- Device Manager Help
- Configuring Cisco DCNM-SAN Server
- Configuring Authentication in Cisco DCNM-SAN
- Configuring Cisco DCNM-SAN Client
- Device Manager
- Configuring Performance Manager
- Configuring High Availability
- Configuring Trunking
- Configuring PortChannels
- Configuring N Port Virtualization
- Configuring Interfaces
- Configuration of Fibre Channel Interfaces
- Using the CFS Infrastructure
- Configuring SNMP
- Configuring Domain Parameters
- Configuring and Managing Zones
- Configuring FCoE
- Configuring Dense Wavelength Division Multiplexing
- Configuring and Managing VSANs
- Discovering SCSI Targets
- Configuring SAN Device Virtualization
- Configuring Fibre Channel Routing Services and Protocols
- Managing FLOGI, Name Server, FDMI, and RSCN Databases
- Configuring FICON
- Creating Dynamic VSANs
- Distributing Device Alias Services
- Configuring Advanced Fabric Features
- Configuring Users and Common Role
- Configuring Security Features on an External AAA Server
- Configuring Certificate Authorities and Digital Certificates
- Configuring FC-SP and DHCHAP
- Configuring Cisco TrustSec Fibre Channel Link Encryption
- Configuring FIPS
- Configuring IPv4 and IPv6 Access Control Lists
- Configuring IPsec Network Security
- Configuring Port Security
- Configuring Fabric Binding
- Configuring FCIP
- Configuring the SAN Extension Tuner
- Configuring iSCSI
- Configuring IP Services
- Configuring IP Storage
- Configuring IPv4 for Gigabit Ethernet Interfaces
- Configuring IPv6 for Gigabit Ethernet Interfaces
- Configuring SCSI Flow Services
- Configuring SCSI Flow Statistics
- Configuring Fibre Channel Write Acceleration
- Monitoring the Network
- Monitoring Performance
- Configuring Call Home
- Configuring System Message Logging
- Scheduling Maintenance Jobs
- Configuring RMON
- Configuring Fabric Configuration Server
- Monitoring Network Traffic Using SPAN
- Monitoring System Processes and Logs
- Configuring QoS
- Configuring Port Tracking
- Configuring FlexAttach Virtual pWWN
- Configuring Interface Buffers
- Verifying Ethernet Interfaces
- Information About FICON
- FICON Requirements
- Cisco MDS-Specific FICON Advantages
- FICON Cascading
- FICON VSAN Prerequisites
- FICON Port Numbering
- Default FICON Port Numbering Scheme
- Port Addresses
- Implemented and Unimplemented Port Addresses
- About the Reserved FICON Port Numbering Scheme
- Installed and Uninstalled Ports
- About Port Numbers for FCIP and PortChannel
- FC ID Allocation
- About Enabling FICON on a VSAN
- FICON Information Refresh
- About FICON Device Allegiance
- Automatically Saving the Running Configuration
- Port Prohibiting
- About RLIR
- FICON Configuration Files
- Licensing Requirements for FICON
- Guidelines and Limitations
- Default Settings
- Configuring FICON
- Assigning FICON Port Numbers to Slots
- Reserving FICON Port Numbers for FCIP and PortChannel Interfaces
- Enabling FICON on the Switch
- Setting Up a Basic FICON Configuration
- Enabling FICON on a VSAN
- Manually Enabling FICON on a VSAN
- Deleting FICON VSANs
- Suspending a FICON VSAN
- Moving a FICON VSAN to an Offline State
- Configuring the code-page Option
- Assigning FC ID Last Byte
- Allowing the Host to Move the Switch Offline
- Allowing the Host to Change FICON Port Parameters
- Allowing the Host to Control the Timestamp
- Clearing the Time Stamp
- Configuring SNMP Control of FICON Parameters
- Clearing FICON Device Allegiance
- Automatically Saving the Running Configuration
- Configuring FICON Ports
- Binding Port Numbers to PortChannels
- Binding Port Numbers to FCIP Interfaces
- Configuring Port Blocking
- Configuring the Default State for Port Prohibiting
- Configuring Port Prohibiting
- Assigning a Port Address Name
- Specifying an RLIR Preferred Host
- Clearing RLIR Information
- Applying the Saved Configuration Files to the Running Configuration
- Editing FICON Configuration Files
- Copying FICON Configuration Files
- Swapping Ports
- Configuring FICON Tape Acceleration
- Configuring FICON Tape Read Acceleration
- Configuring XRC Acceleration
- Placing CUPs in a Zone
- Calculating FICON Flow Load Balance
- Receiving FICON Alerts
- Verifying FICON Configuration
- Displaying the FICON Port Number Assignments
- Viewing ESCON Style Ports
- Displaying RLIR Information
- Displaying FICON Configuration Files
- Displaying XRC Acceleration Statistics
- Displaying Control Unit Information
- Displaying FICON Port Address Information
- Displaying IPL File Information
- Displaying FICON Configuration File Information
- Displaying the Configured FICON State
- Displaying a Port Administrative State
- Displaying Buffer Information
- Viewing the History Buffer
- Displaying FICON Information in the Running Configuration
- Displaying FICON Information in the Startup Configuration
- Displaying FICON-Related Log Information
- Field Descriptions for FICON
- Additional References
- Feature History for FICON
Configuring FICON
Fibre Connection (FICON) interface capabilities enhance the Cisco MDS 9000 Family by supporting both open systems and mainframe storage network environments. The control unit port (CUP) also is supported, which allows in-band management of the switch from FICON processors.

Note Cisco Fabric Manager release 3.x does not support FICON management of Cisco MDS 9000 Family switches running SAN-OS release 2.(x).
Information About FICON
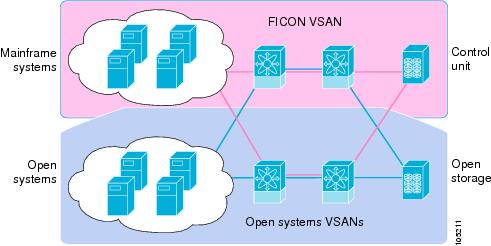
The Cisco MDS 9000 Family supports the Fibre Channel Protocol (FCP), FICON, iSCSI, and FCIP capabilities within a single, high-availability platform (see Figure 24-1).
The FICON feature is not supported on:
- Cisco MDS 9120 switches
- Cisco MDS 9124 switches
- Cisco MDS 9140 switches
- The 32-port Fibre Channel switching module
- Cisco Fabric Switch for HP c-Class BladeSystem
- Cisco Fabric Switch for IBM BladeSystem
FCP and FICON are different FC4 protocols and their traffic is independent of each other. Devices using these protocols should be isolated using VSANs.
The fabric binding feature helps prevent unauthorized switches from joining the fabric or disrupting current fabric operations (refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide ). The Registered Link Incident Report (RLIR) application provides a method for a switch port to send an LIR to a registered Nx port.
Figure 24-1 Shared System Storage Network
This section includes the following topics:
- FICON Requirements
- Cisco MDS-Specific FICON Advantages
- FICON Cascading
- FICON VSAN Prerequisites
- FICON Port Numbering
- Default FICON Port Numbering Scheme
- Port Addresses
- Implemented and Unimplemented Port Addresses
- About the Reserved FICON Port Numbering Scheme
- Installed and Uninstalled Ports
- About Port Numbers for FCIP and PortChannel
- FC ID Allocation
- About Enabling FICON on a VSAN
- FICON Information Refresh
- About FICON Device Allegiance
- Automatically Saving the Running Configuration
- Port Prohibiting
- About RLIR
- Port Swapping
- FICON Tape Acceleration
- CUP In-Band Management
FICON Requirements
The FICON feature has the following requirements:
– Any switch in the Cisco MDS 9500 Series
– Any switch in the Cisco MDS 9200 Series (including the Cisco MDS 9222i Multiservice Modular Switch)
Cisco MDS-Specific FICON Advantages
This section explains the additional FICON advantages in Cisco MDS switches and includes the following topics:
Fabric Optimization with VSANs
Generally, separate physical fabrics have a high level of switch management and have a higher implementation cost. The ports in each island also may be over-provisioned depending on the fabric configuration.
By using the Cisco MDS-specific VSAN technology, you can have greater efficiency between these physical fabrics by lowering the cost of over-provisioning and reducing the number of switches to be managed. VSANs also help you to move unused ports nondisruptively and provide a common redundant physical infrastructure (see Figure 24-2).
Figure 24-2 VSAN-Specific Fabric Optimization
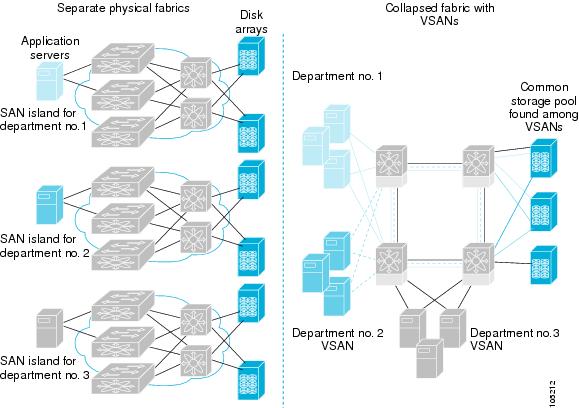
VSANs enable global SAN consolidation by allowing you to convert existing SAN islands into virtual SAN islands on a single physical network. It provides hardware-enforced security and separation between applications or departments to allow coexistence on a single network. It also allows virtual rewiring to consolidate your storage infrastructure. You can move assets between departments or applications without the expense and disruption of physical relocation of equipment.

Note You can configure VSANs in any Cisco MDS switch, but you only can enable FICON in up to eight of these VSANs. The number of VSANs configured depends on the platform.
Mainframe users can think of VSANs as being like FICON LPARs in the MDS SAN fabric. You can partition switch resources into FICON LPARs (VSANs) that are isolated from each other, in much the same way that you can partition resources on a zSeries or DS8000. Each VSAN has its own set of fabric services (such as fabric server and name server), FICON CUP, domain ID, Fabric Shortest Path First (FSPF) routing, operating mode, IP address, and security profile.
FICON LPARs can span line cards and are dynamic in size. For example, one FICON LPAR with 10 ports can span 10 different line cards. FICON LPARs can also include ports on more than one switch in a cascaded configuration. The consistent fairness of the Cisco MDS 9000 switching architecture means that “all ports are created equal,” simplifying provisioning by eliminating the “local switching” issues seen on other vendors’ platforms.
Addition of ports to a FICON LPAR is a nondisruptive process. The maximum number of ports for a FICON LPAR is 255 due to FICON addressing limitations.
FCIP Support
The multilayer architecture of the Cisco MDS 9000 Family enables a consistent feature set over a protocol-agnostic switch fabric. Cisco MDS 9500 Series and 9200 Series switches transparently integrate Fibre Channel, FICON, and Fibre Channel over IP (FCIP) in one system. The FICON over FCIP feature enables cost-effective access to remotely located mainframe resources. With the Cisco MDS 9000 Family platform, storage replication services such as IBM PPRC and XRC can be extended over metro to global distances using ubiquitous IP infrastructure which simplifies business continuance strategies.
Refer to the Cisco MDS 9000 Family NX-OS IP Services Configuration Guide .
PortChannel Support
The Cisco MDS implementation of FICON provides support for efficient utilization and increased availability of Inter-Switch Links (ISLs) necessary to build stable large-scale SAN environments. PortChannels ensure an enhanced ISL availability and performance in Cisco MDS switches.
Refer to the Cisco MDS 9000 Family NX-OS Interfaces Configuration Guide for more information on PortChannels.
VSANs for FICON and FCP Mixing
Cisco MDS 9000 Family FICON-enabled switches simplify deployment of even the most complex mixed environments. Multiple logical FICON, Z-Series Linux/FCP, and Open-Systems Fibre Channel Protocol (FCP) fabrics can be overlaid onto a single physical fabric by simply creating VSANs as required for each service. VSANs provide both hardware isolation and protocol specific fabric services, eliminating the complexity and potential instability of zone-based mixed schemes.
By default, the FICON feature is disabled in all switches in the Cisco MDS 9000 Family. When the FICON feature is disabled, FC IDs can be allocated seamlessly. Mixed environments are addressed by the Cisco NX-OS software. The challenge of mixing FCP and FICON protocols are addressed by Cisco MDS switches when implementing VSANs.
Switches and directors in the Cisco MDS 9000 Family support FCP and FICON protocol mixing at the port level. If these protocols are mixed in the same switch, you can use VSANs to isolate FCP and FICON ports.

Tip When creating a mixed environment, place all FICON devices in one VSAN (other than the default VSAN) and segregate the FCP switch ports in a separate VSAN (other than the default VSAN). This isolation ensures proper communication for all connected devices.
Cisco MDS-Supported FICON Features
The Cisco MDS 9000 Family FICON features include:
- Flexibility and investment protection—The Cisco MDS 9000 Family shares common switching and service modules across the Cisco MDS 9500 Series and the 9200 Series.
Refer to the Cisco MDS 9500 Series Hardware Installation Guide and the Cisco MDS 9200 Series Hardware Installation Guide.
- High-availability FICON-enabled director—The Cisco MDS 9500 Series combines nondisruptive software upgrades, stateful process restart and failover, and full redundancy of all major components for a new standard in director-class availability. It supports up to 528 autosensing, 4/2/1-Gbps, 10-Gbps, FICON or FCP ports in any combination in a single chassis. Refer to the Cisco MDS 9000 Family NX-OS High Availability and Redundancy Configuration Guide .
- Infrastructure protection—Common software releases provide infrastructure protection across all Cisco MDS 9000 platforms. Refer to the Cisco MDS 9000 Family NX-OS Software Upgrade and Downgrade Guide .
- VSAN technology—The Cisco MDS 9000 Family provides VSAN technology for hardware-enforced, isolated environments within a single physical fabric for secure sharing of physical infrastructure and enhanced FICON mixed support. See Chapter19, “Configuring and Managing VSANs”
- Port-level configurations—There are BB_credits, beacon mode, and port security for each port. Refer to the Cisco MDS 9000 Family NX-OS Interfaces Configuration Guide for information about buffer-to-buffer credits, beacon LEDs, and trunking.
- Alias name configuration—Provides user-friendly aliases instead of the WWN for switches and attached node devices. See Chapter16, “Configuring and Managing Zones”
- Comprehensive security framework—The Cisco MDS 9000 Family supports RADIUS and TACACS+ authentication, Simple Network Management Protocol Version 3 (SNMPv3), role-based access control, Secure Shell Protocol (SSH), Secure File Transfer Protocol (SFTP), VSANs, hardware-enforced zoning, ACLs, fabric binding, Fibre Channel Security Protocol (FC-SP), LUN zoning, read-only zones, and VSAN-based access control. Refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide for information about RADIUS, TACACS+, FC-SP, and DHCHAP.
- Traffic encryption—IPsec is supported over FCIP. You can encrypt FICON and Fibre Channel traffic that is carried over FCIP. Refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide .
- Local accounting log—View the local accounting log to locate FICON events. For more information about MSCHAP authentication, and local AAA services, refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide .
- Unified storage management—Cisco MDS 9000 FICON-enabled switches are fully IBM CUP standard compliant for in-band management using the IBM S/A OS/390 I/O operations console. See the “CUP In-Band Management” section.
- Port address-based configurations—Configure port name, blocked or unblocked state, and the prohibit connectivity attributes can be configured on the ports. See the “Configuring FICON Ports” section.
- You can display the following information:
– Individual Fibre Channel ports, such as the port name, port number, Fibre Channel address, operational state, type of port, and login data.
– Port performance and statistics.
See the “Calculating FICON Flow Load Balance” section.
- Configuration files—Store and apply configuration files. See the “FICON Configuration Files” section.
- FICON and Open Systems Management Server features if installed. —See the “VSANs for FICON and FCP Mixing” section.
- Enhanced cascading support—See the “CUP In-Band Management” section.
- Date and time—Set the date and time on the switch. See the “Allowing the Host to Control the Timestamp” section.
- Configure SNMP trap recipients and community names—See the “Configuring SNMP Control of FICON Parameters” section.
- Call Home configurations—Configure the director name, location, description, and contact person. Refer to the Cisco MDS 9000 Family NX-OS System Management Configuration Guide.
- Configure preferred domain ID, FC ID persistence, and principal switch priority—For information about configuring domain parameters, refer to the Cisco MDS 9000 Family NX-OS System Management Configuration Guide .
- Sophisticated SPAN diagnostics—The Cisco MDS 9000 Family provides industry-first intelligent diagnostics, protocol decoding, and network analysis tools as well as integrated Call Home capability for added reliability, faster problem resolution, and reduced service costs. For information about monitoring network traffic using SPAN, refer to the Cisco MDS 9000 Family NX-OS System Management Configuration Guide .
- Configure R_A_TOV, E_D_TOV—— See the “Fibre Channel Time-Out Values” section.
- Director-level maintenance tasks—Perform maintenance tasks for the director including maintaining firmware levels, accessing the director logs, and collecting data to support failure analysis. For information about monitoring system processes and logs refer to the Cisco MDS 9000 Family NX-OS System Management Configuration Guide .
- Port-level incident alerts—Display and clear port-level incident alerts. See the “Clearing RLIR Information” section.
FICON Cascading
The Cisco MDS NX-OS software allows multiple switches in a FICON network. To configure multiple switches, you must enable and configure fabric binding in that switch (see the “Calculating FICON Flow Load Balance” section and refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide ).
FICON VSAN Prerequisites
To ensure that a FICON VSAN is operationally up, be sure to verify the following requirements:
- Set the default zone to permit, if you are not using the zoning feature. See the “About the Default Zone” section.
- Enable in-order delivery on the VSAN. See Chapter22, “Configuring Fibre Channel Routing Services and Protocols”
- Enable (and if required, configure) fabric binding on the VSAN. See the “Calculating FICON Flow Load Balance” section. For more information about Fabric Binding, refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide .
- Verify that conflicting persistent FC IDs do not exist in the switch. For information about configuring domain parameters, refer to the Cisco MDS 9000 Family NX-OS System Management Configuration Guide .
- Verify that the configured domain ID and requested domain ID match. For information about configuring domain parameters, refer to the Cisco MDS 9000 Family NX-OS System Management Configuration Guide .
- Add the CUP (area FE) to the zone, if you are using zoning. See the “CUP In-Band Management” section.
If any of these requirements are not met, the FICON feature cannot be enabled.
FICON Port Numbering
With reference to the FICON feature, ports in Cisco MDS switches are identified by a statically defined 8-bit value known as the port number. A maximum of 255 port numbers are available. You can use the following port numbering schemes:
Default FICON Port Numbering Scheme
Default FICON port numbers are assigned by the Cisco MDS NX-OS software based on the module and the slot in the chassis. The first port in a switch always starts with a zero (0) (see Figure 24-3).
Figure 24-3 Default FICON Port Number in Numbering on the Cisco MDS 9000 Family Switch
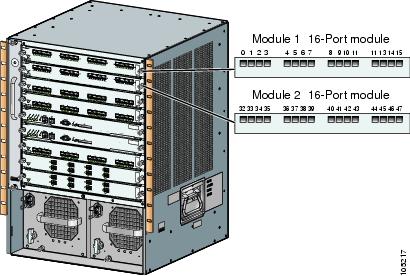
The default FICON port number is assigned based on the front panel location of the port and is specific to the slot in which the module resides. Thirty-two (32) port numbers are assigned to each slot on all Cisco MDS 9000 Family switches except for the Cisco MDS 9513 Director, which has 16 port numbers assigned for each slot. These default numbers are assigned regardless of the module’s physical presence in the chassis, the port status (up or down), or the number of ports on the module (4, 12, 16, 24, or 48). If a module has fewer ports than the number of port numbers assigned to the slot, then the excess port numbers are unused. If a module has more ports than the number of port numbers assigned to the slot, the excess ports cannot be used for FICON traffic unless you manually assign the port numbers.

Note You can use the ficon slot assign port-numbers command to make use of any Follow the steps in “Assigning FICON Port Numbers to Slots” section to make use of excess ports by manually assigning more port numbers to the slots. Before doing this, however, we recommend that you review the default port number assignments for Cisco MDS 9000 switches shown in Table 24-3 Table 24-1, and that you read the following sections to gain a complete understanding of FICON port numbering: “About the Reserved FICON Port Numbering Scheme” section, “FICON Port Numbering Guidelines” section, and “Assigning FICON Port Numbers to Slots” section.

Note Only Fibre Channel, PortChannel, and FCIP ports are mapped to FICON port numbers. Other types of interfaces do not have a corresponding port number.
Table 24-1 lists the default port number assignment for the Cisco MDS 9000 Family of switches and directors.
Port Addresses
By default, port numbers are the same as port addresses. You can swap the port addresses (see the “Port Swapping” section).
You can swap the port addresses by issuing the ficon swap portnumber command.
Implemented and Unimplemented Port Addresses
An implemented port refers to any port address that is assigned by default to a slot in the chassis (see Table 24-3 ). An unimplemented port refers to any port address that is not assigned by default to a slot in the chassis (see Table 24-3 ).
About the Reserved FICON Port Numbering Scheme
A range of 250 port numbers are available for you to assign to all the ports on a switch. Table 24-3 shows that you can have more than 250 physical ports on a switch and the excess ports do not have port numbers in the default numbering scheme. When you have more than 250 physical ports on your switch, you can have ports without a port number assigned if they are not in a FICON VSAN, or you can assign duplicate port numbers if they are not used in the same FICON VSAN. For example, you can configure port number 1 on interface fc1/1 in FICON VSAN 10 and fc10/1 in FICON VSAN 20.

Note A VSAN can have a maximum of 250 port numbers.

Note FICON port numbers are not changed for ports that are active. You must first disable the interfaces using the shutdown command.

Note You can configure port numbers even when no module is installed in the slot.
Installed and Uninstalled Ports
An installed port refers to a port for which all required hardware is present. A specified port number in a VSAN can be implemented, and yet not installed, if any of the following conditions apply:
- The module is not present—For example, if module 1 is not physically present in slot 1 in a Cisco MDS 9509 Director, ports 0 to 31 are considered uninstalled.
- The small form-factor pluggable (SFP) port is not present—For example, if a 16-port module is inserted in slot 2 in a Cisco MDS 9509 Director, ports 48 to 63 are considered uninstalled.
- For slot 1, ports 0 to 31, or 0 to 15 have been assigned. Only the physical port fc1/5 with port number 4 is in VSAN 2. The rest of the physical ports are not in VSAN 2. The port numbers 0 to 249 are considered implemented for any FICON-enabled VSAN. Therefore, VSAN 2 has port numbers 0 to 249 and one physical port, fc1/4. The corresponding physical ports 0 to 3,and 5 to 249 are not in VSAN 2. When the FICON VSAN port address is displayed, those port numbers with the physical ports not in VSAN 2 are not installed (for example, ports 0 to 3, or 5 to 249).
Another scenario is if VSANs 1 through 5 are FICON-enabled, and trunking-enabled interface fc1/1 has VSANs 3 through 10, then port address 0 is uninstalled in VSAN 1 and 2.
- The port is part of a PortChannel—For example, if interface fc 1/1 is part of PortChanne1 5, port address 0 is uninstalled in all FICON VSANs. See Table 24-3 .
About Port Numbers for FCIP and PortChannel
FCIP and PortChannels cannot be used in a FICON-enabled VSAN unless they are explicitly bound to a port number.
See the “Configuring FICON Ports” section, “Configuring FICON Ports” section, “Reserving FICON Port Numbers for FCIP and PortChannel Interfaces” section, and “Binding Port Numbers to FCIP Interfaces” section.
You can use the default port numbers if they are available (see Table 24-1) or if you reserve port numbers from the pool of port numbers that are not reserved for Fibre Channel interfaces (see the “FICON Port Numbering” section and the “About the Reserved FICON Port Numbering Scheme” section).
To find the first available port number to bind an FCIP or PortChannel interface, use the show ficon first-available port-number command (see Example 24-12 on page 24-57 ).

Tip The show ficon vsan portaddress brief command displays the port number to interface mapping. You can assign port numbers in the PortChannel/FCIP range that are not already assigned to a PortChannel or FCIP interface (see Example 24-13 on page 24-58).
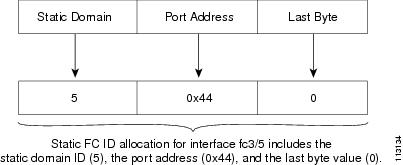
FC ID Allocation
FICON requires a predictable and static FC ID allocation scheme. When FICON is enabled, the FC ID allocated to a device is based on the port address of the port to which it is attached. The port address forms the middle byte of the fabric address. Additionally, the last byte of the fabric address should be the same for all devices in the fabric. By default, the last byte value is 0 and can be configured (see the “Assigning FC ID Last Byte” section).

Note You cannot configure persistent FC IDs in FICON-enabled VSANs.
Cisco MDS switches have a dynamic FC ID allocation scheme. When FICON is enabled or disabled on a VSAN, all the ports are shut down and restarted to switch from the dynamic to static FC IDs and vice versa (see Figure 24-4).
Figure 24-4 Static FC ID Allocation for FICON
About Enabling FICON on a VSAN
By default FICON is disabled in all VSANs on the switch.
You can enable FICON on a per VSAN basis in one of the following ways:
See the “Setting Up a Basic FICON Configuration” section.
See the “Information About FICON” section.
When you enable the FICON feature in Cisco MDS switches, the following restrictions apply:
- You cannot disable in-order delivery for the FICON-enabled VSAN.
- You cannot disable fabric binding or static domain ID configurations for the FICON-enabled VSAN.
- The load balancing scheme is changed to Source ID (SID)—Destination ID (DID). You cannot change it back to SID—DID—OXID.
- The IPL configuration file is automatically created.
See the “FICON Configuration Files” section.

Tip Using Device Manager, FICON auto-save can be invoked by multiple users logged on to the same FICON-enabled switch. Device Manager performs a periodic auto-save on any FICON-enabled switch causing increments in the FICON key counter. These increments highlight a change that has actually not occurred. To avoid this situation, we recommend that only one instance of Device Manager monitor a FICON-enabled switch.
FICON Information Refresh
When viewing FICON information through the Device Manager dialog boxes, you must manually refresh the display by clicking the Refresh button to see the latest updates. You need to take this step whether you configure FICON through the CLI or through the Device Manager.
There is no automatic refresh of FICON information. This information would be refreshed so often that it would affect performance.
About FICON Device Allegiance
FICON requires serialization of access among multiple mainframes, CLI, and SNMP sessions be maintained on Cisco MDS 9000 Family switches by controlling device allegiance for the currently executing session. Any other session is denied permission to perform configuration changes unless the required allegiance is available.

Automatically Saving the Running Configuration
Cisco MDS NX-OS provides an option to automatically save any configuration changes to the startup configuration. This ensures that the new configuration is present after a switch reboot. By default, the Active=Saved active equals saved option is automatically enabled on any FICON VSAN.
Table 24-2 displays the results of the Active = Saved option active equals saved command and the implicit copy from the running configuration to the startup configuration ( copy running start ) copy running-config startup-config command in various scenarios.
When the Active=Saved option active equals saved command is enabled in any FICON-enabled VSAN in the fabric, then the following apply (see Number 1 and 2 in Table 24-2 ):
- All configuration changes (FICON-specific or not) are automatically saved to persistent storage (implicit copy running start ) and stored in the startup configuration.
- FICON-specific configuration changes are immediately saved to the IPL file (see the “FICON Configuration Files” section).
If the Active=Saved option active equals saved command is not enabled in any FICON-enabled VSAN in the fabric, then FICON-specific configuration changes are not saved in the IPL file and an implicit copy running startup command is not issued, you must explicitly save the running configuration to the startup configuration issue the copy running start command explicitly (see number 3 in Table 24-2 ).
|
1.When the Cisco NX-OS software implicitly issues a copy running-config startup-config command in the Cisco MDS switch, only a binary configuration is generated—an ASCII configuration is not generated (see Example 24-24 on page 24-64). If you wish to generate an additional ASCII configuration at this stage, you must explicitly issue the copy running-config startup-config command again. |

Note If active equals saved is enabled, the Cisco NX-OS software ensures that you do not have to perform the copy running startup command for the FICON configuration as well. If your switch or fabric consists of multiple FICON-enabled VSANs, and one of these VSANs have active equals saved enabled, changes made to the non-FICON configuration results in all configurations being saved to the startup configuration.
Port Prohibiting
To prevent implemented ports from talking to each other, configure prohibits between two or more ports. If you prohibit ports, the specified ports are prevented from communicating with each other.

Tip You cannot prohibit a PortChannel or FCIP interface.
Unimplemented ports are always prohibited. In addition, prohibit configurations are always symmetrically applied—if you prohibit port 0 from talking to port 15, port 15 is automatically prohibited from talking to port 0.

Note If an interface is already configured in E or TE mode and you try to prohibit that port, your prohibit configuration is rejected. Similarly, if a port is not up and you prohibit that port, the port is not allowed to come up in E mode or in TE mode.
About RLIR
The Registered Link Incident Report (RLIR) application provides a method for a switch port to send a Link Incident Record (LIR) to a registered Nx port.
When an LIR is detected in FICON-enabled switches in the Cisco MDS 9000 Family from an RLIR Extended Link Service (ELS), the switch sends that record to the members in its Established Registration List (ERL).
In case of multiswitch topology, a Distribute Registered Link Incident Record (DRLIR) Inter-Link Service (ILS) is sent to all reachable remote domains along with the RLIR ELS. On receiving the DRLIR ILS, the switch extracts the RLIR ELS and sends it to the members of the ERL.
The Nx ports interested in receiving the RLIR ELS send the Link Incident Record Registration (LIRR) ELS request to the management server on the switch. The RLIRs are processed on a per-VSAN basis.
The RLIR data is written to persistent storage when you enter the copy running-config startup-config command.
The RLIR data is written to persistent storage when you copy the running configuration to the startup configuration.
FICON Configuration Files
You can save up to 16 FICON configuration files on each FICON-enabled VSAN (in persistent storage). The file format is proprietary to IBM. These files can be read and written by IBM hosts using the in-band CUP protocol. Additionally, you can use the Cisco MDS CLI or DCNM-SAN applications to operate on these FICON configuration files.

Note Multiple FICON configuration files with the same name can exist in the same switch, provided they reside in different VSANs. For example, you can create a configuration file named XYZ in both VSAN 1 and VSAN 3.
When you enable the FICON feature in a VSAN, the switches always use the startup FICON configuration file, called IPL. This file is created with a default configuration as soon as FICON is enabled in a VSAN.

FICON configuration files contain the following configuration for each implemented port address:

Note Normal configuration files used by Cisco MDS switches include FICON-enabled attributes for a VSAN, port number mapping for PortChannels and FCIP interfaces, port number to port address mapping, port and trunk allowed VSAN configuration for ports, in-order guarantee, static domain ID configuration, and fabric binding configuration.
Refer to the Cisco MDS 9000 Family NX-OS Fundamentals Configuration Guide for details on the normal configuration files used by Cisco MDS switches.
Only one user can access the configuration file at any given time:
- If this file is being accessed by user 1, user 2 cannot access this file.
- If user 2 does attempt to access this file, an error is issued to user 2.
- If user 1 is inactive for more than 15 seconds, the file is automatically closed and available for use by any other permitted user.
FICON configuration files can be accessed by any host, SNMP, or CLI user who is permitted to access the switch. The locking mechanism in the Cisco NX-OS software restricts access to one user at a time per file. This lock applies to newly created files and previously saved files. Before accessing any file, you must lock the file and obtain the file key. A new file key is used by the locking mechanism for each lock request. The key is discarded when the lock timeout of 15 seconds expires. The lock timeout value cannot be changed.
Port Swapping
The FICON port-swapping feature is only provided for maintenance purposes.
The FICON port-swapping feature causes all configurations associated with old-port-number and new port-number to be swapped, including VSAN configurations.
Cisco MDS switches allow port swapping for nonexistent ports as follows:
- Only FICON-specific configurations (prohibit, block, and port address mapping) are swapped.
- No other system configuration is swapped.
- All other system configurations are only maintained for existing ports.
- If you swap a port in a module that has unlimited oversubscription ratios enabled with a port in a module that has limited oversubscription ratios, then you may experience a degradation in bandwidth.

Tip If you check the Active=Saved check box active equals saved is enabled on any FICON VSAN, then the swapped configuration is automatically saved to startup. Otherwise, you must explicitly save the running configuration immediately after swapping the ports.
Once you swap ports, the switch automatically performs the following actions:
If you attempt to bring the port up, you must explicitly shut down the port to resume traffic.

Note To view the latest FICON information, you must click the Refresh button. See the “Automatically Saving the Running Configuration”.
The ficon swap portnumber command is only associated with the two ports concerned. You must issue this VSAN-independent command from EXEC mode. Cisco MDS NX-OS checks for duplicate port numbers in a VSAN before performing the port swap.
If you attempt to bring the port up by specifying the ficon swap portnumber old-port-number new-port-number after swap noshut command, you must explicitly issue the no shutdown command to resume traffic.
FICON Tape Acceleration
The sequential nature of tape devices causes each I/O operation to the tape device over an FCIP link to incur the latency of the FCIP link. Throughput drastically decreases as the round-trip time through the FCIP link increases, leading to longer backup windows. Also, after each I/O operation, the tape device is idle until the next I/O arrives. Starting and stopping of the tape head reduces the lifespan of the tape, except when I/O operations are directed to a virtual tape.
Cisco MDS NX-OS software provides acceleration for the following FICON tape write operations:
- The link between mainframe and native tape drives (both IBM and Sun/STK)
- The back-end link between the VSM (Virtual Storage Management) and tape drive (Sun/STK)
FICON tape acceleration over FCIP provides the following advantages:
- Efficiently utilizes the tape device by decreasing idle time
- More sustained throughput as latency increases
- Similar to FCP tape acceleration, and does not conflict with it

Note FICON tape read acceleration over FCIP is supported from Cisco MDS NX-OS Release 5.0(1). For more information refer to the “Configuring FICON Tape Read Acceleration”.
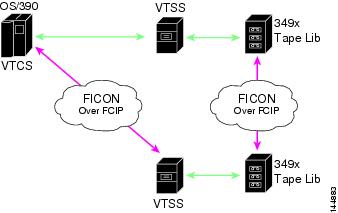
Figure 24-5 through Figure 24-8 show supported configurations.
Figure 24-5 Host Directly Accessing IBM/STK (StorageTek) Library

Figure 24-6 Host Accessing Standalone IBM-VTS (Virtual Tape Server) /STK-VSM (Virtual Shared Memory)
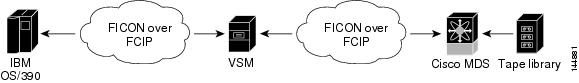
Figure 24-7 Host Accessing Peer-to-Peer VTS (Virtual Tape Server)
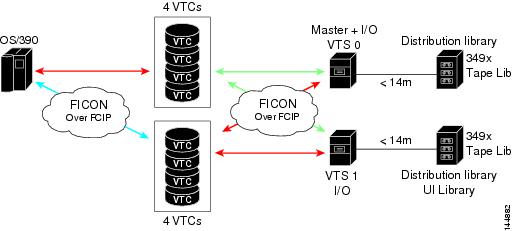
Figure 24-8 Host Accessing Peer-to-Peer VTS (Virtual Tape Server)

Note For information about FCIP tape acceleration, refer to the Cisco MDS 9000 Family NX-OS IP Services Configuration Guide.
CUP In-Band Management
The CUP protocol configures access control and provides unified storage management capabilities from a mainframe computer. Cisco MDS 9000 FICON-enabled switches are fully IBM CUP standard compliant for in-band management using the IBM S/A OS/390 I/O operations console.

Note The CUP specification is proprietary to IBM.
CUP is supported by switches and directors in the Cisco MDS 9000 Family. The CUP function allows the mainframe to manage the Cisco MDS switches.
Host communication includes control functions such as blocking and unblocking ports, as well as monitoring and error reporting functions.
Licensing Requirements for FICON
The following table shows the licensing requirements for this feature:
Guidelines and Limitations
This section includes the guidelines and limitations for this feature:
- FICON Port Numbering Guidelines
- Port Swapping Guidelines
- FICON Tape Acceleration Configuration Guidelines
FICON Port Numbering Guidelines
The following guidelines apply to FICON port numbers:
- Supervisor modules do not have port number assignments.
- Port numbers do not change based on TE ports. Since TE ports appear in multiple VSANs, chassis-wide unique port numbers should be reserved for TE ports.
- Each PortChannel must be explicitly associated with a FICON port number.
- When the port number for a physical PortChannel becomes uninstalled, the relevant PortChannel configuration is applied to the physical port.
- Each FCIP tunnel must be explicitly associated with a FICON port number. If the port numbers are not assigned for PortChannels or for FCIP tunnels, then the associated ports will not come up.
See the “About Port Numbers for FCIP and PortChannel” section.
Port Swapping Guidelines
Be sure to follow these guidelines when using the FICON port swapping feature:
- Port swapping is not supported for logical ports (PortChannels, FCIP links). Neither the old-port-number nor the new-port-number can be a logical port.
- Port swapping is not supported between physical ports that are part of a PortChannel. Neither the old-port-number nor the new-port-number can be a physical port that is part of a PortChannel.
- Before performing a port swap, the Cisco NX-OS software performs a compatibility check. If the two ports have incompatible configurations, the port swap is rejected with an appropriate reason code. For example, if a port with BB_credits as 25 is being swapped with an OSM port for which a maximum of 12 BB_credits is allowed (not a configurable parameter), the port swapping operation is rejected.
- Before performing a port swap, the Cisco NX-OS software performs a compatibility check to verify the extended BB_credits configuration.
- If ports have default values (for some incompatible parameters), then a port swap operation is allowed and the ports retain their default values.
- Port tracking information is not included in port swapping. This information must be configured separately (refer to the Cisco MDS 9000 Family NX-OS Quality of Service Configuration Guide ).

Note The 32-port module guidelines also apply for port swapping configurations (Refer to the Cisco MDS 9000 Family NX-OS Interfaces Configuration Guide).
FICON Tape Acceleration Configuration Guidelines
FICON tape acceleration has the following configuration guidelines:
- In addition to the normal FICON configuration, FICON tape acceleration must be enabled on both ends of the FCIP interface. If only one end has FICON tape acceleration enabled, acceleration does not occur.
- FICON tape acceleration is enabled on a per VSAN basis.
- FICON tape acceleration cannot function if multiple ISLs are present in the same VSAN (PortChannels or FSPF load balanced).
- You can enable both Fibre Channel write acceleration and FICON tape acceleration on the same FCIP interface.
Enabling or disabling FICON tape acceleration disrupts traffic on the FCIP interface.
Default Settings
Table 24-3 lists the default settings for FICON features.
Configuring FICON
By default FICON is disabled in all switches in the Cisco MDS 9000 Family. You can enable FICON on a per VSAN basis by using the Device Manager.
This section includes the following topics:
- Assigning FICON Port Numbers to Slots
- Reserving FICON Port Numbers for FCIP and PortChannel Interfaces
- Enabling FICON on the Switch
- Setting Up a Basic FICON Configuration
- Enabling FICON on a VSAN
- Manually Enabling FICON on a VSAN
- Deleting FICON VSANs
- Suspending a FICON VSAN
- Configuring the code-page Option
- Assigning FC ID Last Byte
- Allowing the Host to Move the Switch Offline
- Allowing the Host to Change FICON Port Parameters
- Allowing the Host to Control the Timestamp
- Clearing the Time Stamp
- Configuring SNMP Control of FICON Parameters
- Clearing FICON Device Allegiance
- Automatically Saving the Running Configuration
Assigning FICON Port Numbers to Slots
You can use the show ficon port-number assign and show ficon first-available port-number commands to determine which port numbers to use.

To assign FICON port numbers to a slot, follow these steps:
To assign FICON port numbers to slots using Device Manager, follow these steps:
Step 1 Click FICON and then select Port Numbers .
You see the FICON port number.
Step 2 Enter the chassis slot port numbers in the Reserved Port Numbers field.
Reserving FICON Port Numbers for FCIP and PortChannel Interfaces
You must reserve port numbers for logical interfaces, such as FCIP and PortChannels, if you plan to use them.
Detailed Steps
To reserve FICON port numbers for logical interfaces, follow these steps:
switch(config)# ficon logical-port assign port-numbers 230-249 |
Reserves port numbers 230 through 249 for FCIP and PortChannel interfaces. |
|
switch(config)# ficon logical-port assign port-numbers 0xe6-0xf9 |
Reserves port numbers 0xe6 through 0xf9 for FCIP and PortChannel interfaces. Note You cannot change port numbers that are active. You must disable the interfaces using the shutdown command and unbind port numbers using the no ficon portnumber command. See the “Configuring FICON Ports” section. |
|
switch(config)# no ficon logical-port assign port-numbers 230-249 |
Note You cannot release port numbers for interfaces that are active.You must disable the interfaces using the shutdown command and unbind port numbers using the no ficon portnumber command. See the “Configuring FICON Ports” section. |
To reserve FICON port numbers for FCIP and PortChannel interfaces using Device Manager, follow these steps:
Step 1 Click FICON > Port Numbers.
You see the FICON port numbers dialog box.
Step 2 Click the Logical tab to see the reserved port numbers for the slot.
Step 3 Enter the chassis slot port numbers. These are the reserved port numbers for one chassis slot. There can be up to 64 port numbers reserved for each slot in the chassis.
Enabling FICON on the Switch
By default FICON is disabled in all switches in the Cisco MDS 9000 Family. You can enable FICON on the switch either explicitly or implicitly by enabling FICON on a VSAN. However, disabling FICON on all VSANs does not disable FICON on the switch. You must explicitly disable FICON.
To explicitly enable or disable FICON globally on the switch, follow these steps:
Setting Up a Basic FICON Configuration
This section steps you through the procedure to set up FICON on a specified VSAN in a Cisco MDS 9000 Family switch.

Note Press Ctrl-C at any prompt to skip the remaining configuration options and proceed with what is configured until that point.

Tip If you do not want to answer a previously configured question, or if you want to skip answers to any questions, press Enter. If a default answer is not available (for example, switch name), the switch uses what was previously configured and skips to the next question.
To enable and set up FICON, follow these steps:
Step 1 Enter the setup ficon command at the EXEC command mode.
Step 2 Enter yes (the default is yes ) to enter the basic FICON configuration setup.
The FICON setup utility guides you through the basic configuration process. Press Ctrl-C at any prompt to end the configuration process.
Step 3 Enter the VSAN number for which FICON should be enabled.
Step 4 Enter yes (the default is yes ) to create a VSAN.
Step 5 Enter yes (the default is yes ) to confirm your VSAN choice:

Note At this point, the software creates the VSAN if it does not already exist.
Step 6 Enter the domain ID number for the specified FICON VSAN.
Step 7 Enter yes (the default is no ) to set up FICON in cascaded mode. If you enter no , skip to Step 8 (see the “CUP In-Band Management” section).
a. Assign the peer WWN for the FICON: CUP.
b. Assign the peer domain ID for the FICON: CUP
c. Enter yes if you wish to configure additional peers (and repeat Steps 7 a and 7 b ). Enter no , if you do wish to configure additional peers.
Step 8 Enter yes (the default is yes ) to allow SNMP permission to modify existing port connectivity parameters (see the “Configuring SNMP Control of FICON Parameters” section).
Step 9 Enter no (the default is no ) to allow the host (mainframe) to modify the port connectivity parameters, if required (see the “Allowing the Host to Change FICON Port Parameters” section).
Step 10 Enter yes (the default is yes ) to enable the active equals saved feature (see the “Automatically Saving the Running Configuration” section).
Step 11 Enter yes (the default is yes ) if you wish to configure additional FICON VSANs.
Step 12 Review and edit the configuration that you have just entered.
Step 13 Enter no (the default is no ) if you are satisfied with the configuration.

Note For documentation purposes, the following configurations shows three VSANs with different FICON settings. These settings provide a sample output for different FICON scenarios.
Step 14 Enter yes (the default is yes ) to use and save this configuration. The implemented commands are displayed. After FICON is enabled for the specified VSAN, you are returned to the EXEC mode switch prompt.

Note If a new VSAN is created, two additional commands are displayed— vsan database and vsan number.
Enabling FICON on a VSAN
To create a FICON-enabled VSAN, follow these steps:
Step 1 Click the Create VSAN icon (see Figure 24-9).
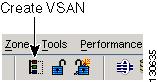
You see the Create VSAN dialog box.
Step 2 Select the switches you want to be in the VSAN.
Step 4 Enter the name of the VSAN, if desired.
Step 5 Select the type of load balancing, the interop value, and the administrative state for this VSAN.
Step 6 Check the FICON check box.

Note You cannot enable interop modes on FICON-enabled VSANs.
Step 7 Check the option, if appropriate, to enable fabric binding for the selected switches.
Step 8 Check the All Ports Prohibited option if all ports in this VSAN are prohibited.
Step 9 Click Create to create the VSAN.
Step 10 Choose Tools > Device Manager to open Device Manager for each switch in the FICON VSAN.
Step 12 Enter the VSAN membership information.
Step 13 Click the VSAN you want to become a FICON VSAN and select Add from the FICON drop-down menu.
Step 14 Click Apply to save these changes.
Manually Enabling FICON on a VSAN

Note This section describes the procedure to manually enable FICON on a VSAN. If you have already enabled FICON on the required VSAN using the automated setup (recommended), skip to the “Automatically Saving the Running Configuration” section.
To manually enable FICON on a VSAN, follow these steps:
|
switch(config-vsan-db)# vsan 5 switch(config-vsan-db)# do show vsan usage |
||
Configures the domain ID for VSAN 2. For information about configuring domain parameters, refer to the Cisco MDS 9000 Family NX-OS System Management Configuration Guide . |
||
Activates fabric binding on VSAN 2. Refer to the Cisco MDS 9000 Family NX-OS Security Configuration Guide |
||
Sets the default zone to permit for VSAN 2. See the “CUP In-Band Management” section. |
||
Prohibits mainframe users from moving the switch to an offline state. See the “Allowing the Host to Move the Switch Offline” section. |
To manually enable FICON on a VSAN, follow these steps:
You see the FICON VSAN configuration information in the Information pane.
Step 2 Select the switch in the VSAN on which you want to enable FICON.
Step 3 Click enable from the Command drop-down menu.
Step 4 Click the Apply Changes icon to save these changes.
Deleting FICON VSANs
To delete a FICON VSAN, follow these steps:
You see the VSAN table in the Information pane.
Step 2 Click anywhere in the row of the VSAN that you want to delete.
Step 3 Click Delete Row to delete the VSAN.

Note Deleting the VSAN will also delete the associated FICON configuration file, and the file cannot be recovered.
Suspending a FICON VSAN
To suspend a FICON VSAN, follow these steps:
You see all the VSANs listed in the Information pane.
Step 2 Select the VSAN that you want to suspend.
Step 3 Set the Admin drop-down menu for a VSAN to suspended.
Step 4 Click the Apply Changes icon to save these changes.

Note This command can be issued by the host if the host is allowed to do so (see the “Allowing the Host to Move the Switch Offline”).
Moving a FICON VSAN to an Offline State
Issue the ficon vsan vsan-id offline command in EXEC mode to log out all ports in the VSAN that need to be suspended.
Issue the EXEC-level ficon vsan vsan-id online command in EXEC mode to remove the offline condition and to allow ports to log on again.

Note This command can be issued by the host if the host is allowed to do so (see the “Allowing the Host to Move the Switch Offline” section).
Configuring the code-page Option
FICON strings are coded in Extended Binary-Coded Decimal Interchange Code (EBCDIC) format. Refer to your mainframe documentation for details on the code-page options.
Cisco MDS switches support international-5 , france , brazil , germany , italy , japan , spain-latinamerica , uk , and us-canada (default) EBCDIC format options.
To configure the code-page option in a VSAN, follow these steps:
To modify the code-page option using Device Manager, follow these steps:
You see the FICON VSAN configuration dialog box. The VSANs tab is the default tab.
Step 2 From the CodePage drop-down menu, choose an option for the FICON VSAN you want to configure.
Step 3 Click Apply to save the changes.
Restrictions
If the FICON feature is configured in cascaded mode, the Cisco MDS switches use ISLs to connect to other switches.
To assign the last byte for the FC ID, follow these steps:
Step 1 Choose All VSANs > Domain Manager.
Step 2 Click the Persistent FCIDs tab.
Step 3 Select single in the Mask column and then assign the entire FC ID at once. The single option allows you to enter the FC ID in the ###### format.
Step 4 Click the Apply Changes icon to save these changes.
Allowing the Host to Move the Switch Offline
By default, hosts are allowed to move the switch to an offline state. To do this, the host sends a "Set offline" command (x'FD') to the CUP.
To allow the host to move the switch to an offline state, follow these steps:
Prohibits mainframe users from moving the switch to an offline state. |
||
Allows the host to move the switch to an offline state (default) and shuts down the ports. |
To allow the host (mainframe) to move the switch to an offline state, follow these steps:
You see a list of switches under the Control tab in the Information pane.
You see the FICON VSAN configuration information in the Information pane.
Step 3 Check the Host Can Offline Sw check box to allow the mainframe to move a switch to the offline state.
Step 4 Check the Host Can Sync Time check box to allow the mainframe to set the system time on the switch.
Step 5 Click the Apply Changes icon to save the changes.
Allowing the Host to Change FICON Port Parameters
By default, mainframe users are not allowed to configure FICON parameters on Cisco MDS switches—they can only query the switch.
Use the host port control command to permit mainframe users to configure FICON parameters.
To allow the host (mainframe) to configure FICON parameters on the Cisco MDS switch, follow these steps:
Prohibits mainframe users from configuring FICON parameters on the Cisco MDS switch. |
||
Allows mainframe users to configure FICON parameters on the Cisco MDS switch (default). |
To allow the host (mainframe) to configure FICON parameters on the Cisco MDS switch, follow these steps:
You see a list of switches under the Control tab in the Information pane.
You see the FICON VSAN configuration information in the Information pane.
Step 3 Check the Port Control By Host check box to allow the mainframe to control a switch.
Step 4 Click the Apply Changes icon to save the changes.
Allowing the Host to Control the Timestamp
By default, the clock in each VSAN is the same as the switch hardware clock. Each VSAN in a Cisco MDS 9000 Family switch represents a virtual director. The clock and time present in each virtual director can be different.To maintain separate clocks for each VSAN, the Cisco NX-OS software maintains the difference of the VSAN-specific clock and the hardware-based director clock. When a host (mainframe) sets the time, the Cisco NX-OS software updates this difference between the clocks. When a host reads the clock, it computes the difference between the VSAN-clock and the current director hardware clock and presents a value to the mainframe.
The VSAN-clock current time is reported in the output of show ficon vsan vsan-id , show ficon , and show accounting log commands.
To configure host control of the timestamp, follow these steps:
To configure host (mainframe) control for the VSAN time stamp, follow these steps:
You see a list of switches under the Control tab in the Information pane.
You see the FICON VSAN configuration information in the Information pane.
Step 3 Check the Host Can Sync Time checkbox to allow the mainframe to set the system time on the switch.
Step 4 Click the Apply Changes icon to save these changes.
Clearing the Time Stamp

Note You can clear time stamps only from the Cisco MDS switch—not the mainframe.
Use the clear ficon vsan vsan-id timestamp command in EXEC mode to clear the VSAN clock.
Configuring SNMP Control of FICON Parameters
By default, SNMP users can configure FICON parameters using Cisco DCNM for SAN.
Restrictions
If you disable SNMP in the Cisco MDS switch, you cannot configure FICON parameters using DCNM-SAN.
To configure SNMP control of FICON parameters, follow these steps:
To configure SNMP control of FICON parameters, follow these steps:
You see a list of switches under the Control tab in the Information pane.
You see the FICON VSAN configuration information in the Information pane.
Step 3 Check the Port Control By SNMP checkbox to allow SNMP users to configure FICON on the switch.
Step 4 Click the Apply Changes icon to save these changes.
Clearing FICON Device Allegiance
You can clear the current device allegiance by issuing the clear ficon vsan vsan-id allegiance command in EXEC mode.
Automatically Saving the Running Configuration
To automatically save the running configuration, follow these steps:
To save the running configuration, follow these steps:
You see a list of switches under the Control tab in the Information pane.
You see the FICON VSAN configuration information in the Information pane.
Step 3 Check the Active=Saved check box to automatically save the running configuration to the startup configuration whenever there is a FICON configuration change.
Step 4 Click the Apply Changes icon to save these changes.
Configuring FICON Ports
You can perform FICON configurations on a per-port address basis in the Cisco MDS 9000 Family switches.
Even if a port is uninstalled, the port address-based configuration is accepted by the Cisco MDS switch. This configuration is applied to the port when the port becomes installed.
This section includes the following topics:
- Binding Port Numbers to PortChannels
- Binding Port Numbers to FCIP Interfaces
- Configuring Port Blocking
- Assigning a Port Address Name
- Specifying an RLIR Preferred Host
- Clearing RLIR Information
- Applying the Saved Configuration Files to the Running Configuration
- Editing FICON Configuration Files
- Copying FICON Configuration Files
- Swapping Ports
- Configuring FICON Tape Acceleration
- Configuring FICON Tape Read Acceleration
- Configuring XRC Acceleration
- Placing CUPs in a Zone
- Calculating FICON Flow Load Balance
- Receiving FICON Alerts
Binding Port Numbers to PortChannels

You can bind (or associate) a PortChannel with a FICON port number to bring up that interface.
To bind a PortChannel with a FICON port number, follow these steps:
Binding Port Numbers to FCIP Interfaces
You can bind (or associate) an FCIP interface with a FICON port number to bring up that interface.
To bind an FCIP interface with a FICON port number, follow these steps:
Configuring Port Blocking
If you block a port, the port is retained in the operationally down state. If you unblock a port, a port initialization is attempted. When a port is blocked, data and control traffic are not allowed on that port.
Physical Fibre Channel port blocks will continue to transmit an Off-line state (OLS) primitive sequence on a blocked port.

Note The shutdown/no shutdown port state is independent of the block/no block port state.
Restrictions
You cannot block or prohibit the CUP port (0XFE). If a port is shut down, unblocking that port does not initialize the port.
To block or unblock port addresses in a VSAN, follow these steps:
Disables a range of port addresses and retains it in the operationally down state. |
||
Enables the selected port address and reverts to the factory default of the port address not being blocked. |
To block or unblock port addresses in a VSAN using Device Manager, follow these steps:
Step 2 Select a VSAN ID and click Port Configuration .
You see the FICON Port Configuration dialog box for the selected VSAN.
Step 3 Check the Blocked check box for the port that you want to block.
Step 4 Click Apply to save the changes.
Configuring the Default State for Port Prohibiting
By default, port prohibiting is disabled on the implemented interfaces on the switch. As of Cisco MDS SAN-OS Release 3.0(2), you can change the default port prohibiting state to enabled in VSANs that you create and then selectively disable port prohibiting on implemented ports, if desired. Also, only the FICON configuration files created after you change the default have the new default setting (see the “FICON Configuration Files” section).
To change the default port prohibiting setting for all implemented interfaces on the switch, follow these steps:
Examples
Use the show ficon port default-state command to display the port prohibiting default state configuration.
Configuring Port Prohibiting
To prohibit port addresses in a VSAN, follow these steps:
Prohibits port address 7 in VSAN 2 from talking to ports 3, 4, and 5. |
||
To prohibit port addresses in a VSAN using Device Manager, follow these steps:
Step 2 Select a VASAN ID and click Port Configuration.
You see the FICON Port Configuration dialog box.
Step 3 Set the port prohibit configuration for the selected FICON VSANs.
Step 4 Click Apply to save these changes.
Assigning a Port Address Name
To assign a port address name, follow these steps:
Assigns a name to the port address. Note The port address name is restricted to 24 alphanumeric characters. |
||

Note To view the latest FICON information, you must click the Refresh button. See the “Automatically Saving the Running Configuration”.
To assign a port address name in Device Manager, follow these steps:
Step 2 Select a VSAN ID and click Port Configuration.
You see the FICON Port Configuration dialog box.
Step 3 Enter the Port Configuration information.
Step 4 Click Apply to save the configuration information.
Specifying an RLIR Preferred Host
As of Cisco MDS SAN-OS Release 3.0(3), you can specify a preferred host to receive RLIR frames. The MDS switch sends RLIR frames to the preferred host only if it meets the following conditions:
- No host in the VSAN is registered for RLIR with the registration function set to “always receive.” If one or more hosts in the VSAN are registered as “always receive,” then RLIR sends only to these hosts and not to the configured preferred host.
- The preferred host is registered with the registration function set to “conditionally receive.”

Note If all registered hosts have the registration function set to “conditionally receive,” then the preferred host receives the RLIR frames.
You can specify only one RLIR preferred host per VSAN. By default, the switch sends RLIR frames to one of the hosts in the VSAN with the register function set to “conditionally receive” if no hosts have the register function set to “always receive.”
To specify the RLIR preferred host for a VSAN, follow these steps:
Specifies FC ID 0x772c00 as the RLIR preferred host in VSAN 5. (FC ID 0x772c00 is used here as an example.) |
||
Removes FC ID 0x772c00 as the RLIR preferred host for VSAN 5. |
To display the RLIR preferred host configuration, use the show rlir erl command.
Clearing RLIR Information
Use the clear rlir statistics command to clear all existing statistics for a specified VSAN.
Use the clear rlir history command to clear the RLIR history where all link incident records are logged for all interfaces.
Use the clear rlir recent interface command to clear the most recent RLIR information for a specified interface.
Use the clear rlir recent portnumber command to clear the most recent RLIR information for a specified port number.
Applying the Saved Configuration Files to the Running Configuration
You can apply the configuration from the saved files to the running configuration using the ficon vsan number apply file filename command.
To apply the saved configuration files to the running configuration using Device Manager, follow these steps:
You see the FICON Files dialog box.
Step 3 Highlight the file you want to apply and click Apply File to apply the configuration to the running configuration.
Editing FICON Configuration Files
The configuration file submode allows you to create and edit FICON configuration files. If a specified file does not exist, it is created. Up to 16 files can be saved. Each file name is restricted to eight alphanumeric characters.
To edit the contents of a specified FICON configuration file, follow these steps:

Note To view the latest FICON information, you must click the Refresh button. See the “Automatically Saving the Running Configuration” section.
To edit the contents of a specified FICON configuration file using Device Manager, follow these steps:
You see the FICON VSANs dialog box.
Step 3 Select a VSAN ID and then click Open to edit the FICON configuration file.
Step 4 Select a VSAN ID and then click Delete to delete the FICON configuration file.
Step 5 Click Apply to apply the changed FICON configuration file.
Copying FICON Configuration Files
Use the ficon vsan vsan-id copy file existing-file-name save-as-file-name command in EXEC mode to copy an existing FICON configuration file.
To copy an existing FICON configuration file using Device Manager, follow these steps:
You see the FICON VSANs dialog box.
Step 3 Click Create to create a FICON configuration file.
You see the Create FICON VSANs Files dialog box.
a. Select a VSAN ID for the FICON VSAN you want to configure.
b. Enter the file name and the description.
c. Click Create to create the file.
Step 4 Click Copy to copy the file to a new file.
Step 5 Click Apply to apply the FICON configuration file.
Examples
You can see the list of existing configuration files by issuing the show ficon vsan vsan-id command.
Swapping Ports
If there are no duplicate port numbers on the switch, you can swap physical Fibre Channel ports, except the port numbers, by following these steps:
Step 1 Issue the ficon swap portnumber old-port-number new-port-number command in EXEC mode.

Note The ficon swap portnumber command might fail if more than one interface on the MDS switch has the same port number as the old-port-number or new-port-number specified in the command.
The specified ports are operationally shut down.
Step 2 Physically swap the front panel port cables between the two ports.
Step 3 Issue the no shutdown command on each port to enable traffic flow.

Note If you specify the ficon swap portnumber old-port-number new-port-number after swap noshut command, the ports are automatically initialized.
If there are duplicate port numbers on the switch, you can swap physical Fibre Channel ports, including the port numbers, by following these steps:
Step 1 Issue the ficon swap interface old-interface new-interface command in EXEC mode.
The specified interfaces are operationally shut down.
Step 2 Physically swap the front panel port cables between the two ports.
Step 3 Issue the no shutdown command on each port to enable traffic flow.

Note If you specify the ficon swap interface old-interface new-interface after swap noshut command, the ports are automatically initialized.
To swap ports using Device Manager, follow these steps:
Step 1 Select two Fibre Channel ports by holding down the CTRL key and clicking them.
Step 2 Choose FICON > Swap Selected Ports.
Configuring FICON Tape Acceleration
To configure FICON tape acceleration, follow these steps:
Use the show running-config command to verify the FICON tape acceleration over FCIP configuration.
To configure FICON tape acceleration over FCIP, follow these steps:
Step 1 Expand ISL and then select FCIP in the Physical Attributes pane.
Step 2 Click the Tunnels tab in the Information pane.
You see a list of available switches.
Step 3 Click the Create Row icon to create an FCIP tunnel.
You see the Create FCIP Tunnel dialog box.
Step 4 Configure the tunnel with the options.
Step 5 Check the TapeAccelerator check box to enable FICON tape acceleration over this FCIP tunnel.
Configuring FICON Tape Read Acceleration
All the configuration guidelines and restrictions applicable for FICON tape acceleration are also applicable for FICON tape read acceleration. Both FICON tape acceleration and FICON tape read acceleration can coexist.
To configure FICON tape read acceleration, follow these steps:
Configuring XRC Acceleration
IBM z/OS Global Mirror eXtended Remote Copy (XRC) is supported on the MSM-18+4 modules. For XRC to function, XRC acceleration must be enabled on the FCIP tunnel interfaces on both ends. XRC acceleration is disabled by default.
Restrictions
To enable XRC acceleration, follow these steps:
Specifies an FCIP tunnel interface and enters interface configuration submode. |
||
Disables (default) XRC acceleration over the FCIP tunnel interface. |
XRC acceleration and FICON tape acceleration cannot be enabled on the same FCIP tunnel interface and cannot exist in the same VSAN.
To configure XRC acceleration on a FCIP tunnel interface, follow these steps:
Step 1 Expand ISL and then select FCIP in the Physical Attributes pane.
Step 2 Click the Tunnels(Advanced) tab in the Information pane.
You see a list of available FCIP interfaces.
Step 3 Check the check box in the XRC Emulator column to enable XRC acceleration over the FCIP tunnel.
To configure XRC acceleration on an FCIP tunnel interface using Device Manager, follow these steps:
Step 1 In the Device Manager window, click IP and then select FCIP from the menu.
Step 2 Click the Tunnels(Advanced) tab in the Information pane.
You see a list of FCIP interfaces.
Step 3 Check the check box in the XRC Emulator column to enable XRC acceleration over the FCIP tunnel.
Placing CUPs in a Zone
To place the CUP in a zone, follow these steps:
Step 1 Set the default zone to permit for the required VSAN.
Step 2 Issue the show fcns database command for the required VSAN and obtain the required FICON CUP WWN.

Note If more than one FICON:CUP WWN exists in this fabric, be sure to add all the FICON:CUP WWN PWWNs to the required zone. The previous sample output displays multiple FICON:CUP occurrences to indicate a cascade configuration.
Step 3 Add the identified FICON:CUP WWN to the zone database.
To place the CUP in a zone, follow these steps:
Step 1 In DCNM-SAN, choose Zone > Edit Full Zoneset, and then choose Edit > Edit Default Zone Attributes to set the default zone to permit for the required VSAN.
Step 2 In Device Manager, choose FC > Name Server... for the required VSAN and obtain the FICON:CUP WWN.

Note If more than one FICON:CUP WWN exists in this fabric, be sure to add all the FICON:CUP pWWNs to the required zone.
Step 3 In DCNM-SAN, choose Zone > Edit Full Zoneset and add the FICON:CUP pWWN to the zone database.
Calculating FICON Flow Load Balance
The FICON Flow Load Balance Calculator allows you to get the best load balancing configuration for your FICON flows. The calculator does not rely on any switch or flow discovery in the fabric. It is available from the DCNM-SAN Tools menu.
To use the FICON Flow Load Balance Calculator, follow these steps:
Step 1 Choose Tools > Flow Load Balance Calculator.
You see the Flow Load Balance Calculator.
Step 2 Click Add to enter the source and destination(s) flows.
Step 3 Enter source and destination using 2 byte hex (by domain and area IDs).You can copy and paste these IDs, and then edit them if required.
Step 4 Enter (or select) the number of ISLs between the two switches (for example, between domain ID 0a and 0b).
Step 5 Select a row to remove it and click Remove .
Step 6 Select the module for which you are calculating the load balance.
Step 7 Click Calculate to show the recommended topology.

Note If you change flows or ISLs, you must click Calculate to see the new recommendation.
Receiving FICON Alerts
In Example 24-1, the user alert mode is Enabled output confirms that you will receive an alert to indicate any changes in the FICON configuration.
Example 24-1 Displays Configured FICON Information
To receive an alert to indicate any changes in the FICON configuration using Device Manager, follow these steps:
You see the FICON VSANs dialog box.
Step 2 Check the User Alert Mode check box to receive an alert when the FICON configuration changes.
Step 3 Click Apply to apply this change.
Verifying FICON Configuration
To display the FICON configuration information, perform one of the following tasks:
For detailed information about the fields in the output from these commands, refer to the Cisco MDS 9000 Family Command Reference .
This section includes the following topics:
- Displaying the FICON Port Number Assignments
- Viewing ESCON Style Ports
- Displaying RLIR Information
- Displaying FICON Configuration Files
- Displaying XRC Acceleration Statistics
- Displaying Control Unit Information
- Displaying FICON Port Address Information
- Displaying IPL File Information
- Displaying FICON Configuration File Information
- Displaying the Configured FICON State
- Displaying a Port Administrative State
- Displaying Buffer Information
- Viewing the History Buffer
- Displaying FICON Information in the Running Configuration
- Displaying FICON Information in the Startup Configuration
- Displaying FICON-Related Log Information
Displaying the FICON Port Number Assignments
Use the show ficon port-numbers assign command to display the port numbers assigned on the switch.
Use the show ficon port-numbers assign slot command to display the port numbers assigned to a specific slot.
Use the show ficon port-numbers assign command to display the port numbers reserved for logical ports.
Viewing ESCON Style Ports
To view the available and prohibited ESCON style ports using Device Manager, follow these steps:
Step 1 Check the ESCON Style check box to see the available and prohibited ESCON style ports.
In Figure 24-10, A stands for available and P stands for prohibited.
When the port address is highlighted red, it represents the E/TE port or multiple interfaces.
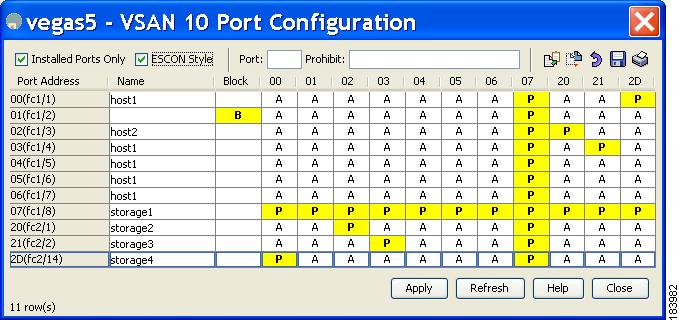
Step 2 Click Apply to save the changes.
Displaying RLIR Information
The show rlir statistics command displays the complete statistics of LIRR, RLIR, and DRLIR frames. It lists the number of frames received, sent, and rejected. Specify the VSAN ID to obtain VSAN statistics for a specific VSAN. If you do not specify the VSAN ID, then the statistics are shown for all active VSANs (see Examples 24-2 and 24-3 ).
Example 24-2 Displays RLIR Statistics for All VSANs
Example 24-3 Displays RLIR Statistics for a Specified VSAN
The show rlir erl command shows the list of Nx ports that are registered to receive the RLIRs with the switch. If the VSAN ID is not specified, the details are shown for all active VSANs (see Examples 24-4 and 24-5 ).
Example 24-4 Displays All ERLs
In Example 24-4, if the Registered For column states that an FC ID is conditional receive, the source port is registered as a valid recipient of subsequent RLIRs. This source port is selected as an RLIR recipient only if no other ERL recipient is selected.
In Example 24-4, if the Registered For column states that an FC ID is always receive, the source port is registered as a valid recipient of subsequent RLIRs. This source port is always selected as an LIR recipient.

Note If an always receive RLIR is not registered for any N port or if the delivery of an RLIR fails for one of those ports, then the RLIR is sent to a port registered to conditional receive RLIRs.
Example 24-5 Displays ERLs for the Specified VSAN

Note In Example 24-6, through Example 24-8, if the host time stamp (marked by the *) is available, it is printed along with the switch time stamp. If the host time stamp is not available, only the switch time stamp is printed.
Example 24-6 Displays the LIR History
Example 24-7 Displays Recent LIRs for a Specified Interface
Example 24-8 Displays Recent LIRs for a Specified Port Number
As of Cisco SAN-OS Release 3.0(3), the show rlir history command output includes remote link incidents that are received as DRLIRs from other switches. RLIRs are generated as a result of DRLIRs as in previous Cisco NX-OS releases (see Example 24-9).
Example 24-9 Displays the LIR History as of Cisco SAN-OS Release 3.0(3)
To view RLIR information using Device Manager, follow these steps:
Step 1 Choose FICON > RLIR ERL.
You see the Show RLIR ERL dialog box.
Step 2 Click Close to close the dialog box.
Displaying FICON Configuration Files
Use the show ficon vsan vsan-id file all command to display the contents of all FICON configuration files.
Use the show ficon vsan vsan-id file name command to display the contents of a specific FICON configuration file.
Use the show ficon vsan vsan-id file name filename portaddress command to display the FICON configuration file information for a specific FICON port.
To open and view configuration files in DCNM-SAN, follow these steps:
You see the FICON configuration table in the Information pane.
Step 3 Select the file you want to open.
Displaying XRC Acceleration Statistics
To display XRC acceleration statistics, follow these steps:
Step 1 Expand ISL and then select FCIP in the Physical Attributes pane.
Step 2 Click the XRC Statistics tab in the Information pane.
You see the XRC session statistics.
To display XRC acceleration statistics using Device Manager, follow these steps:
Step 1 In the Device Manager window, click IP, and then select FCIP from the menu.
Step 2 Click the XRC Statistics tab in the Information pane.
You see the XRC session statistics.
Displaying Control Unit Information
Example 24-10 displays configured control device information.
Displaying FICON Port Address Information
Examples 24-11 to 24-14 display FICON Port Address information.
Example 24-11 Displays Port Address Information
Example 24-12 Displays the Available Port Numbers
In Example 24-13, the interface column is populated with the corresponding interface if the port number is installed. If the port number is uninstalled, this space remains blank and indicates an unbound port number. For example, 56 is an unbound port number in Example 24-13.
Example 24-13 Displays Port Address Information in a Brief Format
Example 24-14 displays the counters in FICON version format 1 (32-bit format)
Example 24-14 Displays Port Address Counter Information
To display FICON port address information using Device Manager, follow these steps:
You see the FICON VSANs dialog box.
Step 2 Select a VSAN ID and click Port Configuration.
You see the FICON Port Configuration dialog box.
Step 3 Click Close to close the dialog box.
Displaying IPL File Information
To display the IPL file information using Device Manager, follow these steps:
Step 1 Select VSANs from the FICON menu.
You see the FICON VSANs dialog box.
Step 3 Select the file that you want to view and click Open.
Displaying FICON Configuration File Information
Examples 24-15 to 24-17 display FICON configuration file information.
Example 24-15 Displays the Contents of the Specified FICON Configuration File
Example 24-16 Displays All FICON Configuration Files
Example 24-17 Displays the Specified Port Addresses for a FICON Configuration File
Displaying the Configured FICON State
If FICON is enabled on a VSAN, you can display the port address information for that VSAN (see Example 24-18).
Example 24-18 Displays the Specified Port Address When FICON Is Enabled
Displaying a Port Administrative State
Examples 24-19 to 24-20 display the administrative state of a FICON port. If the port is blocked, the show ficon vsan number portaddress number command displays the blocked state of the port. If a specific port is prohibited, this command also displays the specifically prohibited port (3) along with the ports that are prohibited by default (0, 241 to 253, and 255). If a name is assigned, that name is also displayed.
Displaying Buffer Information
In Example 24-21, the Key Counter column displays the 32-bit value maintained by Cisco MDS switches. This value is incremented when any port changes state in that VSAN. The key counter (a 32-bit value) is incremented when a FICON-related configuration is changed. Host programs can increment this value at the start of the channel program and then perform operations on multiple ports. The director history buffer keeps a log of which port address configuration was changed for each key-counter value.
The director history buffer provides a mechanism to determine the change in the port state from the previous time when a value was contained in the key counter.
Example 24-21 Displays the History Buffer for the Specified VSAN
Viewing the History Buffer
In the directory history buffer, the Key Counter column displays the 32-bit value maintained by Cisco MDS switches. This value is incremented when any port changes state in that VSAN. The key counter (a 32-bit value) is incremented when a FICON-related configuration is changed. Host programs can increment this value at the start of the channel program and then perform operations on multiple ports. The director history buffer keeps a log of which port address configuration was changed for each key-counter value.
The director history buffer provides a mechanism to determine the change in the port state from the previous time when a value was contained in the key counter.
To view the directory history buffer using Device Manager, follow these steps:
You see the FICON VSANs dialog box.
Step 2 Click the Director History button.
You see the history buffer dialog box.
Step 3 Click Close to close the dialog box.
Displaying FICON Information in the Running Configuration
Example 24-22 displays the FICON-related information in the running configuration.
Example 24-22 Displays the Running Configuration Information
Displaying FICON Information in the Startup Configuration
Example 24-23 displays the FICON-related information in the startup configuration.
Example 24-23 Displays the Startup Configuration
Example 24-24 displays the switch response to an implicitly-issued copy running start command. In this case, only a binary configuration is saved until you explicitly issue the copy running start command again (see Table 24-2)
Displaying FICON-Related Log Information
Example 24-25 and Example 24-26 display the logging information for FICON-related configurations.
Field Descriptions for FICON
This section displays the field descriptions for this feature.
FICON VSANs
FICON Port Attributes
FICON Port Configuration
Additional References
For additional information related to implementing VSANs, see the following section:
Feature History for FICON
Table 24-4 lists the release history for this feature. Only features that were introduced or modified in 5.0(1a) or a later release appear in the table.
FICON tape acceleration over FCIP efficiently utilizes the tape device by decreasing idle time. The following sections provide information about this feature:
The following commands were introduced or modified: ficon-tape-read-accelerator. |
||
 Feedback
Feedback