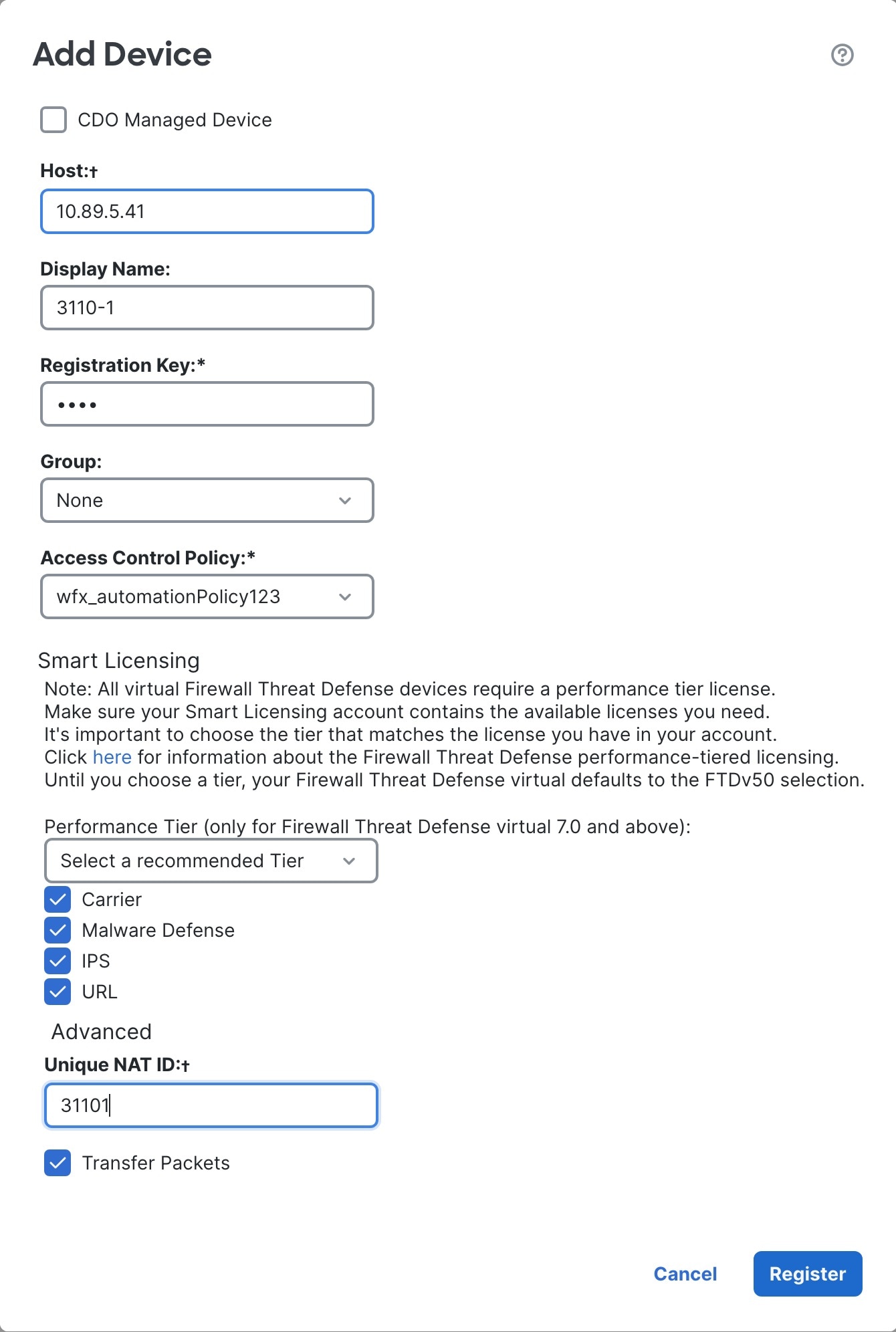
NAT Environments
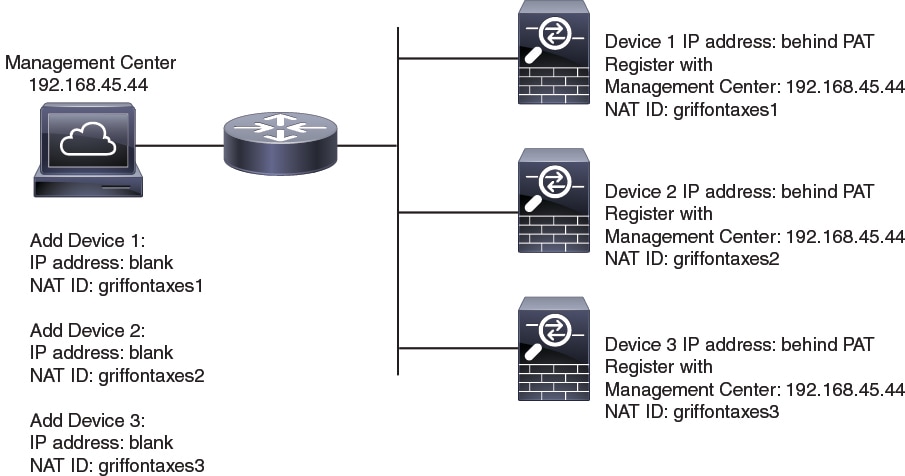
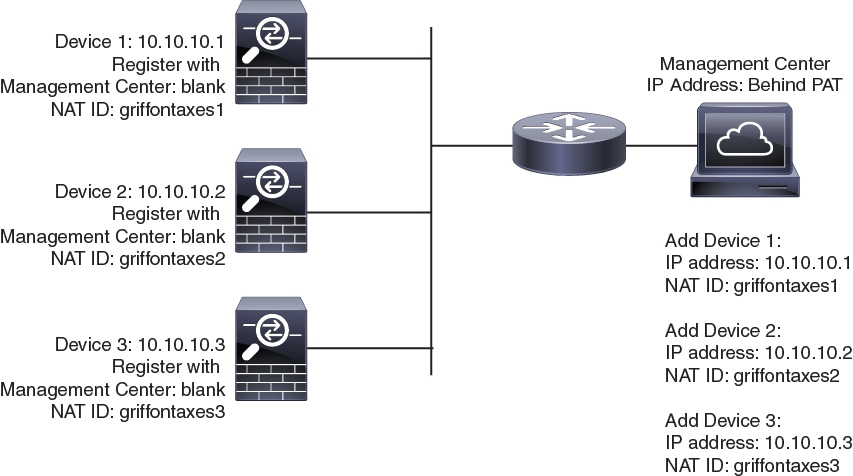
Network address translation (NAT) is a method of transmitting and receiving network traffic through a router that involves reassigning the source or destination IP address. The most common use for NAT is to allow private networks to communicate with the internet. Static NAT performs a 1:1 translation, which does not pose a problem for management center communication with devices, but port address translation (PAT) is more common. PAT lets you use a single public IP address and unique ports to access the public network; these ports are dynamically assigned as needed, so you cannot initiate a connection to a device behind a PAT router.
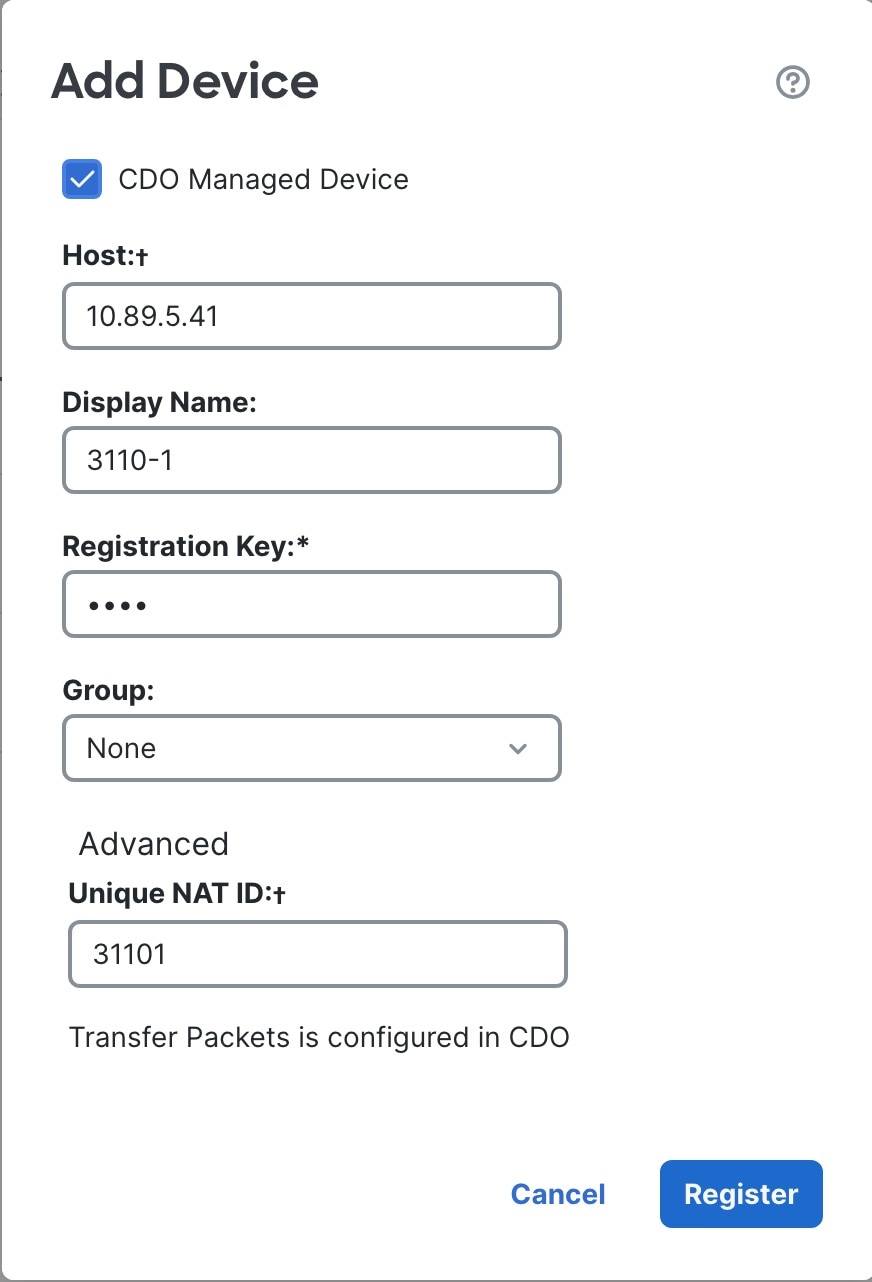
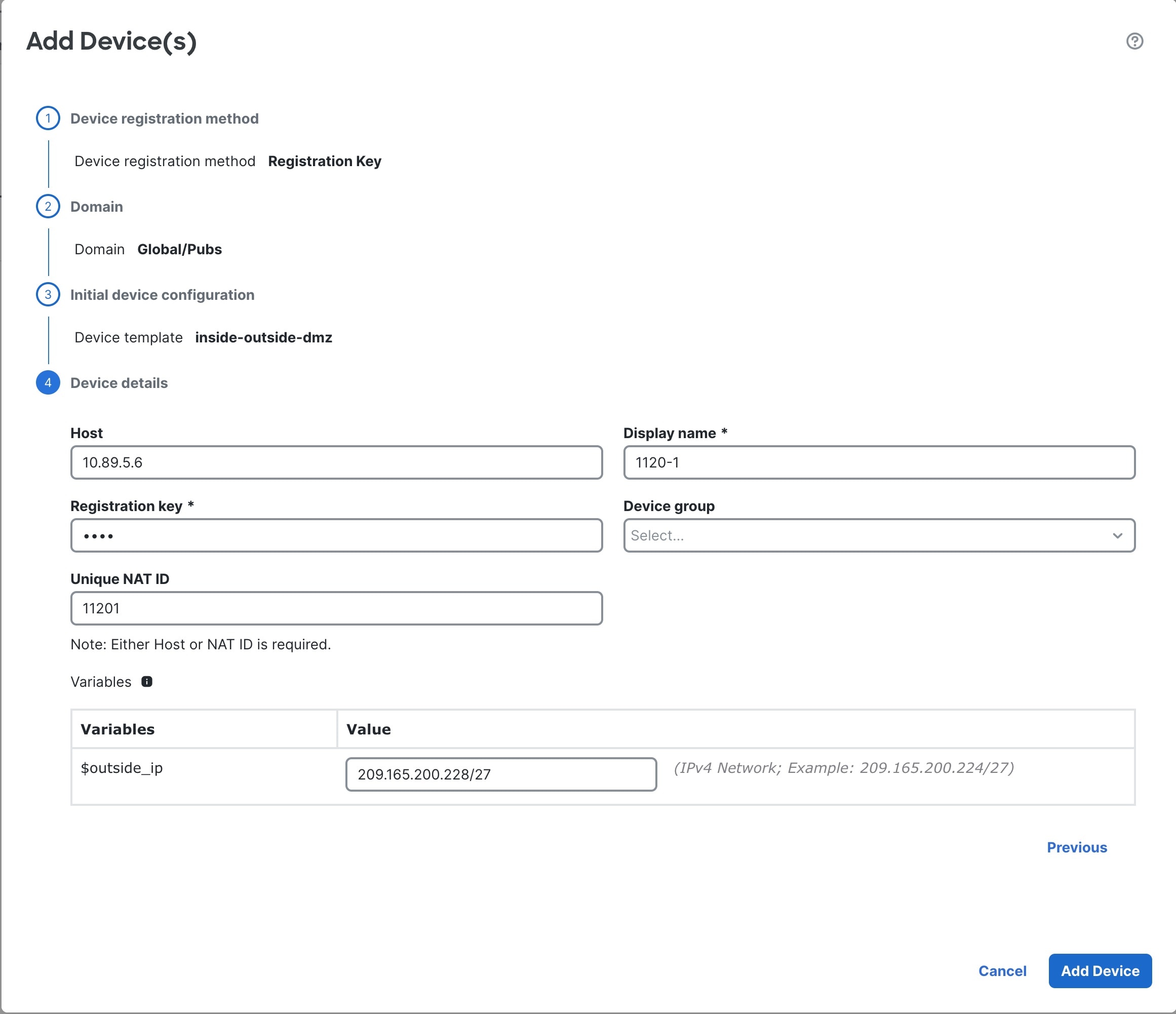
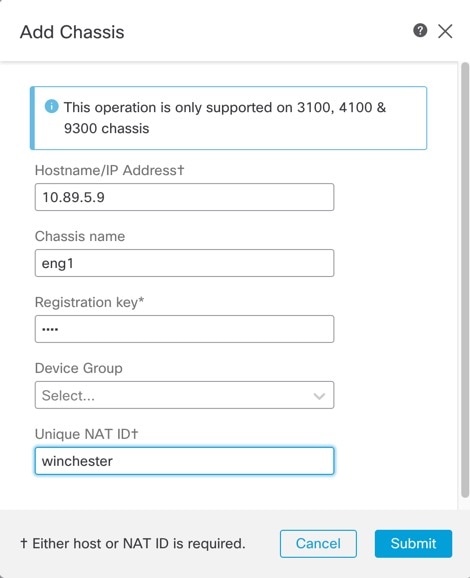
Normally, you need both IP addresses (along with a registration key) for both routing purposes and for authentication: the management center specifies the device IP address when you add a device, and the device specifies the management center IP address. However, if you only know one of the IP addresses, which is the minimum requirement for routing purposes, then you must also specify a unique NAT ID on both sides of the connection to establish trust for the initial communication and to look up the correct registration key. The management center and device use the registration key and NAT ID (instead of IP addresses) to authenticate and authorize for initial registration.
For example, you add a device to the management center, and you do not know the device IP address (for example, the device is behind a PAT router), so you specify only the NAT ID and the registration key on the management center; leave the IP address blank. On the device, you specify the management center IP address, the same NAT ID, and the same registration key. The device registers to the management center's IP address. At this point, the management center uses the NAT ID instead of IP address to authenticate the device.
Although the use of a NAT ID is most common for NAT environments, you might choose to use the NAT ID to simplify adding many devices to the management center. On the management center, specify a unique NAT ID for each device you want to add while leaving the IP address blank, and then on each device, specify both the management center IP address and the NAT ID. Note: The NAT ID must be unique per device.
The following example shows three devices behind a PAT IP address. In this case, specify a unique NAT ID per device on both the management center and the devices, and specify the management center IP address on the devices.
The following example shows the management center behind a PAT IP address. In this case, specify a unique NAT ID per device on both the management center and the devices, and specify the device IP addresses on the management center.
Management and Event Traffic Channel Examples
 Note |
If you use a data interface for management on a threat defense, you cannot use separate management and event interfaces for that device. |
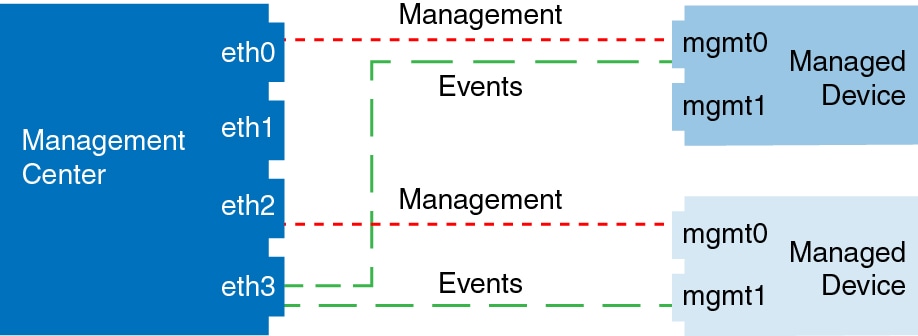
The following example shows the management center and managed devices using only the default management interfaces.
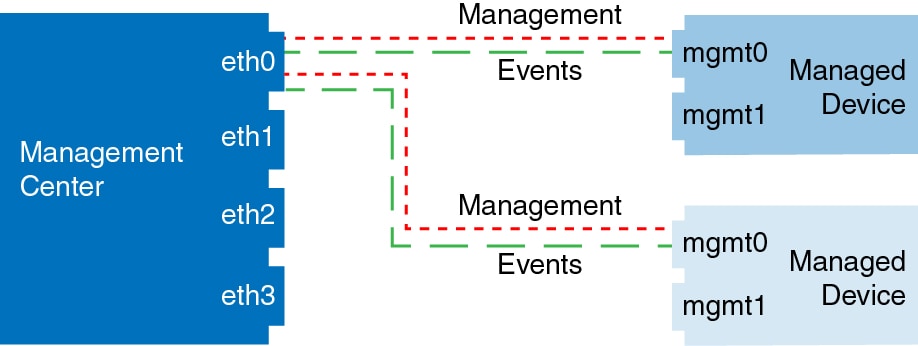
The following example shows the management center using separate management interfaces for devices; and each managed device using 1 management interface.
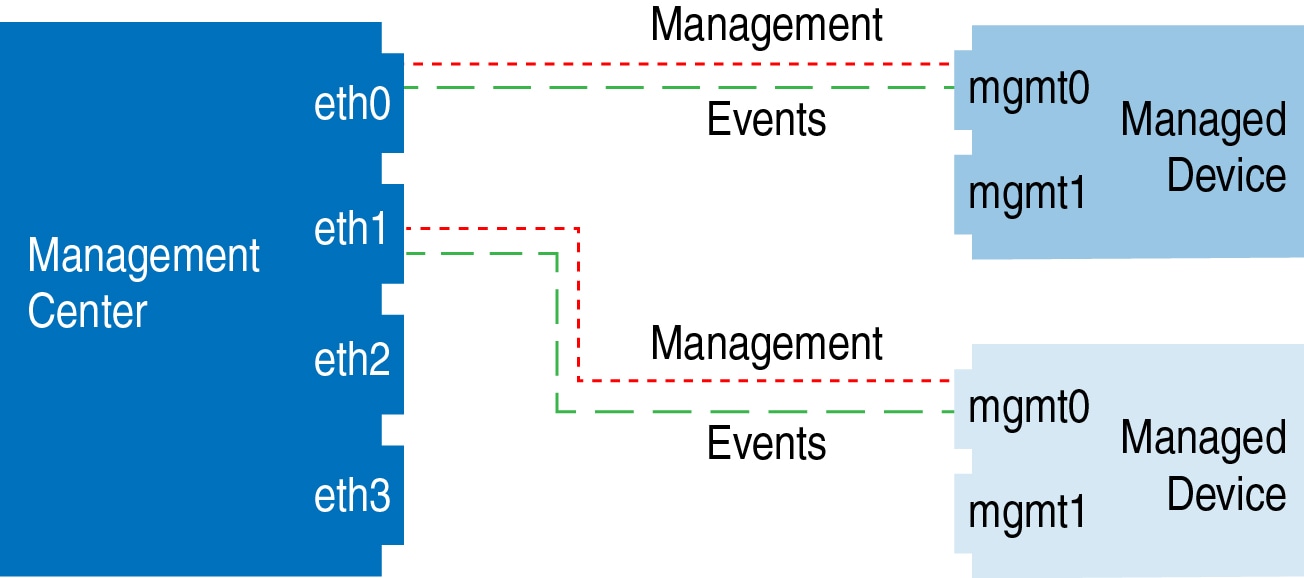
The following example shows the management center and managed devices using a separate event interface.
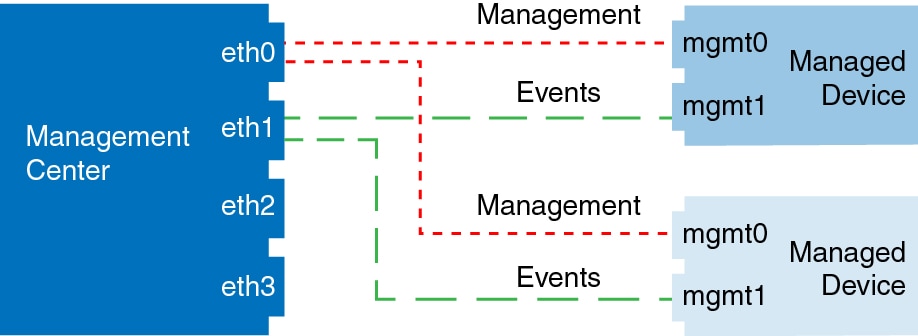
The following example shows a mix of multiple management interfaces and a separate event interface on the management center and a mix of managed devices using a separate event interface, or using a single management interface.




 )
)

 Feedback
Feedback