- Device Manager Help
- Configuring Cisco DCNM-SAN Server
- Configuring Authentication in Cisco DCNM-SAN
- Configuring Cisco DCNM-SAN Client
- Device Manager
- Configuring Performance Manager
- Configuring High Availability
- Configuring Trunking
- Configuring PortChannels
- Configuring N Port Virtualization
- Configuring Interfaces
- Configuration of Fibre Channel Interfaces
- Using the CFS Infrastructure
- Configuring SNMP
- Configuring Domain Parameters
- Configuring and Managing Zones
- Configuring FCoE
- Configuring Dense Wavelength Division Multiplexing
- Configuring and Managing VSANs
- Discovering SCSI Targets
- Configuring SAN Device Virtualization
- Configuring Fibre Channel Routing Services and Protocols
- Managing FLOGI, Name Server, FDMI, and RSCN Databases
- Configuring FICON
- Creating Dynamic VSANs
- Distributing Device Alias Services
- Configuring Advanced Fabric Features
- Configuring Users and Common Role
- Configuring Security Features on an External AAA Server
- Configuring Certificate Authorities and Digital Certificates
- Configuring FC-SP and DHCHAP
- Configuring Cisco TrustSec Fibre Channel Link Encryption
- Configuring FIPS
- Configuring IPv4 and IPv6 Access Control Lists
- Configuring IPsec Network Security
- Configuring Port Security
- Configuring Fabric Binding
- Configuring FCIP
- Configuring the SAN Extension Tuner
- Configuring iSCSI
- Configuring IP Services
- Configuring IP Storage
- Configuring IPv4 for Gigabit Ethernet Interfaces
- Configuring IPv6 for Gigabit Ethernet Interfaces
- Configuring SCSI Flow Services
- Configuring SCSI Flow Statistics
- Configuring Fibre Channel Write Acceleration
- Monitoring the Network
- Monitoring Performance
- Configuring Call Home
- Configuring System Message Logging
- Scheduling Maintenance Jobs
- Configuring RMON
- Configuring Fabric Configuration Server
- Monitoring Network Traffic Using SPAN
- Monitoring System Processes and Logs
- Configuring QoS
- Configuring Port Tracking
- Configuring FlexAttach Virtual pWWN
- Configuring Interface Buffers
- Verifying Ethernet Interfaces
- Information About Role-Based Authorization
- About Roles
- Rules and Features for Each Role
- Rule Changes Between SAN-OS Release 3.3(1c) and NX-OS Release 4.2(1a) Affect Role Behavior
- About the VSAN Policy
- Role Distributions
- About Role Databases
- Locking the Fabric
- About Common Roles
- Mapping of CLI Operations to SNMP
- Creating Users Guidelines
- Characteristics of Strong Passwords
- About SSH
- Boot Mode SSH
- SSH Authentication Using Digital Certificates
- Passwordless File copy and SSH
- Guidelines and Limitations
- Default Settings
- Configuring Users and Common Role
- Configuring Roles and Profiles
- Deleting Common Roles
- Modifying Profiles
- Modifying Rules
- Modifying the VSAN Policy
- Committing Role-Based Configuration Changes
- Discarding Role-Based Configuration Changes
- Enabling Role-Based Configuration Distribution
- Clearing Sessions
- Checking Password Strength
- Configuring Users
- Logging Out Users
- Deleting a User
- Configuring SSH Services
Configuring Users and Common Role
The CLI and SNMP use common roles in all switches in the Cisco MDS 9000 Family. You can use the CLI to modify a role that was created using SNMP and vice versa.
Users, passwords, and roles for all CLI and SNMP users are the same. A user configured through the CLI can access the switch using SNMP (for example, DCNM for SAN (DCNM-SAN or Device Manager) and vice versa.
Information About Role-Based Authorization
Switches in the Cisco MDS 9000 Family perform authentication based on roles. Role-based authorization limits access to switch operations by assigning users to roles. This kind of authentication restricts you to management operations based on the roles to which you have been added.
When you execute a command, perform command completion, or obtain context-sensitive help, the switch software allows the operation to progress if you have permission to access that command.
This section includes the following topics:
- About Roles
- Rules and Features for Each Role
- Rule Changes Between SAN-OS Release 3.3(1c) and NX-OS Release 4.2(1a) Affect Role Behavior
- About the VSAN Policy
- Role Distributions
- About Role Databases
- Locking the Fabric
- About Common Roles
- Mapping of CLI Operations to SNMP
- Creating Users Guidelines
- Characteristics of Strong Passwords
- About SSH
- Boot Mode SSH
- SSH Authentication Using Digital Certificates
- Passwordless File copy and SSH
About Roles
Each role can contain multiple users and each user can be part of multiple roles. For example, if role1 users are only allowed access to configuration commands, and role2 users are only allowed access to debug commands, then if Joe belongs to both role1 and role2, he can access configuration as well as debug commands.

Note If you belong to multiple roles, you can execute a union of all the commands permitted by these roles. Access to a command takes priority over being denied access to a command. For example, suppose you belong to a TechDocs group and you were denied access to configuration commands. However, you also belong to the engineering group and have access to configuration commands. In this case, you will have access to configuration commands.

Tip Any role, when created, does not allow access to the required commands immediately. The administrator must configure appropriate rules for each role to allow access to the required commands.
Rules and Features for Each Role
Up to 16 rules can be configured for each role. These rules reflect what CLI commands are allowed. The user-specified rule number determines the order in which the rules are applied. For example, rule 1 is applied before rule 2, which is applied before rule 3, and so on. A user not belonging to the network-admin role cannot perform commands related to roles.
For example, if user A is permitted to perform all show CLI commands, user A cannot view the output of the show role CLI command if user A does not belong to the network-admin role.
A rule specifies operations that can be performed by a specific role. Each rule consists of a rule number, a rule type (permit or deny), a CLI command type (for example, config , clear , show , exec , debug ), and an optional feature name (for example, FSPF, zone, VSAN, fcping, or interface).

Note In this case, exec CLI commands refer to all commands in the EXEC mode that are not included in the show, debug, and clear CLI command categories.
Rule Changes Between SAN-OS Release 3.3(1c) and NX-OS Release 4.2(1a) Affect Role Behavior
The rules that can be configured for roles were modified between SAN-OS Release 3.3(1c) and NX-OS Release 4.2(1a). As a result, roles do not behave as expected following an upgrade from SAN-OS Release 3.3(1c) to NX-OS Release 4.2(1a). Manual configuration changes are required to restore the desired behavior.
Rule 4 and Rule 3: after the upgrade, exec and feature are removed. Change rule 4 and rule 3 as follows:
Rule 2: after the upgrade, exec feature license is obsolete.
Rule 9, Rule 8, and Rule 7: after the upgrade, you need to have the feature enabled to configure it. In SAN-OS Release 3.3(1c), you could configure a feature without enabling it.
About the VSAN Policy
Configuring the VSAN policy requires the ENTERPRISE_PKG license (For more information, see Cisco MDS 9000 Family NX-OS Licensing Guide).
You can configure a role so that it only allows tasks to be performed for a selected set of VSANs. By default, the VSAN policy for any role is permit, which allows tasks to be performed for all VSANs. You can configure a role that only allows tasks to be performed for a selected set of VSANs. To selectively allow VSANs for a role, set the VSAN policy to deny, and then set the configuration to permit or the appropriate VSANs.

Note Users configured in roles where the VSAN policy is set to deny cannot modify the configuration for E ports. They can only modify the configuration for F or FL ports (depending on whether the configured rules allow such configuration to be made). This is to prevent such users from modifying configurations that may impact the core topology of the fabric.

Tip Roles can be used to create VSAN administrators. Depending on the configured rules, these VSAN administrators can configure MDS features (for example, zone, fcdomain, or VSAN properties) for their VSANs without affecting other VSANs. Also, if the role permits operations in multiple VSANs, then the VSAN administrators can change VSAN membership of F or FL ports among these VSANs.
Users belonging to roles in which the VSAN policy is set to deny are referred to as VSAN-restricted users.
Role Distributions
Role-based configurations use the Cisco Fabric Services (CFS) infrastructure to enable efficient database management, and to provide a single point of configuration for the entire fabric.
About Role Databases
Role-based configurations use two databases to accept and implement configurations.
- Configuration database—The running database currently enforced by the fabric.
- Pending database—Your subsequent configuration changes are stored in the pending database. If you modify the configuration, you need to commit or discard the pending database changes to the configuration database. The fabric remains locked during this period. Changes to the pending database are not reflected in the configuration database until you commit the changes.
Locking the Fabric
The first action that modifies the database creates the pending database and locks the feature in the entire fabric. Once you lock the fabric, the following situations apply:
About Common Roles
The CLI and SNMP in all switches in the Cisco MDS 9000 Family use common roles. You can use SNMP to modify a role that was created using the CLI and vice versa (see Figure 28-1).
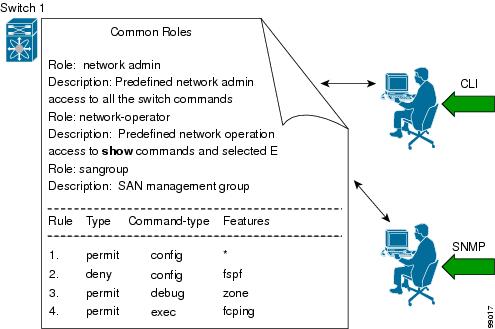
Each role in SNMP is the same as a role created or modified through the CLI (see the “Information About Role-Based Authorization” section).
Each role can be restricted to one or more VSANs as required.
You can create new roles or modify existing roles using SNMP or the CLI.
Mapping of CLI Operations to SNMP
SNMP has only three possible operations: GET, SET, and NOTIFY. The CLI has five possible operations: DEBUG, SHOW, CONFIG, CLEAR, and EXEC.

Note NOTIFY does not have any restrictions like the syslog messages in the CLI.
Table 28-1 explains how the CLI operations are mapped to the SNMP operations.
Creating Users Guidelines
The passphrase specified in the snmp-server user option and the password specified username option are synchronized.
By default, the user account does not expire unless you explicitly configure it to expire. The expire option determines the date on which the user account is disabled. The date is specified in the YYYY-MM-DD format.
When creating users, note the following guidelines:
- You can configure up to a maximum of 256 users on a switch.
- The following words are reserved and cannot be used to configure users: bin, daemon, adm, lp, sync, shutdown, halt, mail, news, uucp, operator, games, gopher, ftp, nobody, nscd, mailnull, rpc, rpcuser, xfs, gdm, mtsuser, ftpuser, man, and sys.
- User passwords are not displayed in the switch configuration file.
- If a password is trivial (short, easy-to-decipher), your password configuration is rejected. Be sure to configure a strong password as shown in the sample configuration. Passwords are case-sensitive. “admin” is no longer the default password for any Cisco MDS 9000 Family switch. You must explicitly configure a strong password.
- To issue commands with the internal keyword for troubleshooting purposes, you must have an account that is a member of the network-admin group.

Characteristics of Strong Passwords
About SSH
SSH provides secure communications to the Cisco NX-OS CLI. You can use SSH keys for the following SSH options:
Boot Mode SSH
Due to the increasing emphasis on security and security-related issues, the ssh command in this release runs in the Boot mode. SSH is a preferred and more secure method of data exchange over the network because it communicates over the secure channel, and the data is encrypted before sending on the channel.
Example 28-1 shows how to use the ssh command to conncet to a remote server from any switch.
SSH Authentication Using Digital Certificates
SSH authentication on the Cisco MDS 9000 Family switches provide X.509 digital certificate support for host authentication. An X.509 digital certificate is a data item that vouches for the origin and integrity of a message. It contains encryption keys for secured communications and is “signed” by a trusted certification authority (CA) to verify the identity of the presenter. The X.509 digital certificate support provides either DSA or RSA algorithms for authentication.
The certificate infrastructure uses the first certificate that supports the Secure Socket Layer (SSL) and is returned by the security infrastructure, either through query or notification. Verification of certificates is successful if the certificates are from any of the trusted CAs.
You can configure your switch for either SSH authentication using an X.509 certificate or SSH authentication using a Public Key Certificate, but not both. If either of them is configured and the authentication fails, you will be prompted for a password.
For more information on CAs and digital certificates, see Chapter30, “Configuring Certificate Authorities and Digital Certificates”
Passwordless File copy and SSH
Secure Shell (SSH) public key authentication can be used to achieve password-free logins. SCP and SFTP uses SSH in the background, which enables these copy protocols to be used for a password-free copy with public key authentication. The NX-OS version only supports the SCP and STFP client functionality.
You can create an RSA and DSA identity that can be used for authentication with SSH. The identity consists of two parts: public and private keys. The public and the private keys are generated by the switch or can be generated externally and imported to the switch. For import purposes, the keys should be in OPENSSH format.
To use the key on a host machine hosting an SSH server, you must transfer the public key file to the machine and add the contents of it to the authorized_keys file in your SSH directory (for example, $HOME/.ssh) on the server. For the import and export of private keys, the key is protected by encryption. You are asked to enter the passphrase for the keys. If you enter a passphrase, the private key is protected by encryption. If you leave the password field blank, the key will not be encrypted.
If you need to copy the keys to another switch, you will have to export the keys out of the switch to a host machine, and then import the keys to other switches from that machine.
Guidelines and Limitations
Fabric merge does not modify the role database on a switch. If two fabrics merge, and the fabrics have different role databases, the software generates an alert message.
See the “Merge Guidelines for RADIUS and TACACS+ Configurations” section for detailed concepts.
Default Settings
Table 28-2 lists the default settings for all switch security features in any switch.
Configuring Users and Common Role
This section includes the following topics:
- Configuring Roles and Profiles
- Deleting Common Roles
- Modifying Profiles
- Modifying Rules
- Modifying the VSAN Policy
- Committing Role-Based Configuration Changes
- Discarding Role-Based Configuration Changes
- Enabling Role-Based Configuration Distribution
- Clearing Sessions
- Checking Password Strength
- Configuring Users
- Logging Out Users
- Deleting a User
Configuring Roles and Profiles
To create an additional role or to modify the profile for an existing role, follow these steps:

Note Only users belonging to the network-admin role can create roles.
To create an additional role or to modify the profile for an existing role using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles from the Physical Attributes pane.
Step 2 Click the Roles tab in the Information pane.
Step 3 Click Create Row to create a role in DCNM-SAN.
Step 4 Select the switches on which to configure a role.
Step 5 Enter the name of the role in the Name field.
Step 6 Enter the description of the role in the Description field.
Step 7 (Optional) Check the Enable check box to enable the VSAN scope and enter the list of VSANs in the Scope field to which you want to restrict this role.
Step 8 Click Create to create the role.

Note Device Manager automatically creates six roles that are required for Device Manager to display a view of a switch. These roles are system, snmp, module, interface, hardware, and environment.
Deleting Common Roles
To delete a common role using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles from the Physical Attributes pane.
Step 2 Click the Roles tab in the Information pane.
Step 3 Click the role you want to delete.
Step 4 Click Delete Row to delete the common role.
Step 5 Click Yes to confirm the deletion or No to cancel it.
Modifying Profiles
To modify the profile for an existing role, follow these steps:
In Step 3, rule 1 is applied first, thus permitting sangroup users access to all config commands. Rule 2 is applied next, denying FSPF configuration to sangroup users. As a result, sangroup users can perform all other config commands, except fspf configuration commands.
Modifying Rules
To modify the rules for an existing role using Device Manager, follow these steps:
Step 1 Choose Security > Roles.
Step 2 Click the role for which you want to edit the rules.
Step 3 Click Rules to view the rules for the role.
You see the Edit Role Rules dialog box.
Step 4 Edit the rules you want to enable or disable for the common role.
Step 5 Click Apply to apply the new rules.
Rule 1 is applied first, which permits, for example, sangroup users access to all config CLI commands. Rule 2 is applied next, denying FSPF configuration to sangroup users. As a result, sangroup users can perform all other config CLI commands, except the fspf CLI configuration commands.

Note The order of rule placement is important. If you had swapped these two rules and issued the deny config feature fspf rule first and issued the permit config rule next, you would be allowing all sangroup users to perform all configuration commands because the second rule globally overrode the first rule.
Modifying the VSAN Policy
To modify the VSAN policy for an existing role, follow these steps:
To modify the VSAN policy for an existing role using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles from the Physical Attributes pane.
Step 2 Click the Roles tab in the Information pane.
Step 3 Check the Scope Enable check box if you want to enable the VSAN scope and restrict this role to a subset of VSANs.
Step 4 Enter the list of VSANs in the Scope VSAN Id List field that you want to restrict this role to.
Step 5 Click Apply Changes to save these changes.
Committing Role-Based Configuration Changes
If you commit the changes made to the pending database, the configuration is committed to all the switches in the fabric. On a successful commit, the configuration change is applied throughout the fabric and the lock is released. The configuration database now contains the committed changes and the pending database is now cleared.
To commit role-based configuration changes, follow these steps:
To commit role-based configuration changes using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles in the Physical Attributes pane.
Step 2 Click the Roles CFS tab in the Information pane.
Step 3 Set the Global drop-down menu to enable to enable CFS.
Step 4 Click the Apply Changes icon to save this change.
Step 5 Set the Config Action drop-down menu to commit to commit the roles using CFS.
Step 6 Click the Apply Changes icon to save this change.
Discarding Role-Based Configuration Changes
If you discard (abort) the changes made to the pending database, the configuration database remains unaffected and the lock is released.
To discard role-based configuration changes, follow these steps:
To discard role-based configuration changes using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles in the Physical Attributes pane.
Step 2 Click the Roles CFS tab in the Information pane.
Step 3 Set the Config Action drop-down menu to abort to discard any uncommitted changes.
Step 4 Click the Apply Changes icon to save this change.
Enabling Role-Based Configuration Distribution
To enable role-based configuration distribution, follow these steps:
To enable role-based configuration distribution using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles in the Physical Attributes pane.
Step 2 Click the Roles CFS tab in the Information pane.
Step 3 Set the Global drop-down menu to enable to enable CFS distribution.
Step 4 Click the Apply Changes icon to save this change.
Clearing Sessions
To forcibly clear the existing role session in the fabric, issue the clear role session command from any switch that is part of the initiated session.
To forcibly clear the existing role session in the fabric using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles in the Physical Attributes pane.
Step 2 Click the Roles CFS tab in the Information pane.
Step 3 Set the Config Action drop-down menu to clear to clear the pending database.
Step 4 Click the Apply Changes icon to save this change.

Checking Password Strength
You can check the strength of the configured password.
When you enable password checking, the NX-OS software allows you to create strong passwords only.
Configuring Users
Before configuring users, make sure that you have configured roles to associate with the users that you are creating.

Note As of Cisco SAN-OS Release 3.1(2b), DCNM-SAN automatically checks whether encryption is enabled, which allows you to create users.
To configure a new user or to modify the profile of an existing user, follow these steps:
To configure a new user or to modify the profile of an existing user using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles from the Physical Attributes pane.
Step 2 Click the Users tab in the Information pane to see a list of users.
Step 3 Click the Create Row icon.
You see the Users - Create dialog box as shown in Figure 28-2.
Figure 28-2 Users - Create Dialog Box
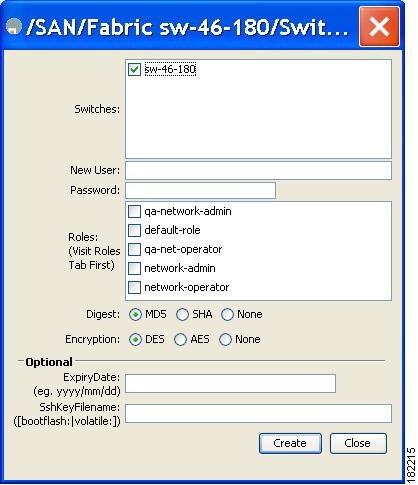
Step 4 (Optional) Alter the Switches check boxes to specify one or more switches.
Step 5 Enter the user name in the New User field.
Step 6 Enter the password for the user.
Step 7 Check the roles that you want to associate with this user.
See the “Rules and Features for Each Role” section.
Step 8 Select the appropriate option for the type of authentication protocol used. The default value is MD5.
Step 9 Select the appropriate option for the type of privacy protocol used. The default value is DES.
Step 10 (Optional) Enter the expiry date for this user.
Step 11 (Optional) Enter the SSH Key filename.
Step 12 Click Create to create the entry.
Logging Out Users
To log out another user on the switch, use the clear user command.
In the following example, the user named vsam is logged out from the switch:
Use the show users command to view a list of the logged in users (see Example 28-2).
Deleting a User
To delete a user using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles from the Physical Attributes pane.
Step 2 Click the Users tab in the Information pane to see a list of users.
Step 3 Click the name of the user you want to delete.
Step 4 Click Delete Row to delete the selected user.
Step 5 Click Apply Changes to save this change.
Configuring SSH Services
A secure SSH connection with an RSA key is available as a default on all Cisco MDS 9000 Family switches. If you require a secure SSH connection with a DSA key, you need to disable the default SSH connection, Generate a DSA key and then enable the SSH connection (see the “Generating the SSH Server Key Pair” section).
Use the ssh key command to generate a server key.

This section includes the following topics:
- Generating the SSH Server Key Pair
- Specifying the SSH Key
- Overwriting a Generated Key Pair
- Enabling SSH or Telnet Service
- Generating SSH User Key Pairs
- Recovering the Administrator Password
Generating the SSH Server Key Pair
Ensure that you have an SSH server key pair with the appropriate version before enabling the SSH service. Generate the SSH server key pair according to the SSH client version used. The number of bits specified for each key pair ranges from 768 to 2048.
The SSH service accepts two types of key pairs for use by SSH version 2.
- The dsa option generates the DSA key pair for the SSH version 2 protocol.
- The rsa option generates the RSA keypair for the SSH version 2 protocol.

To generate the SSH server key pair, follow these steps:
To generate the SSH key pair using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select SSH and Telnet.
Step 2 Click the Create Row icon.
You see the SSH and Telnet Key - Create dialog box (see Figure 28-3).
Figure 28-3 SSH and Telnet - Create Dialog Box
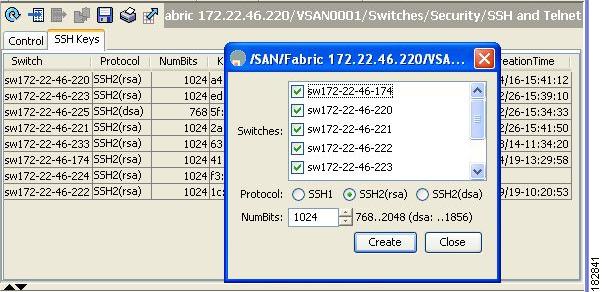
Step 3 Check the switches you want to assign to this SSH key pair.
Step 4 Choose the key pair option type from the listed Protocols. The listed protocols are SSH1, SSH2(rsa), and SSH2(dsa).
Step 5 Set the number of bits that will be used to generate the key pairs in the NumBits drop-down menu.
Step 6 Click Create to generate these keys.

Note 1856 DSA NumberKeys are not supported by switches that running Cisco MDS NX-OS software version 4.1(1) and later.
Specifying the SSH Key
You can specify an SSH key to log in using the SSH client without being prompted for a password. You can specify the SSH key in three different formats:
To specify or delete the SSH key in OpenSSH format for a specified user, follow these steps:
To specify or delete the SSH key in IETF SECSH format for a specified user, follow these steps:
To specify or delete the SSH key in PEM-formatted Public Key Certificate form for a specified user, follow these steps:
Overwriting a Generated Key Pair
If the SSH key pair option is already generated for the required version, you can force the switch to overwrite the previously generated key pair.
To overwrite the previously generated key pair, follow these steps:
To overwrite the previously generated key pair using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select SSH and Telnet.
You see the configuration in the Information pane.
Step 2 Highlight the key that you want to overwrite and click Delete Row.
Step 3 Click the Apply Changes icon to save these changes.
Step 4 Click the Create Row icon.
You see the SSH and Telnet Key - Create dialog box.
Step 5 Check the switches you want to assign this SSH key pair.
Step 6 Choose the key pair option type from the Protocols radio buttons.
Step 7 Set the number of bits that will be used to generate the key pairs in the NumBits drop-down menu.
Step 8 Click Create to generate these keys.
Enabling SSH or Telnet Service
By default, the SSH service is enabled with the RSA key.
To enable or disable the SSH or Telnet service, follow these steps:

Note If you are logging in to a switch through SSH and you have issued the aaa authentication login default none CLI command, you must enter one or more key strokes to log in. If you press the Enter key without entering at least one keystroke, your log in will be rejected.
DCNM-SAN enables SSH automatically when you configure it.
To enable or disable SSH using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select SSH and Telnet.
Step 2 Select the Control tab and check an SSH check box or Telnet check box for each switch (see Figure 28-4).
Figure 28-4 Control Tab under SSH and Telnet
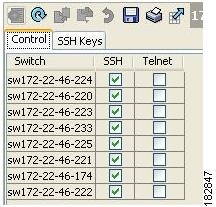
Step 3 Click the Apply Changes icon to save this change.
Generating SSH User Key Pairs
To import and export the key pair, the following CLIs are provided. The CLI command to generate the ssh user key pairs on the switch is defined as follows:
Changing Administrator Password Using DCNM-SAN
To change the administrator password in DCNM-SAN, follow these steps:
Step 1 Click the Open tab in the control panel.
Step 2 Choose the password field to change the password for an already existing user for the fabric.
Step 3 Click Open to open the fabric.

Note New password will be saved after the fabric is open. The user name and password fields are editable in the Fabric tab only after you unmanage the fabric.
Recovering the Administrator Password
You can recover the administrator password using one of two methods:

Note To recover an administrator’s password, refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide.
Using the CLI with Network-Admin Privileges
If you are logged in to, or can log into, switch with a user name that has network-admin privileges and then recover the administrator password, follow these steps:
Step 1 Use the show user-accounts command to verify that your user name has network-admin privileges.
Step 2 If your user name has network-admin privileges, issue the username command to assign a new administrator password.
Step 3 Save the software configuration.
Power Cycling the Switch
If you cannot start a session on the switch that has network-admin privileges, you must recover the administrator password by power cycling the switch.


Note You cannot recover the administrator password from a Telnet or SSH session. You must have access to the local console connection.
To recover a administrator password by power cycling the switch, follow these steps:
Step 1 For Cisco MDS 9500 Series switches with two supervisor modules, remove the supervisor module in
slot 6 from the chassis.

Note On the Cisco MDS 9500 Series, the password recovery procedure must be performed on the active supervisor module. Removing the supervisor module in slot 6 ensures that a switchover will not occur during the password recovery procedure.
Step 2 Power cycle the switch.
Step 3 Press the
Ctrl-]
key sequence when the switch begins its Cisco NX-OS software boot sequence to enter the
switch(boot)#
prompt mode.
Step 4 Change to configuration mode.
Step 5 Issue the admin-password command to reset the administrator password. This will disable remote authentication for login through console, if enabled. This is done to ensure that admin is able to login through console with new password after password recovery. Telnet/SSH authentication will not be affected by this.
For information on strong passwords, see the “Checking Password Strength” section.
Step 7 Issue the load command to load the Cisco NX-OS software.

Step 8 Log in to the switch using the new administrator password.
Step 9 Reset the new password to ensure that is it is also the SNMP password for DCNM-SAN.
Step 10 Save the software configuration.
Step 11 Insert the previously removed supervisor module into slot 6 in the chassis.
Verifying Users and Common Role Configuration
To display Monitoring Users and Common Role configuration information, perform one of the following tasks:
For detailed information about the fields in the output from these commands, refer to the Cisco MDS 9000 Family Command Reference .
This section includes the following topics:
- Displaying Role-Based Information
- Displaying Role-Based Information
- Displaying Roles When Distribution is Enabled
- Displaying User Account Information
- Displaying SSH Protocol Status
Displaying Role-Based Information
The rules are displayed by rule number and are based on each role. All roles are displayed if the role name is not specified.
To view rules for a role using Device Manager, follow these steps:
Step 1 Click Security > Roles.
Step 2 Select a role name and click Rules.
Step 3 Click Summary to get a summarized view of the rules configured for this role.
Displaying Role-Based Information
Use the show role command to display rules configured on the switch. The rules are displayed by rule number and are based on each role. All roles are displayed if the role name is not specified. See Example 28-3.
Displaying Roles When Distribution is Enabled
Use the show role command to display the configuration database.
Use the show role status command to display whether distribution is enabled for role configuration, the current fabric status (locked or unlocked), and the last operation performed. See Example 28-4.
Example 28-4 Displays the Role Status Information
Use the show role pending command to display the pending role database.
Example 28-5 displays the output of the show role pending command by following this procedure:
1. Create the role called
myrole
using the
role name myrole
command.
2. Enter the rule 1 permit config feature fspf command.
3. Enter the show role pending command to see the output.
Example 28-5 Displays Information on the Pending Roles Database
Use the show role pending-diff command to display the differences between the pending and configuration role database. See Example 28-6.
Example 28-6 Displays the Differences Between the Two Databases
To view the roles using DCNM-SAN, follow these steps:
Step 1 Expand Switches > Security and then select Users and Roles in the Physical Attributes pane.
Step 2 Click the Users tab in the Information pane (see Figure 28-5).

Step 3 Set the Config View As drop-down value to pending to view the pending database or set the Config View as drop-down menu to running to view the running database.
Step 4 Click Apply Changes to save this change.
Example 28-7 shows the privileges and rules mapping CLI operations to SNMP operations for a role named my_role.
Example 28-7 Displays CLI Operation to SNMP Operation Mapping

Note Although CONFIG is denied for NTP in rule 4, rule 9 allows the SET to NTP MIB objects because EXEC also maps to the SNMP SET operation
Displaying User Account Information
Use the show user-account command to display configured information about user accounts. See Examples 28-8 to 28-9 .
Example 28-8 Displays Information for a Specified User
Example 28-9 Displays Information for All Users
To display information about configured user accounts using DCNM-SAN, follow these steps:
Step 1 Expand Security and then select Users and Roles in the Physical Attributes pane.
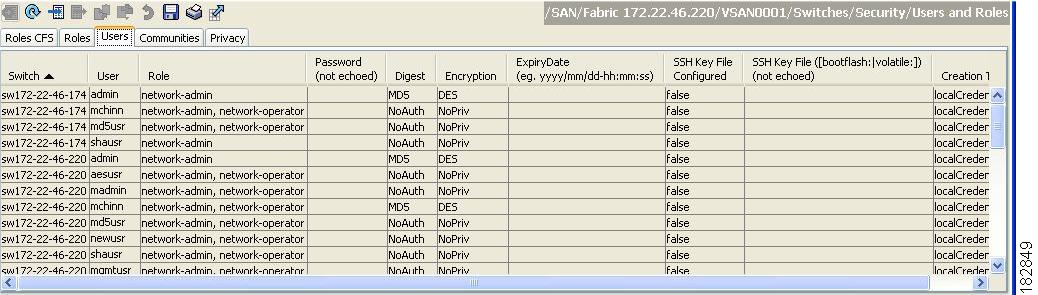
You see the list of SNMP users shown in Figure 28-6 in the Information pane.
Figure 28-6 Users Listed Under the Users Tab
Displaying SSH Protocol Status
Use the show ssh server command to display the status of the SSH protocol (enabled or disabled) and the versions that are enabled for that switch (see Example 28-10).
Example 28-10 Displays SSH Protocol Status
Use the show ssh key command to display the server key-pair details for the specified key or for all keys, (see Example 28-11).
Example 28-11 Displays Server Key-Pair Details

Note If you are logging in to a switch through SSH and you have issued the aaa authentication login default none CLI command, you must enter one or more key strokes to log in. If you press the Enter key without entering at least one keystroke, your log in will be rejected.
Feature History for Users and Common Role
Table 28-3 lists the release history for this feature. Only features that were introduced or modified in 5.x or a later release appear in the table.
 Feedback
Feedback